Embed presentation
Download to read offline
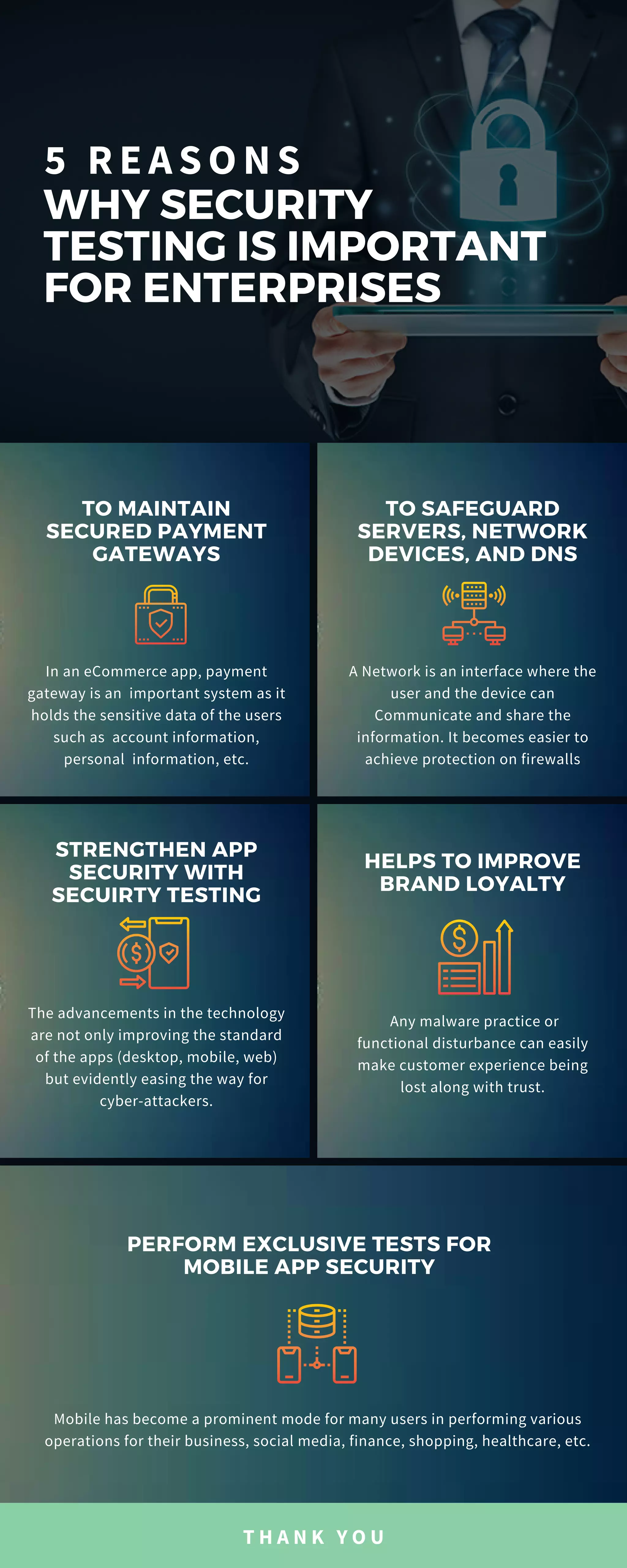

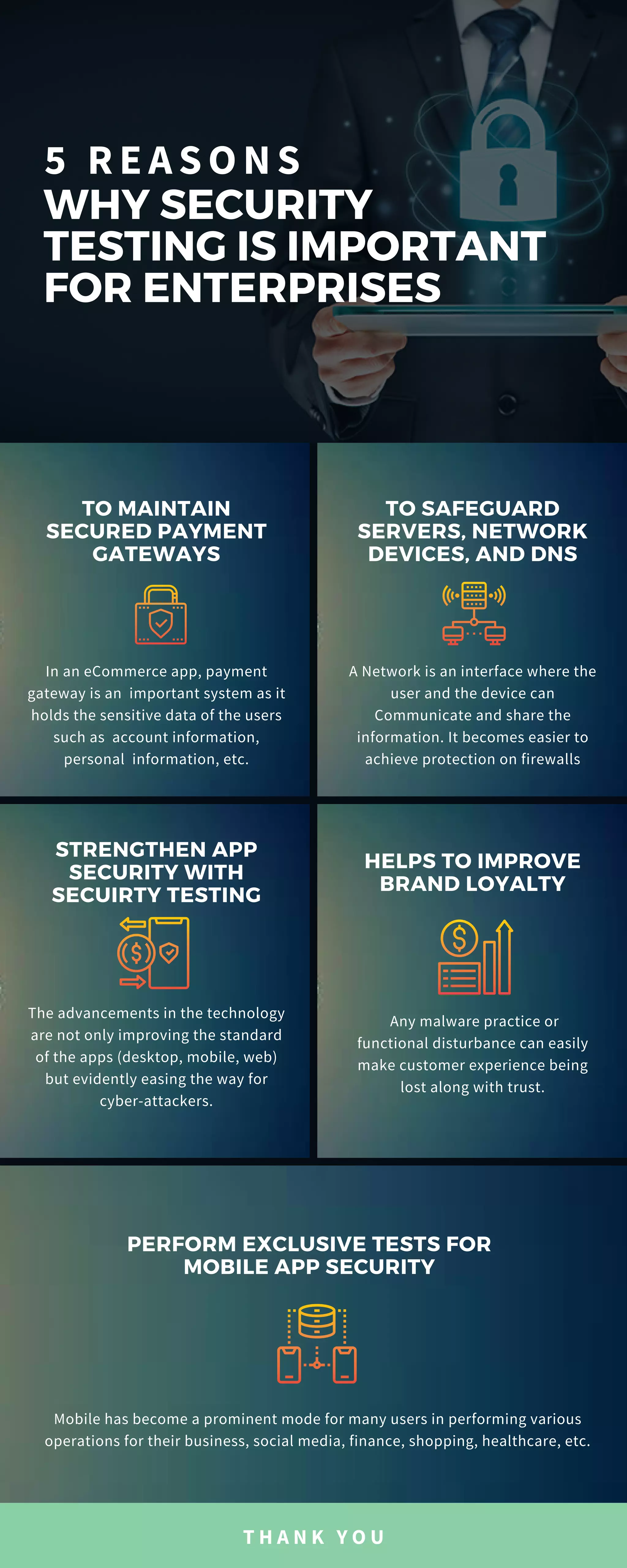
Security testing is crucial for enterprises as mobile apps have become a key platform for business operations. It protects servers and network devices, strengthens app security, and helps maintain customer trust and brand loyalty. Ensuring secure payment gateways in e-commerce apps is essential due to the sensitivity of user data involved.