Regular expressions (regex) are patterns used to match character combinations in strings. This document introduces regex syntax and shows how to master regex from simple to complex patterns. It explains that regex can be used to avoid writing extensive code by concisely matching strings, and is supported by programming languages, tools like log analyzers, and databases. The document guides the reader through the regex syntax with examples to practice and eventually write their own complex regex patterns.






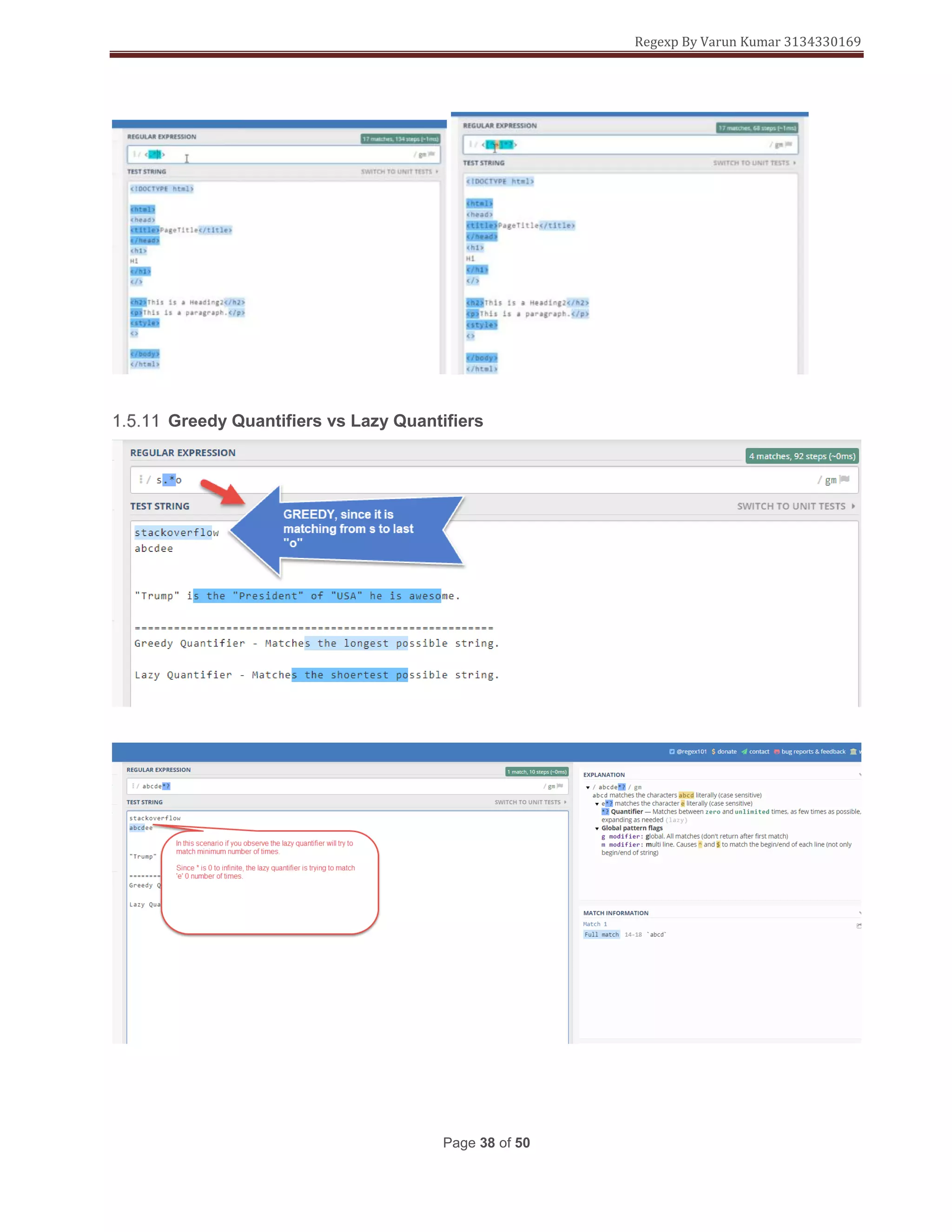
![Regexp By Varun Kumar 3134330169
Page 6 of 50
Regexby default is case sensitive.
