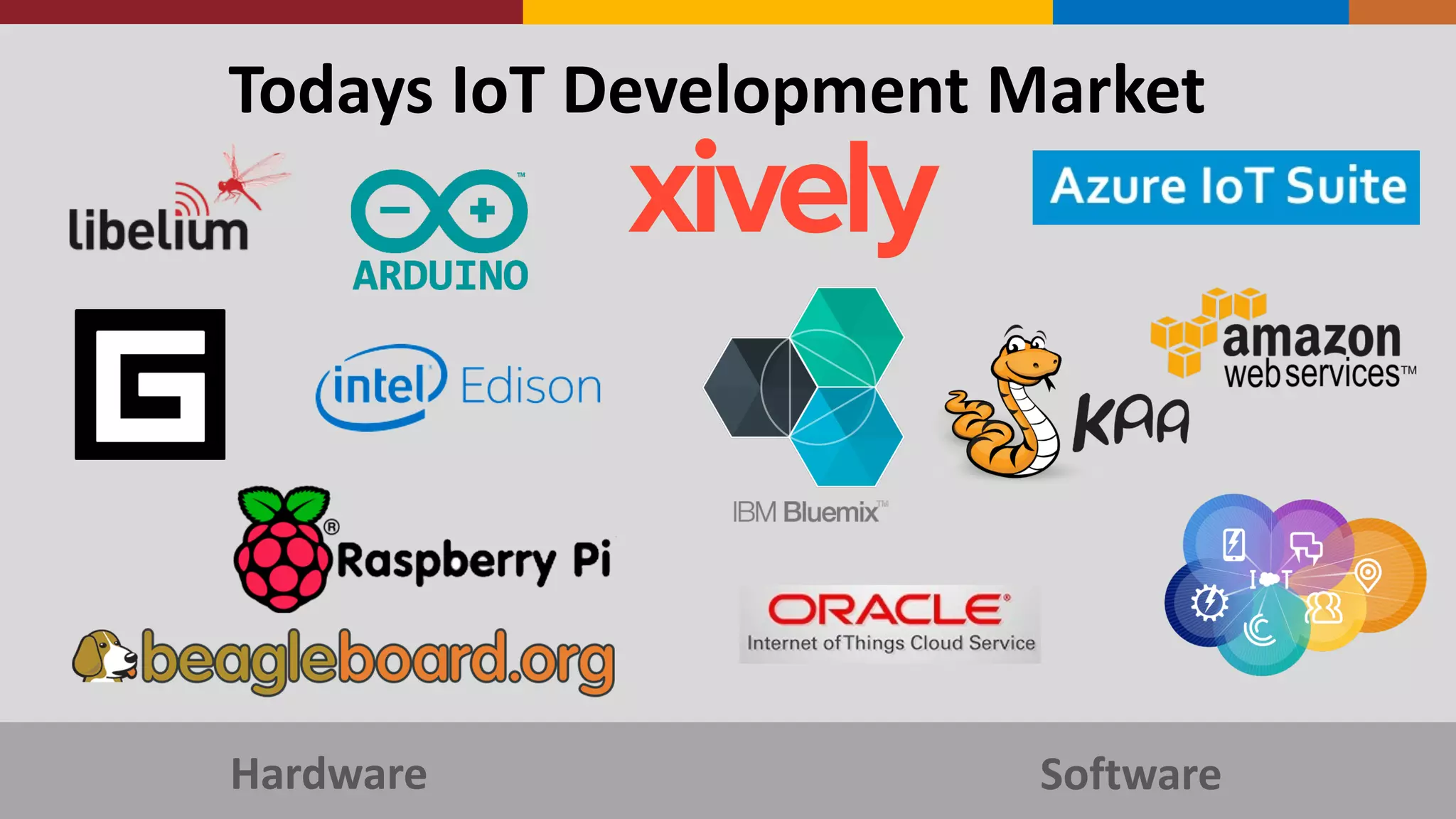
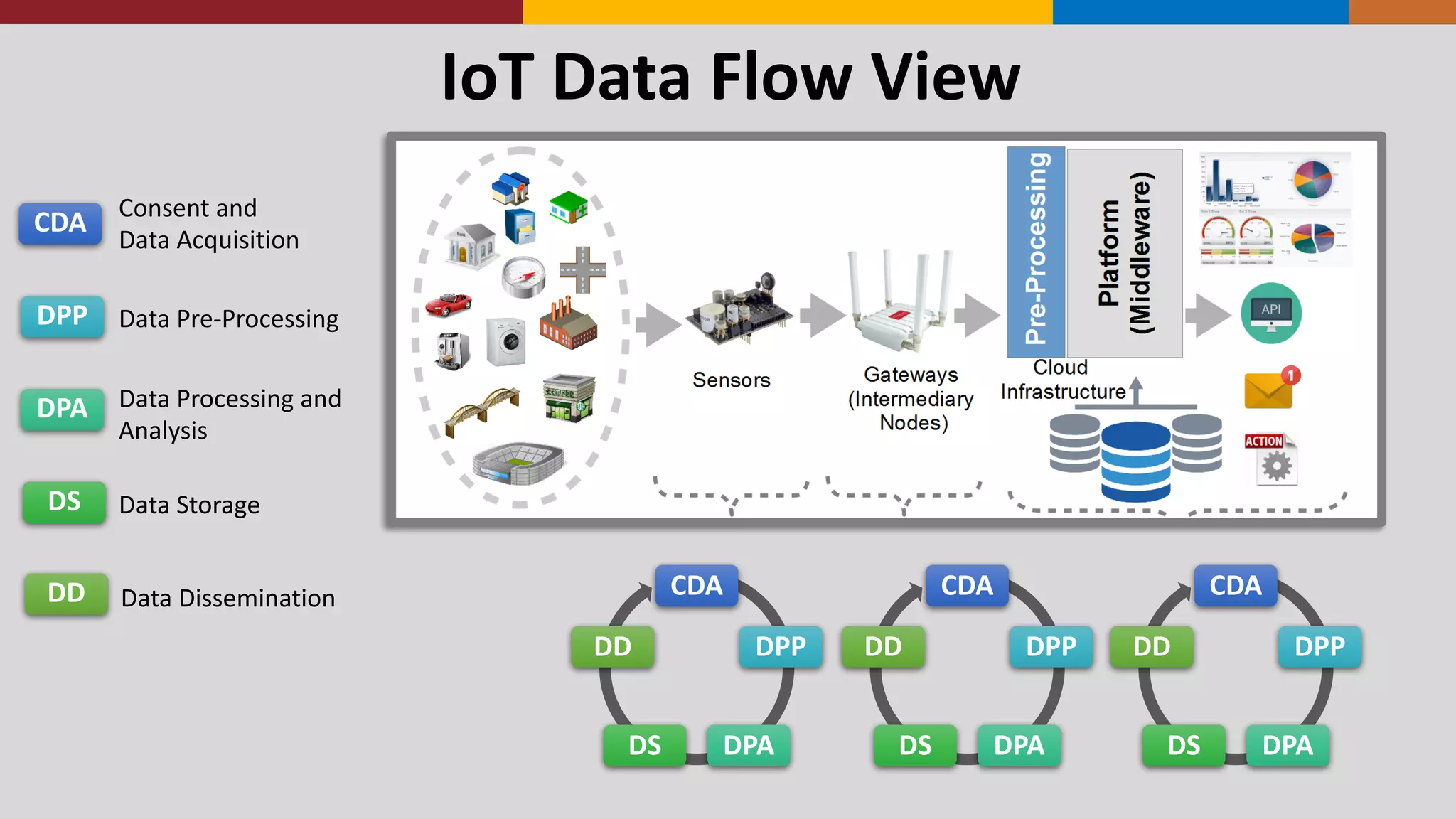
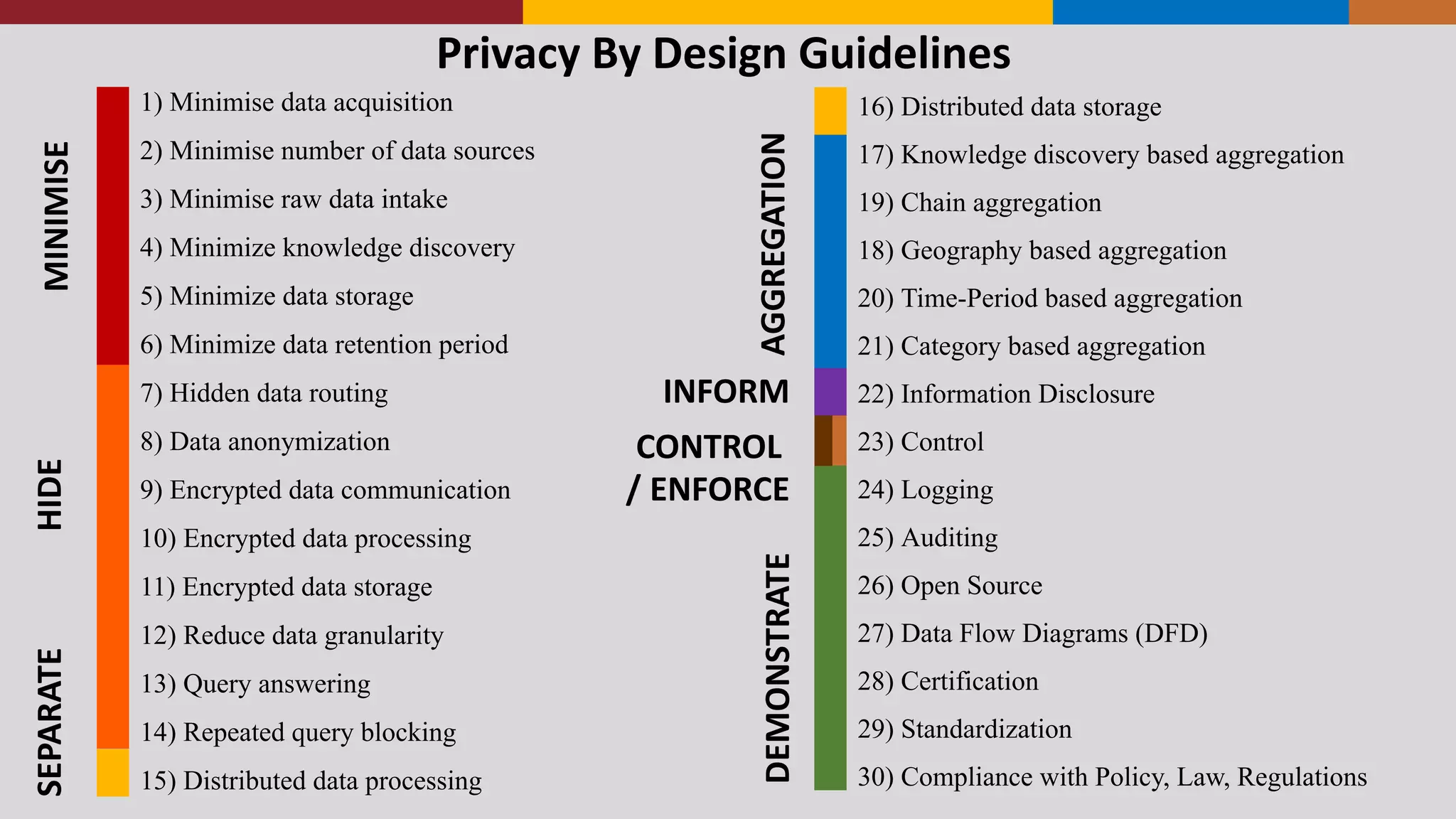
