Red Hat, CentOS, Fedora 2019
•
0 likes•640 views
IBM acquired Red Hat Red Hat logo changed after 20 years Red Hat Enterprise Linux 8 List of New Features of RHEL 8 CentOS 8 Released CentOS released new midstream called CentOS Stream Fedora 31 Released New Fedora spins New Features of Fedora 31
Report
Share
Report
Share
Download to read offline
Recommended
Linux Security and How Web Browser Sandboxes Really Work (NDC Oslo 2017)

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers.
However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context. This is the sandbox used in the Vivaldi, Brave, Chrome and Opera browsers among others. The Chromium Sandbox has a very platform specific implementation, using the platform APIs available to construct it. In this talk we will describe the requirements of the Chromium Sandbox in detail and go through how the Linux implementation fulfills these requirements.
Linux Security and How Web Browser Sandboxes Really Work (Security Researcher...

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers. However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context.
This presentation goes more in depth on some key points from the NDC (2017) presentation.
Explorando Go em Ambiente Embarcado

Golang é uma linguagem fantástica para se desenvolver aplicações e um fator a ser explorado é o seu uso em dispositivos IoT. A linguagem já conta com diversas ferramentas de cross-compile, alguns pacotes experimentais de comunicação baixo nível e diversos projetos relacionados a hardware.
Linux Security and Hardening, 40 Tips 2019

Linux Security and Hardening
Version 2019
System Security
Kernel Security and Hardening
Physical Security
Password Policies and Security
Auto Logout
Disks and Partitions Security
Disk Encryption Guide
Disk Quota and Space Management
Anti-virus
Rootkit Detection Tools
Security Audit Tools
Host-based Intrusion Detection System
Log and Log Management
Network Security
NTP Service
Firewall
SSH Security
Bootloader Security
Authen Free Bsd6 2

1. The document discusses configuring internet authentication and WiFi for FreeBSD 6.2. It involves compiling the FreeBSD kernel to include authentication modules, setting up various services like Apache, MySQL, FreeRADIUS, and Chillispot.
2. Configuration steps include enabling firewall, NAT, and proxy options in the kernel, installing LAMP and SSL modules, and configuring FreeRADIUS for authentication using MySQL with users added to the database.
3. Additional services like Squid and MRTG are also configured for monitoring network traffic and authentication logs. The document provides commands and configuration files needed to set up this authentication infrastructure on FreeBSD 6.2.
Алексей Старов - Как проводить киберраследования?

«Cybercrime» является особым направлением в области компьютерной безопасности и приватности. Это направление объединяет научные работы, которые исследуют различные сценарии атак или мошенничества, анализируют вредоносные экосистемы, обнаруживают злоумышленников и изучает их методы с целью разработки эффективных мер противодействия. В текущем докладе будут предоставлены рекомендации о том, как проводить киберрасследования, основываясь на примерах из наших работ и статей. Например, я расскажу о нашем масштабном исследовании вредоносных веб-оболочек и как мы смогли обнаружить жертв и нападающих по всему земному шару, а так же о том, как мы использовали навыки социальной инженерии, чтобы исследовать экосистему мошеннической технической поддержки, и многое другое. Моя цель состоит в том, чтобы заинтересовать научных исследователей и других представителей области ИБ в работе по направлению “Cybercrime”, в поиске различных путей предотвращения и расследования киберпреступлений. А также, показать, что подобные полезные исследования не всегда требует огромных ресурсов и сотрудничеств. Формат доклада: разговор в виде легкого семинара с элементами коллективного мозгового штурма (ноутбук не требуется). Мы рассмотрим 3 урока, из каждого выделяя полезные методы, инструменты и навыки. Язык: русский (с элементами английского).
Pursue the Attackers – Identify and Investigate Lateral Movement Based on Beh...

The document discusses methods for identifying and investigating lateral movement by attackers during security incidents. It describes common tools and techniques used by attackers during different stages of an advanced persistent threat (APT) incident, including initial investigation, internal reconnaissance, spreading infection, and deleting evidence. The document analyzes logs and commands from past APT attacks to identify patterns in attacker behavior that can help with incident response. It notes that default system logs often do not provide enough information, so additional logging of events, processes, and network connections may be needed to fully trace attacker activities within a target network.
securing_syslog_onFreeBSD

The document discusses securing syslog logging on FreeBSD systems. It introduces syslog, its insecurities, and describes implementing digital signatures using an extension called syslog-sign. Syslog-sign calculates hashes of messages and stores signatures to assure integrity and detect any modifications. The implementation modifies the syslog daemon to generate signatures without other configuration. Verification can then validate log file contents offline.
Recommended
Linux Security and How Web Browser Sandboxes Really Work (NDC Oslo 2017)

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers.
However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context. This is the sandbox used in the Vivaldi, Brave, Chrome and Opera browsers among others. The Chromium Sandbox has a very platform specific implementation, using the platform APIs available to construct it. In this talk we will describe the requirements of the Chromium Sandbox in detail and go through how the Linux implementation fulfills these requirements.
Linux Security and How Web Browser Sandboxes Really Work (Security Researcher...

