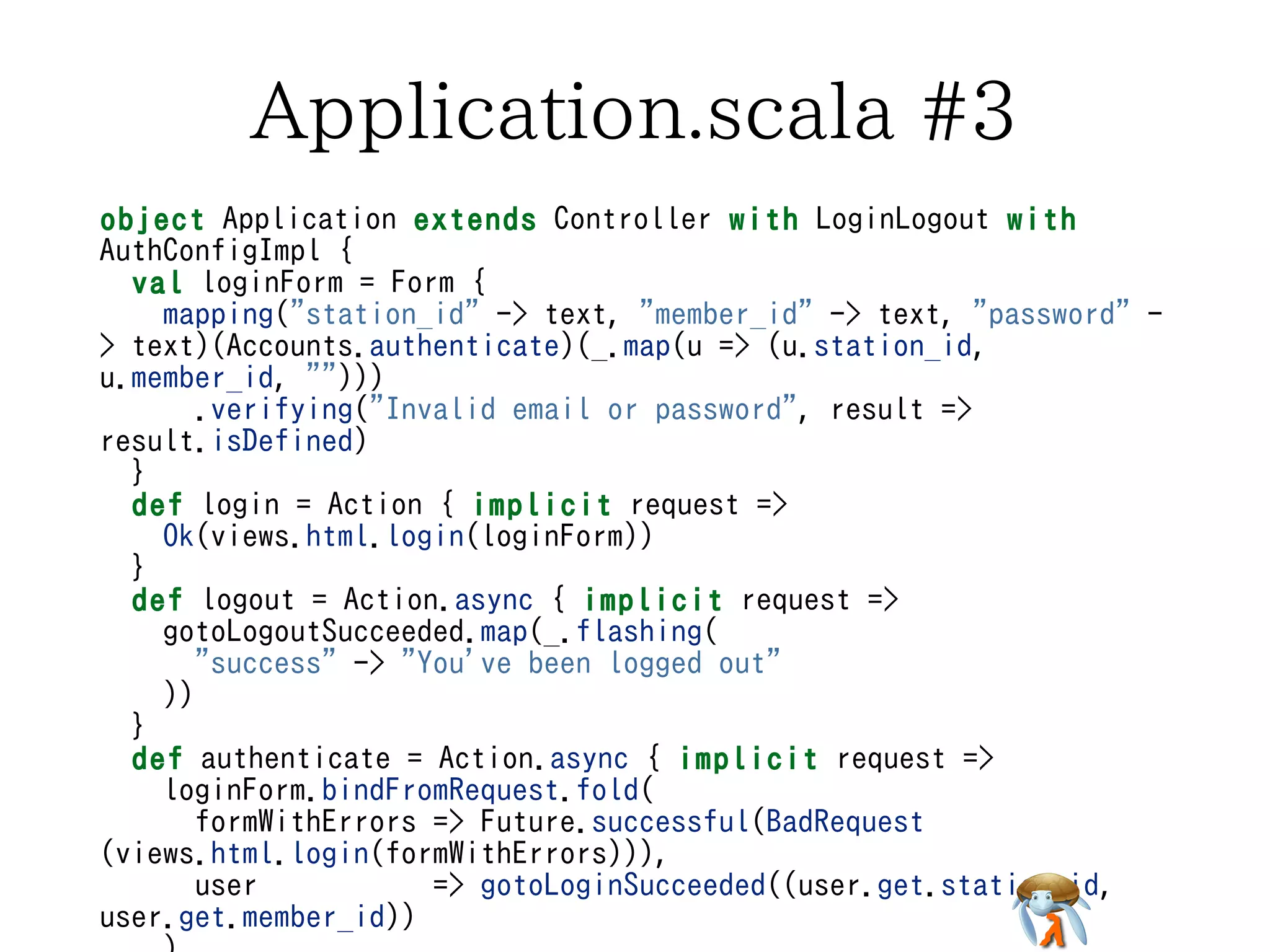
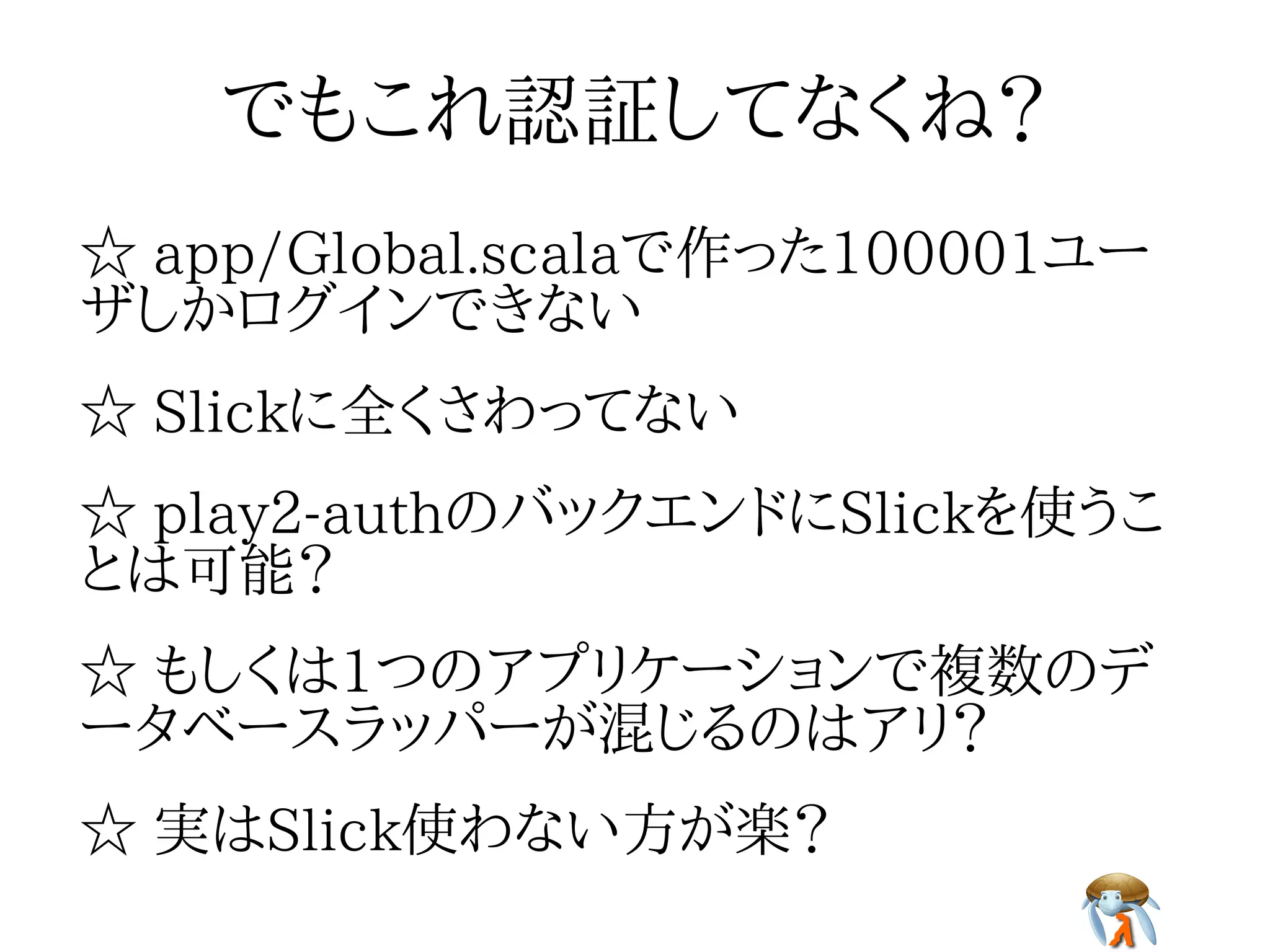
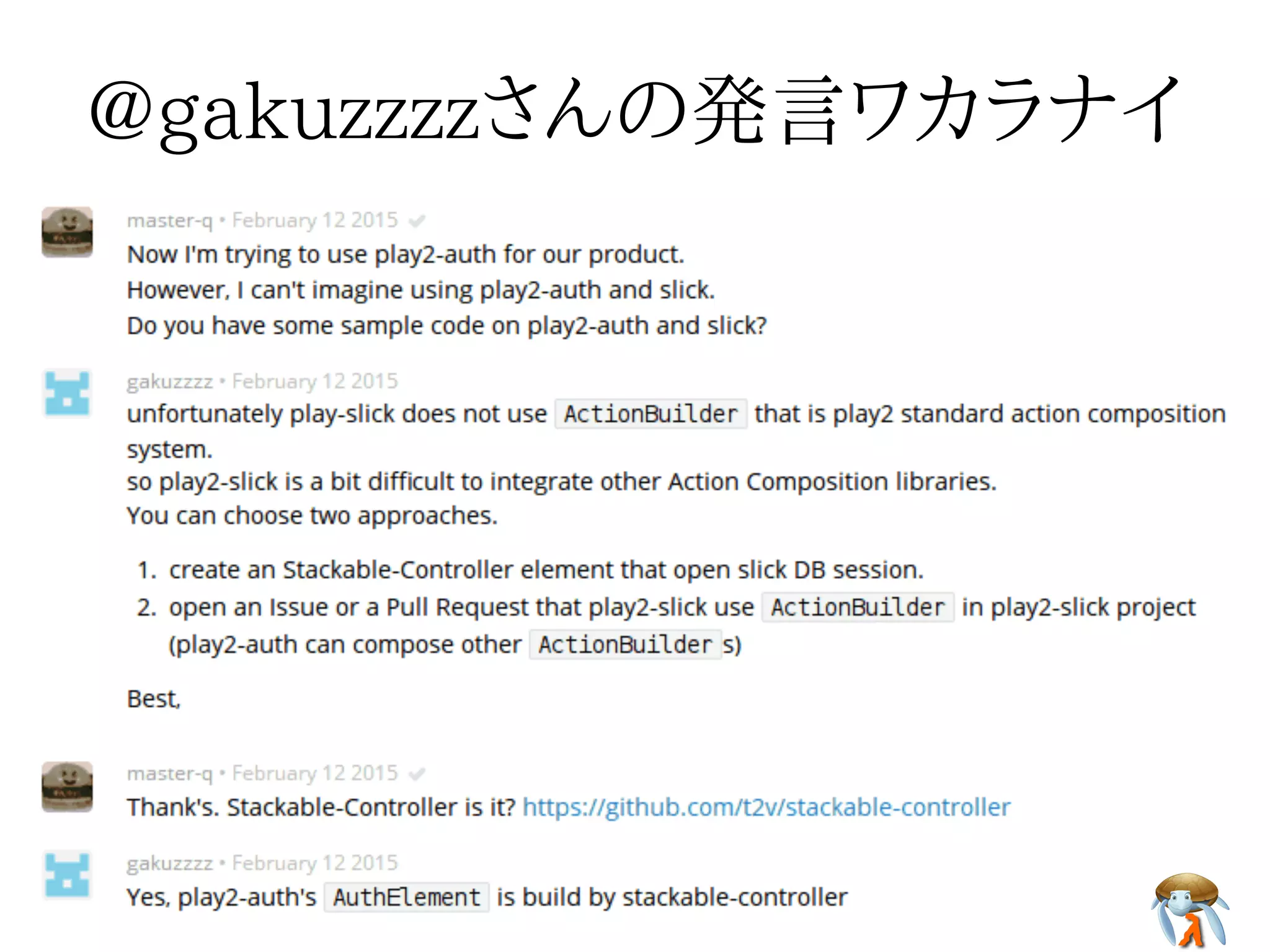