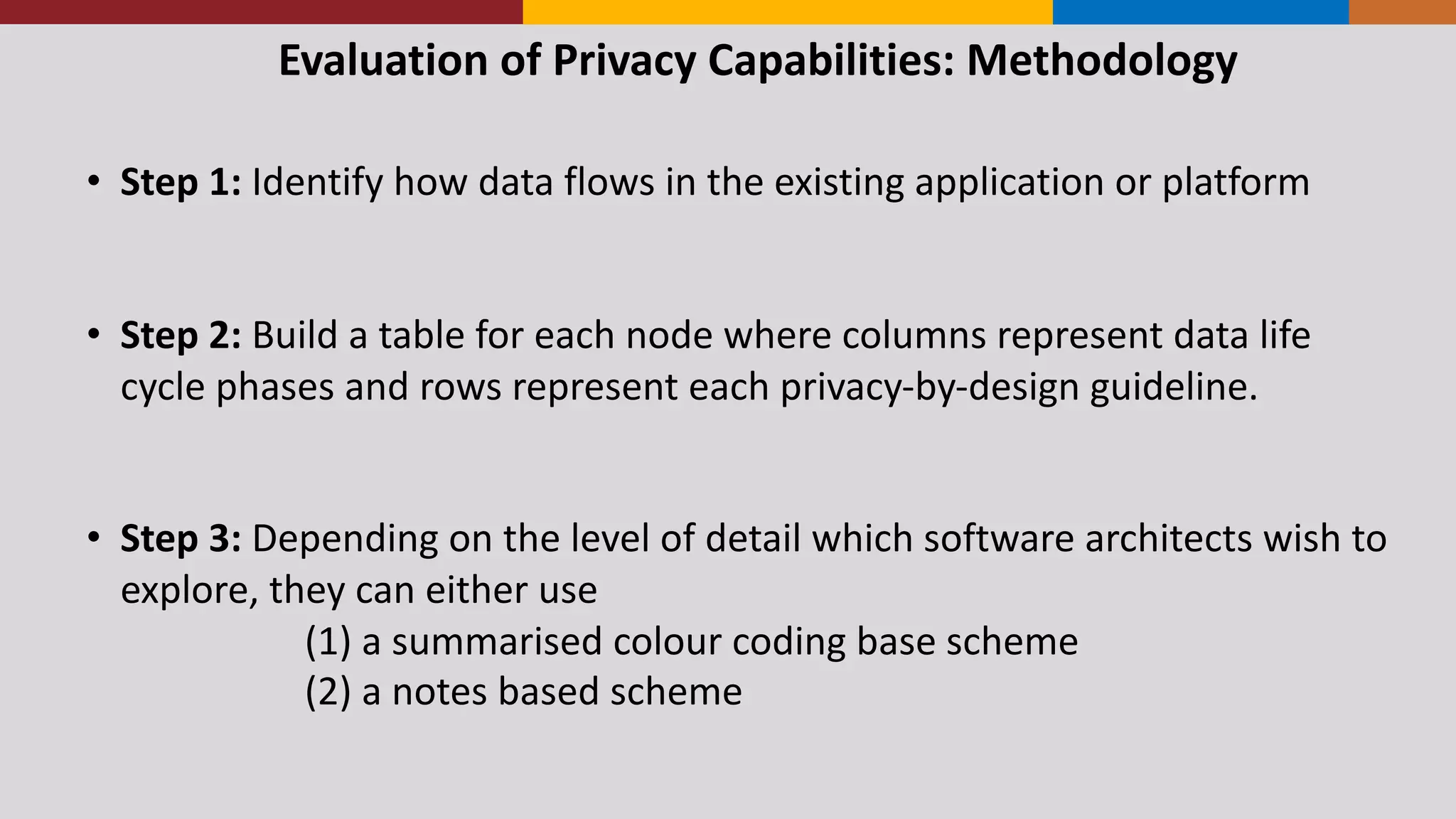
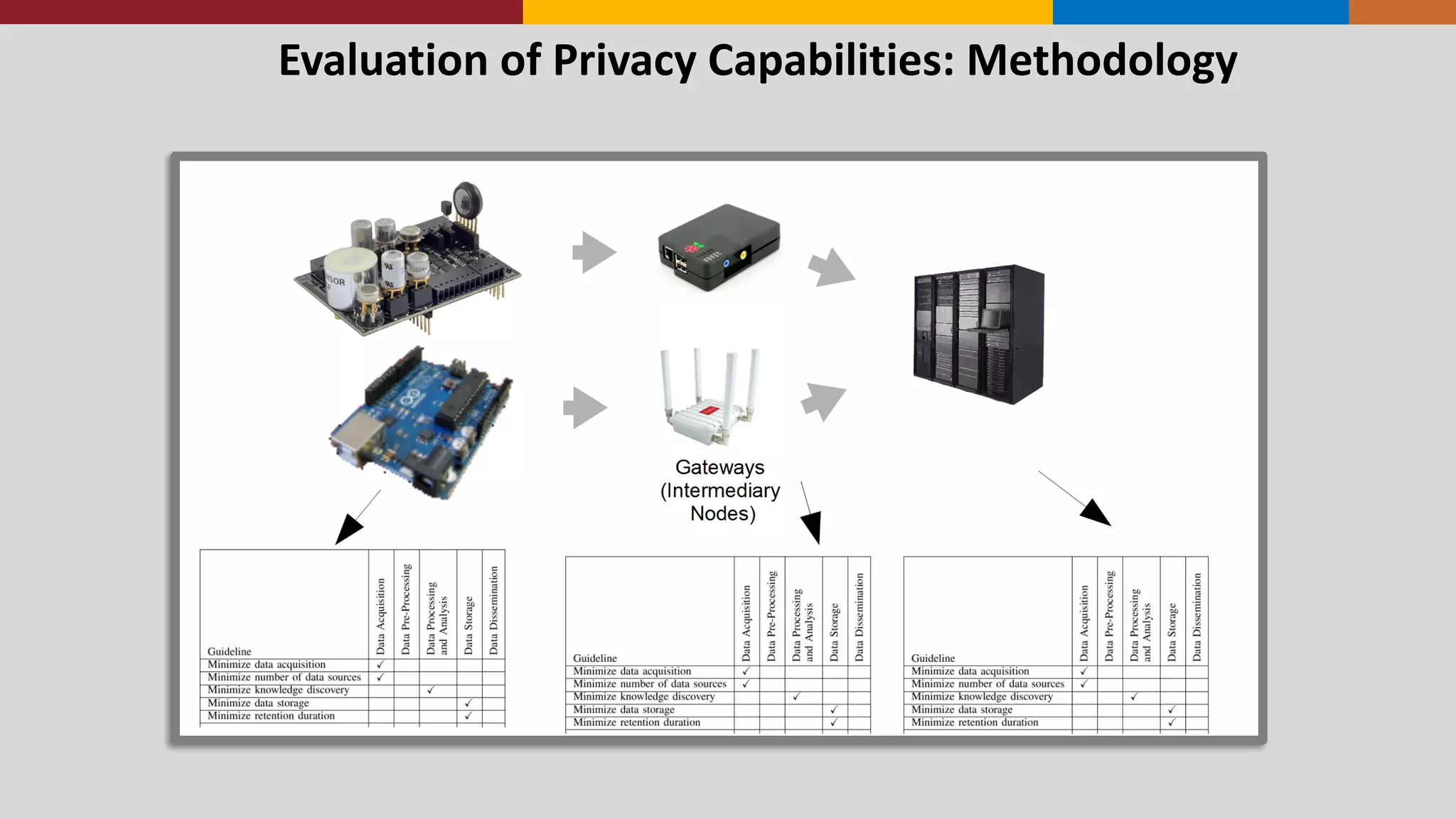
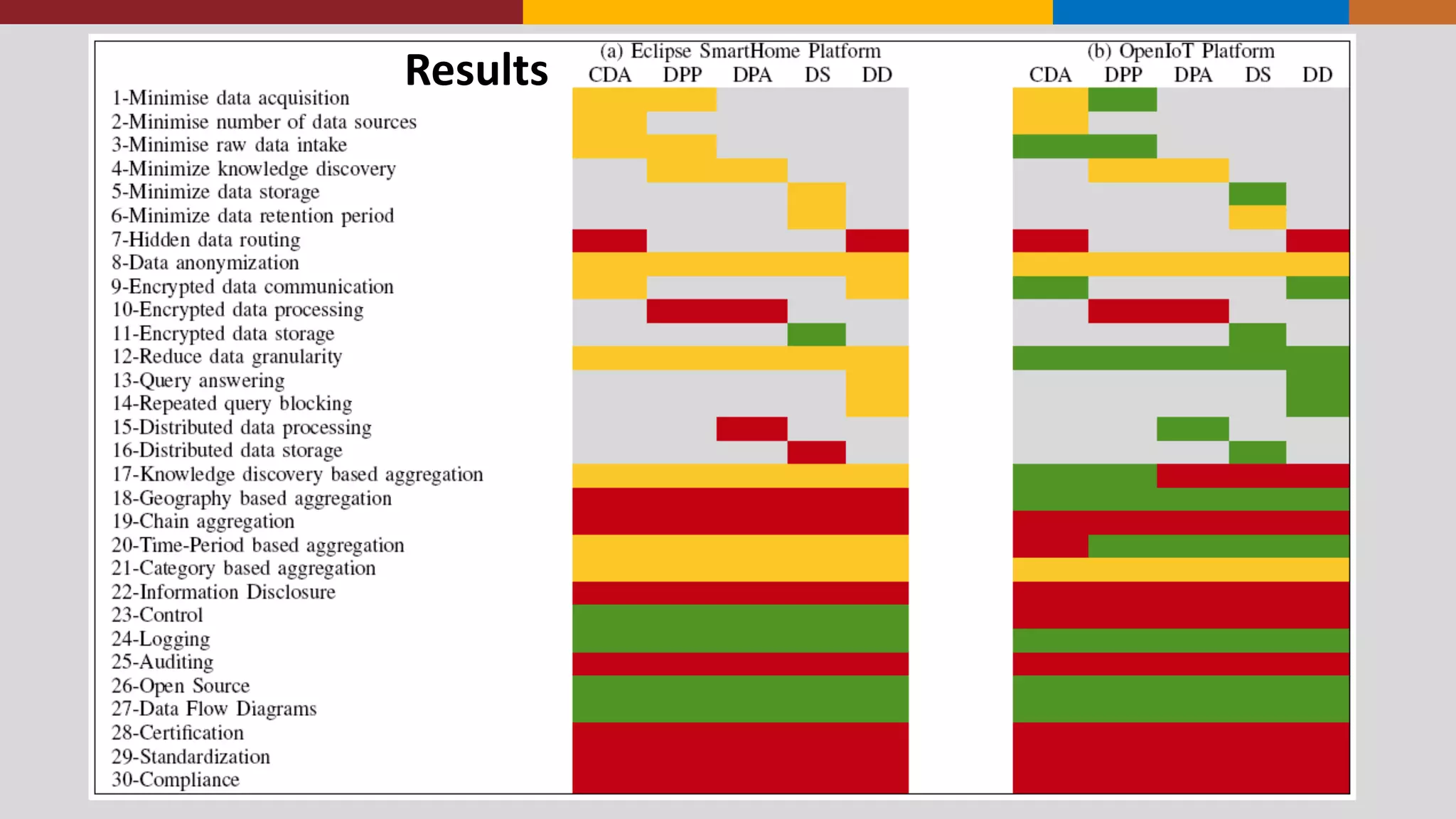
The document presents a privacy-by-design framework aimed at guiding software architects in assessing Internet of Things (IoT) applications, addressing the complexity and privacy concerns inherent in IoT systems. It reviews existing methodologies and guidelines, ultimately proposing a detailed approach that emphasizes minimizing data acquisition and enhancing user-centric privacy measures. The framework aims to improve the privacy capabilities of IoT applications and evaluate the effectiveness of various platforms in safeguarding user data.

