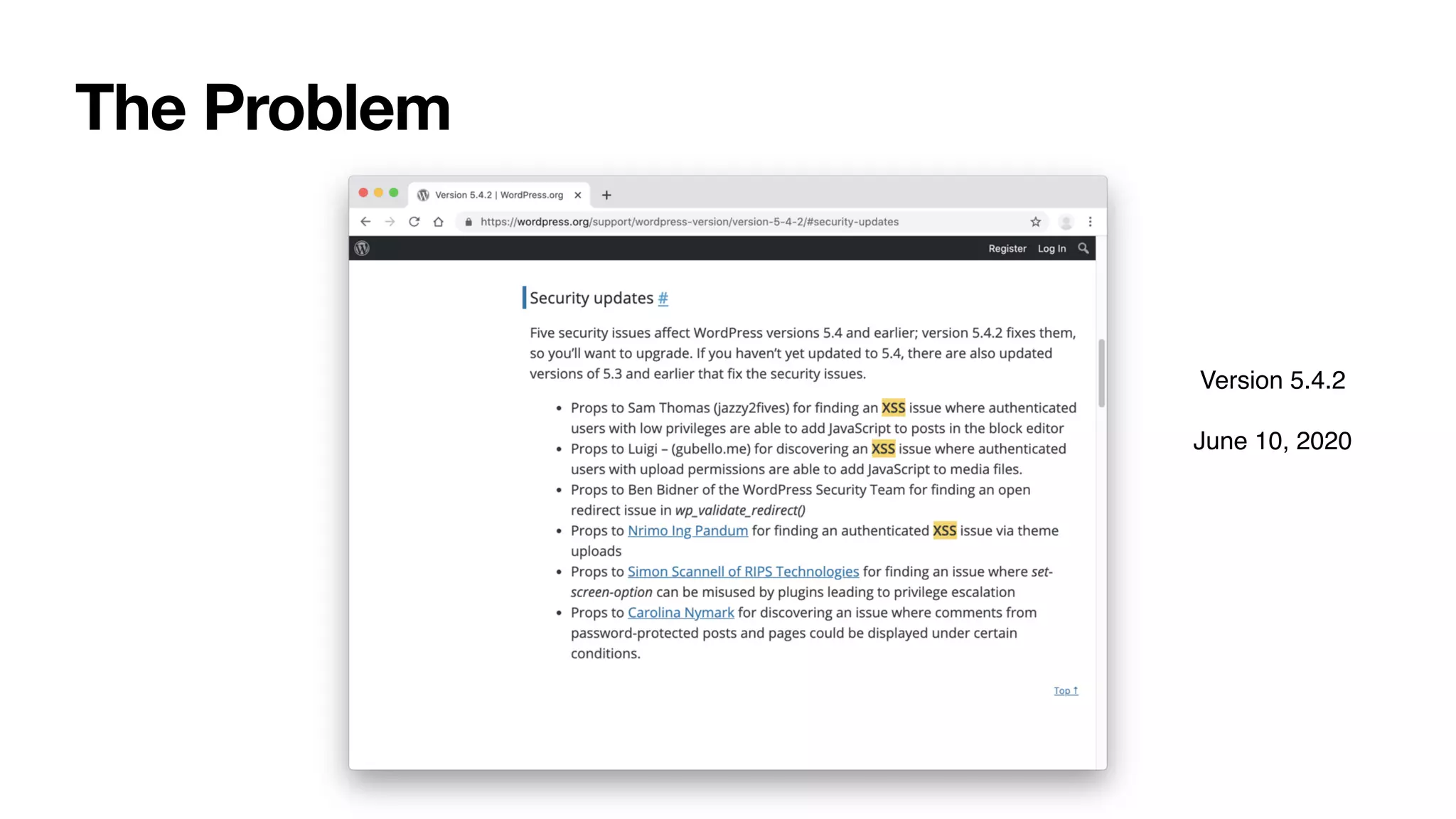
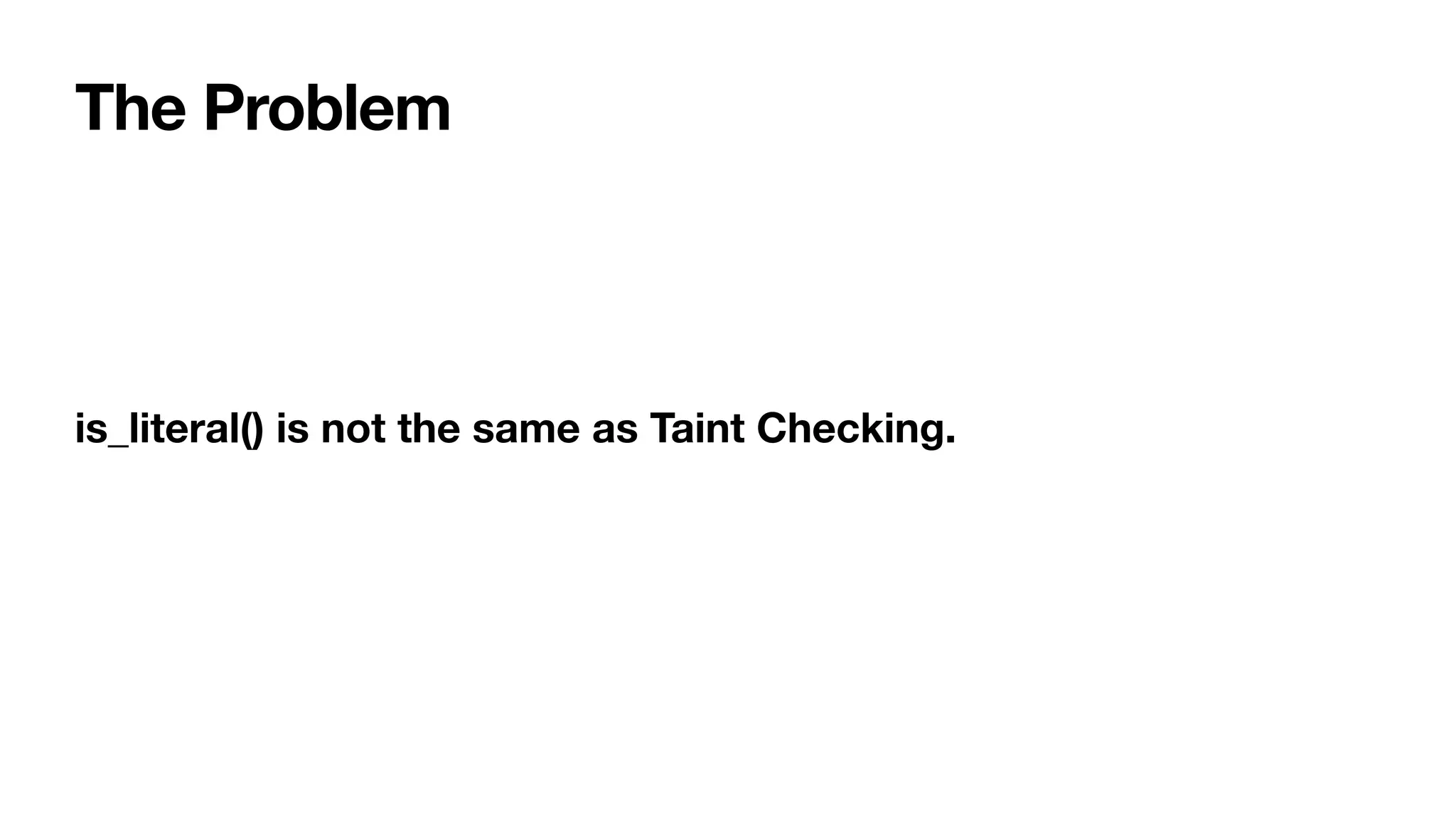
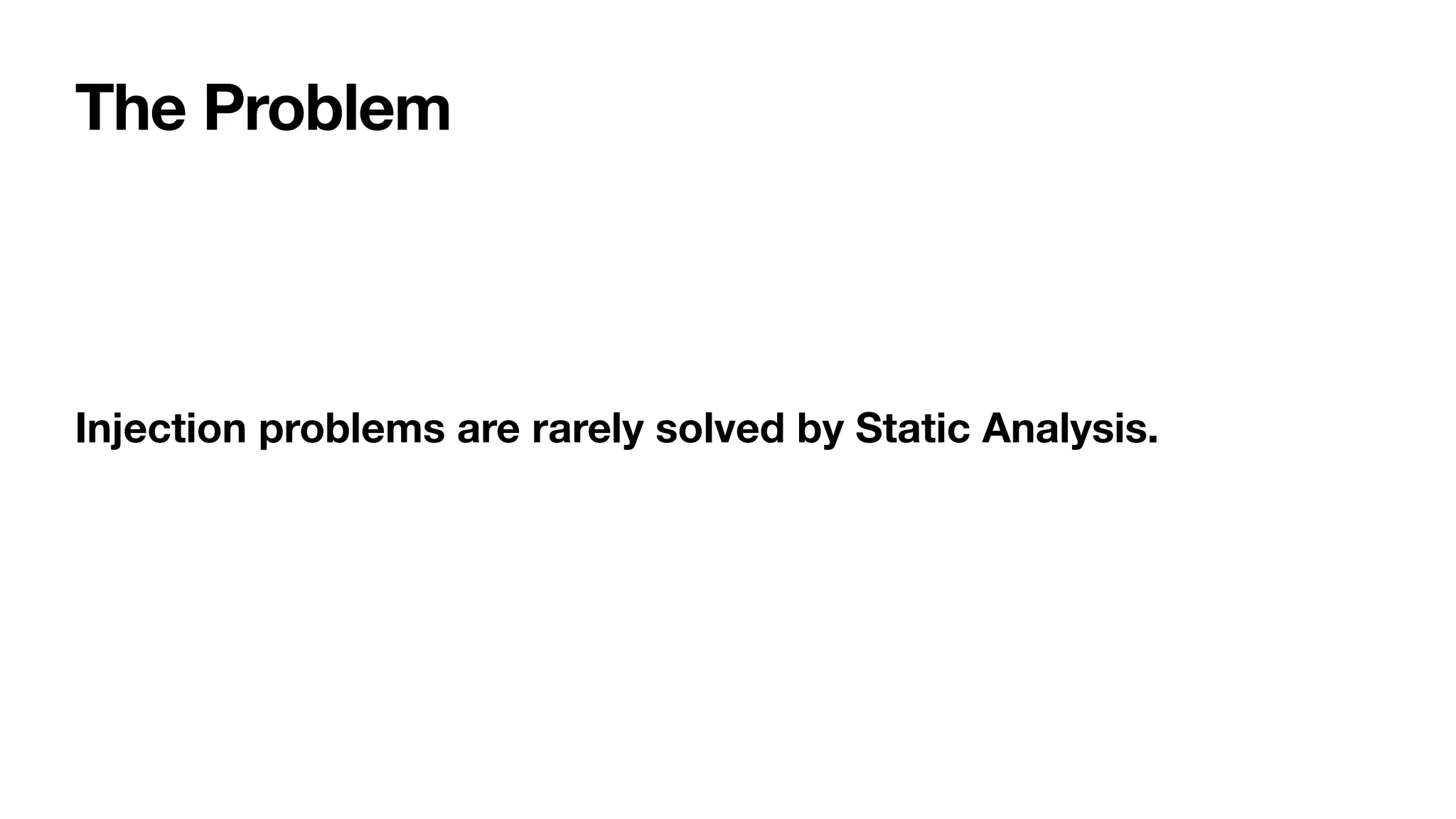
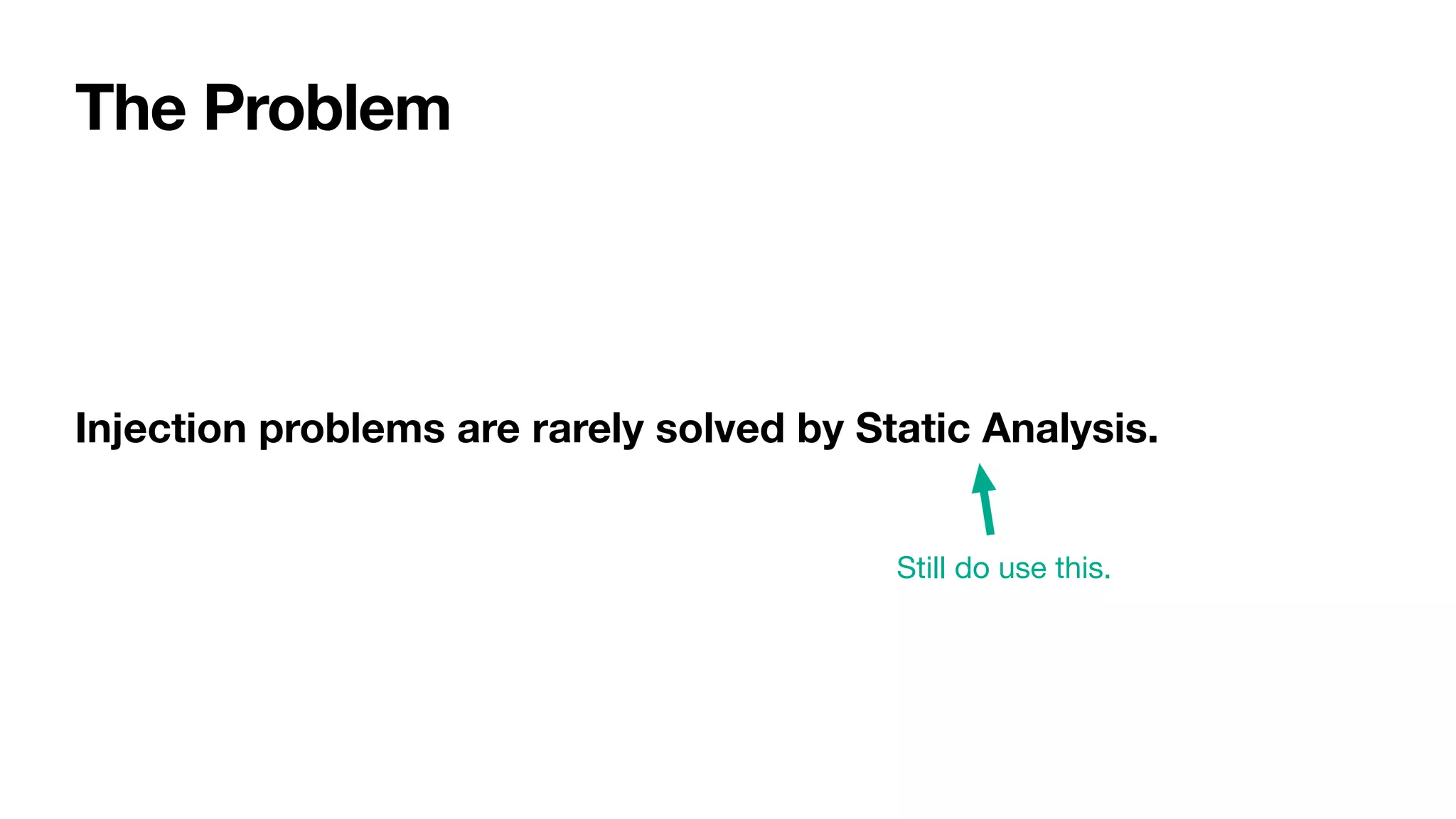
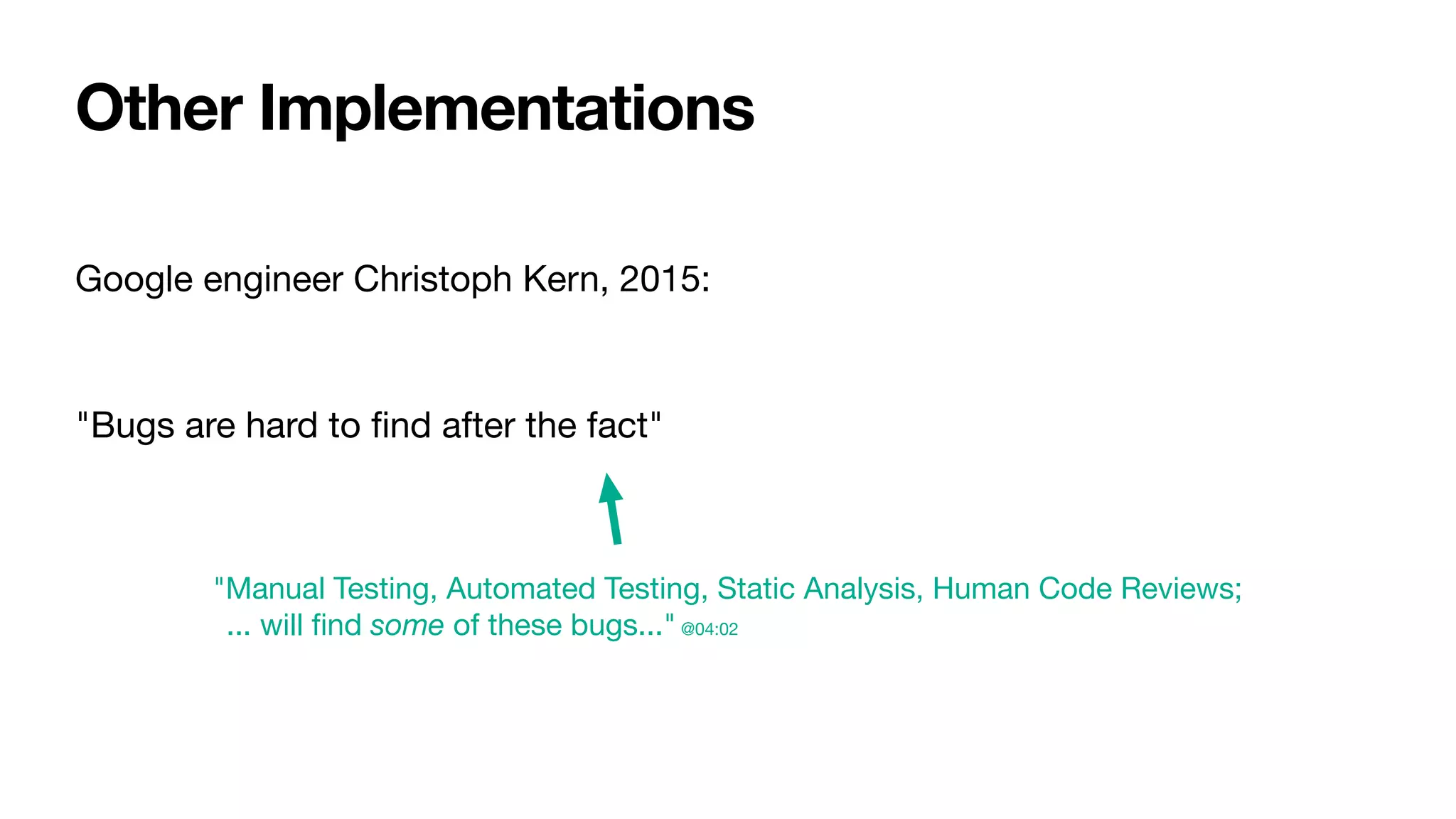
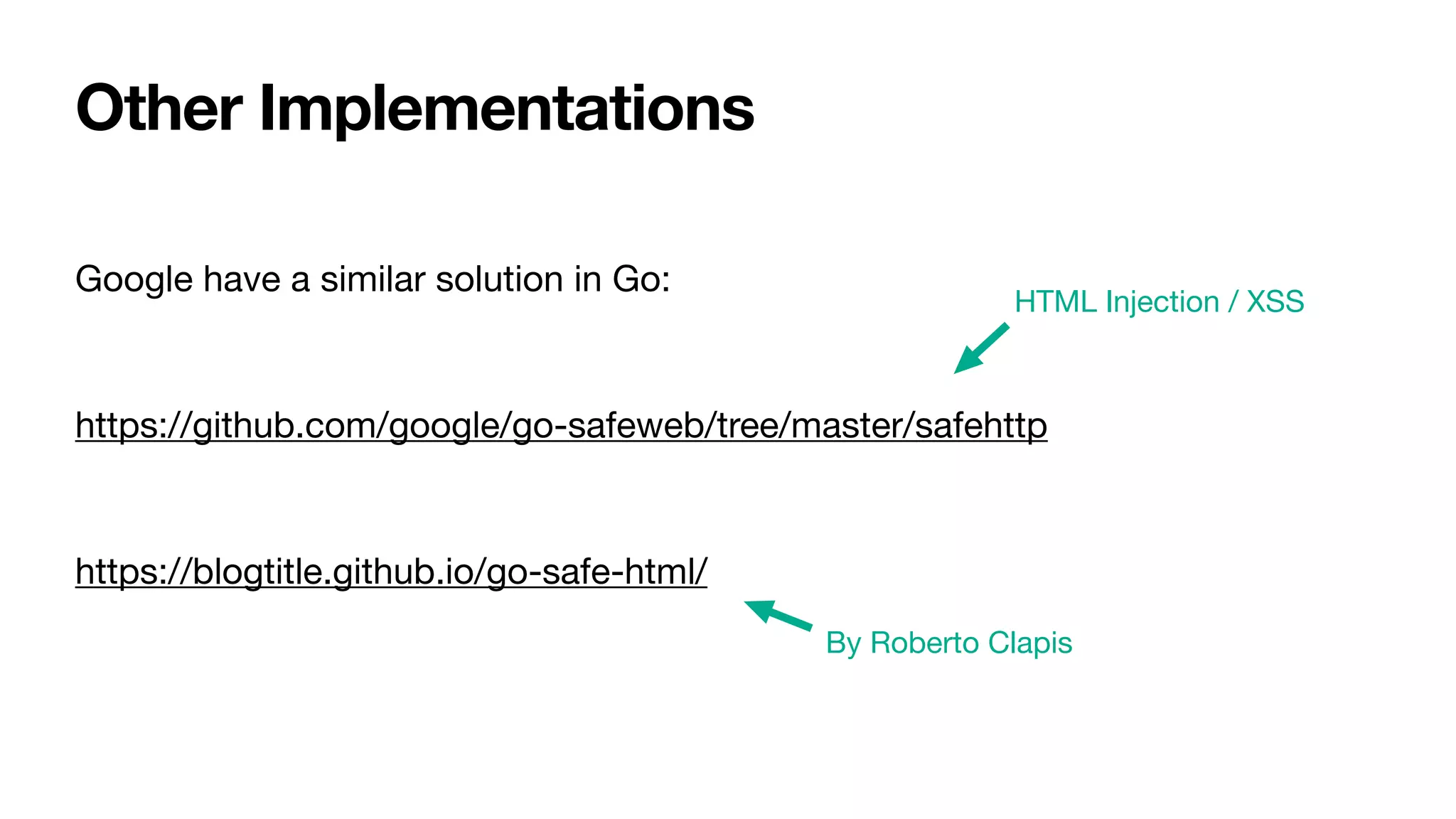
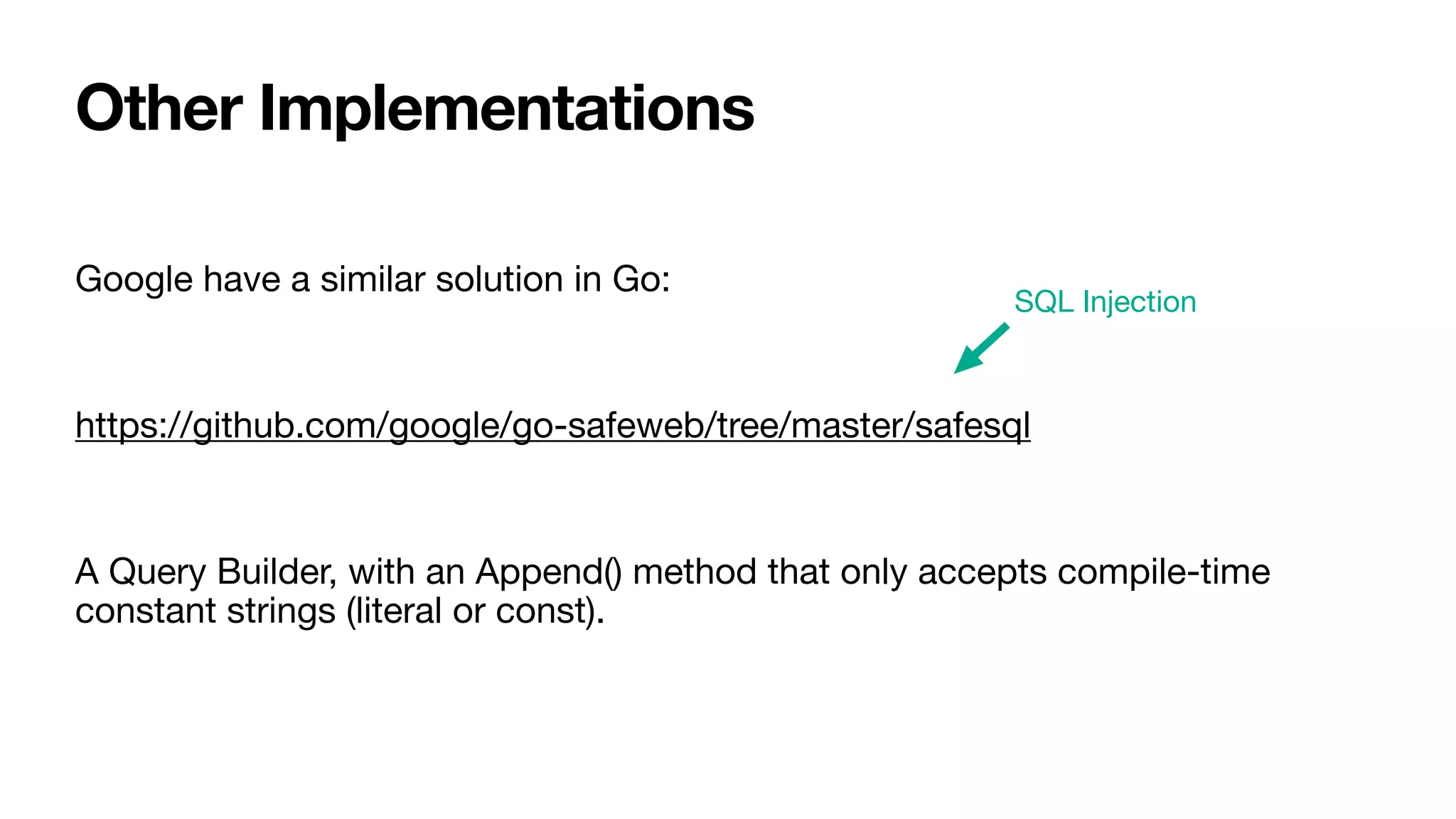
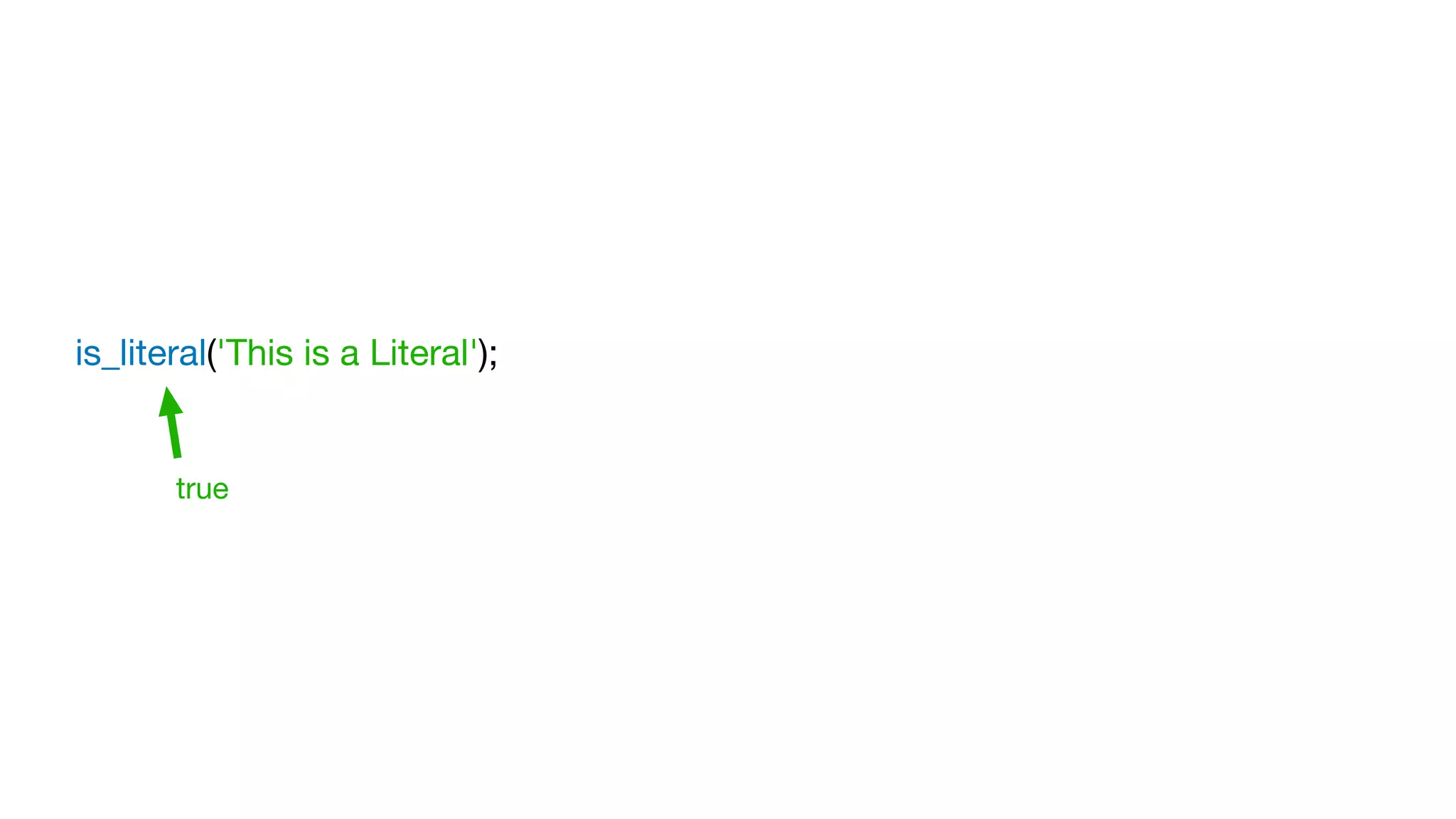
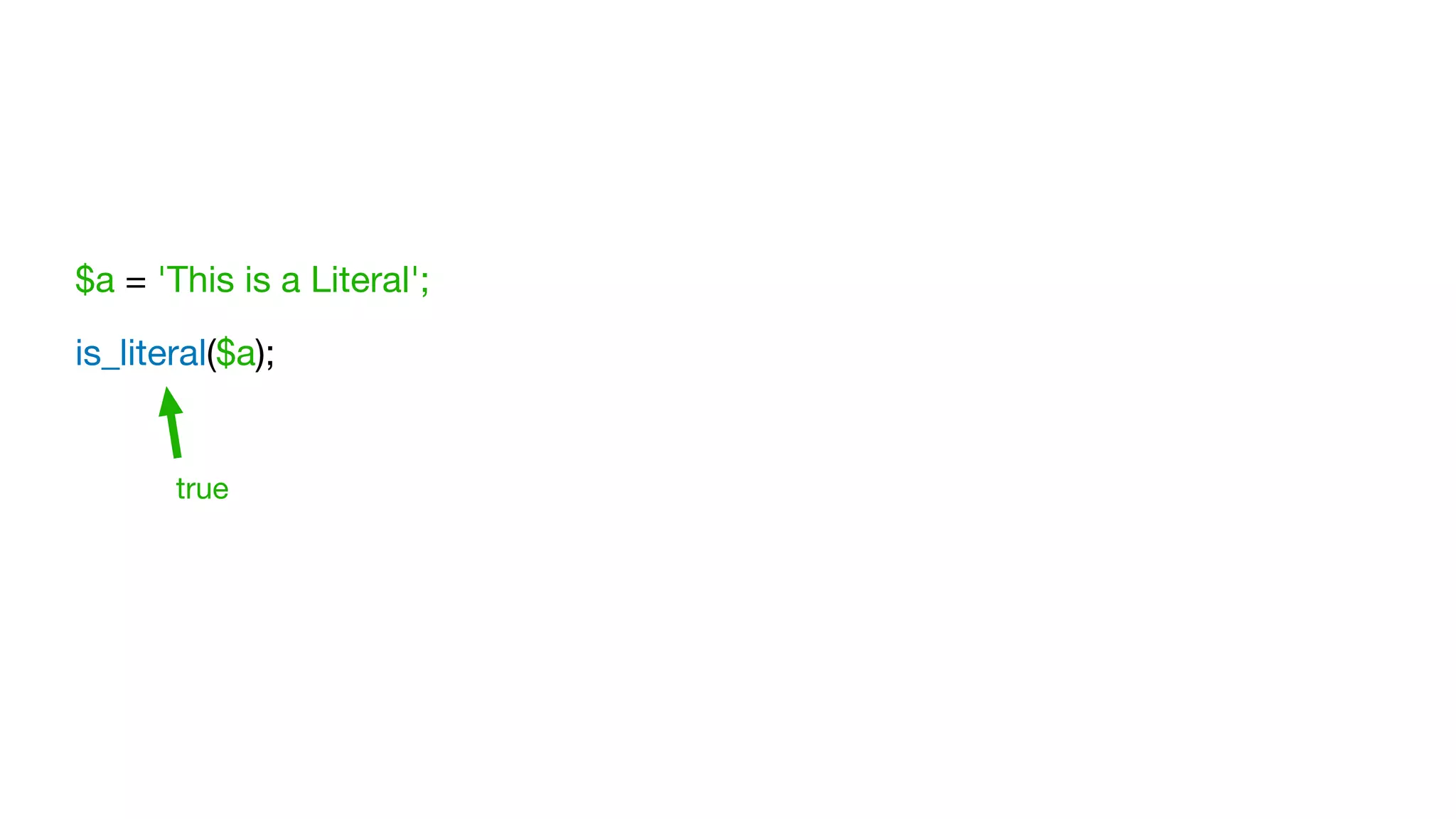
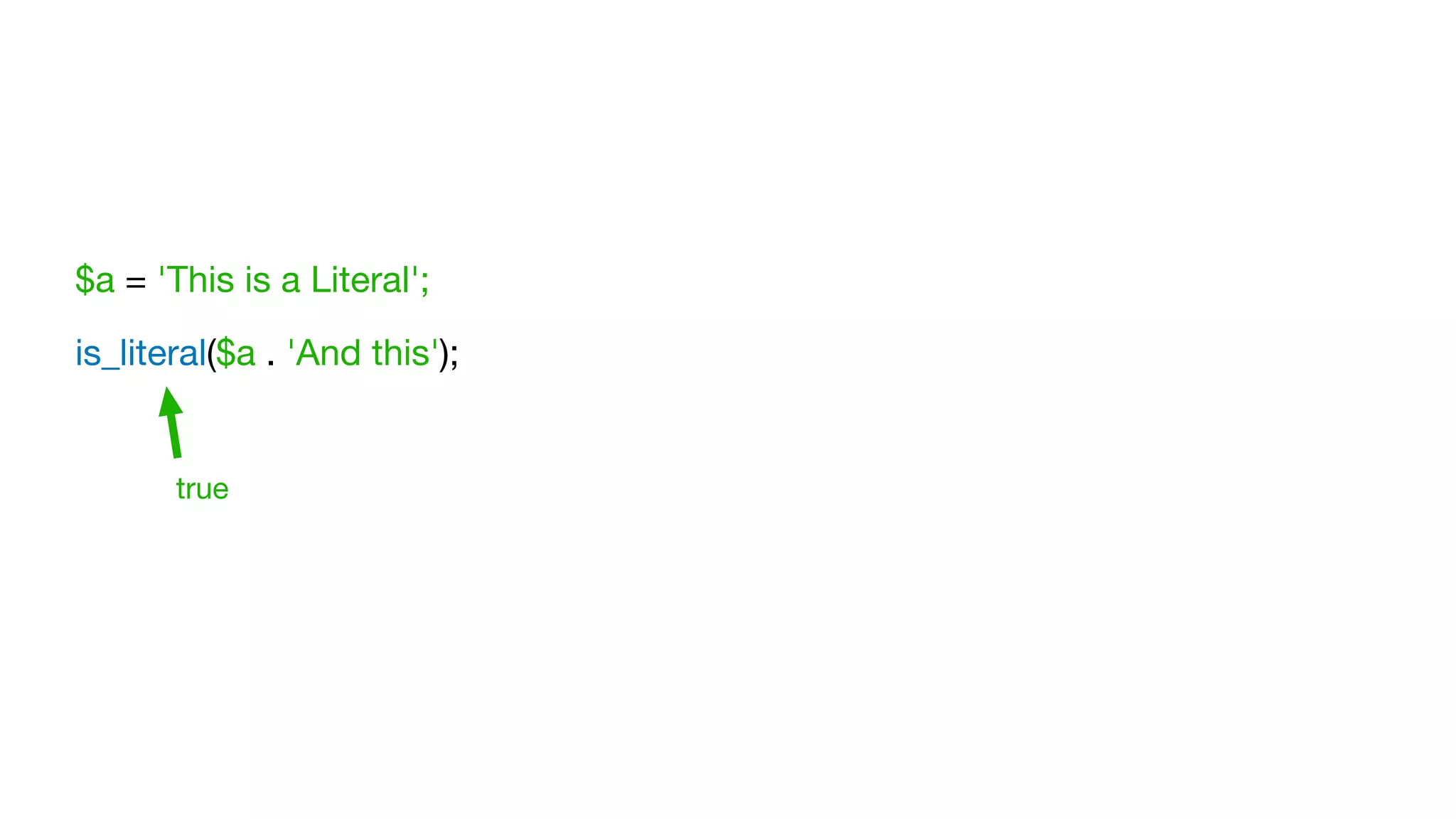
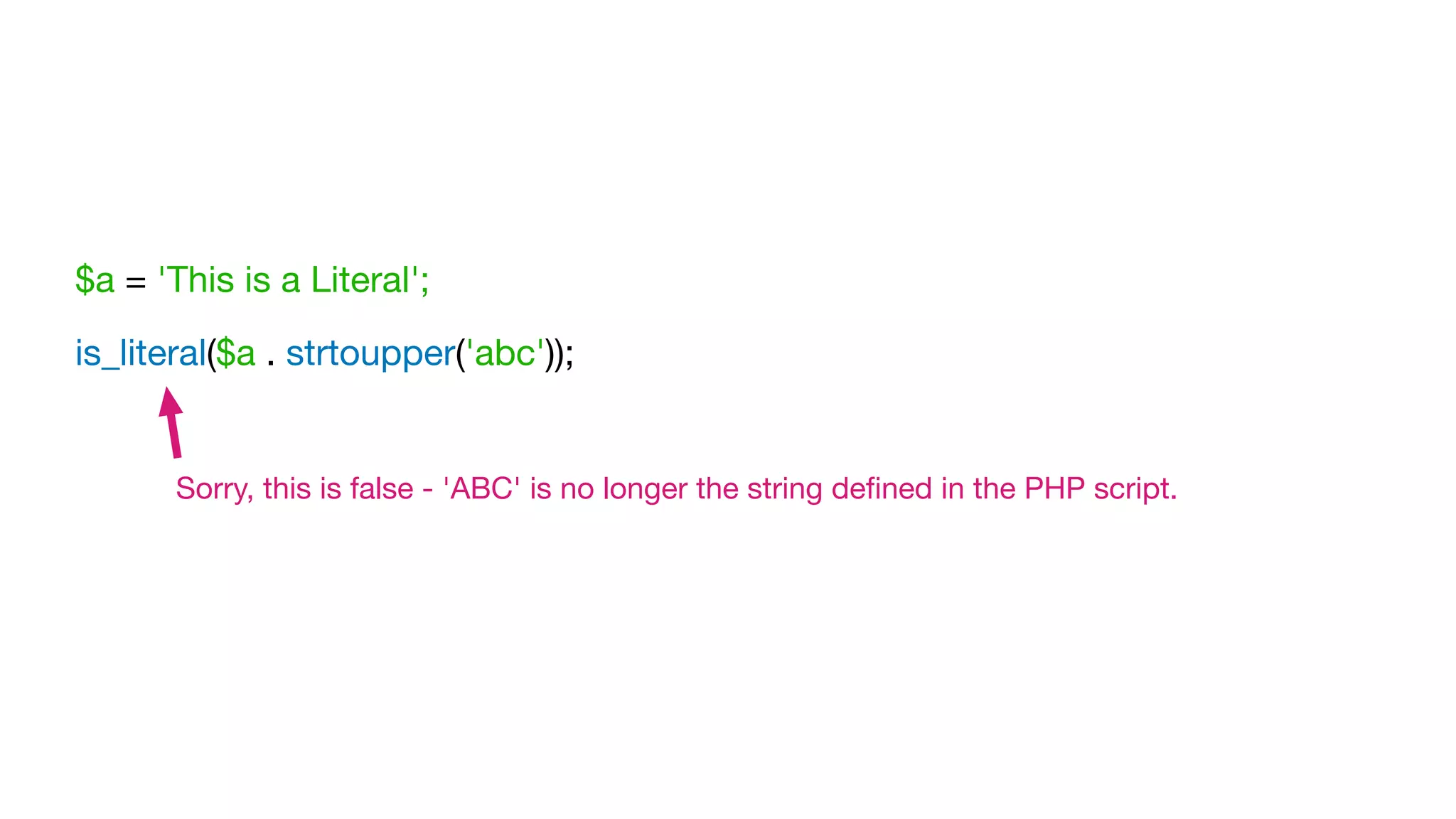
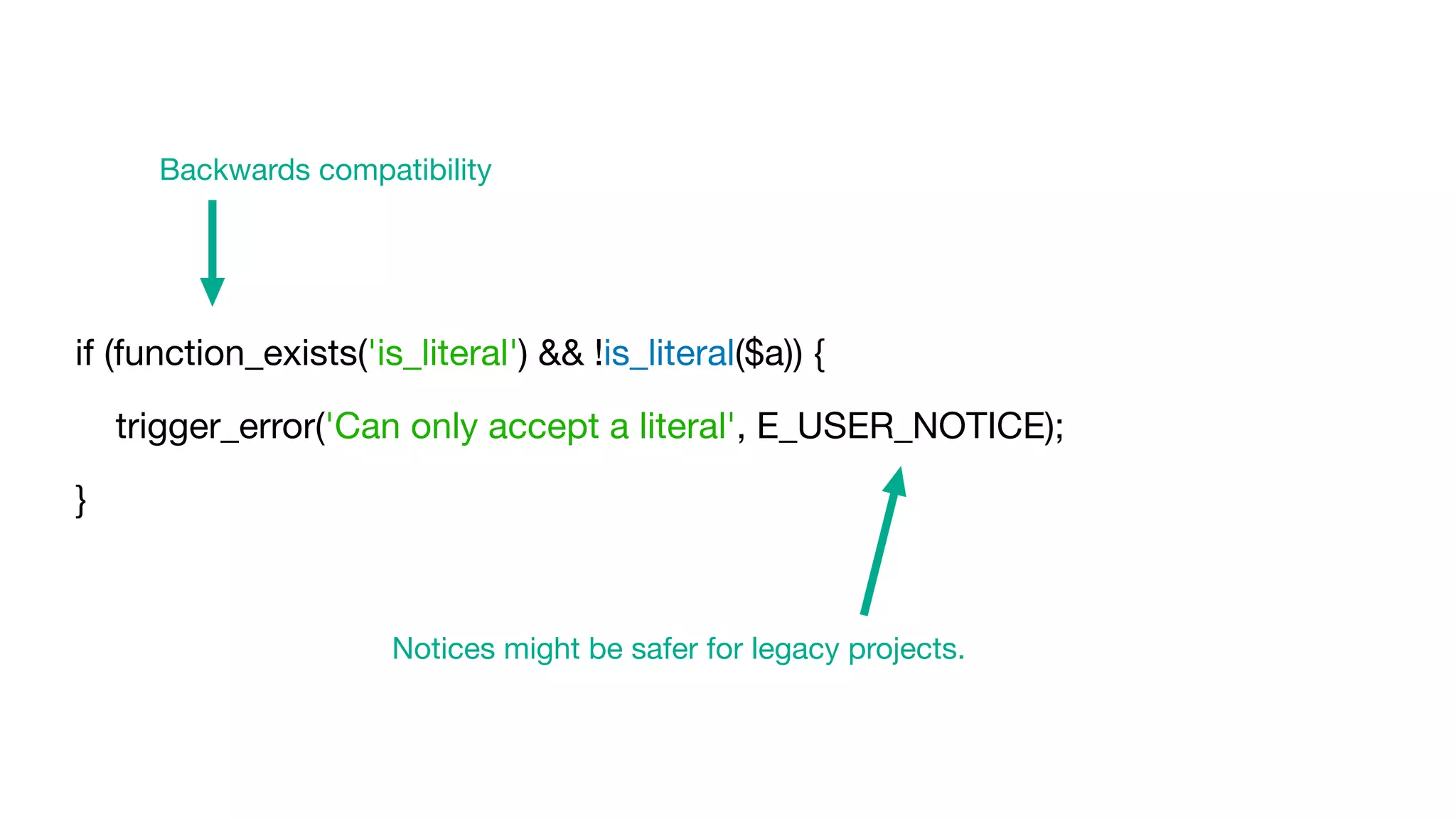
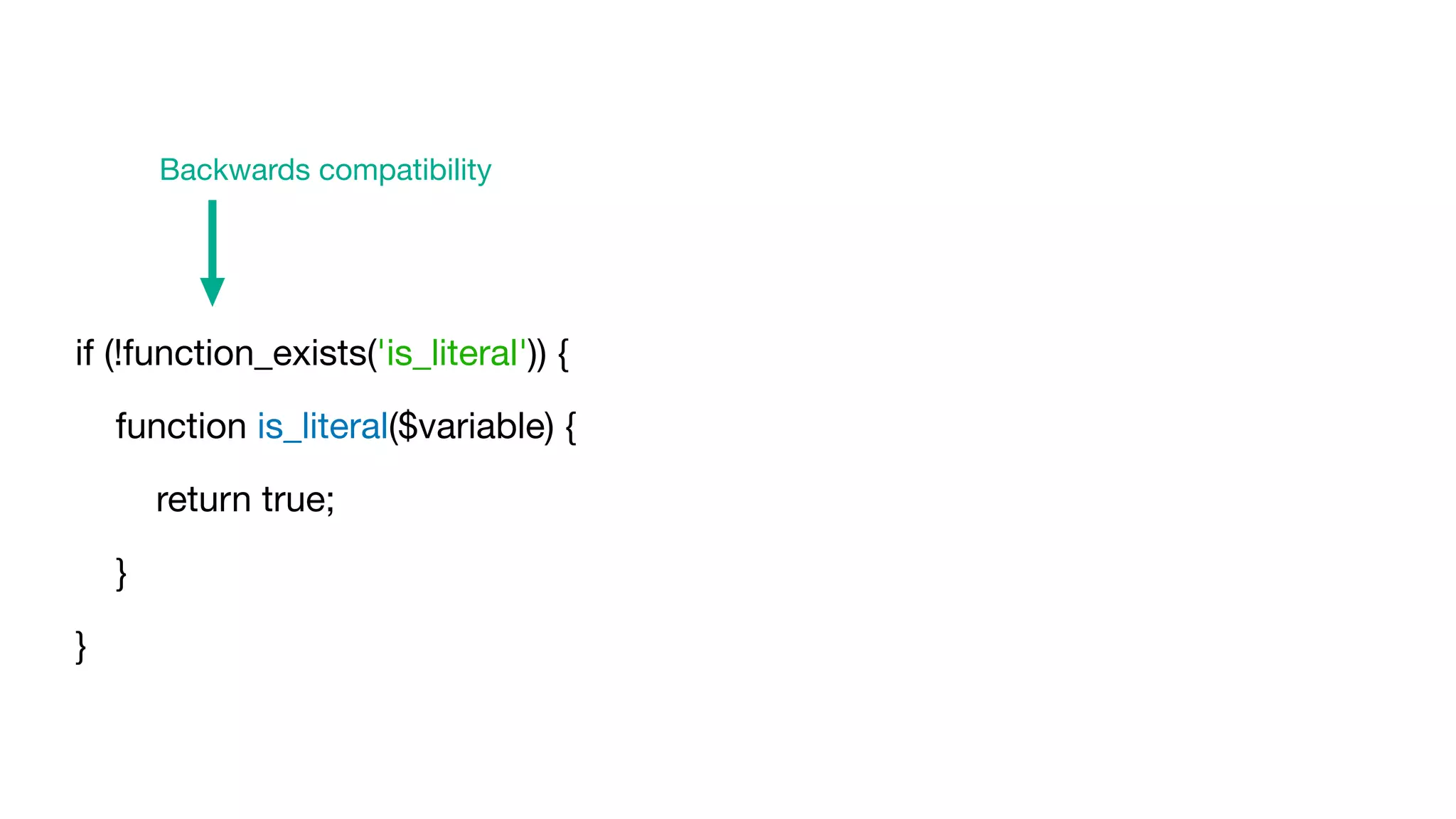
The document proposes the is_literal() function for PHP to differentiate safe strings defined in scripts from unsafe strings, particularly those tainted by external sources. It emphasizes that injection problems are not effectively resolved by static analysis and suggests that the function can improve string safety. The document also discusses examples and implications of the function in various coding scenarios, including its necessity for preventing SQL injection and XSS vulnerabilities.