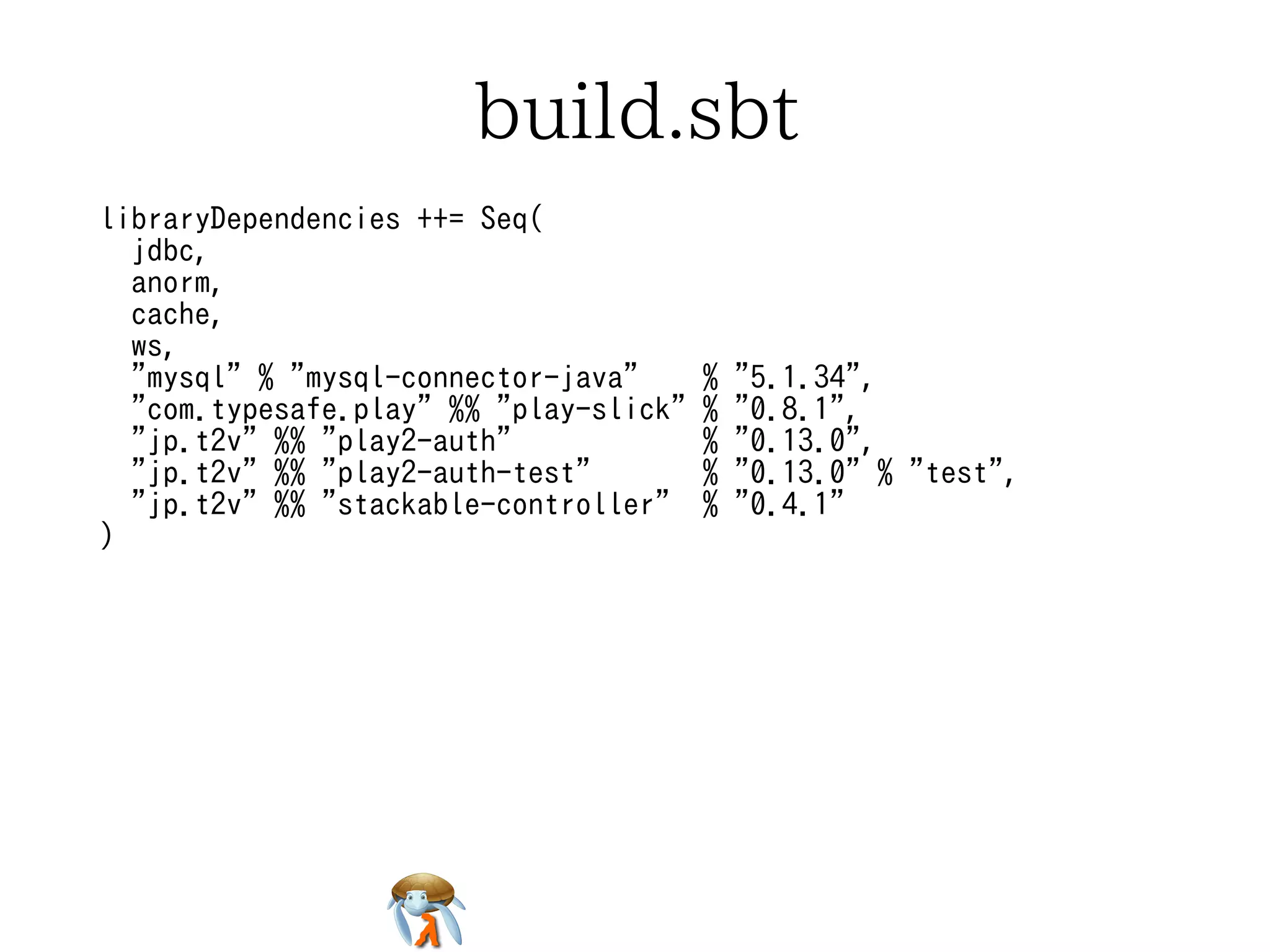
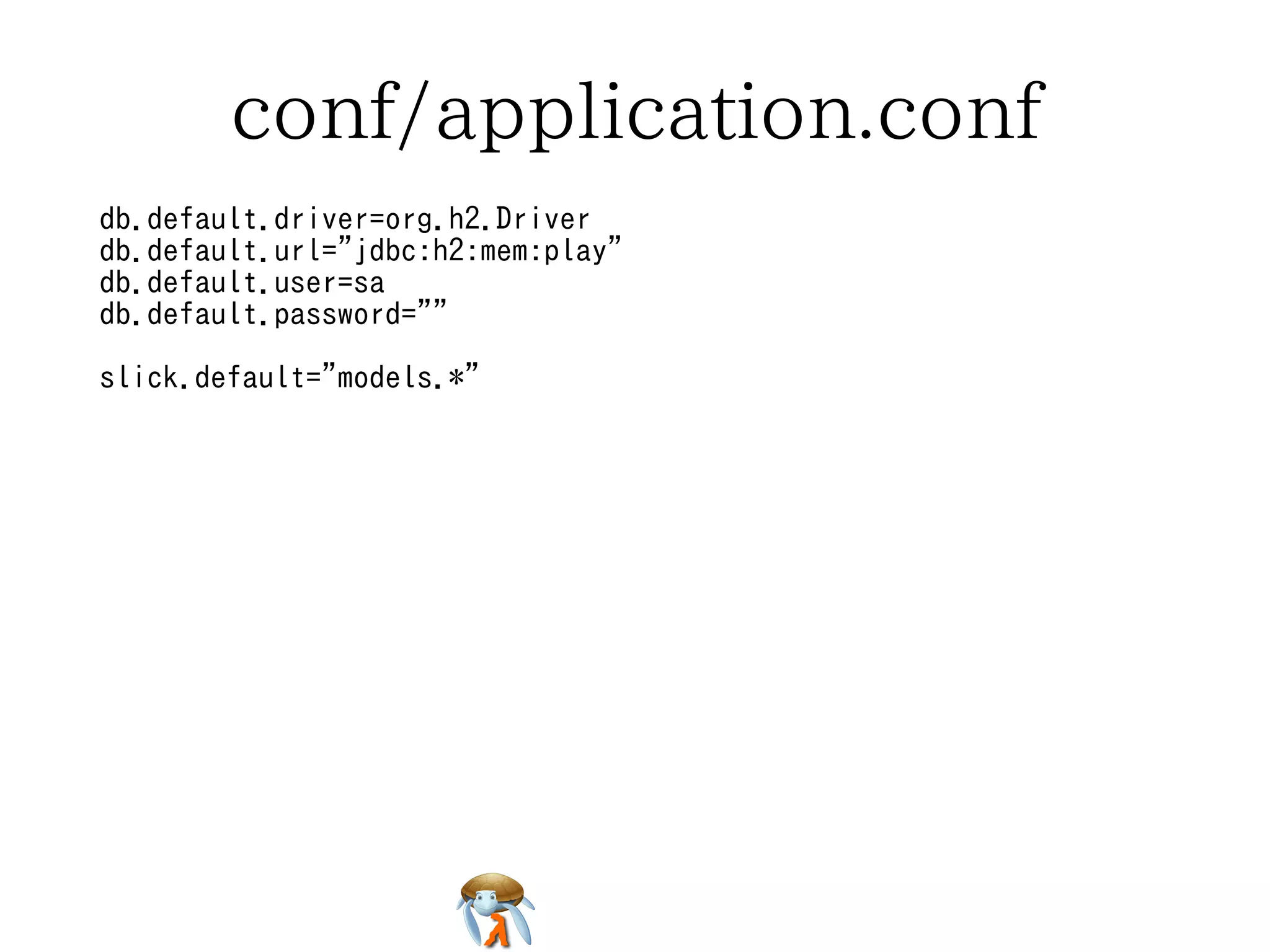
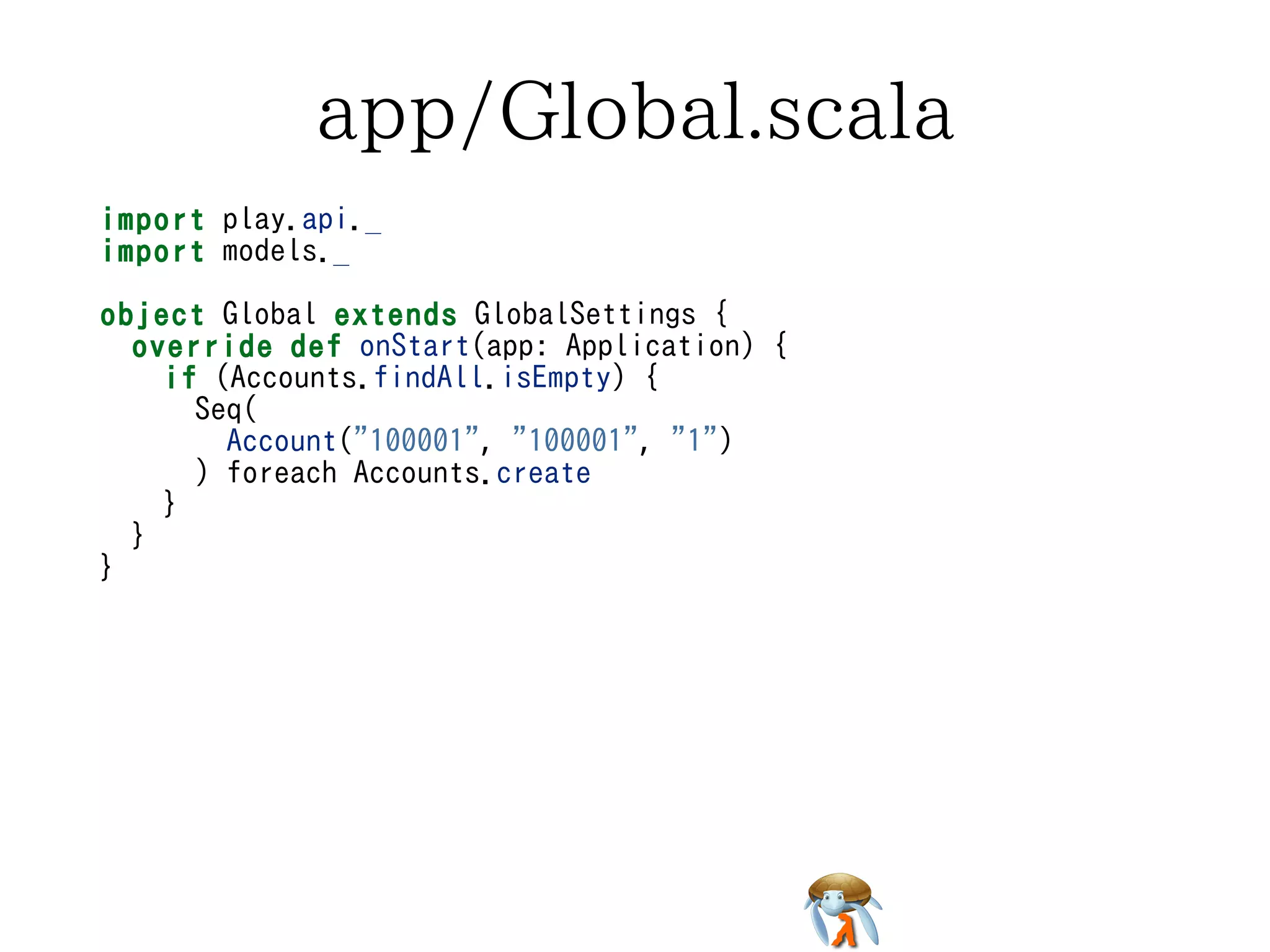