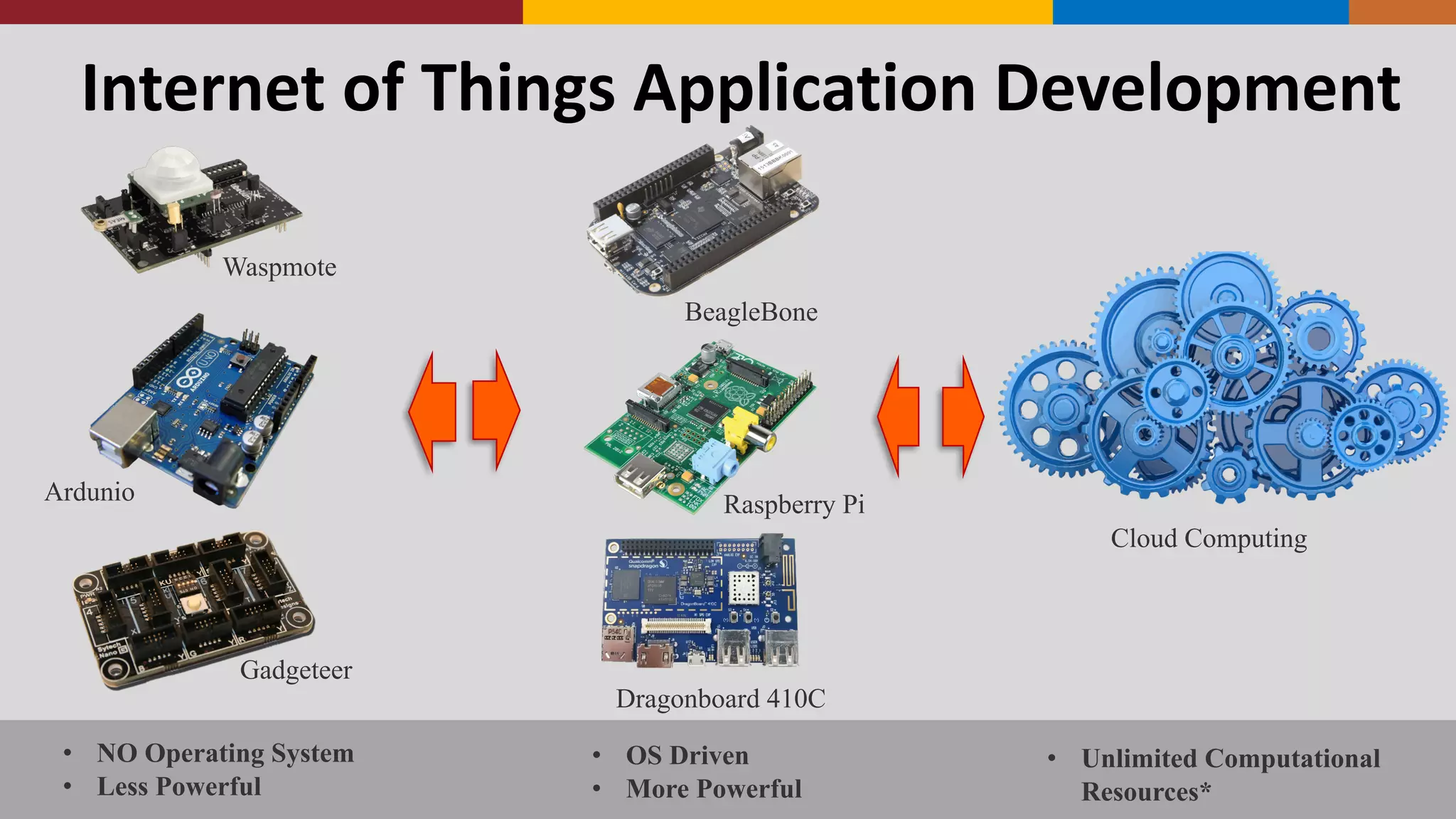

![Research
Directions
• Can
1)
Novice
2)
Experience
Software
architects
assess
a
given
platform
using
the
proposed
guidelines
consistently?
If
there
are
variation,
why?
• Given
a
case
study,
can
privacy
guidelines
guide
1)
Novice
2)
Experience
Towards
a better privacy-‐aware
IoT
applications
Evaluation
Future
work
• Privacy
Tactics
-‐ Tactics
are
design
decisions
that
improve
individual
quality
attribute
(e.g.
Privacy)
concerns.
[Basic
building
blocks]
• Privacy
Patterns
-‐ Patterns describe
the
high-‐level
structure
and
behaviour
of
software
systems
as
the
solution
to
multiple
system
requirements
[Complex
Compositions]](https://image.slidesharecdn.com/privacyguidelines-160912102024/75/IOT-2016-7-9-Septermber-2016-Stuttgart-Germany-19-2048.jpg)