:/Java/gm (Case sensitive)
:/Java/gmi (Case insensitive)
Regex starts searching from left to right
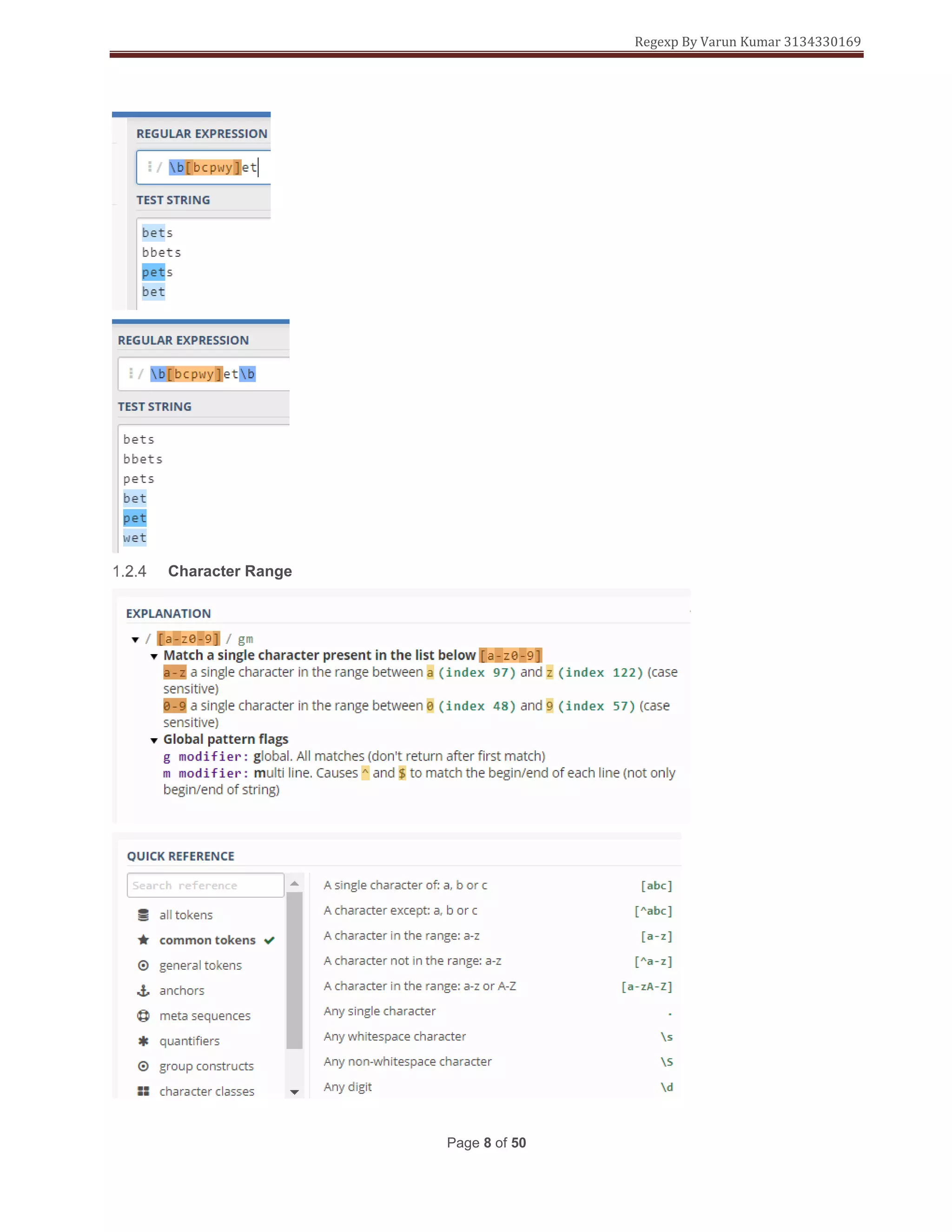
Character Classes
Character class are enclosed in [] brackets](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-7-2048.jpg)


