Repairs questions
•
0 likes•356 views
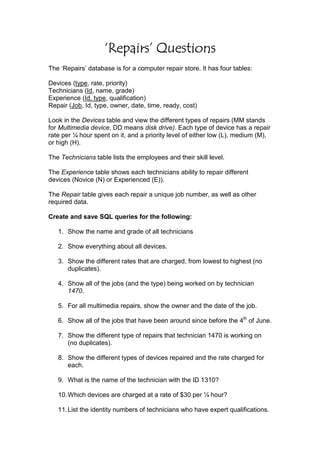
This document describes the tables in a database for a computer repair store. It includes tables for devices, technicians, experience, and repairs. It then lists 39 queries to run on the database to return requested information.
Report
Share
Report
Share
Download to read offline
Recommended
Assignment DetailsYou have learned that some markets are compet.docx

Assignment Details:
You have learned that some markets are competitive but that there are also a few markets that are serviced by just one firm. Examples include utility companies that provide electricity and natural gas to homeowners.
Please draw on your own experiences and what you have learned in Unit 4 to discuss the following points. Please use economic concepts; and use references in your main contribution.
Please identify and describe your local utility.
Please explain what products or services it provides.
Are there other companies that provide these products in your community?
Have prices increased in the last 2 years? Please explain.
Do you think prices would be higher or lower if there were 2 or more providers? Please explain.
Deliverable Length: 200 words (minimum)
Reading Assignment
Read the following chapters from the Microeconomics textbook:
· Chapter 7
· Barriers to Entry, Economies of Scale, p. 98
· Welfare and Monopoly, pp. 103-150
· Antitrust, pp. 110-116
· Price Discrimination, p. 104
· Average Cost Pricing, p. 105
Liem Le | COSC2436 #1
School of Engineering and Technology
COSC2436 – LAB 7
Title Tree Data Structure – Binary Search Tree
Time to
complete
Two weeks
COURSE OBJECTIVES
LEARNING OUTCOME
LAB OBJECTIVES
-Apply Object Oriented programming
-Complete the lab on time (Time
Management)
-Do the lab by following the project process:
analysis, design, write the code, test, debug,
implement
-UML of data type class
-Write comments
-Write the code of data type classes including
data members, no-argument constructor,
parameter constructors, mutator methods,
assessor methods, toString and other methods
-INHERITANCE: write the code of child classes
including, data members, constructors and
other methods inherited from parent class
-apply Polymorphism: using object of the
parent class to point to object of child classes
-control structure: if..else, switch, do..while
-create object, access members of data type
class
-format the output in columns and double
numbers with 2 decimal digits
-display message box
-create and access 4 operations of the tree
data structure
-Create a new project, add source file to the project,
compile and run the program without errors and qualified
to the requirement
-Declare variables of int, double, String;
-provide UML of data types
-Create data types with data members, constructors,
mutator methods
-Apply Inheritance relationship
-Apply polymorphism in the project
-provide the pseudo-code of program
-create and manage the menu to loop back to re-display
after each task: using do.. while
-Use switch statement to determine and define the action
for each task
-Format the output in columns and double numbers wiwth 2
decimal digits
-Display message box
-can figure out the base case, reduce problem, general
solution and recursion algorithm to write the recursion code
for som.
FUNCTIONAL AND NON FUNCTIONAL REQUIREMENT

HOW TO IDENTIFY FUNCTIONAL AND NON-FUNCTIONAL REQUIREMENTS FROM THE SCENARIO BASED QUESTION
Recommended
Assignment DetailsYou have learned that some markets are compet.docx

