This tutorial provides a comprehensive guide on Python environment variables, explaining their significance in configuring applications and enhancing security by preventing hard-coding sensitive information. It describes how to access and set environment variables using the os module, along with troubleshooting common issues and best practices to maintain security and proper functionality. The tutorial aims to equip both beginners and experienced developers with practical skills in managing environment variables in Python projects.
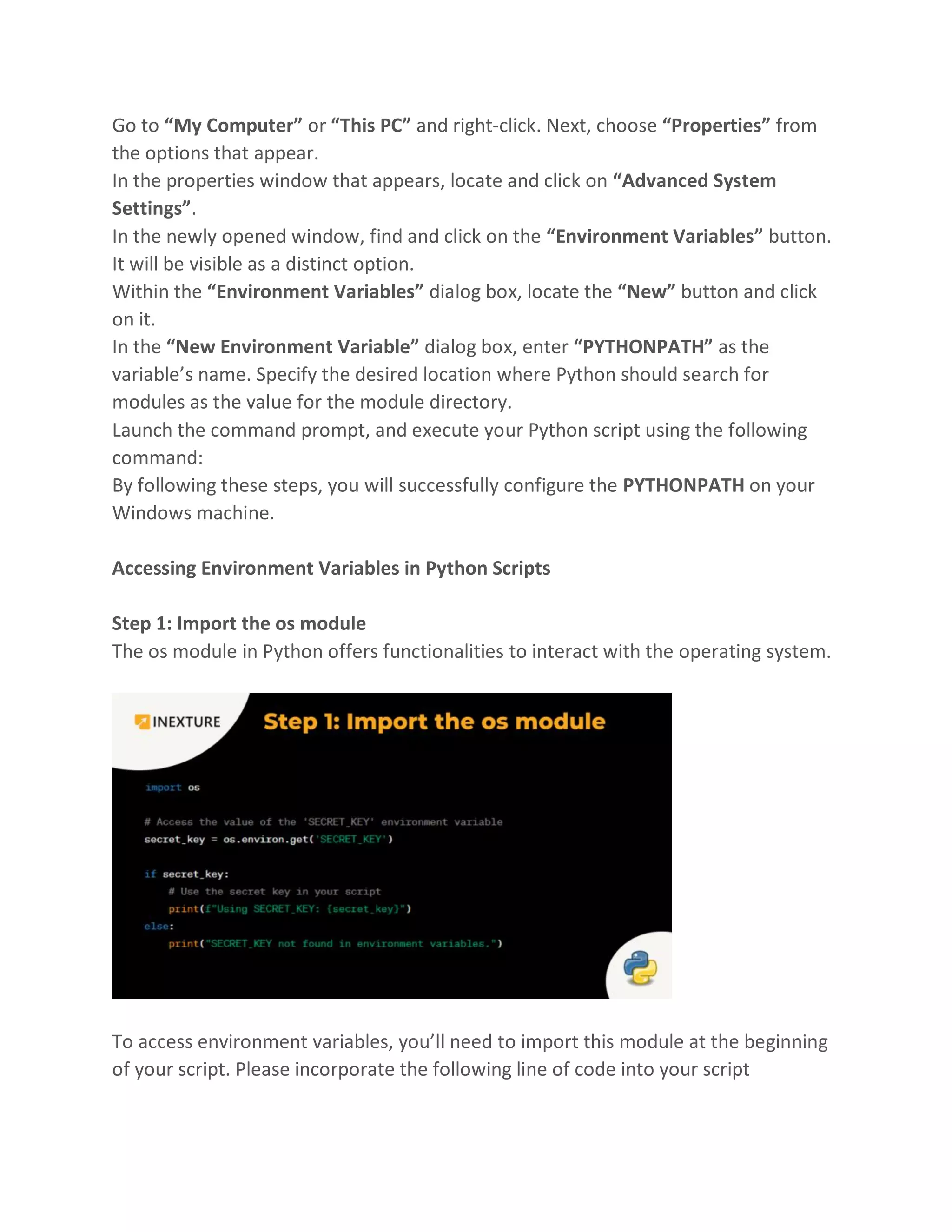
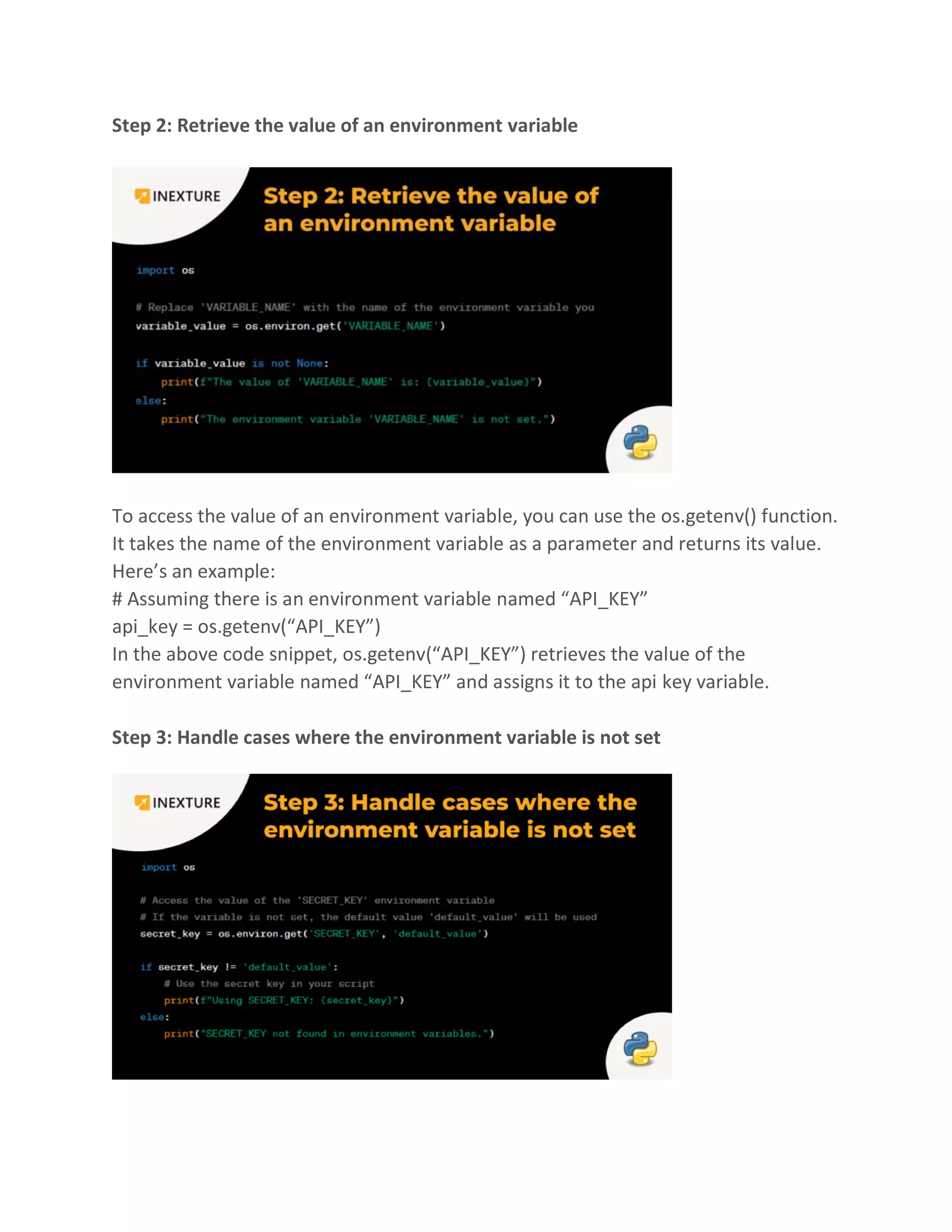
![If the specified environment variable does not exist, os.getenv() will return None. It’s
important to handle this case in your script to avoid errors. You can use an if
statement to check if the environment variable exists before using its value. Here’s
an example:
api_key = os.getenv(“API_KEY”)
if api_key is not None:
# Use the API key
print(“API Key:”, api_key)
else:
print(“API key not found.”)
In this code snippet, if the environment variable “API_KEY” exists, it will be printed.
Alternatively, it will output the message “API key not found.”
Step 4: Set environment variables
To set an environment variable, you can use the os.environ dictionary. Here’s an
example:
# Set an environment variable named “API_KEY”
os.environ[“API_KEY”] = “your_api_key_value”
In the above code, os.environ[“API_KEY”] = “your_api_key_value” sets the value of
the environment variable “API_KEY” to “your_api_key_value”.](https://image.slidesharecdn.com/pythonenvironmentvariablesastepbysteptutorialforbeginners-230731100911-0da60b36/75/Python-Environment-Variables-A-Step-by-Step-Tutorial-for-Beginners-5-2048.jpg)