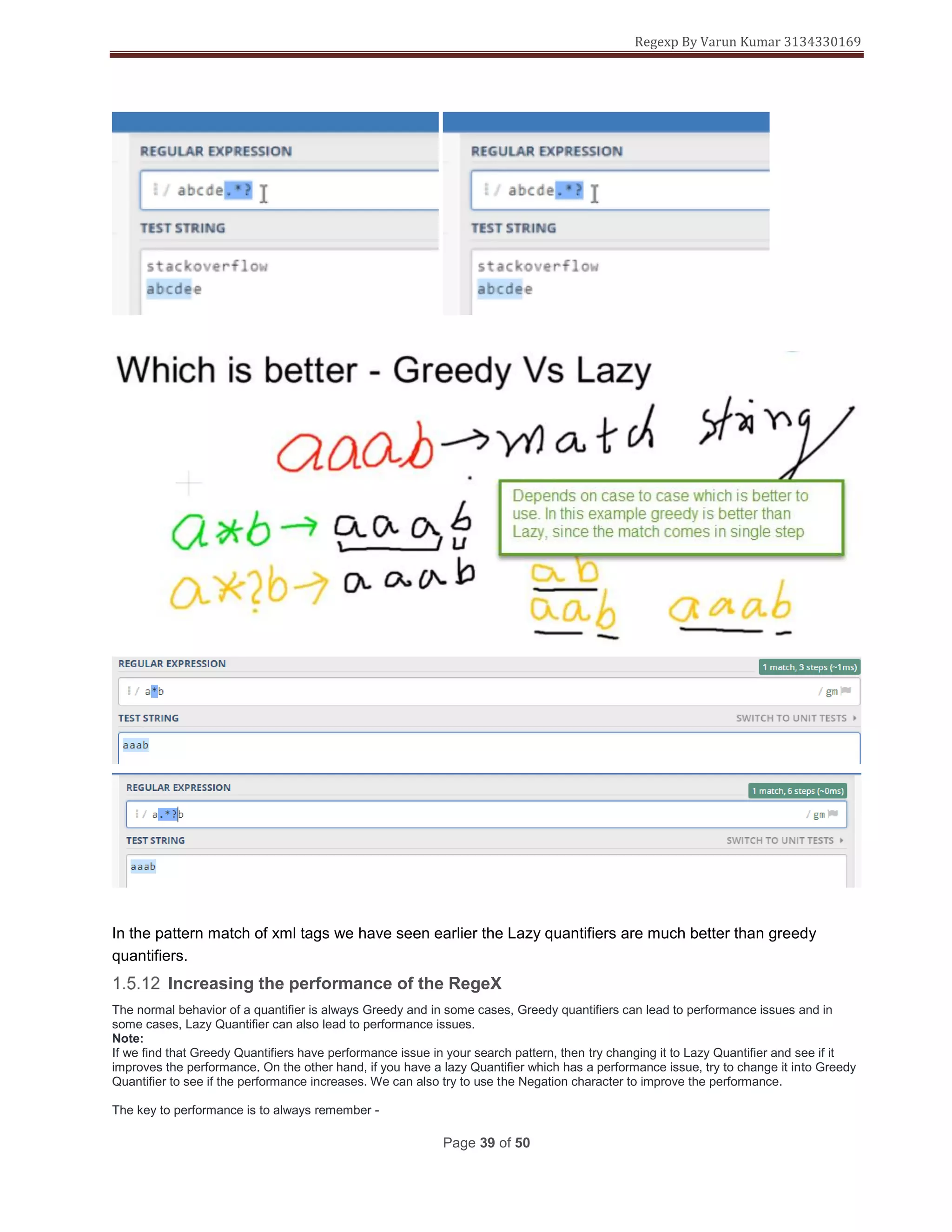
![Regexp By Varun Kumar 3134330169
Page 10 of 50
You needs to match the index when defining the character ranges you need to go from small to big
[A-z] This is correct
[a-Z] This is wrong.