Assignment Details:
You have learned that some markets are competitive but that there are also a few markets that are serviced by just one firm. Examples include utility companies that provide electricity and natural gas to homeowners.
Please draw on your own experiences and what you have learned in Unit 4 to discuss the following points. Please use economic concepts; and use references in your main contribution.
Please identify and describe your local utility.
Please explain what products or services it provides.
Are there other companies that provide these products in your community?
Have prices increased in the last 2 years? Please explain.
Do you think prices would be higher or lower if there were 2 or more providers? Please explain.
Deliverable Length: 200 words (minimum)
Reading Assignment
Read the following chapters from the Microeconomics textbook:
· Chapter 7
· Barriers to Entry, Economies of Scale, p. 98
· Welfare and Monopoly, pp. 103-150
· Antitrust, pp. 110-116
· Price Discrimination, p. 104
· Average Cost Pricing, p. 105
Liem Le | COSC2436 #1
School of Engineering and Technology
COSC2436 – LAB 7
Title Tree Data Structure – Binary Search Tree
Time to
complete
Two weeks
COURSE OBJECTIVES
LEARNING OUTCOME
LAB OBJECTIVES
-Apply Object Oriented programming
-Complete the lab on time (Time
Management)
-Do the lab by following the project process:
analysis, design, write the code, test, debug,
implement
-UML of data type class
-Write comments
-Write the code of data type classes including
data members, no-argument constructor,
parameter constructors, mutator methods,
assessor methods, toString and other methods
-INHERITANCE: write the code of child classes
including, data members, constructors and
other methods inherited from parent class
-apply Polymorphism: using object of the
parent class to point to object of child classes
-control structure: if..else, switch, do..while
-create object, access members of data type
class
-format the output in columns and double
numbers with 2 decimal digits
-display message box
-create and access 4 operations of the tree
data structure
-Create a new project, add source file to the project,
compile and run the program without errors and qualified
to the requirement
-Declare variables of int, double, String;
-provide UML of data types
-Create data types with data members, constructors,
mutator methods
-Apply Inheritance relationship
-Apply polymorphism in the project
-provide the pseudo-code of program
-create and manage the menu to loop back to re-display
after each task: using do.. while
-Use switch statement to determine and define the action
for each task
-Format the output in columns and double numbers wiwth 2
decimal digits
-Display message box
-can figure out the base case, reduce problem, general
solution and recursion algorithm to write the recursion code
for som.
FUNCTIONAL AND NON FUNCTIONAL REQUIREMENT

HOW TO IDENTIFY FUNCTIONAL AND NON-FUNCTIONAL REQUIREMENTS FROM THE SCENARIO BASED QUESTION
What is data center availability modes slide

What is data center availability modes slide, types of data center availability modes, What is uptime institute data center certificates, What is data center availability modes slide,EN 50600 Availability classes (1-4), TIA 942-B Ratings (1-4), 10 Syska Hennessy Criticality Levels, ANSI/BICSI Classes (F0-F4), N, N+1, 2N, 2(N+1) for data centers
Computer paper 3 may june 2004 9691 cambridge General Certificate of educatio...

Computer paper 3 may june 2004 9691 cambridge General Certificate of education advanced level zimsec zimbabwe computers
Digital Electronics & Fundamental of Microprocessor-I

It contents number system, Logical expression its minimization and implementation, Combinational circuit, Sequential circuit.
90 Informatics Practices.pdf

JJHJHDJHHHDHHDJHJHDGDHHDGHGGDGHGDGDGHDGHGDGDDDHJKHDHJDHJDJHDJHDKDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDD
CIS 115 Exceptional Education - snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
CMMS - From Theory to Execution

A complete guide on preparation, planning and execution of a computerized maintenance management system with examples and illustration of the program modules interaction and the way these programs operate.
Cis 115 Education Organization -- snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
Peripherals and Ports

Peripherals are additional devices that are attached to the computer they can be classified as input, output, input-output or network as discussed in the previous unit.
Ports offer standard connection points between the motherboard and external devices.
Cis 115 Education Organization / snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
More Related Content
Similar to Repairs questions
What is data center availability modes slide

What is data center availability modes slide, types of data center availability modes, What is uptime institute data center certificates, What is data center availability modes slide,EN 50600 Availability classes (1-4), TIA 942-B Ratings (1-4), 10 Syska Hennessy Criticality Levels, ANSI/BICSI Classes (F0-F4), N, N+1, 2N, 2(N+1) for data centers
Computer paper 3 may june 2004 9691 cambridge General Certificate of educatio...