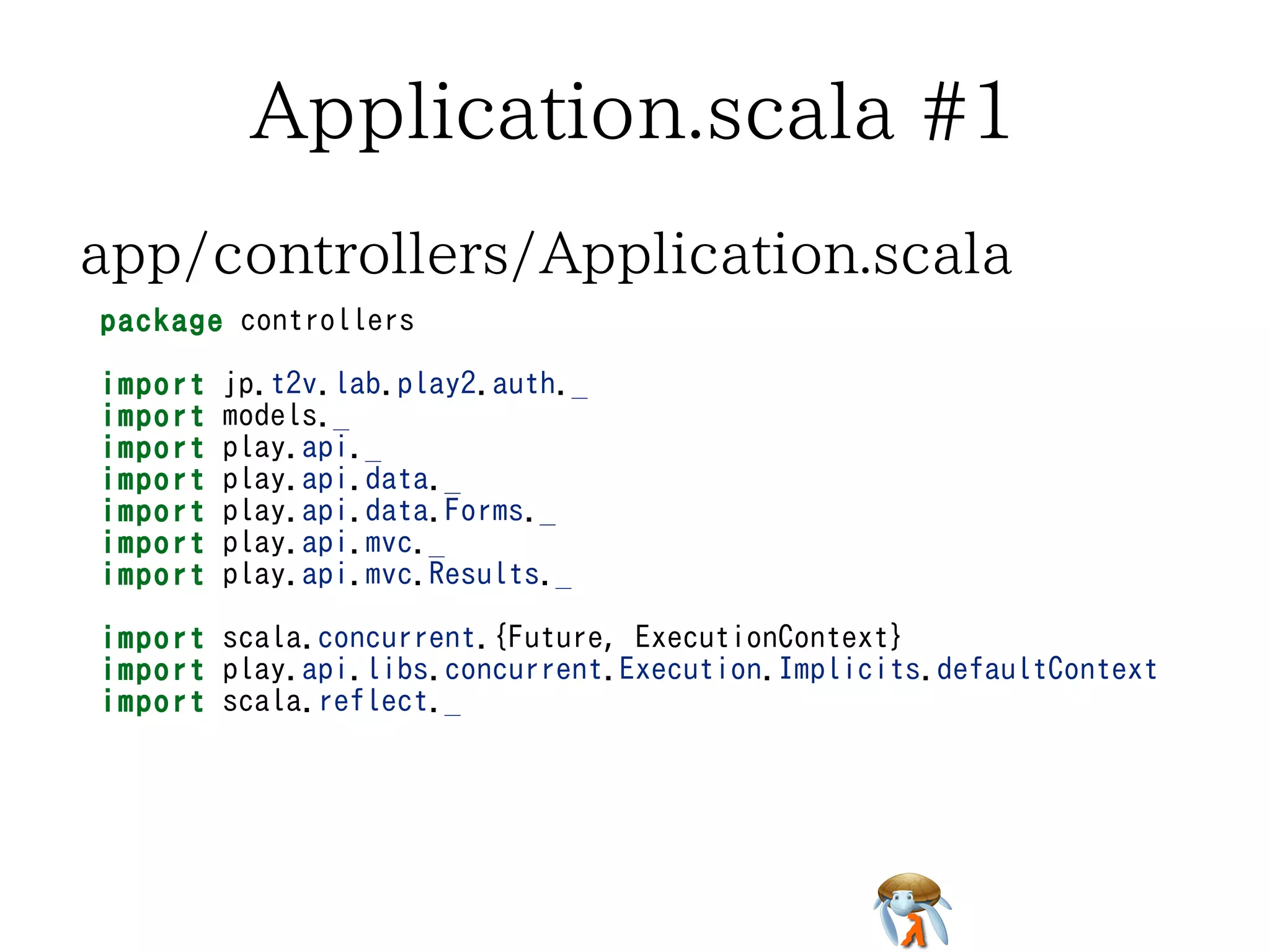
The document discusses an attempt to use Play, Slick, and play2-auth together for a web application project. It describes setting up the build configuration and dependencies, defining Account and Role models using Slick, and implementing authentication and authorization logic. However, the author encountered difficulties after only one month of using Scala and was not able to complete the implementation.