Regex Live Example
<!DOCTYPE html>
<html>
<head>
<title>Testing Regular Expressions in HTML forms</title>
</head>
<body>
<h1>Test your Regular Expressions here</h1>
<fieldset>
<legend>Write your Regular expressions</legend>
<form>
<div>
<label for="display-name"> Prove that you are not a robot:
<span class="warning">*(Enter a single English capital letter.)</span>
</label>
<input type="text" id="display-name" name="ip-display"
pattern="[A-Z]"
title="Enter any single English capital Letter only"/>
</div>
<div>
<input type="submit" class="submit" value="Submit" />
</div>
</form>
</fieldset>
</body>
</html>](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-11-2048.jpg)

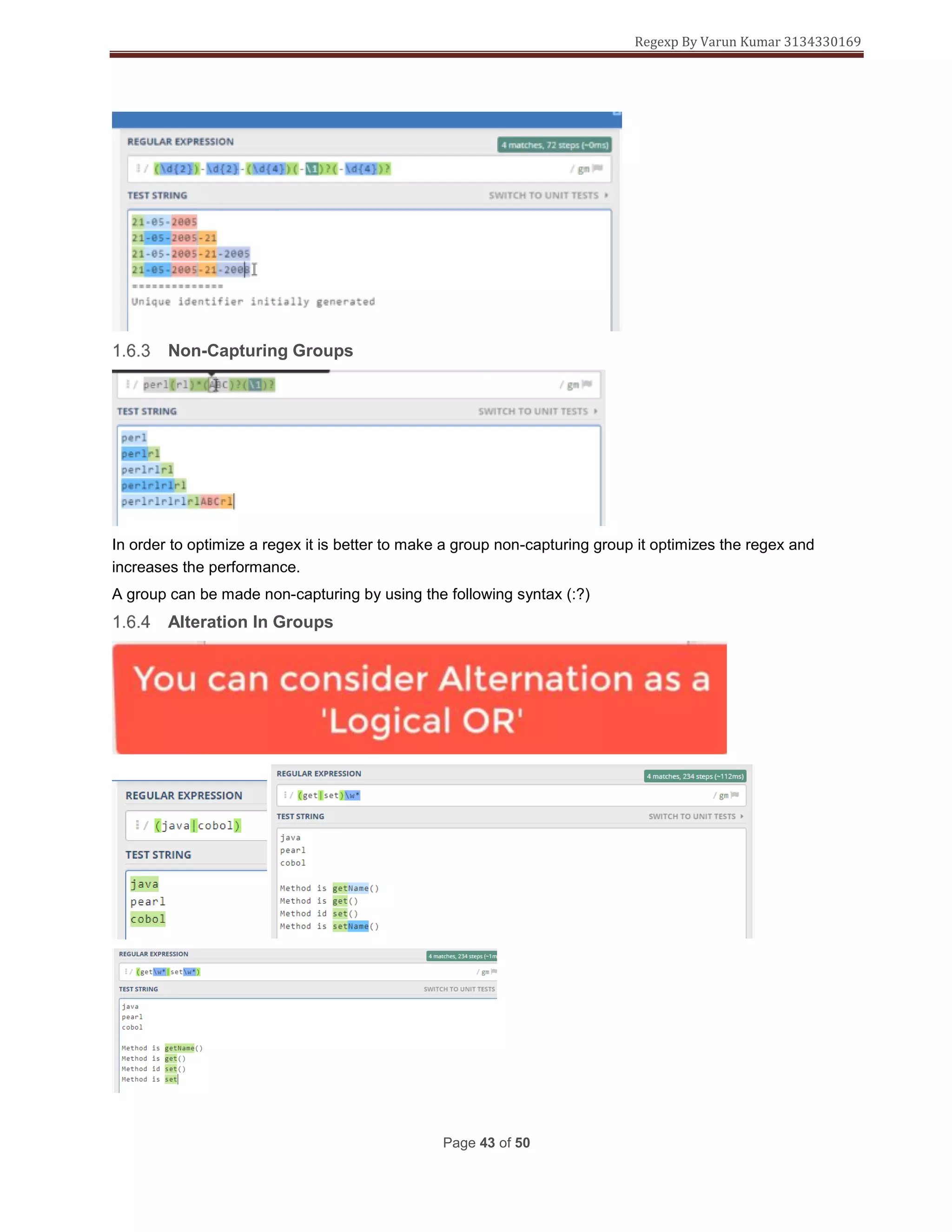
![Regexp By Varun Kumar 3134330169
Page 12 of 50
Negation Characters
Are represented with a ^ symbol inside [] brackets.