Computer paper 3 may june 2004 9691 cambridge General Certificate of education advanced level zimsec zimbabwe computers
Digital Electronics & Fundamental of Microprocessor-I

It contents number system, Logical expression its minimization and implementation, Combinational circuit, Sequential circuit.
90 Informatics Practices.pdf

JJHJHDJHHHDHHDJHJHDGDHHDGHGGDGHGDGDGHDGHGDGDDDHJKHDHJDHJDJHDJHDKDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDDD
CIS 115 Exceptional Education - snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
CMMS - From Theory to Execution

A complete guide on preparation, planning and execution of a computerized maintenance management system with examples and illustration of the program modules interaction and the way these programs operate.
Cis 115 Education Organization -- snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
Peripherals and Ports

Peripherals are additional devices that are attached to the computer they can be classified as input, output, input-output or network as discussed in the previous unit.
Ports offer standard connection points between the motherboard and external devices.
Cis 115 Education Organization / snaptutorial.com

For more classes visit
www.snaptutorial.com
CIS 115 All Exercises Devry University
Similar to Repairs questions (20)
Computer paper 3 may june 2004 9691 cambridge General Certificate of educatio...

Computer paper 3 may june 2004 9691 cambridge General Certificate of educatio...
Digital Electronics & Fundamental of Microprocessor-I

Digital Electronics & Fundamental of Microprocessor-I
Cis 115 Education Organization -- snaptutorial.com

Cis 115 Education Organization -- snaptutorial.com
More from hccit
More from hccit (20)
Recently uploaded
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Monitoring and observability aren’t traditionally found in software curriculums and many of us cobble this knowledge together from whatever vendor or ecosystem we were first introduced to and whatever is a part of your current company’s observability stack.
While the dev and ops silo continues to crumble….many organizations still relegate monitoring & observability as the purview of ops, infra and SRE teams. This is a mistake - achieving a highly observable system requires collaboration up and down the stack.
I, a former op, would like to extend an invitation to all application developers to join the observability party will share these foundational concepts to build on:
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
GridMate - End to end testing is a critical piece to ensure quality and avoid...

End to end testing is a critical piece to ensure quality and avoid regressions. In this session, we share our journey building an E2E testing pipeline for GridMate components (LWC and Aura) using Cypress, JSForce, FakerJS…
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

Sudheer Mechineni, Head of Application Frameworks, Standard Chartered Bank
Discover how Standard Chartered Bank harnessed the power of Neo4j to transform complex data access challenges into a dynamic, scalable graph database solution. This keynote will cover their journey from initial adoption to deploying a fully automated, enterprise-grade causal cluster, highlighting key strategies for modelling organisational changes and ensuring robust disaster recovery. Learn how these innovations have not only enhanced Standard Chartered Bank’s data infrastructure but also positioned them as pioneers in the banking sector’s adoption of graph technology.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

Leonard Jayamohan, Partner & Generative AI Lead, Deloitte
This keynote will reveal how Deloitte leverages Neo4j’s graph power for groundbreaking digital twin solutions, achieving a staggering 100x performance boost. Discover the essential role knowledge graphs play in successful generative AI implementations. Plus, get an exclusive look at an innovative Neo4j + Generative AI solution Deloitte is developing in-house.
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
UiPath Test Automation using UiPath Test Suite series, part 5

Welcome to UiPath Test Automation using UiPath Test Suite series part 5. In this session, we will cover CI/CD with devops.
Topics covered:
CI/CD with in UiPath
End-to-end overview of CI/CD pipeline with Azure devops
Speaker:
Lyndsey Byblow, Test Suite Sales Engineer @ UiPath, Inc.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Recently uploaded (20)
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf

Observability Concepts EVERY Developer Should Know -- DeveloperWeek Europe.pdf
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
GridMate - End to end testing is a critical piece to ensure quality and avoid...