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers. However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context.
This presentation goes more in depth on some key points from the NDC (2017) presentation.
Explorando Go em Ambiente Embarcado

Golang é uma linguagem fantástica para se desenvolver aplicações e um fator a ser explorado é o seu uso em dispositivos IoT. A linguagem já conta com diversas ferramentas de cross-compile, alguns pacotes experimentais de comunicação baixo nível e diversos projetos relacionados a hardware.
Linux Security and Hardening, 40 Tips 2019

Linux Security and Hardening
Version 2019
System Security
Kernel Security and Hardening
Physical Security
Password Policies and Security
Auto Logout
Disks and Partitions Security
Disk Encryption Guide
Disk Quota and Space Management
Anti-virus
Rootkit Detection Tools
Security Audit Tools
Host-based Intrusion Detection System
Log and Log Management
Network Security
NTP Service
Firewall
SSH Security
Bootloader Security
Authen Free Bsd6 2

1. The document discusses configuring internet authentication and WiFi for FreeBSD 6.2. It involves compiling the FreeBSD kernel to include authentication modules, setting up various services like Apache, MySQL, FreeRADIUS, and Chillispot.
2. Configuration steps include enabling firewall, NAT, and proxy options in the kernel, installing LAMP and SSL modules, and configuring FreeRADIUS for authentication using MySQL with users added to the database.
3. Additional services like Squid and MRTG are also configured for monitoring network traffic and authentication logs. The document provides commands and configuration files needed to set up this authentication infrastructure on FreeBSD 6.2.
Алексей Старов - Как проводить киберраследования?

«Cybercrime» является особым направлением в области компьютерной безопасности и приватности. Это направление объединяет научные работы, которые исследуют различные сценарии атак или мошенничества, анализируют вредоносные экосистемы, обнаруживают злоумышленников и изучает их методы с целью разработки эффективных мер противодействия. В текущем докладе будут предоставлены рекомендации о том, как проводить киберрасследования, основываясь на примерах из наших работ и статей. Например, я расскажу о нашем масштабном исследовании вредоносных веб-оболочек и как мы смогли обнаружить жертв и нападающих по всему земному шару, а так же о том, как мы использовали навыки социальной инженерии, чтобы исследовать экосистему мошеннической технической поддержки, и многое другое. Моя цель состоит в том, чтобы заинтересовать научных исследователей и других представителей области ИБ в работе по направлению “Cybercrime”, в поиске различных путей предотвращения и расследования киберпреступлений. А также, показать, что подобные полезные исследования не всегда требует огромных ресурсов и сотрудничеств. Формат доклада: разговор в виде легкого семинара с элементами коллективного мозгового штурма (ноутбук не требуется). Мы рассмотрим 3 урока, из каждого выделяя полезные методы, инструменты и навыки. Язык: русский (с элементами английского).
Pursue the Attackers – Identify and Investigate Lateral Movement Based on Beh...

The document discusses methods for identifying and investigating lateral movement by attackers during security incidents. It describes common tools and techniques used by attackers during different stages of an advanced persistent threat (APT) incident, including initial investigation, internal reconnaissance, spreading infection, and deleting evidence. The document analyzes logs and commands from past APT attacks to identify patterns in attacker behavior that can help with incident response. It notes that default system logs often do not provide enough information, so additional logging of events, processes, and network connections may be needed to fully trace attacker activities within a target network.
securing_syslog_onFreeBSD

The document discusses securing syslog logging on FreeBSD systems. It introduces syslog, its insecurities, and describes implementing digital signatures using an extension called syslog-sign. Syslog-sign calculates hashes of messages and stores signatures to assure integrity and detect any modifications. The implementation modifies the syslog daemon to generate signatures without other configuration. Verification can then validate log file contents offline.
Linux Security APIs and the Chromium Sandbox (SwedenCpp Meetup 2017)

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers. However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context.
This presentation goes more in depth on some key points from the NDC (2017) presentation.
Lightweight development (Lightning talk)

This document discusses lightweight development approaches for running local web servers and services. It describes using MAMP and Vagrant in the past but prefers running everything in the foreground locally using tools like httpd, MySQL, memcached and Solr. The ideal solution runs services for each project in the foreground and uses easily installable tools like Homebrew. Automating this is achieved with a Procfile and Foreman to manage the process-based applications.
Bringing-it-all-together-overview-of-rpm-packaging-in-fedora

This document discusses RPM packaging in Fedora. It begins by explaining why packaging is important, noting that it automates software installation and management while preventing errors. It then describes RPM, the package format used in Fedora and other distributions. The document outlines the RPM build process using tools like rpmbuild and spec files. It also introduces services like Koji, which builds RPMs, distribution git repositories for packages, Bodhi for release management, and COPR for alternative builds. It concludes by recommending ways for readers to get involved in Fedora packaging.
Magento and Continuous Integration - Damian Luszczymak

Magento and Continuous Integration, what you can do ! How you can use CI Systems with Magento and how to start.
I show you one possible way to introduce this in small company's or even for your private project without much money.
Pharo IoT Installation Improvements and Continuous Integration

Presented at Pharo Days 2019, Lille, France.
Now you can start with Pharo IoT runtime (PharoThings, TelePharo, ARM VM) in a Raspberry from scratch in less than 10 minutes or in less than 1 minute if your Raspberry Pi has Raspbian already installed. And in less than 1 minute you can run Pharo IoT IDE in your Linux, Window or Mac OSX.
How did we do this?? The answers are in this presentation :)
Take your Raspberry Pi and start now: get.pharoiot.org
PHARO IoT: Installation Improvements and Continuous Integration