![$mysqli = new mysqli('localhost', 'test', '???', 'test');
$result = $mysqli->query('SELECT * FROM user WHERE id = ' . $_GET['id']);
if ($result instanceof mysqli_result) {
print_r($result->fetch_all());
}
Static Analysis
PHPStan](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-14-2048.jpg)
![$mysqli = new mysqli('localhost', 'test', '???', 'test');
$id = (string) $_GET['id'];
$result = $mysqli->query('SELECT * FROM user WHERE id = ' . $id);
if ($result instanceof mysqli_result) {
print_r($result->fetch_all());
}
Static Analysis
Avoid MixedAssignment
Psalm](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-15-2048.jpg)
![$mysqli = new mysqli('localhost', 'test', '???', 'test');
$id = (string) $_GET['id'];
$result = $mysqli->query('SELECT * FROM user WHERE id = ' . $id);
if ($result instanceof mysqli_result) {
print_r($result->fetch_all());
}
Static Analysis
Psalm,
Taint Analysis
I'm not using "mysqli_query()"
https://github.com/vimeo/psalm/issues/4155
Avoid MixedAssignment](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-16-2048.jpg)
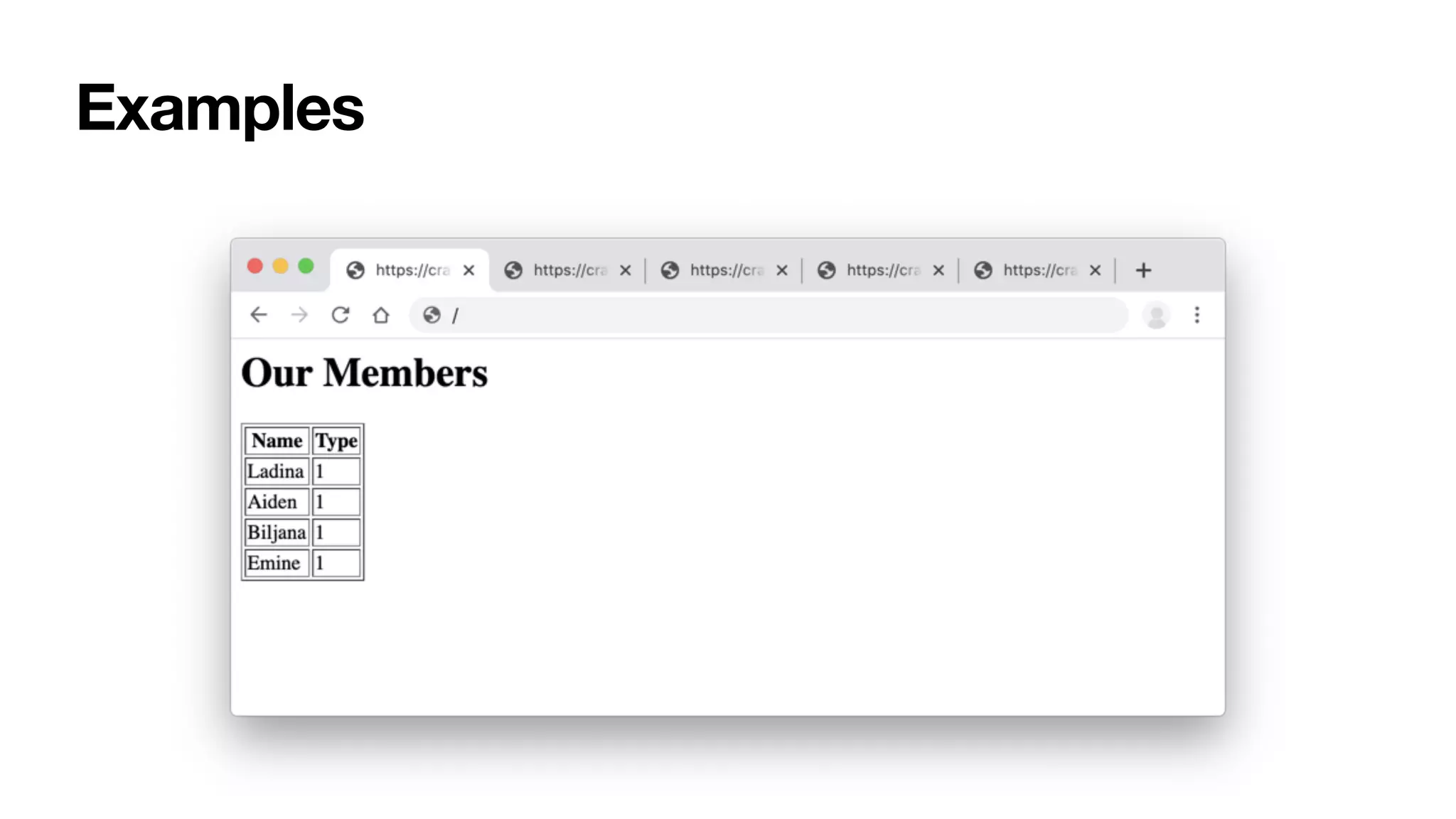
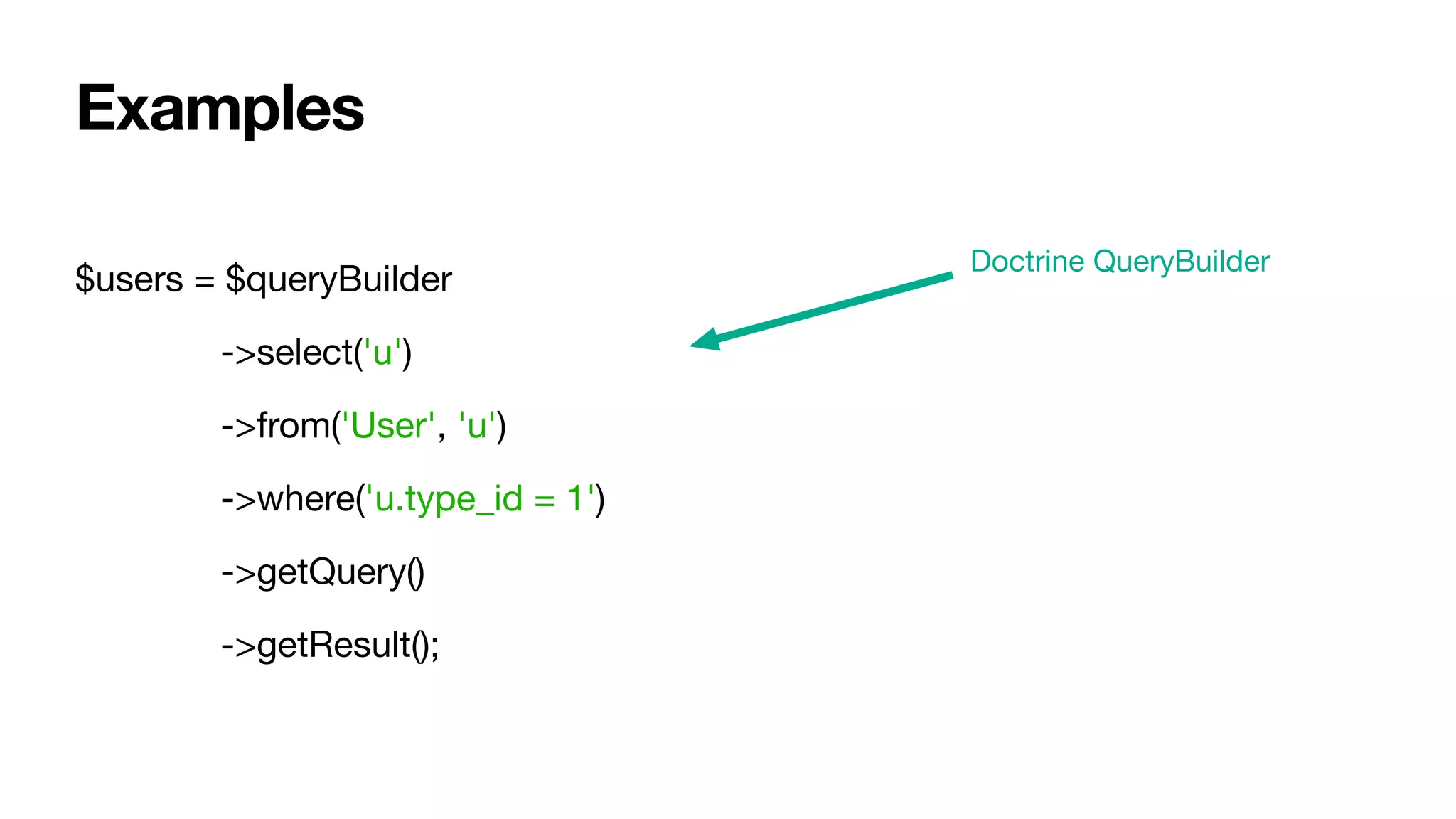
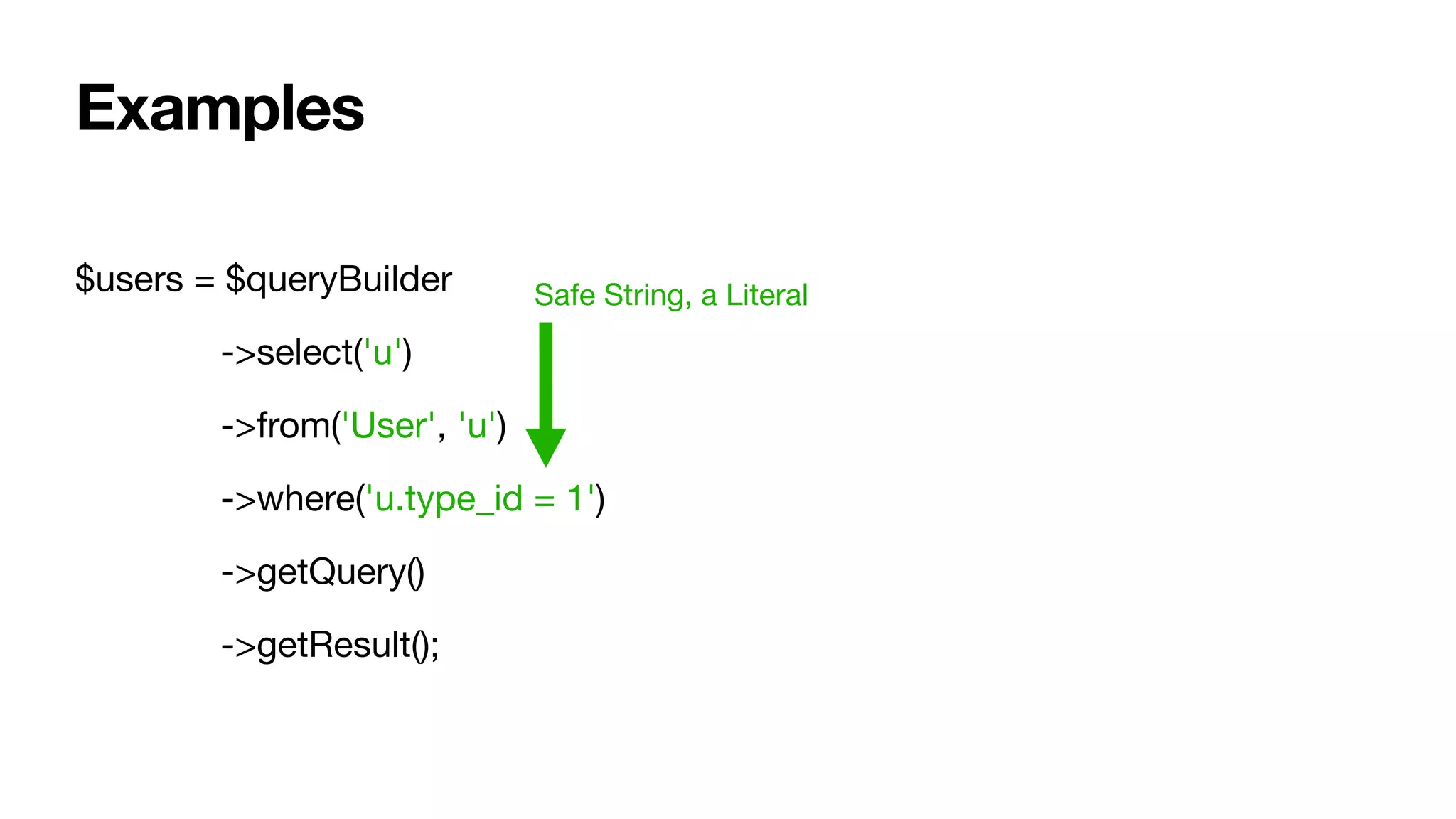
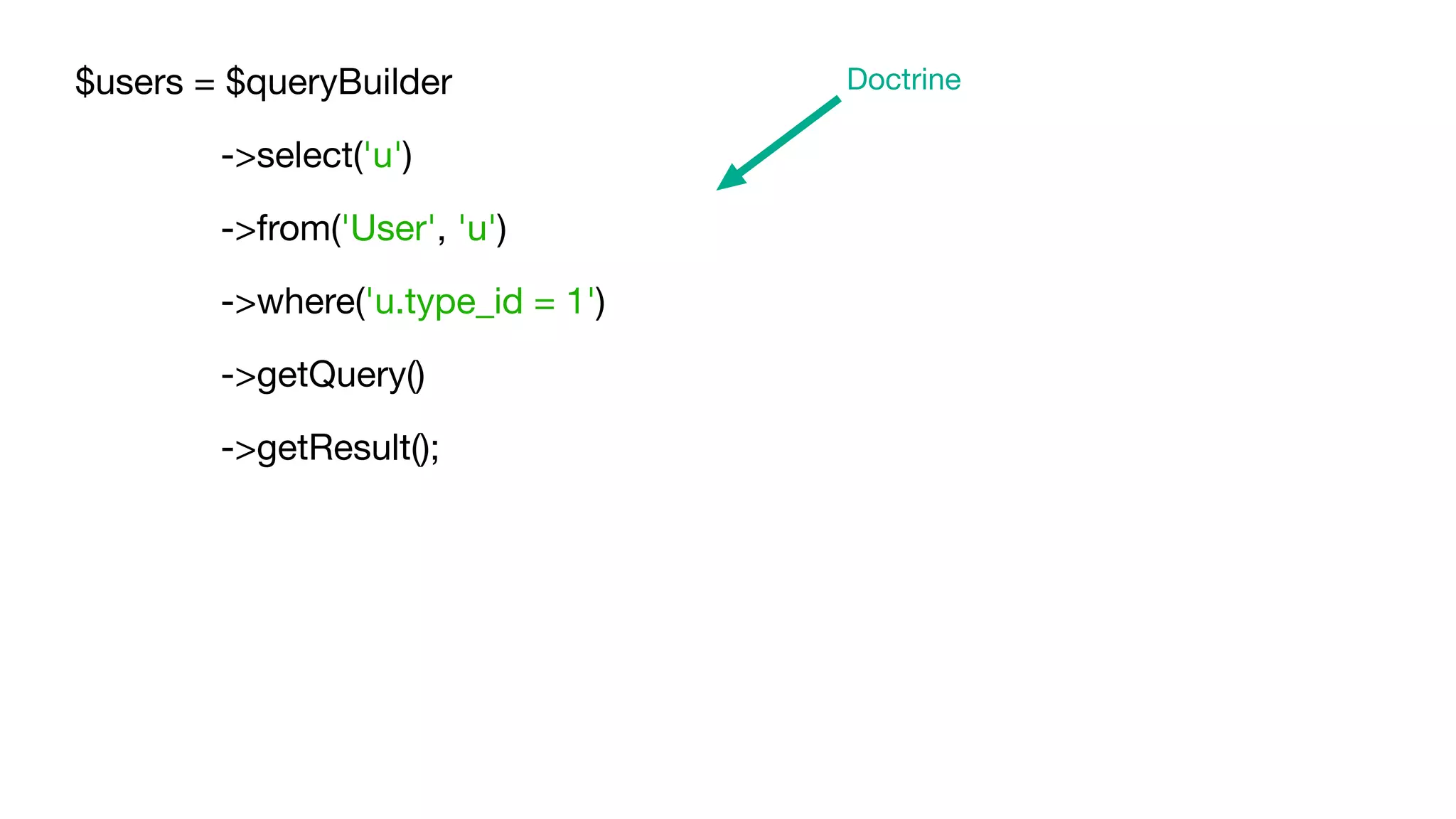
![$users = $queryBuilder
->select('u')
->from('User', 'u')
->where('u.type_id = ?1')
->setParameter(1, $_GET['type_id'])
->getQuery()
->getResult();
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-28-2048.jpg)
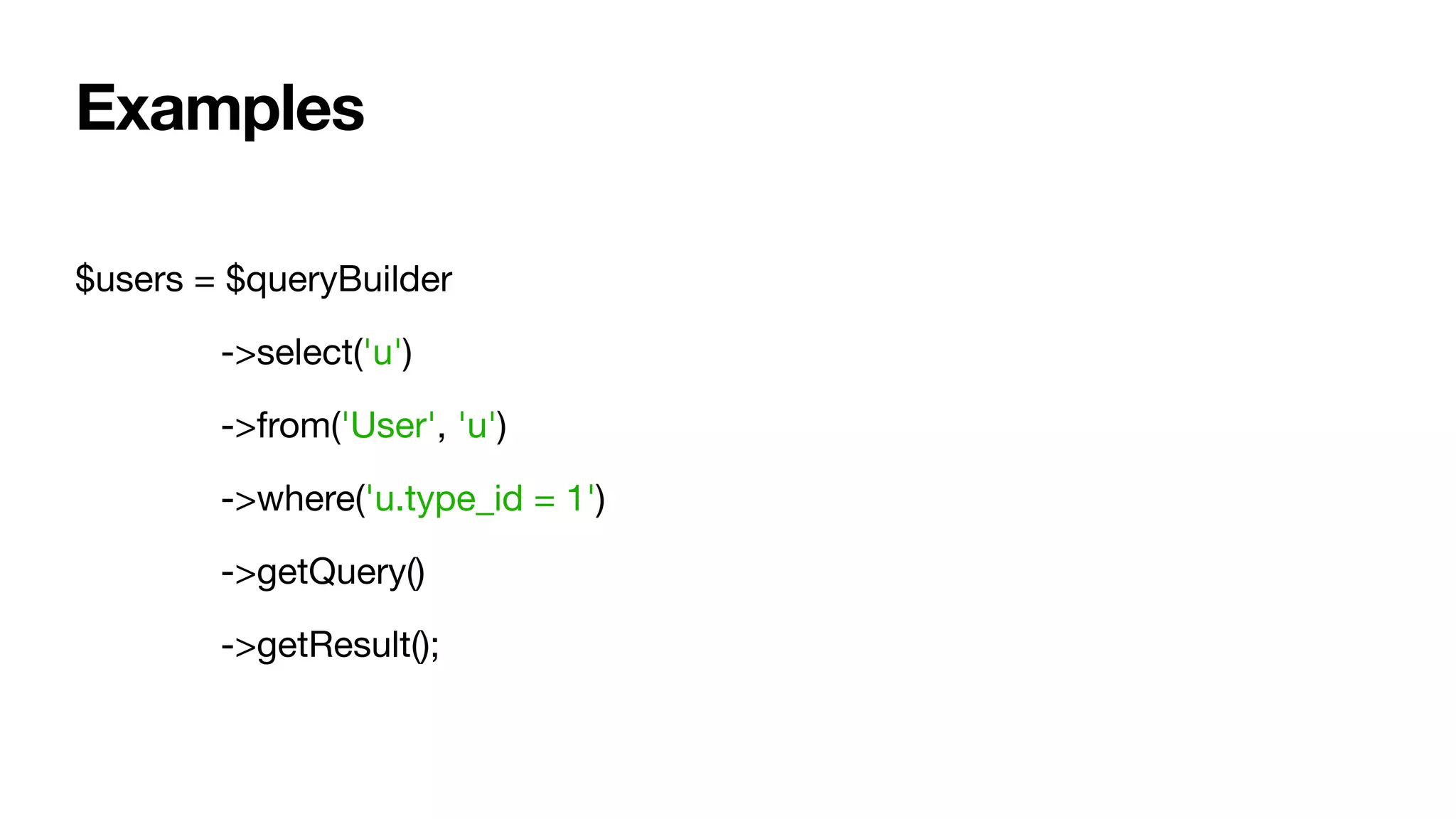
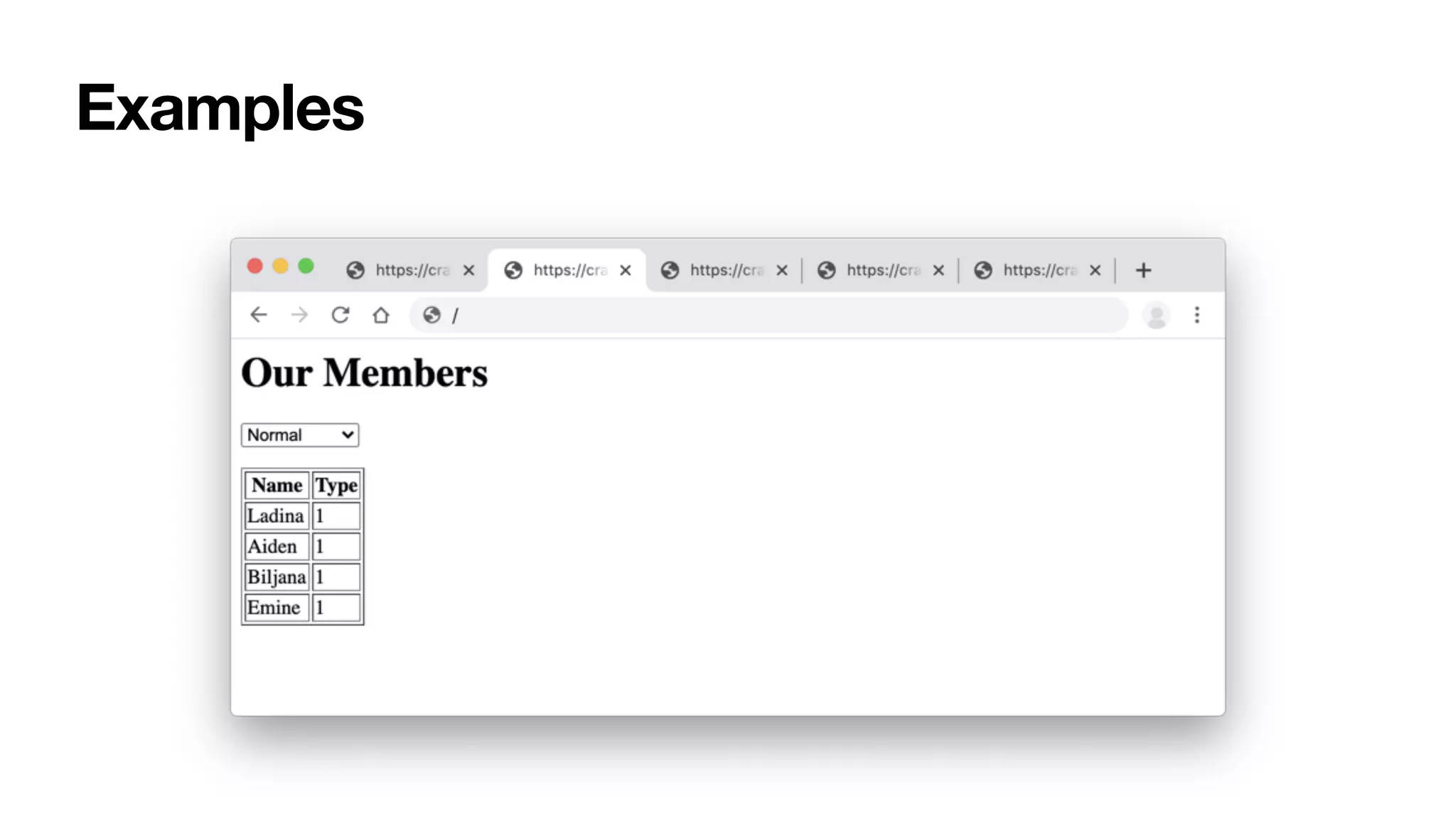
![$users = $queryBuilder
->select('u')
->from('User', 'u')
->where('u.type_id = ' . $_GET['type_id'])
->getQuery()
->getResult();
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-30-2048.jpg)
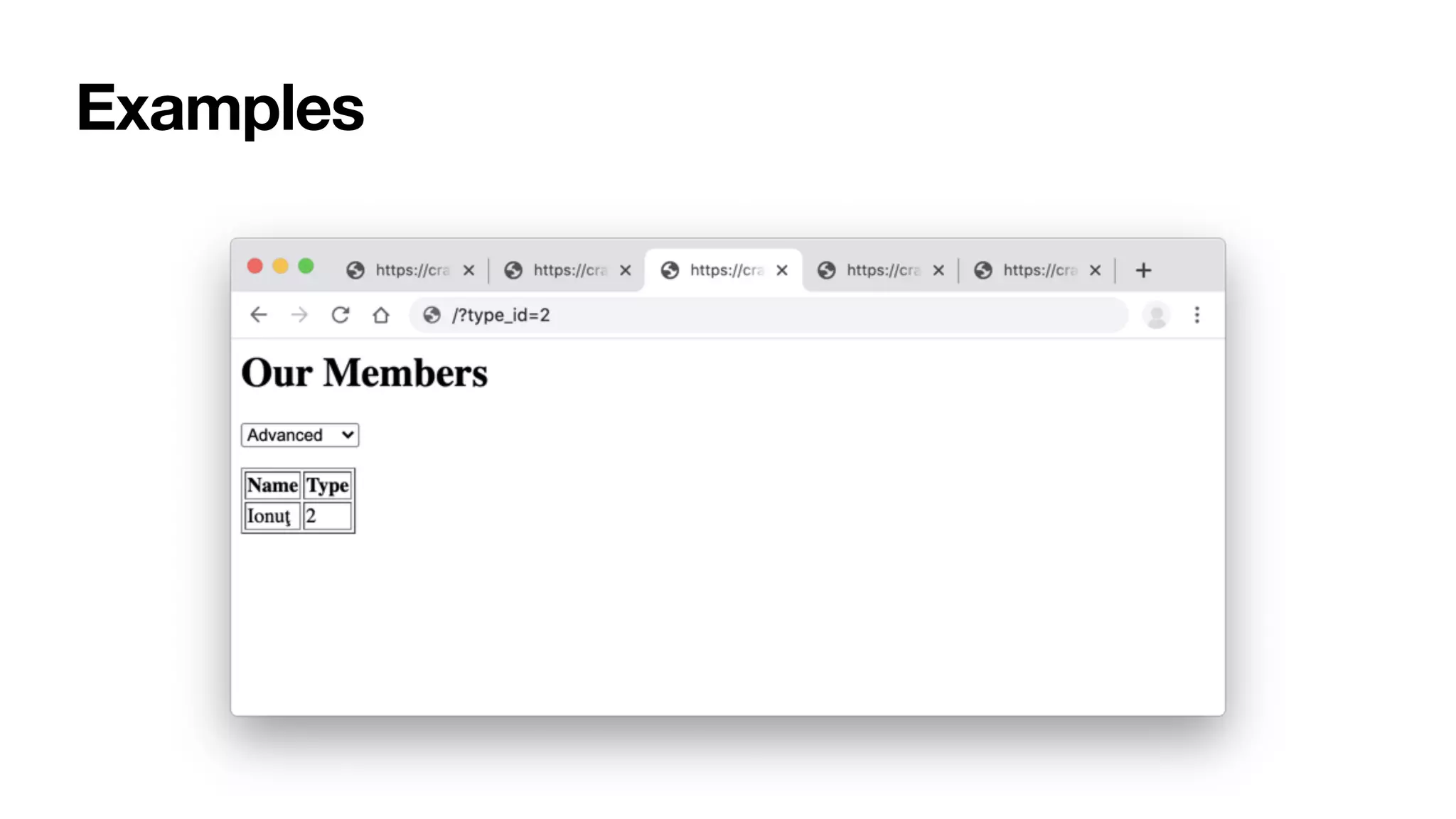
![$users = $queryBuilder
->select('u')
->from('User', 'u')
->where('u.type_id = ' . $_GET['type_id'])