[^a-e] will match all characters except a-e
Example 1:-
The First Character should be any character except a comma(,)
The Second Character must be a comma(,)
The Third Character should be any character except a comma(,)
Example 2:-
The First Character must be a vowel(a,e,i,o,u)
The Second Character must be a English alphabet(it can be lowercase or
uppercase English alphabets)](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-13-2048.jpg)

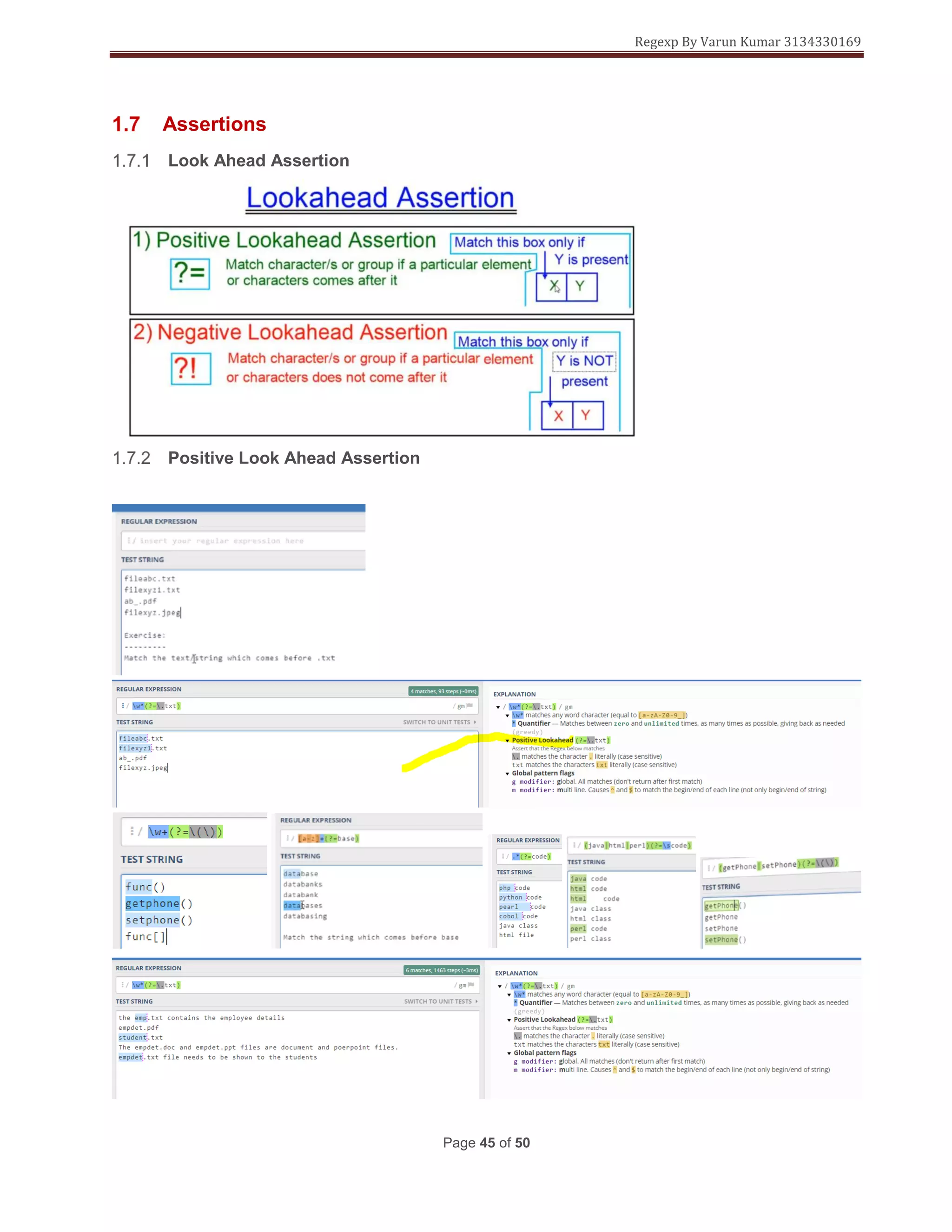
![Regexp By Varun Kumar 3134330169
Page 14 of 50
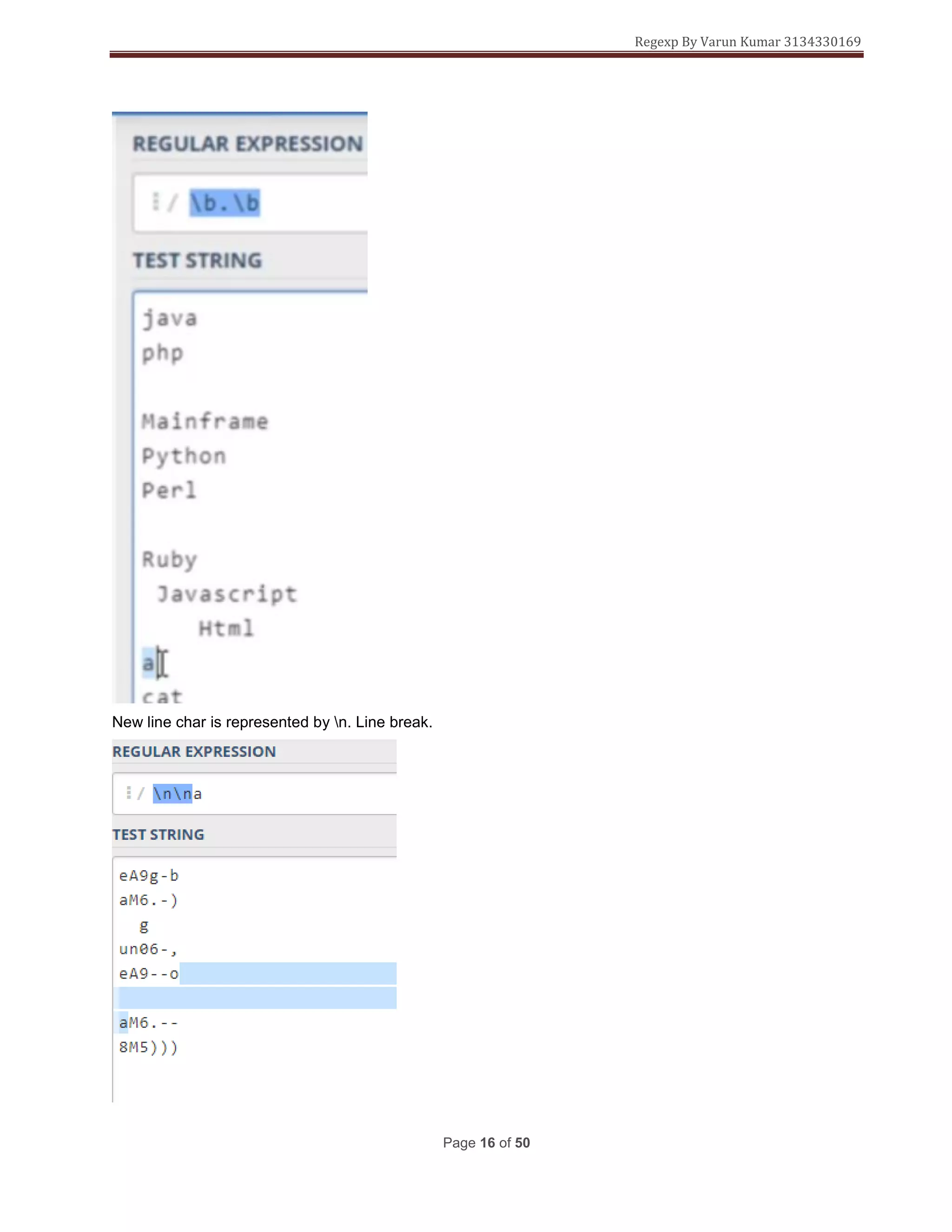
used to preceed a meta char or predefine character class.