1. The document discusses improvements made to the installation process and continuous integration of Pharo IoT.
2. Previously, installing Pharo IoT manually took many steps and was difficult for newcomers. The process has been simplified to take less than 10 minutes with pre-packaged files.
3. Continuous integration was added using Travis CI to automatically build documentation, load libraries, and release packaged files with each code change. This makes the process transparent and easy to contribute to.
PHP Development Tools

Why I like PHPStorm
Advantages of Using Docker
Client, Docker Host, Registry
Docker Usage
Solr Docker File
Every Day Docker Commands
Docker Search
One Line Scripts
Portainer
Kinematic
Docker Compose
Grafana
Coding style guide
PHPCS/MD
Documentation Rules
Xdebug
Postman
Linux security quick reference guide

This document provides guidance on securing Linux systems through various configuration and monitoring techniques. It discusses:
- Regularly auditing systems for unauthorized permissions and removing unnecessary setuid/setgid permissions.
- Locating and removing world-writable and unowned files, which could be altered by intruders.
- Using attributes like append-only and immutable to prevent log files from being deleted or binaries from being replaced.
- Configuring options like nosuid in /etc/fstab to restrict permissions on partitions.
Installing nagios core_from_source

This document provides instructions for installing Nagios Core and Nagios Plugins from source on CentOS and Ubuntu servers. It describes downloading the necessary tarballs, adding the Nagios user and group, compiling and installing Nagios Core and Plugins, configuring Nagios as a service, and accessing the Nagios web interface. Key steps include configuring with the appropriate options, making and installing, adding the nagios user, installing plugins, and enabling Nagios and the web server to start on boot.
Perl on embedded Linux with Buildroot

Buildroot (www.buildroot.net) is a tool for building small embedded linux system.
For example : Kernel + Busybox + Perl + Dancer2 ~= 60 MB
Buildroot could create also Qemu Virtual Machine image with the same footprint.
Demo with a Olimex iMX233 board (45€).
Web Server Free Bsd

The document provides instructions for updating the FreeBSD 7.2 ports tree on a WebServer. The following steps are outlined:
1. Log in as the user "sermpan" and su to root.
2. Extract a backup of the ports tree files from /backups/distfiles72.tar.
3. Install and clean the cvsup port to update the ports tree files.
اسلاید اول جلسه دوم کلاس پایتون برای هکرهای قانونی

This document introduces Python and discusses why it is useful for ethical hacking and information security work. It provides a brief history of Python, describing its creation and major versions. It outlines Python's advantages such as being open source, cross-platform, having a rich library of tools, and being suitable for rapid prototyping. It also discusses how to set up Python on major operating systems like Linux, Mac OS, and Windows.
Efficient System Monitoring in Cloud Native Environments

This document discusses efficient system monitoring in cloud native environments using eBPF. It provides an overview of eBPF and how it can be used for monitoring applications like Prometheus. Specific topics covered include BPF, Linux kernel tracing using kprobes and tracepoints, eBPF maps and programs, and an example Prometheus exporter that leverages eBPF to export metrics.
Deployment tales

The document discusses different eras of software deployment:
1. The shared hosting era involved editing files, uploading, and refreshing the browser frequently with many issues.
2. The dedicated server era used Linux distros like Debian and involved more command line work like sudo and vim but still had restart issues.
3. The cloud era saw the rise of tools like Capistrano, Vlad, and Mina to automate deploys but still had restart problems.
4. Every era had issues with daemons not running, crashes, and bugs after restarts due to a lack of process supervision. Runit and systemd help address this by making applications into supervised services.
Deployment tales

The document discusses different eras of software deployment:
1. The shared hosting era involved editing files, uploading, and refreshing the browser frequently with many issues.
2. The dedicated server era used Linux distros like Debian and involved more command line work like sudo and vim but still had restart issues.
3. The cloud era saw the rise of tools like Capistrano, Vlad, and Mina to automate deployments but restarts were still an issue.
4. No matter the era, issues with daemons not persisting through restarts and bugs were common. Solutions like init scripts, Passenger, and systemd helped but Runit provides even better service supervision and restart capabilities when
Red Hat Linux 5 Hardening Tips - National Security Agency

This document provides a summary of tips for hardening the default installation of Red Hat Enterprise Linux 5. It recommends securing physical access to servers, minimizing installed software, regularly updating systems, disabling unnecessary services, removing SUID/SGID permissions and X Windows, configuring firewalls and SELinux, and securing SSH access. The full document provides more detailed guidance for implementing these security configurations.
PHP QA Tools

Doing Quality Assurance in PHP projects sometimes looks like a dark art! Picking the right tools, making all tools work together, analysing your code and even then deliver all the required features of the software project can be quite challenging.
This talks aims to help lowering the entry barrier for doing QA on your project, sharing the experience, knowledge and some tricks that brings QA back from the dark arts to the every day of a PHP programmer.
We will review tools like Jenkins, PHPUnit, phpcs, pdepend, phpcpd, etc and how we can chain them together to make sure we are building a great software.
Installing php 7.4 Nginx Laravel 7.x on Centos 8

This document provides instructions over 14 steps to install PHP 7.4, Nginx 1.14, PHP-FPM, and Laravel 7.15 on CentOS 8. It begins by enabling EPEL and Remi repositories to access the latest PHP version. Nginx, PHP, and other packages are then installed. Laravel is created and configured in the Nginx server block. Security contexts are set and the Laravel site can be accessed via browser.
Groß steuert klein - Wie lässt sich ein Arduino steuern?

