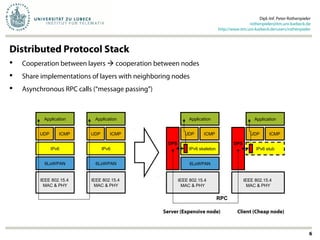
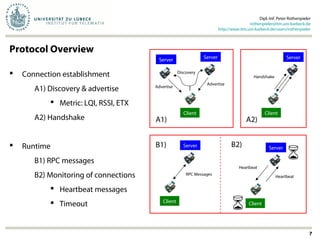
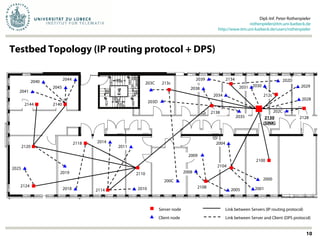
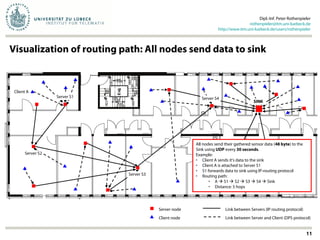
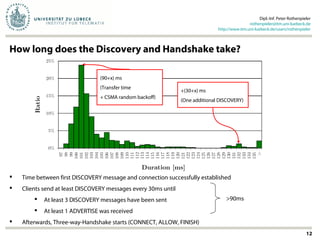
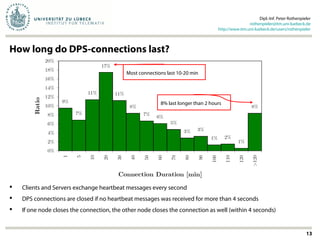
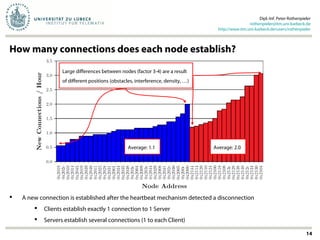
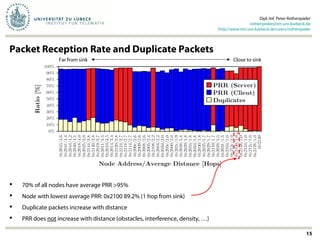
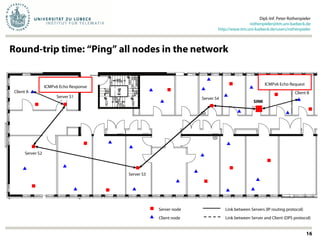
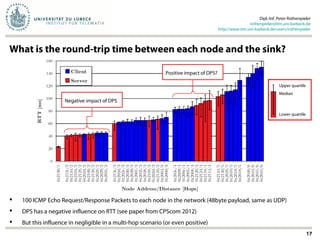
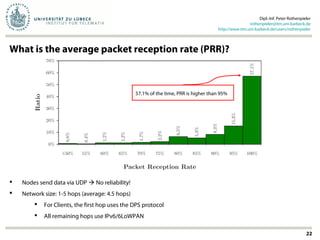
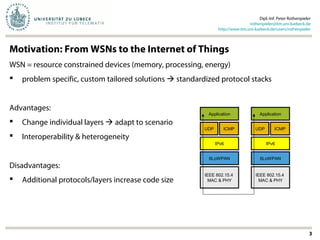
The document discusses the implementation and evaluation of distributed protocol stacks, particularly focusing on a protocol named DPS. It highlights the motivation behind using such stacks, their advantages and disadvantages, as well as performance metrics like connection establishment time and packet reception rates. The evaluation indicates that the DPS protocol does not negatively impact packet reception rates, although it may have a minor effect on round-trip time at shorter distances.
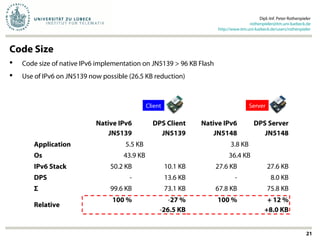
![Motivation: Code Size of 6LoWPAN & IPv6
Dipl.-Inf. Peter Rothenpieler
rothenpieler@itm.uni-luebeck.de
http://www.itm.uni-luebeck.de/users/rothenpieler
4
61%
50%
53%
26%
24%
0% 10% 20% 30% 40% 50% 60% 70% 80% 90% 100%
Contiki (JN5148, 128KB)
iSense (JN5148, 128KB)
Contiki (MSP430, 48KB)
Contiki (JN5139, 96KB)
iSense (JN5139, 96KB)
Platform
Code size [% of available program memory]
Source: Instant Contiki 2.6, Jennisense (07/2012), iSense SVN (04/2012)
Cheap*
(6.25€ / $8.30 / ¥50.90)
Expensive*
(8.95€ / $11.90 / ¥72.80) +43%
*Prices from Farnell/element14 (08/2013)
Not included:
OS, hardware / sensor drivers, …
Duty cycle protocol, security mechanisms, …
Application logic and protocols
IPv6 not possible on JN5139: IPv6+OS+Application = 99KB > 96KB available](https://image.slidesharecdn.com/reliabilityextensionsandmulti-hopevaluationofdistributedprotocolstacks-130807080929-phpapp01/85/Reliability-extensions-and-multi-hop-evaluation-of-distributed-protocol-stacks-4-320.jpg)