 {
def station_id = column[String]("STATION_ID")
def member_id = column[String]("MEMBER_ID")
def password = column[String]("PASSWORD")
def * = (station_id, member_id, password) <> (Account.tupled,
Account.unapply _)
def pk = primaryKey("pk_a", (station_id, member_id))
}
package models
import play.api.db.slick.Config.driver.simple._
case class Account(station_id: String, member_id: String,
password: String)
class Accounts(tag: Tag) extends Table[Account](tag, "ACCOUNT") {
def station_id = column[String]("STATION_ID")
def member_id = column[String]("MEMBER_ID")
def password = column[String]("PASSWORD")
def * = (station_id, member_id, password) <> (Account.tupled,
Account.unapply _)
def pk = primaryKey("pk_a", (station_id, member_id))
}
package models
import play.api.db.slick.Config.driver.simple._
case class Account(station_id: String, member_id: String,
password: String)
class Accounts(tag: Tag) extends Table[Account](tag, "ACCOUNT") {
def station_id = column[String]("STATION_ID")
def member_id = column[String]("MEMBER_ID")
def password = column[String]("PASSWORD")
def * = (station_id, member_id, password) <> (Account.tupled,
Account.unapply _)
def pk = primaryKey("pk_a", (station_id, member_id))
}
package models
import play.api.db.slick.Config.driver.simple._
case class Account(station_id: String, member_id: String,
password: String)
class Accounts(tag: Tag) extends Table[Account](tag, "ACCOUNT") {
def station_id = column[String]("STATION_ID")
def member_id = column[String]("MEMBER_ID")
def password = column[String]("PASSWORD")
def * = (station_id, member_id, password) <> (Account.tupled,
Account.unapply _)
def pk = primaryKey("pk_a", (station_id, member_id))
}
package models
import play.api.db.slick.Config.driver.simple._
case class Account(station_id: String, member_id: String,
password: String)
class Accounts(tag: Tag) extends Table[Account](tag, "ACCOUNT") {
def station_id = column[String]("STATION_ID")
def member_id = column[String]("MEMBER_ID")
def password = column[String]("PASSWORD")
def * = (station_id, member_id, password) <> (Account.tupled,
Account.unapply _)
def pk = primaryKey("pk_a", (station_id, member_id))
}](https://image.slidesharecdn.com/20150408slinkplay2-auth-150408023007-conversion-gate01/75/Play-Slick-play2-auth-9-2048.jpg)
![app/models/Account.scala #2app/models/Account.scala #2app/models/Account.scala #2app/models/Account.scala #2app/models/Account.scala #2
object Accounts {
val account = TableQuery[Accounts]
def authenticate(sid: String, mid: String, password: String):
Option[Account] = {
findById((sid, mid)).filter {
account => password.equals(account.password)
}
}
// xxx
def findById(smid: (String, String)): Option[Account] = None
// xxx
def findAll(): Seq[Account] = Seq.empty
// xxx
def create(account: Account) {
}
}
object Accounts {
val account = TableQuery[Accounts]
def authenticate(sid: String, mid: String, password: String):
Option[Account] = {
findById((sid, mid)).filter {
account => password.equals(account.password)
}
}
// xxx
def findById(smid: (String, String)): Option[Account] = None
// xxx
def findAll(): Seq[Account] = Seq.empty
// xxx
def create(account: Account) {
}
}
object Accounts {
val account = TableQuery[Accounts]
def authenticate(sid: String, mid: String, password: String):
Option[Account] = {
findById((sid, mid)).filter {
account => password.equals(account.password)
}
}
// xxx
def findById(smid: (String, String)): Option[Account] = None
// xxx
def findAll(): Seq[Account] = Seq.empty
// xxx
def create(account: Account) {
}
}
object Accounts {
val account = TableQuery[Accounts]
def authenticate(sid: String, mid: String, password: String):
Option[Account] = {
findById((sid, mid)).filter {
account => password.equals(account.password)
}
}
// xxx
def findById(smid: (String, String)): Option[Account] = None
// xxx
def findAll(): Seq[Account] = Seq.empty
// xxx
def create(account: Account) {
}
}
object Accounts {
val account = TableQuery[Accounts]
def authenticate(sid: String, mid: String, password: String):
Option[Account] = {
findById((sid, mid)).filter {
account => password.equals(account.password)
}
}
// xxx