Der Arduino ist ideal, um analoge und digitale Sensordaten zu lesen und um Aktoren wie LEDs zu steuern. Zudem werden eine Vielzahl von Bibliotheken angeboten. Möchte man ihn aber als IoT-‚Ding‘ ins Internet bringen oder steuern, ergeben sich unterschiedliche Möglichkeiten. In meinem Vortrag zeige ich hierzu verschiedene Wege. Zunächst, wie sich der Arduino mithilfe von Firmata und einem Computer steuern lässt. Hierzu existieren Bibliothen, die das Firmata-Protokoll für verschiedene Programmiersprachen implementieren. Es werden zu Java, JavaScript und Go Beispiele gezeigt. Die serielle Schnittstelle ist eine weitere Möglichkeit, bei der ein Arduino entweder mit einem Computer oder Raspberry Pi direkt kommunizieren kann. Um hingegen mehrere Arduinos mit dem Raspberry Pi anzusprechen, eignet sich ein Datenbus-Protokoll. Der Raspberry Pi bietet hierzu SPI und I2C an, deren Unterschiede aufgezeigt werden. Zu den jeweiligen Arten werden praxisnahe Demos und Codebeispiele gezeigt.
socradar-q1-2024-aviation-industry-report.pdf

SOCRadar's Aviation Industry Q1 Incident Report is out now!
The aviation industry has always been a prime target for cybercriminals due to its critical infrastructure and high stakes. In the first quarter of 2024, the sector faced an alarming surge in cybersecurity threats, revealing its vulnerabilities and the relentless sophistication of cyber attackers.
SOCRadar’s Aviation Industry, Quarterly Incident Report, provides an in-depth analysis of these threats, detected and examined through our extensive monitoring of hacker forums, Telegram channels, and dark web platforms.
Empowering Growth with Best Software Development Company in Noida - Deuglo

Do you want Software for your Business? Visit Deuglo
Deuglo has top Software Developers in India. They are experts in software development and help design and create custom Software solutions.
Deuglo follows seven steps methods for delivering their services to their customers. They called it the Software development life cycle process (SDLC).
Requirement — Collecting the Requirements is the first Phase in the SSLC process.
Feasibility Study — after completing the requirement process they move to the design phase.
Design — in this phase, they start designing the software.
Coding — when designing is completed, the developers start coding for the software.
Testing — in this phase when the coding of the software is done the testing team will start testing.
Installation — after completion of testing, the application opens to the live server and launches!
Maintenance — after completing the software development, customers start using the software.
More Related Content
Similar to Red Hat, CentOS, Fedora 2019
Linux Security APIs and the Chromium Sandbox (SwedenCpp Meetup 2017)

The Linux Security and Isolation APIs have become the basis of some of the most useful features server-side, providing the isolation required for efficient containers. However, these APIs also form the basis of the Chromium Sandbox on Linux, and we will study them in that context.
This presentation goes more in depth on some key points from the NDC (2017) presentation.
Lightweight development (Lightning talk)

This document discusses lightweight development approaches for running local web servers and services. It describes using MAMP and Vagrant in the past but prefers running everything in the foreground locally using tools like httpd, MySQL, memcached and Solr. The ideal solution runs services for each project in the foreground and uses easily installable tools like Homebrew. Automating this is achieved with a Procfile and Foreman to manage the process-based applications.
Bringing-it-all-together-overview-of-rpm-packaging-in-fedora

This document discusses RPM packaging in Fedora. It begins by explaining why packaging is important, noting that it automates software installation and management while preventing errors. It then describes RPM, the package format used in Fedora and other distributions. The document outlines the RPM build process using tools like rpmbuild and spec files. It also introduces services like Koji, which builds RPMs, distribution git repositories for packages, Bodhi for release management, and COPR for alternative builds. It concludes by recommending ways for readers to get involved in Fedora packaging.
Magento and Continuous Integration - Damian Luszczymak

Magento and Continuous Integration, what you can do ! How you can use CI Systems with Magento and how to start.
I show you one possible way to introduce this in small company's or even for your private project without much money.
Pharo IoT Installation Improvements and Continuous Integration

Presented at Pharo Days 2019, Lille, France.
Now you can start with Pharo IoT runtime (PharoThings, TelePharo, ARM VM) in a Raspberry from scratch in less than 10 minutes or in less than 1 minute if your Raspberry Pi has Raspbian already installed. And in less than 1 minute you can run Pharo IoT IDE in your Linux, Window or Mac OSX.
How did we do this?? The answers are in this presentation :)
Take your Raspberry Pi and start now: get.pharoiot.org
PHARO IoT: Installation Improvements and Continuous Integration

1. The document discusses improvements made to the installation process and continuous integration of Pharo IoT.
2. Previously, installing Pharo IoT manually took many steps and was difficult for newcomers. The process has been simplified to take less than 10 minutes with pre-packaged files.
3. Continuous integration was added using Travis CI to automatically build documentation, load libraries, and release packaged files with each code change. This makes the process transparent and easy to contribute to.
PHP Development Tools

Why I like PHPStorm
Advantages of Using Docker
Client, Docker Host, Registry
Docker Usage
Solr Docker File
Every Day Docker Commands
Docker Search
One Line Scripts
Portainer
Kinematic
Docker Compose
Grafana
Coding style guide
PHPCS/MD
Documentation Rules
Xdebug
Postman
Linux security quick reference guide