GridMate - End to end testing is a critical piece to ensure quality and avoid...
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...
Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx

Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
UiPath Test Automation using UiPath Test Suite series, part 5

UiPath Test Automation using UiPath Test Suite series, part 5
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Repairs questions
- 1. ‘Repairs’ Questions The ‘Repairs’ database is for a computer repair store. It has four tables: Devices (type, rate, priority) Technicians (Id, name, grade) Experience (Id, type, qualification) Repair (Job, Id, type, owner, date, time, ready, cost) Look in the Devices table and view the different types of repairs (MM stands for Multimedia device, DD means disk drive). Each type of device has a repair rate per ¼ hour spent on it, and a priority level of either low (L), medium (M), or high (H). The Technicians table lists the employees and their skill level. The Experience table shows each technicians ability to repair different devices (Novice (N) or Experienced (E)). The Repair table gives each repair a unique job number, as well as other required data. Create and save SQL queries for the following: 1. Show the name and grade of all technicians 2. Show everything about all devices. 3. Show the different rates that are charged, from lowest to highest (no duplicates). 4. Show all of the jobs (and the type) being worked on by technician 1470. 5. For all multimedia repairs, show the owner and the date of the job. 6. Show all of the jobs that have been around since before the 4th of June. 7. Show the different type of repairs that technician 1470 is working on (no duplicates). 8. Show the different types of devices repaired and the rate charged for each. 9. What is the name of the technician with the ID 1310? 10. Which devices are charged at a rate of $30 per ¼ hour? 11. List the identity numbers of technicians who have expert qualifications.
- 2. 12. Which devices are ready for collection? 13. What is the level of experience of technician 1470 when working on iMacs? 14. Find the jobs being worked on by technicians 1470 and 1011. 15. The order of ANDs and ORs can affect the result. ANDs are always worked out first. To make sure you get the result you expect, always use brackets. For example, type the following two queries in and see what difference the brackets make: SELECT job, id, type FROM repair WHERE id=1470 OR id=1008 AND type=’iMac’ OR type=’MM’ SELECT job, id, type FROM repair WHERE (id=1470 OR id=1008) AND (type=’iMac’ OR type=’MM’) 16. Show type, rate and priority of devices that have a rate of $20 or $25, and are also either a multimedia device or a disk drive. 17. Show the owners and job dates of all repairs between June 4th and June 6th. 18. Use the In operator to show the rates for input and output devices. 19. Show all of the owners with names beginning with ‘B’. 20. Show any five-letter technician names starting with ‘C’.
- 3. 21. Show the number of hard drives being repaired. 22. Show the maximum time taken to repair each device type. 23. Edit the previous query to display the maximum time with the heading “Maximum Time” and with the text “quarter hours” appended to the values (e.g. ‘4 quarter hours’). 24. What is the average time each technician takes to complete a job? 25. Show the number of jobs entered on each date. 26. Show the type of devices that have exactly two jobs. 27. List the jobs that have a high priority. 28. Show the ID and name of technicians who are classed as experts. 29. Which high priority devices being worked on by Johnson are ready for collection? 30. What is the date entered for all low priority repairs? 31. Show the device type and repair rate for devices that have technicians who are novices. 32. Which technicians are experts at repairing iMacs? 33. What is the grade of the technician repairing the device owned by James? 34. What will be the charge for the repair to Elliot’s device?
- 4. 35. Who owns devices being repaired by Ted Carrol? 36. What are the names of the technicians who are still not expert (N) at repairing Macs? 37. What rate will Byrne be charged for repairs? 38. List the owners whose devices have a high priority for repair. 39. What level of qualification has the technician who is doing Taylor’s repair job?