def findById(smid: (String, String)): Option[Account] = None
// xxx
def findAll(): Seq[Account] = Seq.empty
// xxx
def create(account: Account) {
}
}](https://image.slidesharecdn.com/20150408slinkplay2-auth-150408023007-conversion-gate01/75/Play-Slick-play2-auth-10-2048.jpg)
![Application.scala #2Application.scala #2Application.scala #2Application.scala #2Application.scala #2
trait AuthConfigImpl extends AuthConfig {
type Id = (String, String)
type User = Account
val idTag: ClassTag[Id] = classTag[Id]
val sessionTimeoutInSeconds: Int = 3600
def resolveUser(id: Id)(implicit ctx: ExecutionContext): Future
[Option[User]] = Future.successful(Accounts.findById(id))
def loginSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def logoutSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authenticationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authorizationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Forbidden("no permission"))
def authorize(user: User, authority: Authority)(implicit ctx:
ExecutionContext): Future[Boolean] =
Future.successful(false) // xxx
trait AuthConfigImpl extends AuthConfig {
type Id = (String, String)
type User = Account
val idTag: ClassTag[Id] = classTag[Id]
val sessionTimeoutInSeconds: Int = 3600
def resolveUser(id: Id)(implicit ctx: ExecutionContext): Future
[Option[User]] = Future.successful(Accounts.findById(id))
def loginSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def logoutSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authenticationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authorizationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Forbidden("no permission"))
def authorize(user: User, authority: Authority)(implicit ctx:
ExecutionContext): Future[Boolean] =
Future.successful(false) // xxx
trait AuthConfigImpl extends AuthConfig {
type Id = (String, String)
type User = Account
val idTag: ClassTag[Id] = classTag[Id]
val sessionTimeoutInSeconds: Int = 3600
def resolveUser(id: Id)(implicit ctx: ExecutionContext): Future
[Option[User]] = Future.successful(Accounts.findById(id))
def loginSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def logoutSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authenticationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authorizationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Forbidden("no permission"))
def authorize(user: User, authority: Authority)(implicit ctx:
ExecutionContext): Future[Boolean] =
Future.successful(false) // xxx
trait AuthConfigImpl extends AuthConfig {
type Id = (String, String)
type User = Account
val idTag: ClassTag[Id] = classTag[Id]
val sessionTimeoutInSeconds: Int = 3600
def resolveUser(id: Id)(implicit ctx: ExecutionContext): Future
[Option[User]] = Future.successful(Accounts.findById(id))
def loginSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def logoutSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authenticationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authorizationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Forbidden("no permission"))
def authorize(user: User, authority: Authority)(implicit ctx:
ExecutionContext): Future[Boolean] =
Future.successful(false) // xxx
trait AuthConfigImpl extends AuthConfig {
type Id = (String, String)
type User = Account
val idTag: ClassTag[Id] = classTag[Id]
val sessionTimeoutInSeconds: Int = 3600
def resolveUser(id: Id)(implicit ctx: ExecutionContext): Future
[Option[User]] = Future.successful(Accounts.findById(id))
def loginSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def logoutSucceeded(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authenticationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Redirect(routes.Application.login))
def authorizationFailed(request: RequestHeader)(implicit ctx:
ExecutionContext): Future[Result] =
Future.successful(Forbidden("no permission"))
def authorize(user: User, authority: Authority)(implicit ctx:
ExecutionContext): Future[Boolean] =
Future.successful(false) // xxx](https://image.slidesharecdn.com/20150408slinkplay2-auth-150408023007-conversion-gate01/75/Play-Slick-play2-auth-14-2048.jpg)