This document provides guidance on securing Linux systems through various configuration and monitoring techniques. It discusses:
- Regularly auditing systems for unauthorized permissions and removing unnecessary setuid/setgid permissions.
- Locating and removing world-writable and unowned files, which could be altered by intruders.
- Using attributes like append-only and immutable to prevent log files from being deleted or binaries from being replaced.
- Configuring options like nosuid in /etc/fstab to restrict permissions on partitions.
Installing nagios core_from_source

This document provides instructions for installing Nagios Core and Nagios Plugins from source on CentOS and Ubuntu servers. It describes downloading the necessary tarballs, adding the Nagios user and group, compiling and installing Nagios Core and Plugins, configuring Nagios as a service, and accessing the Nagios web interface. Key steps include configuring with the appropriate options, making and installing, adding the nagios user, installing plugins, and enabling Nagios and the web server to start on boot.
Perl on embedded Linux with Buildroot

Buildroot (www.buildroot.net) is a tool for building small embedded linux system.
For example : Kernel + Busybox + Perl + Dancer2 ~= 60 MB
Buildroot could create also Qemu Virtual Machine image with the same footprint.
Demo with a Olimex iMX233 board (45€).
Web Server Free Bsd

The document provides instructions for updating the FreeBSD 7.2 ports tree on a WebServer. The following steps are outlined:
1. Log in as the user "sermpan" and su to root.
2. Extract a backup of the ports tree files from /backups/distfiles72.tar.
3. Install and clean the cvsup port to update the ports tree files.
اسلاید اول جلسه دوم کلاس پایتون برای هکرهای قانونی

This document introduces Python and discusses why it is useful for ethical hacking and information security work. It provides a brief history of Python, describing its creation and major versions. It outlines Python's advantages such as being open source, cross-platform, having a rich library of tools, and being suitable for rapid prototyping. It also discusses how to set up Python on major operating systems like Linux, Mac OS, and Windows.
Efficient System Monitoring in Cloud Native Environments

This document discusses efficient system monitoring in cloud native environments using eBPF. It provides an overview of eBPF and how it can be used for monitoring applications like Prometheus. Specific topics covered include BPF, Linux kernel tracing using kprobes and tracepoints, eBPF maps and programs, and an example Prometheus exporter that leverages eBPF to export metrics.
Deployment tales

The document discusses different eras of software deployment:
1. The shared hosting era involved editing files, uploading, and refreshing the browser frequently with many issues.
2. The dedicated server era used Linux distros like Debian and involved more command line work like sudo and vim but still had restart issues.
3. The cloud era saw the rise of tools like Capistrano, Vlad, and Mina to automate deploys but still had restart problems.
4. Every era had issues with daemons not running, crashes, and bugs after restarts due to a lack of process supervision. Runit and systemd help address this by making applications into supervised services.
Deployment tales

The document discusses different eras of software deployment:
1. The shared hosting era involved editing files, uploading, and refreshing the browser frequently with many issues.
2. The dedicated server era used Linux distros like Debian and involved more command line work like sudo and vim but still had restart issues.
3. The cloud era saw the rise of tools like Capistrano, Vlad, and Mina to automate deployments but restarts were still an issue.
4. No matter the era, issues with daemons not persisting through restarts and bugs were common. Solutions like init scripts, Passenger, and systemd helped but Runit provides even better service supervision and restart capabilities when
Red Hat Linux 5 Hardening Tips - National Security Agency

This document provides a summary of tips for hardening the default installation of Red Hat Enterprise Linux 5. It recommends securing physical access to servers, minimizing installed software, regularly updating systems, disabling unnecessary services, removing SUID/SGID permissions and X Windows, configuring firewalls and SELinux, and securing SSH access. The full document provides more detailed guidance for implementing these security configurations.
PHP QA Tools

Doing Quality Assurance in PHP projects sometimes looks like a dark art! Picking the right tools, making all tools work together, analysing your code and even then deliver all the required features of the software project can be quite challenging.
This talks aims to help lowering the entry barrier for doing QA on your project, sharing the experience, knowledge and some tricks that brings QA back from the dark arts to the every day of a PHP programmer.
We will review tools like Jenkins, PHPUnit, phpcs, pdepend, phpcpd, etc and how we can chain them together to make sure we are building a great software.
Installing php 7.4 Nginx Laravel 7.x on Centos 8

This document provides instructions over 14 steps to install PHP 7.4, Nginx 1.14, PHP-FPM, and Laravel 7.15 on CentOS 8. It begins by enabling EPEL and Remi repositories to access the latest PHP version. Nginx, PHP, and other packages are then installed. Laravel is created and configured in the Nginx server block. Security contexts are set and the Laravel site can be accessed via browser.
Groß steuert klein - Wie lässt sich ein Arduino steuern?

