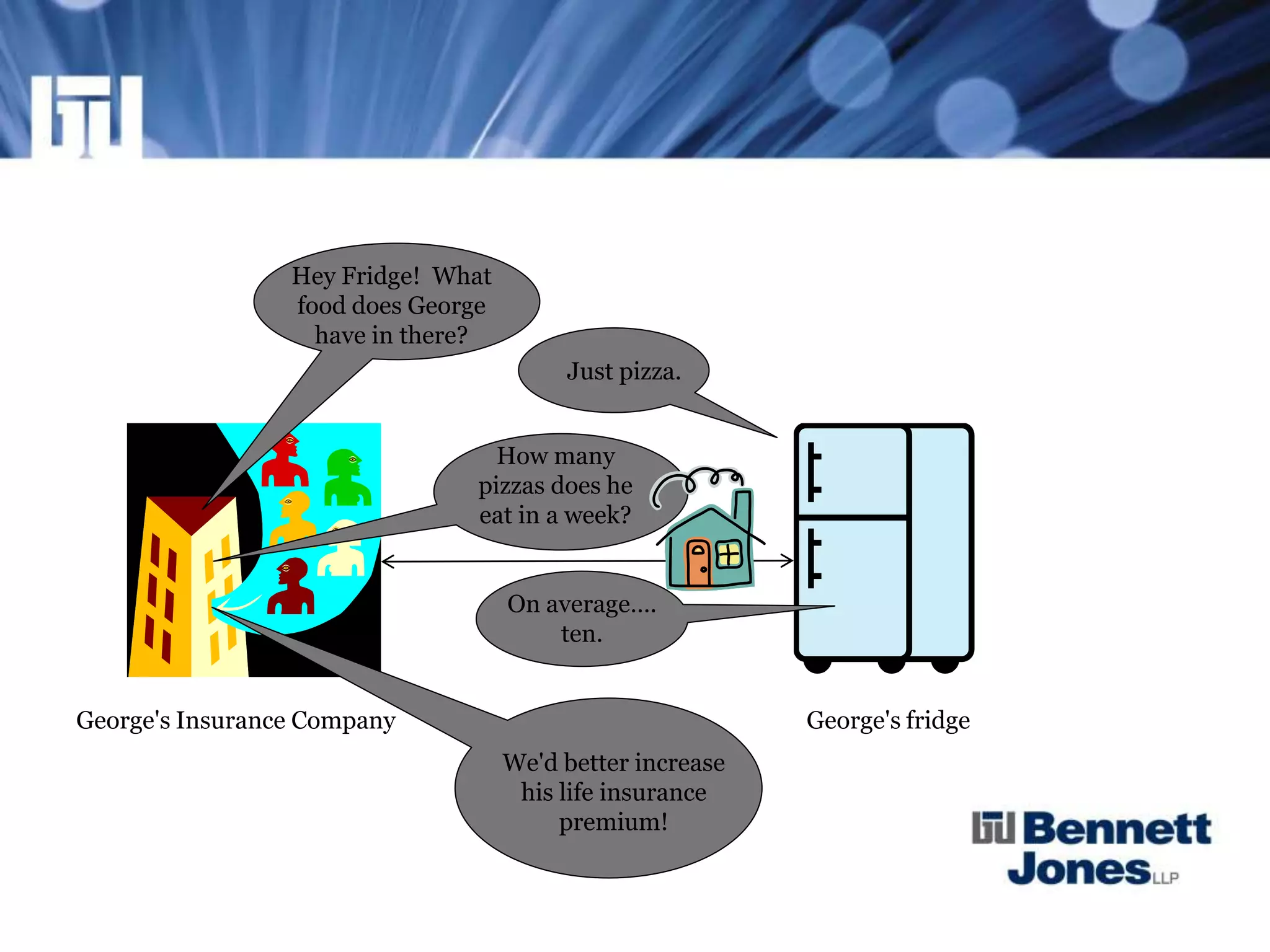
This document discusses the Internet of Things (IoT) and provides examples of connected devices. It notes that by 2020, 50 billion devices are estimated to be connected to the Internet. It discusses privacy issues regarding personal data collection and use by IoT devices. Security issues are also examined, such as vulnerabilities of connected devices to hacking. Intellectual property questions are raised about who owns works created by machines. The document concludes by stating that more regulation of IoT is expected.


![Privacy Issues
• SCC in Dagg v. Canada (Minister of Finance), [1997] 2 S.C.R. 403
said broadly:
"its intent seems to be to capture any information about a specific person,
subject only to specific exceptions"
• Privacy Commissioner in its 2001-2002 Annual Report to
Parliament also stated that:
"the definition ['about an identifiable individual'] is deliberately broad…It
does not matter who generated the information, or how, or who
technically "owns" it…information [is] personal even if there is the
smallest potential for it to be about an identifiable individual"](https://image.slidesharecdn.com/0315eeb5-cc75-49bb-a961-1bdca94c9fb5-141222160642-conversion-gate02/75/Internet-of-Things-TCLG-Oct-23-2014-8-2048.jpg)
![Privacy Issues
• Information that alone does not identify an individual can be
"personal information" if, in combination with other information,
it could be used to identify an individual
• Federal Court determined that such data, which could be combined
with other data to identify someone, is "personal information". See
Gordon v. Canada (Minister of Health), [2008] CarswellNat 522
paragraph/line 34
• IoT becomes complicated as it generates BIG DATA. Data, when
coupled with other available data, could lead to identifying individuals](https://image.slidesharecdn.com/0315eeb5-cc75-49bb-a961-1bdca94c9fb5-141222160642-conversion-gate02/75/Internet-of-Things-TCLG-Oct-23-2014-9-2048.jpg)