^ negation character and used in anchors
^ Is also used for matching a boundary at the start of the line
$ Is used for matching a boundary at the end of the line
. used to match any character aprart from new line
? quantifiers
* quantifiers
+ quantifiers
{} quantifiers
| Alternation
() Grouping
[] Ranges
= Assertions (look ahead, look behind)
! Assertions (look ahead, look behind)](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-15-2048.jpg)













![Regexp By Varun Kumar 3134330169
Page 31 of 50
<!DOCTYPE html>
<html>
<head>
<title>Testing Regular Expressions in HTML forms</title>
</head>
<body>
<h1>Test your Regular Expressions here</h1>
<fieldset>
<legend>Write your Regular expressions</legend>
<form>
<div>
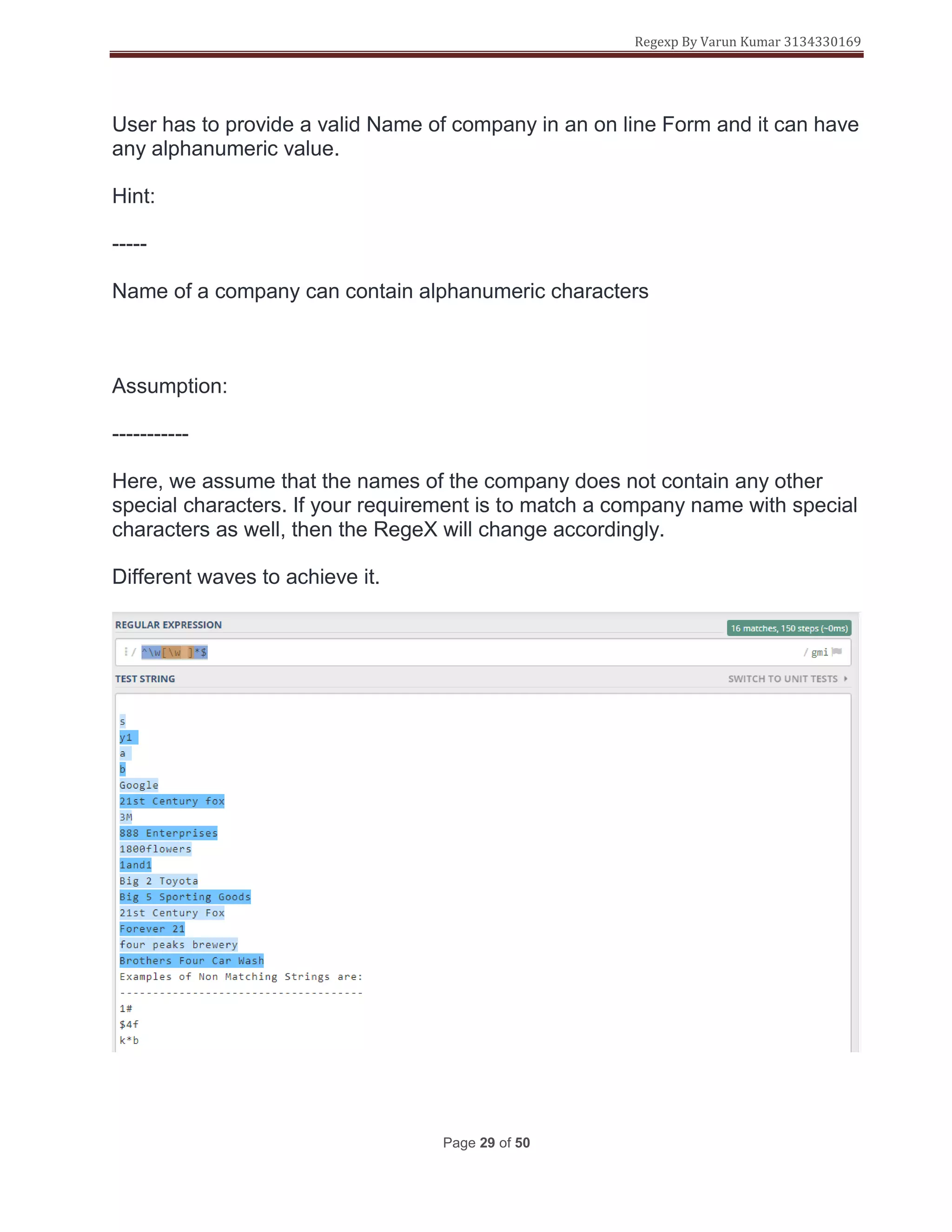
<label for="display-name"> Enter a company name here:
<span class="warning">*(Enter an alpha numeric character.)</span>
</label>
<input type="text" id="display-name" name="ip-display"
pattern="^[0-z][A-zds]*$"
title="Special Characters Not Allowed"/>
</div>
<div>
<input type="submit" class="submit" value="Submit" />
</div>
</form>
</fieldset>
</body>
</html>
Command explanation.](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-32-2048.jpg)












![Regexp By Varun Kumar 3134330169
Page 50 of 50
"email": "test@email.com",
"name": "Test Name",
"phone": "5555555",
"state": "REGION METROPOLITANA"
},
"packageDetails": {
"currency": "CLP",
"orderedProduct": "501180",
"packageDesc": "Desc",
"packageId": "TEST1234L1",
"weight": 10,
"weightUom": "G"
}
}
]
}
]
}
Match "shipments": [ from the payload](https://image.slidesharecdn.com/regularexpressions-181225013905/75/Regular-expressions-51-2048.jpg)