Der Arduino ist ideal, um analoge und digitale Sensordaten zu lesen und um Aktoren wie LEDs zu steuern. Zudem werden eine Vielzahl von Bibliotheken angeboten. Möchte man ihn aber als IoT-‚Ding‘ ins Internet bringen oder steuern, ergeben sich unterschiedliche Möglichkeiten. In meinem Vortrag zeige ich hierzu verschiedene Wege. Zunächst, wie sich der Arduino mithilfe von Firmata und einem Computer steuern lässt. Hierzu existieren Bibliothen, die das Firmata-Protokoll für verschiedene Programmiersprachen implementieren. Es werden zu Java, JavaScript und Go Beispiele gezeigt. Die serielle Schnittstelle ist eine weitere Möglichkeit, bei der ein Arduino entweder mit einem Computer oder Raspberry Pi direkt kommunizieren kann. Um hingegen mehrere Arduinos mit dem Raspberry Pi anzusprechen, eignet sich ein Datenbus-Protokoll. Der Raspberry Pi bietet hierzu SPI und I2C an, deren Unterschiede aufgezeigt werden. Zu den jeweiligen Arten werden praxisnahe Demos und Codebeispiele gezeigt.
Similar to Red Hat, CentOS, Fedora 2019 (20)
Linux Security APIs and the Chromium Sandbox (SwedenCpp Meetup 2017)

Linux Security APIs and the Chromium Sandbox (SwedenCpp Meetup 2017)
Bringing-it-all-together-overview-of-rpm-packaging-in-fedora

Bringing-it-all-together-overview-of-rpm-packaging-in-fedora
Magento and Continuous Integration - Damian Luszczymak

Magento and Continuous Integration - Damian Luszczymak
Pharo IoT Installation Improvements and Continuous Integration

Pharo IoT Installation Improvements and Continuous Integration
PHARO IoT: Installation Improvements and Continuous Integration

PHARO IoT: Installation Improvements and Continuous Integration
اسلاید اول جلسه دوم کلاس پایتون برای هکرهای قانونی

اسلاید اول جلسه دوم کلاس پایتون برای هکرهای قانونی
Efficient System Monitoring in Cloud Native Environments

Efficient System Monitoring in Cloud Native Environments
Red Hat Linux 5 Hardening Tips - National Security Agency

Red Hat Linux 5 Hardening Tips - National Security Agency
Groß steuert klein - Wie lässt sich ein Arduino steuern?

Groß steuert klein - Wie lässt sich ein Arduino steuern?
Recently uploaded
socradar-q1-2024-aviation-industry-report.pdf

SOCRadar's Aviation Industry Q1 Incident Report is out now!
The aviation industry has always been a prime target for cybercriminals due to its critical infrastructure and high stakes. In the first quarter of 2024, the sector faced an alarming surge in cybersecurity threats, revealing its vulnerabilities and the relentless sophistication of cyber attackers.
SOCRadar’s Aviation Industry, Quarterly Incident Report, provides an in-depth analysis of these threats, detected and examined through our extensive monitoring of hacker forums, Telegram channels, and dark web platforms.
Empowering Growth with Best Software Development Company in Noida - Deuglo

Do you want Software for your Business? Visit Deuglo
Deuglo has top Software Developers in India. They are experts in software development and help design and create custom Software solutions.
Deuglo follows seven steps methods for delivering their services to their customers. They called it the Software development life cycle process (SDLC).
Requirement — Collecting the Requirements is the first Phase in the SSLC process.
Feasibility Study — after completing the requirement process they move to the design phase.
Design — in this phase, they start designing the software.
Coding — when designing is completed, the developers start coding for the software.
Testing — in this phase when the coding of the software is done the testing team will start testing.
Installation — after completion of testing, the application opens to the live server and launches!
Maintenance — after completing the software development, customers start using the software.
Enterprise Resource Planning System in Telangana

Enterprise Resource Planning System includes various modules that reduce any business's workload. Additionally, it organizes the workflows, which drives towards enhancing productivity. Here are a detailed explanation of the ERP modules. Going through the points will help you understand how the software is changing the work dynamics.
To know more details here: https://blogs.nyggs.com/nyggs/enterprise-resource-planning-erp-system-modules/
AI Fusion Buddy Review: Brand New, Groundbreaking Gemini-Powered AI App

AI Fusion Buddy Review: Brand New, Groundbreaking Gemini-Powered AI App
👉👉 Click Here To Get More Info 👇👇
https://sumonreview.com/ai-fusion-buddy-review
AI Fusion Buddy Review: Key Features
✅Create Stunning AI App Suite Fully Powered By Google's Latest AI technology, Gemini
✅Use Gemini to Build high-converting Converting Sales Video Scripts, ad copies, Trending Articles, blogs, etc.100% unique!
✅Create Ultra-HD graphics with a single keyword or phrase that commands 10x eyeballs!
✅Fully automated AI articles bulk generation!
✅Auto-post or schedule stunning AI content across all your accounts at once—WordPress, Facebook, LinkedIn, Blogger, and more.
✅With one keyword or URL, generate complete websites, landing pages, and more…
✅Automatically create & sell AI content, graphics, websites, landing pages, & all that gets you paid non-stop 24*7.
✅Pre-built High-Converting 100+ website Templates and 2000+ graphic templates logos, banners, and thumbnail images in Trending Niches.
✅Say goodbye to wasting time logging into multiple Chat GPT & AI Apps once & for all!
✅Save over $5000 per year and kick out dependency on third parties completely!
✅Brand New App: Not available anywhere else!
✅ Beginner-friendly!
✅ZERO upfront cost or any extra expenses
✅Risk-Free: 30-Day Money-Back Guarantee!
✅Commercial License included!
See My Other Reviews Article:
(1) AI Genie Review: https://sumonreview.com/ai-genie-review
(2) SocioWave Review: https://sumonreview.com/sociowave-review
(3) AI Partner & Profit Review: https://sumonreview.com/ai-partner-profit-review
(4) AI Ebook Suite Review: https://sumonreview.com/ai-ebook-suite-review
#AIFusionBuddyReview,
#AIFusionBuddyFeatures,
#AIFusionBuddyPricing,
#AIFusionBuddyProsandCons,
#AIFusionBuddyTutorial,
#AIFusionBuddyUserExperience
#AIFusionBuddyforBeginners,
#AIFusionBuddyBenefits,
#AIFusionBuddyComparison,
#AIFusionBuddyInstallation,
#AIFusionBuddyRefundPolicy,
#AIFusionBuddyDemo,
#AIFusionBuddyMaintenanceFees,
#AIFusionBuddyNewbieFriendly,
#WhatIsAIFusionBuddy?,
#HowDoesAIFusionBuddyWorks
SWEBOK and Education at FUSE Okinawa 2024