->getQuery()
->getResult();
Unsafe StringSafe String
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-34-2048.jpg)
![$users = $queryBuilder
->select('u')
->from('User', 'u')
->where('u.type_id = ' . $_GET['type_id'])
->getQuery()
->getResult();
Examples
'WHERE u.type_id = u.type_id'](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-35-2048.jpg)
![$sql = 'SELECT u FROM User u WHERE u.type_id = ' . $_GET['type_id'];
$query = $entityManager->createQuery($sql);
Doctrine - CreateQuery
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-36-2048.jpg)
![$users = UserQuery::create()->where('type_id = ' . $_GET['type_id'])->find();
Propel ORM - Where
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-37-2048.jpg)
![$result = R::find('user', 'type_id = ' . $_GET['type_id']);
RedBeanPHP - Find
Examples](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-38-2048.jpg)
![$template = $twig->createTemplate('<p>Hello {{ name }}</p>');
echo $template->render(['name' => $_GET['name']]);
Examples Safe String, a Literal](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-39-2048.jpg)
![$template = $twig->createTemplate('<p>Hello ' . $_GET['name'] . '</p>');
echo $template->render();
Examples Unsafe String](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-40-2048.jpg)
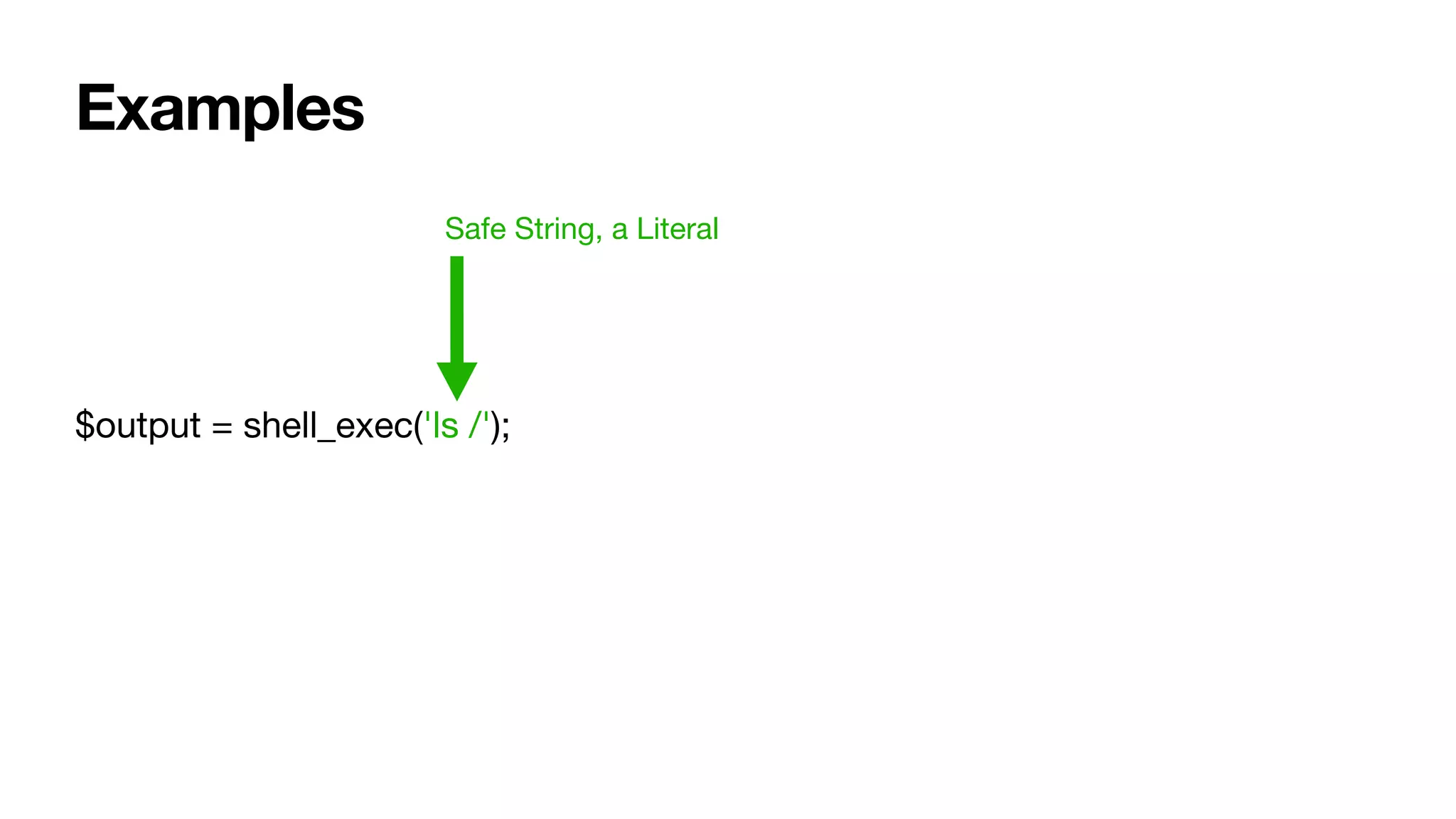
![Examples
$output = shell_exec('ls ' . $_GET['path']);
Unsafe String](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-43-2048.jpg)
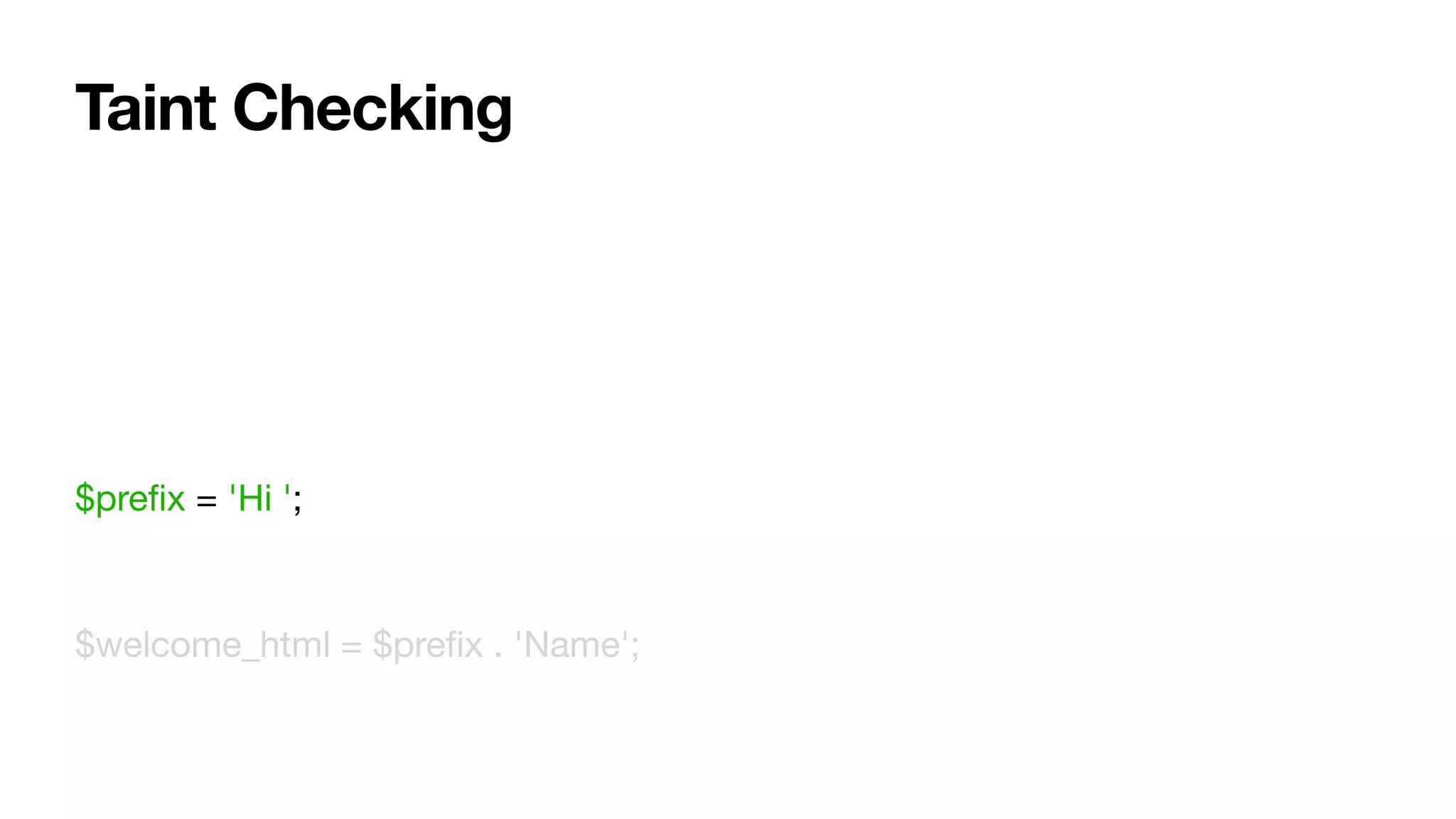
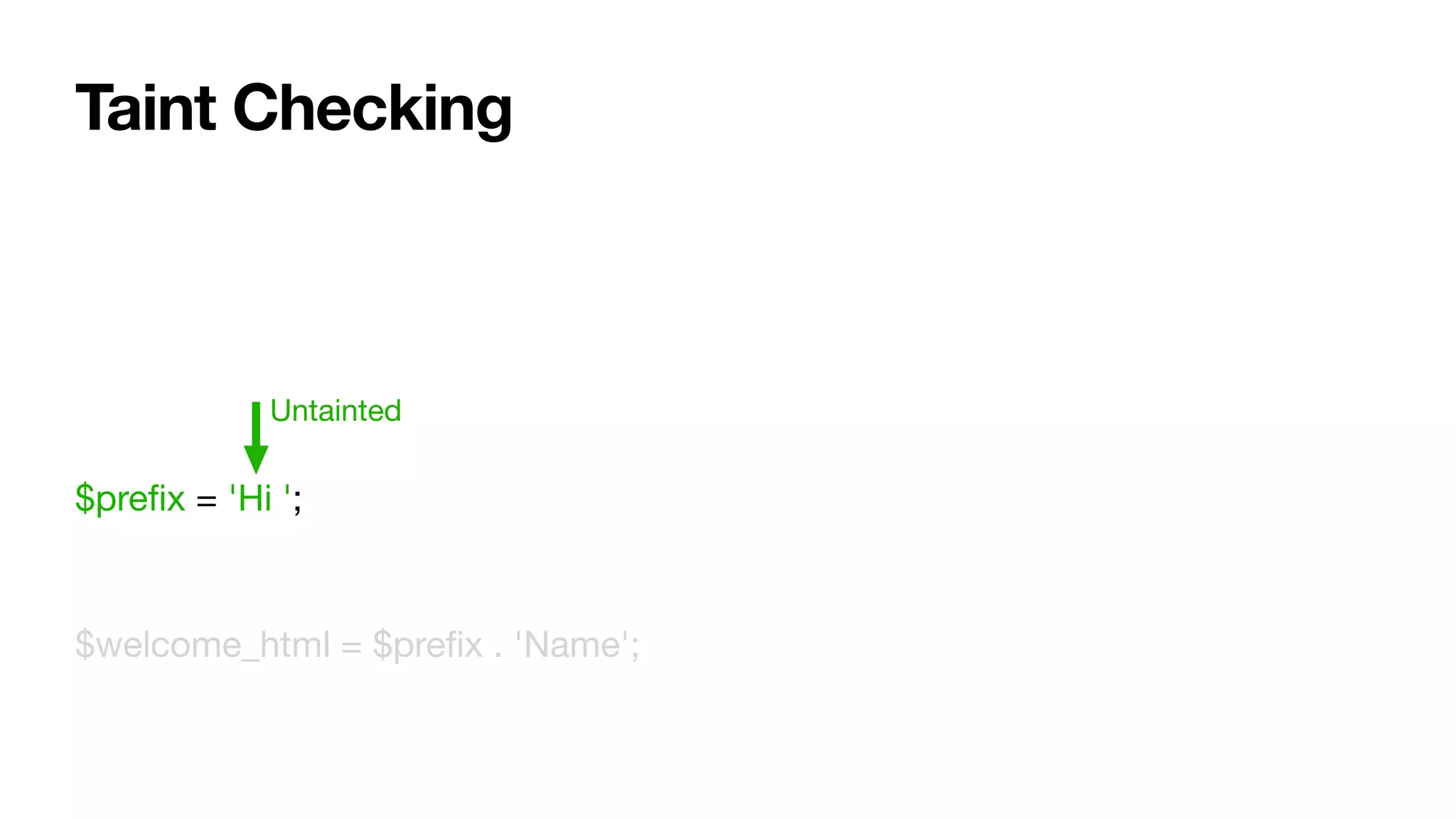
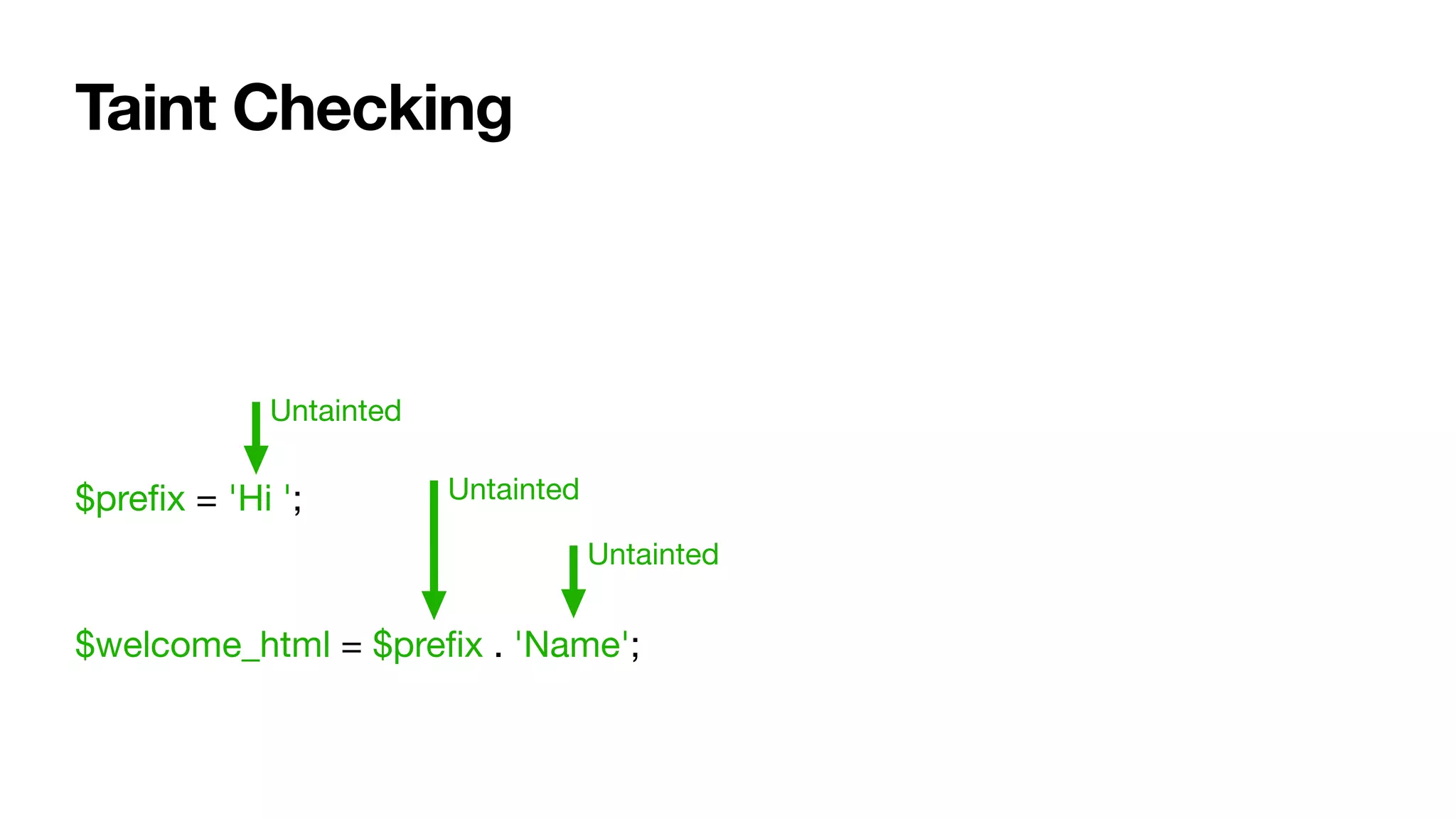
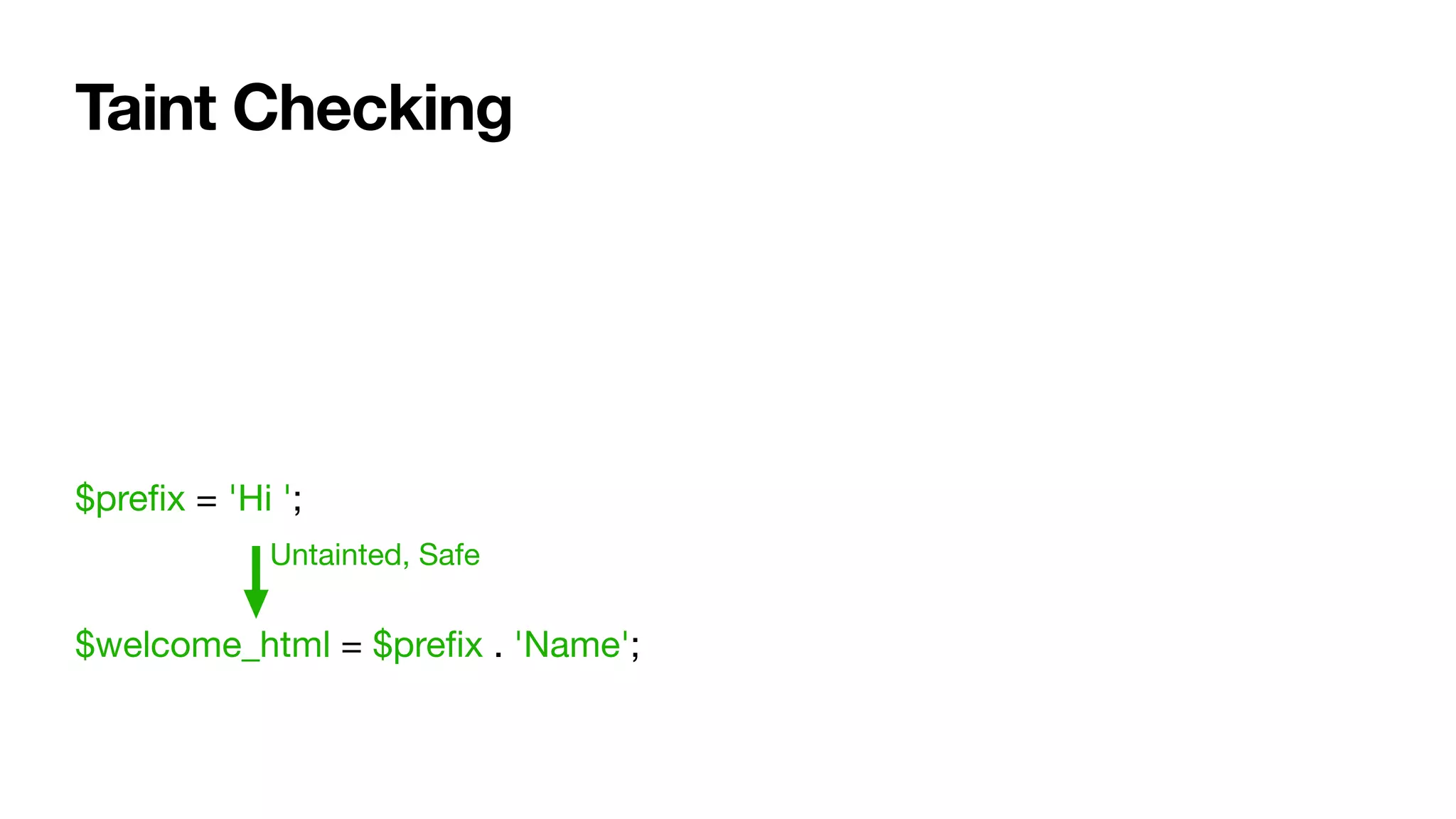
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-49-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;
Tainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-50-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-51-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;
Untainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-52-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;
Untainted
Tainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-53-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . $name;
Tainted, not safe](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-54-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . htmlentities($name);](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-55-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . htmlentities($name);
Un-Taint](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-56-2048.jpg)
![Taint Checking
$name = $_GET['name'];
$prefix = 'Hi ';
$welcome_html = $prefix . htmlentities($name);
Untainted, should be safe.](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-57-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-58-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';
Tainted
Tainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-59-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';
Tainted Tainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-60-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';
Un-Taint Un-Taint](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-61-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';
Untainted, surely this is safe?](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-62-2048.jpg)
![Taint Checking
$url = $_GET['url'];
$name = $_GET['name'];
$link_html = '<a href="' . htmlentities($url) . '">' . htmlentities($name) . '</a>';
'javascript:alert("hi")'](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-63-2048.jpg)
![Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);
Tainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-64-2048.jpg)
![Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);
Untainted Un-Taint](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-65-2048.jpg)
![Untainted, surely this is safe?
Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-66-2048.jpg)
![Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);
Missing quotes](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-67-2048.jpg)
![Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);
"id"](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-68-2048.jpg)
![Taint Checking
$sql .= 'WHERE id = ' . mysqli_real_escape_string($link, $_GET['id']);
$sql .= 'WHERE id = id';
"id"](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-69-2048.jpg)
![Taint Checking
$img_html = '<img src=' . htmlentities($_GET['url']) . '>';
TaintedUntainted Untainted](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-70-2048.jpg)
![Taint Checking
$img_html = '<img src=' . htmlentities($_GET['url']) . '>';
Un-Taint](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-71-2048.jpg)
![Taint Checking
$img_html = '<img src=' . htmlentities($_GET['url']) . '>';
Untainted, surely this is safe?](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-72-2048.jpg)
![Taint Checking
$img_html = '<img src=' . htmlentities($_GET['url']) . '>';
Missing quotes](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-73-2048.jpg)
![Taint Checking
$img_html = '<img src=' . htmlentities($_GET['url']) . '>';
$img_html = '<img src=/ onerror=evil-js>';
"/ onerror=evil-js"](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-74-2048.jpg)
![$a = 'This is a Literal';
is_literal($a . $_GET['name']);
false](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-82-2048.jpg)
![$a = 'This is a Literal';
is_literal($a . htmlentities($_GET['name']));
Still false](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-83-2048.jpg)
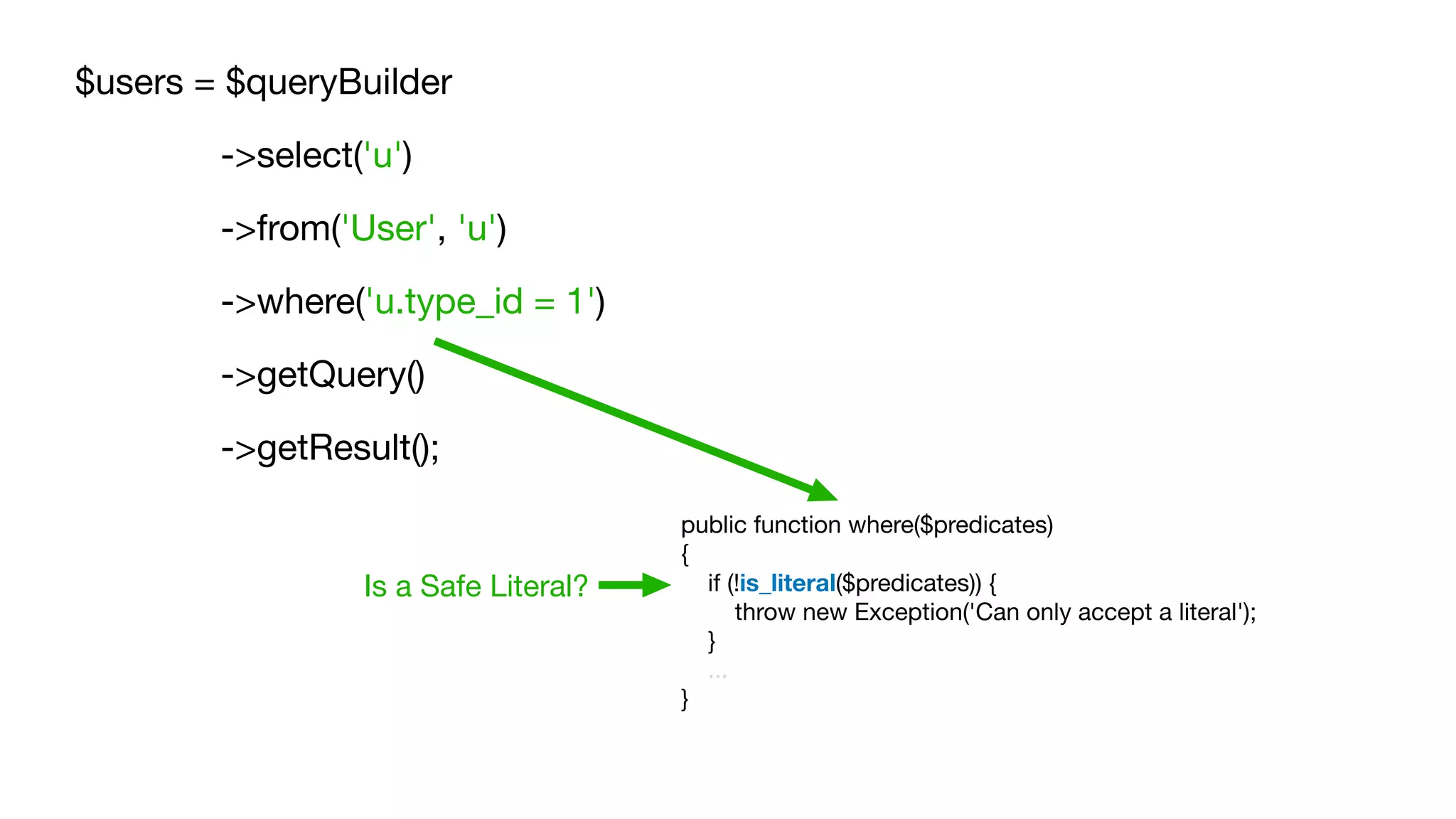
![$users = $queryBuilder
->select('u')
->from('User', 'u')
->where('u.type_id = ' . $_GET['type_id'])
->getQuery()
->getResult();
public function where($predicates)
{
if (!is_literal($predicates)) {
throw new Exception('Can only accept a literal');
}
...
}
Not a Safe Literal](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-87-2048.jpg)
![$template = $twig->createTemplate('<p>Hello {{ name }}</p>');
echo $template->render(['name' => $_GET['name']]);
Twig](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-88-2048.jpg)
![$template = $twig->createTemplate('<p>Hello {{ name }}</p>');
echo $template->render(['name' => $_GET['name']])
public function createTemplate(string $template, string $name = null): TemplateWrapper
{
if (!is_literal($template)) {
throw new Exception('Can only accept a literal');
}
...
}
Is a Safe Literal?](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-89-2048.jpg)
![$template = $twig->createTemplate('<p>Hello ' . $_GET['name'] . '</p>');
echo $template->render()
public function createTemplate(string $template, string $name = null): TemplateWrapper
{
if (!is_literal($template)) {
throw new Exception('Can only accept a literal');
}
...
}
Not a Safe Literal](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-90-2048.jpg)
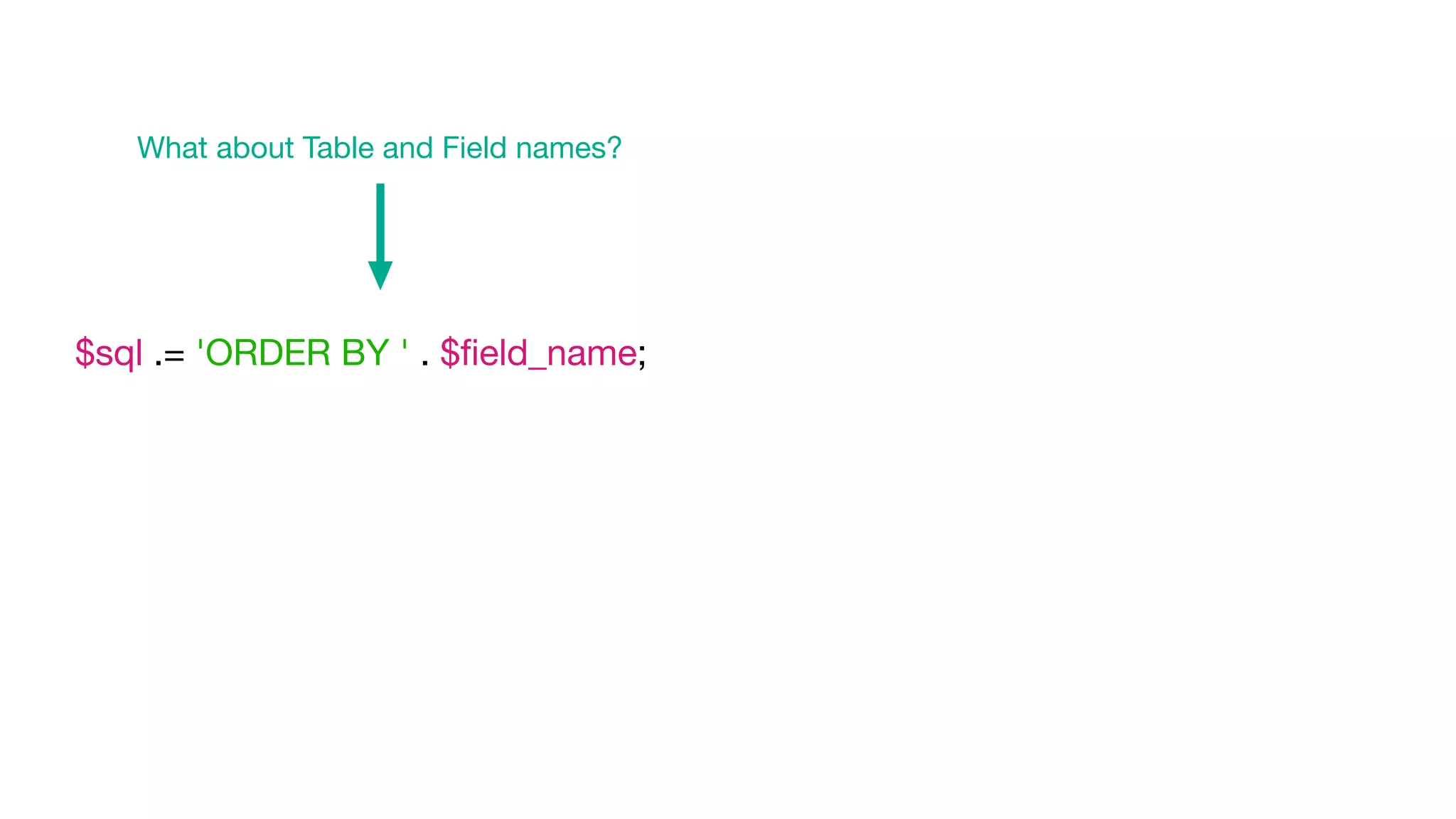
![$fields = [
'name',
'created',
'admin',
];
$field_id = array_search(($_GET['sort'] ?? 'created'), $fields);
$sql = ' ORDER BY ' . $fields[$field_id];](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-94-2048.jpg)
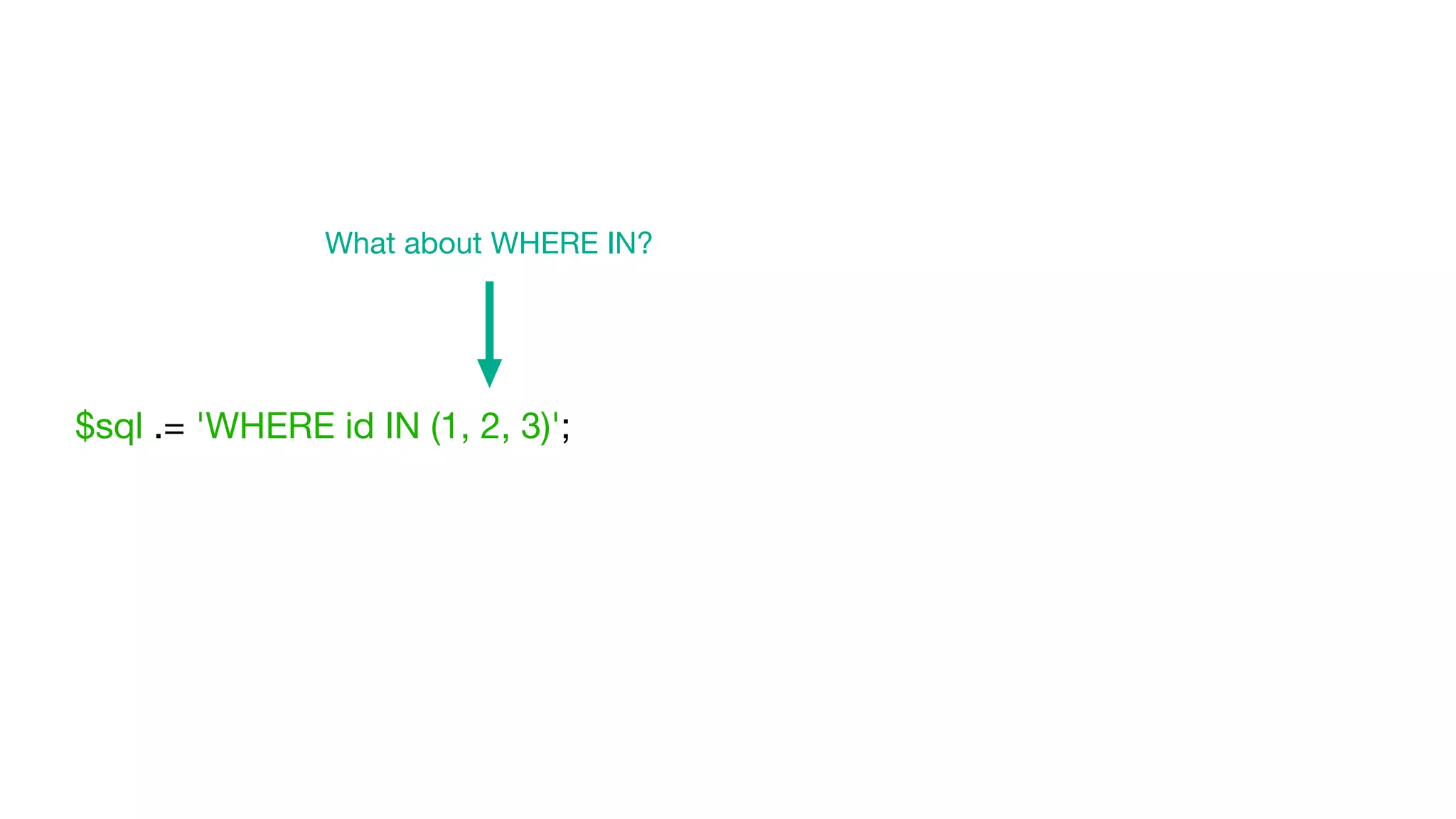
![$ids = [1, 2, 3];
$sql .= 'WHERE id IN (' . implode(', ', $ids) . ')';
From an unknown source](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-96-2048.jpg)
![$ids = [1, 2, 3];
$sql .= 'WHERE id IN (' . implode(',', array_fill(0, count($ids), '?')) . ')';](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-97-2048.jpg)
![$ids = [1, 2, 3];
$sql .= 'WHERE id IN (' . implode(',', array_fill(0, count($ids), '?')) . ')';
$sql .= 'WHERE id IN (?, ?, ?)';](https://image.slidesharecdn.com/isliteral-200910095407/75/Proposed-PHP-function-is_literal-98-2048.jpg)