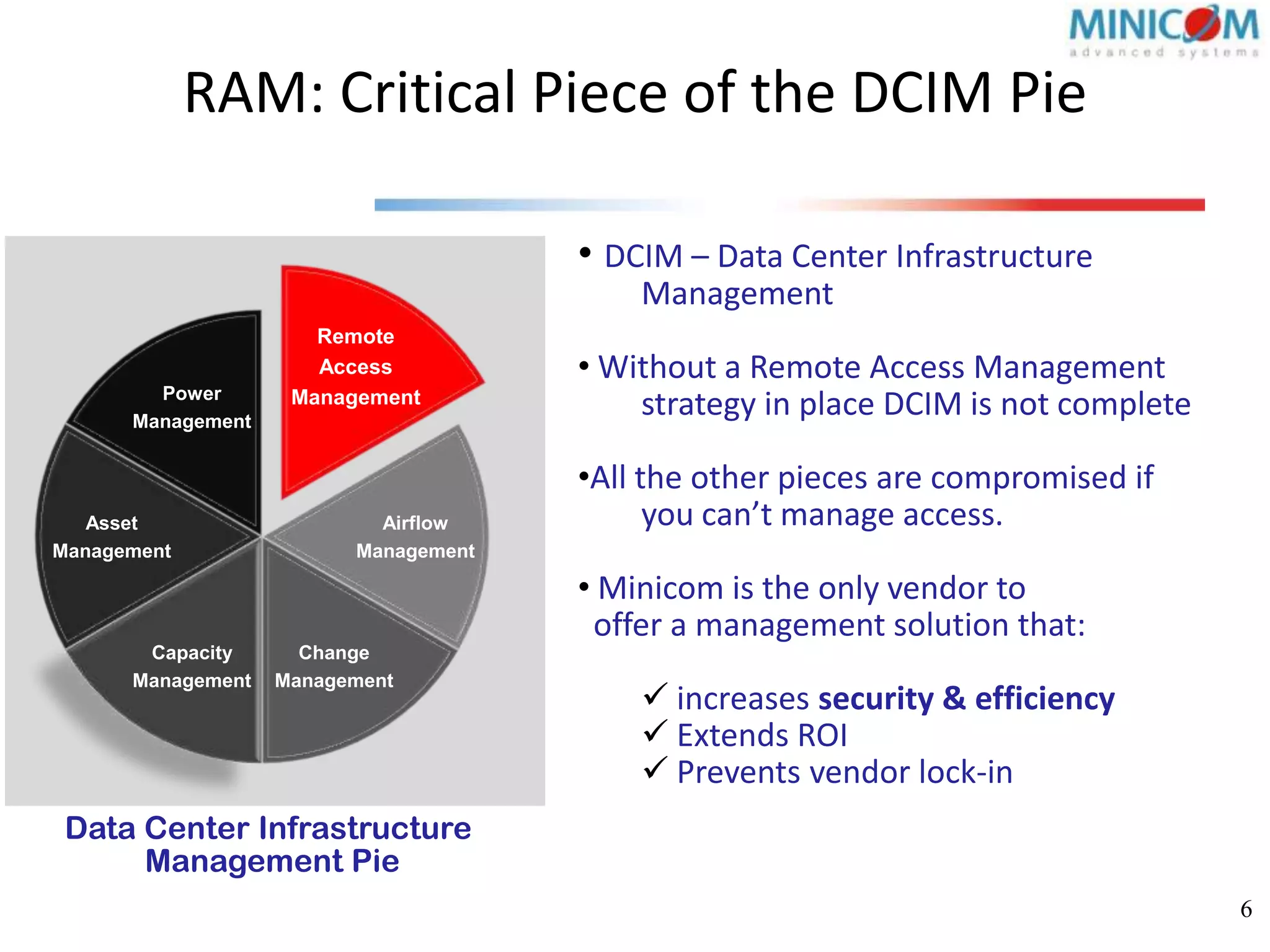
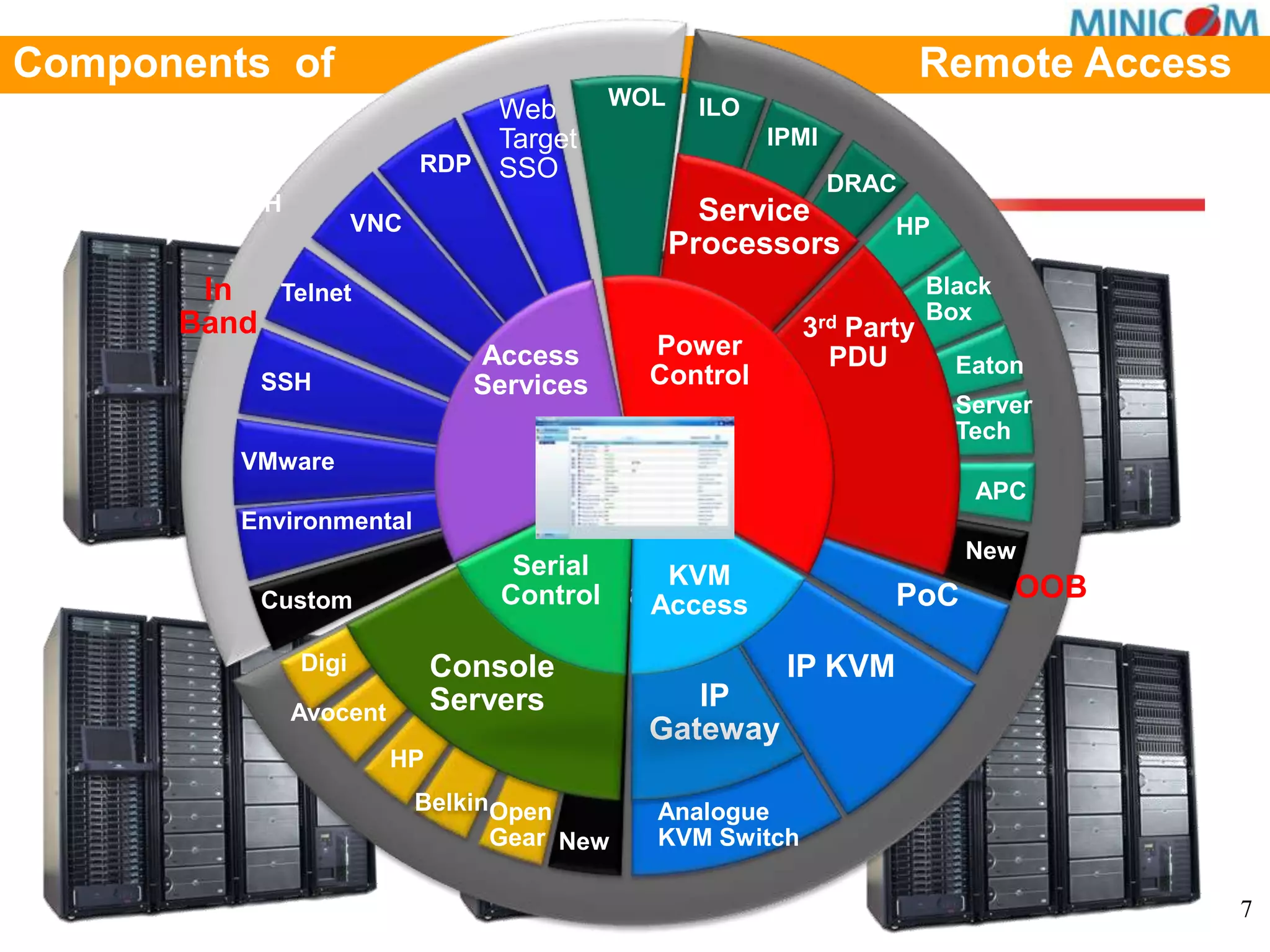
Minicom is a technology company with over 20 years of experience, focusing on remote access management solutions and high-end KVM products. Their offerings aim to centralize remote access, enhance security, improve operational efficiency, and reduce downtime in IT environments. The AccessITTM system simplifies management by consolidating access protocols, allowing for streamlined control of IT infrastructure.