Takashi Kobayashi and Hironori Washizaki, "SWEBOK Guide and Future of SE Education," First International Symposium on the Future of Software Engineering (FUSE), June 3-6, 2024, Okinawa, Japan
UI5con 2024 - Boost Your Development Experience with UI5 Tooling Extensions

The UI5 tooling is the development and build tooling of UI5. It is built in a modular and extensible way so that it can be easily extended by your needs. This session will showcase various tooling extensions which can boost your development experience by far so that you can really work offline, transpile your code in your project to use even newer versions of EcmaScript (than 2022 which is supported right now by the UI5 tooling), consume any npm package of your choice in your project, using different kind of proxies, and even stitching UI5 projects during development together to mimic your target environment.
DDS-Security 1.2 - What's New? Stronger security for long-running systems

DDS Security Version 1.2 was adopted in 2024. This revision strengthens support for long runnings systems adding new cryptographic algorithms, certificate revocation, and hardness against DoS attacks.
OpenMetadata Community Meeting - 5th June 2024

The OpenMetadata Community Meeting was held on June 5th, 2024. In this meeting, we discussed about the data quality capabilities that are integrated with the Incident Manager, providing a complete solution to handle your data observability needs. Watch the end-to-end demo of the data quality features.
* How to run your own data quality framework
* What is the performance impact of running data quality frameworks
* How to run the test cases in your own ETL pipelines
* How the Incident Manager is integrated
* Get notified with alerts when test cases fail
Watch the meeting recording here - https://www.youtube.com/watch?v=UbNOje0kf6E
Transform Your Communication with Cloud-Based IVR Solutions

Discover the power of Cloud-Based IVR Solutions to streamline communication processes. Embrace scalability and cost-efficiency while enhancing customer experiences with features like automated call routing and voice recognition. Accessible from anywhere, these solutions integrate seamlessly with existing systems, providing real-time analytics for continuous improvement. Revolutionize your communication strategy today with Cloud-Based IVR Solutions. Learn more at: https://thesmspoint.com/channel/cloud-telephony
May Marketo Masterclass, London MUG May 22 2024.pdf

Can't make Adobe Summit in Vegas? No sweat because the EMEA Marketo Engage Champions are coming to London to share their Summit sessions, insights and more!
This is a MUG with a twist you don't want to miss.
Revolutionizing Visual Effects Mastering AI Face Swaps.pdf

The quest for the best AI face swap solution is marked by an amalgamation of technological prowess and artistic finesse, where cutting-edge algorithms seamlessly replace faces in images or videos with striking realism. Leveraging advanced deep learning techniques, the best AI face swap tools meticulously analyze facial features, lighting conditions, and expressions to execute flawless transformations, ensuring natural-looking results that blur the line between reality and illusion, captivating users with their ingenuity and sophistication.
Web:- https://undressbaby.com/
Atelier - Innover avec l’IA Générative et les graphes de connaissances

Atelier - Innover avec l’IA Générative et les graphes de connaissances
Allez au-delà du battage médiatique autour de l’IA et découvrez des techniques pratiques pour utiliser l’IA de manière responsable à travers les données de votre organisation. Explorez comment utiliser les graphes de connaissances pour augmenter la précision, la transparence et la capacité d’explication dans les systèmes d’IA générative. Vous partirez avec une expérience pratique combinant les relations entre les données et les LLM pour apporter du contexte spécifique à votre domaine et améliorer votre raisonnement.
Amenez votre ordinateur portable et nous vous guiderons sur la mise en place de votre propre pile d’IA générative, en vous fournissant des exemples pratiques et codés pour démarrer en quelques minutes.
Microservice Teams - How the cloud changes the way we work

A lot of technical challenges and complexity come with building a cloud-native and distributed architecture. The way we develop backend software has fundamentally changed in the last ten years. Managing a microservices architecture demands a lot of us to ensure observability and operational resiliency. But did you also change the way you run your development teams?
Sven will talk about Atlassian’s journey from a monolith to a multi-tenanted architecture and how it affected the way the engineering teams work. You will learn how we shifted to service ownership, moved to more autonomous teams (and its challenges), and established platform and enablement teams.
Why Mobile App Regression Testing is Critical for Sustained Success_ A Detail...

A dynamic process unfolds in the intricate realm of software development, dedicated to crafting and sustaining products that effortlessly address user needs. Amidst vital stages like market analysis and requirement assessments, the heart of software development lies in the meticulous creation and upkeep of source code. Code alterations are inherent, challenging code quality, particularly under stringent deadlines.
openEuler Case Study - The Journey to Supply Chain Security

openEuler Case Study - The Journey to Supply Chain Security
How to write a program in any programming language

How to write a program in any programming language
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Mobile App Development Company In Noida | Drona Infotech

Looking for a reliable mobile app development company in Noida? Look no further than Drona Infotech. We specialize in creating customized apps for your business needs.
Visit Us For : https://www.dronainfotech.com/mobile-application-development/
E-commerce Development Services- Hornet Dynamics

For any business hoping to succeed in the digital age, having a strong online presence is crucial. We offer Ecommerce Development Services that are customized according to your business requirements and client preferences, enabling you to create a dynamic, safe, and user-friendly online store.
Recently uploaded (20)
Empowering Growth with Best Software Development Company in Noida - Deuglo

Empowering Growth with Best Software Development Company in Noida - Deuglo
AI Fusion Buddy Review: Brand New, Groundbreaking Gemini-Powered AI App

AI Fusion Buddy Review: Brand New, Groundbreaking Gemini-Powered AI App
UI5con 2024 - Boost Your Development Experience with UI5 Tooling Extensions

UI5con 2024 - Boost Your Development Experience with UI5 Tooling Extensions
DDS-Security 1.2 - What's New? Stronger security for long-running systems

DDS-Security 1.2 - What's New? Stronger security for long-running systems
Transform Your Communication with Cloud-Based IVR Solutions

Transform Your Communication with Cloud-Based IVR Solutions
May Marketo Masterclass, London MUG May 22 2024.pdf

May Marketo Masterclass, London MUG May 22 2024.pdf
Revolutionizing Visual Effects Mastering AI Face Swaps.pdf

Revolutionizing Visual Effects Mastering AI Face Swaps.pdf
Atelier - Innover avec l’IA Générative et les graphes de connaissances

Atelier - Innover avec l’IA Générative et les graphes de connaissances
Microservice Teams - How the cloud changes the way we work

Microservice Teams - How the cloud changes the way we work
Why Mobile App Regression Testing is Critical for Sustained Success_ A Detail...

Why Mobile App Regression Testing is Critical for Sustained Success_ A Detail...
openEuler Case Study - The Journey to Supply Chain Security

openEuler Case Study - The Journey to Supply Chain Security
How to write a program in any programming language

How to write a program in any programming language
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Mobile App Development Company In Noida | Drona Infotech

Mobile App Development Company In Noida | Drona Infotech
Red Hat, CentOS, Fedora 2019
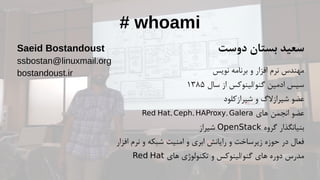
- 1. # whoami دوست بستان سعید نویس برنامه و افزار نرم مهندس سال از گنو/لینوکس ادمین سیس۱۳۸۵ شیرازکلود و شیرازالگ عضو های انجمن عضو, , ,Red Hat Ceph HAProxy Galera گروه بنیانگذارOpenStackشیراز افزار نرم و شبکه امنیت و ابری رایانش و زیرساخت حوزه در فعال های تکنولوژی و گنو/لینوکس های دوره مدرسRed Hat Saeid Bostandoust ssbostan@linuxmail.org bostandoust.ir
- 4. ردهت؟ از خبر چه
- 5. #1
- 9. #2
- 13. #3
- 15. Based on Fedora 28 and the upstream kernel 4.18
- 16. YUMv4 package manager is now based on the DNF technology. BaseOS | AppStream Repositories # yum module list # yum module info php # yum module install php:7.1/minimal # yum module remove php:7.1/minimal
- 17. Python 3.6 is the default Python implementation in RHEL 8. Limited support for Python 2.7 is provided. No version of Python is installed by default.
- 18. GNOME Shell has been rebased to version 3.28. GNOME session and the GNOME Display Manager use Wayland. X.Org server is available as well.
- 21. Custom system images with Image Builder lorax-composer Rethinking how we make ready-to-use operating system images.
- 22. Spectre V2 mitigation default changed from IBRS to Retpolines spectre_v2=ibrs
- 23. nobody user replaces nfsnobody from ID 99 to 65534 (overflow)
- 25. XFSnow supports shared copy-on-write data extents cp --reflink Maximum XFS file system size is 1024 TiB
- 26. Virtual Data Optimizer Data Deduplication | Compression
- 27. LUKS2 is now the default format for encrypting volumes metadata redundancy auto-recovery in case of a partial metadata corruption event
- 29. Docker is not included in RHEL 8.0. For working with containers, use the podman, buildah, skopeo, and runc tools.
- 30. system-wide cryptographic policies update-crypto-policies --show update-crypto-policies --set FUTURE
- 31. #4
- 33. CentOS Stream will be a rolling-release Linux distro midstream between upstream development in Fedora Linux downstream development for RHEL
- 34. #5
- 37. Fedora 31 New Features: “python” command is “python3” Support for cgroups v2 Switching RPM compression to ztsd Support for RPM 4.15 New Desktop Spins: KDE Plasma, Xfce ARM AArch64 architecture for single-board computers (SBCs)
- 38. .باشید پیروز و موفق sudo -u#-1 poweroff
