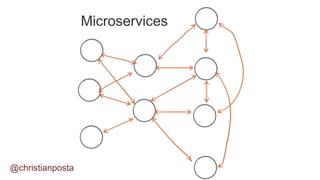
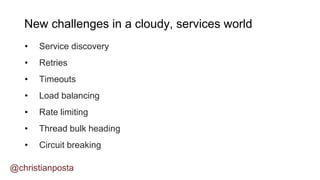
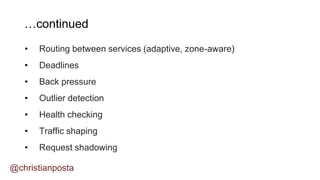
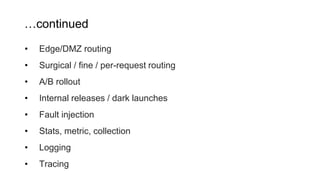
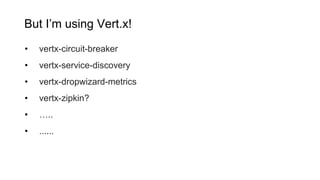
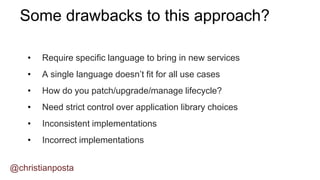
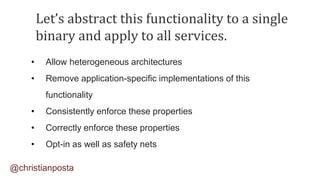
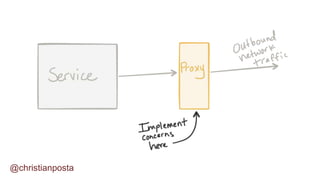
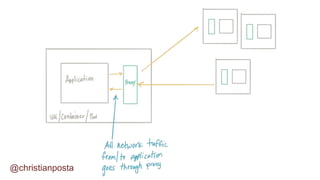
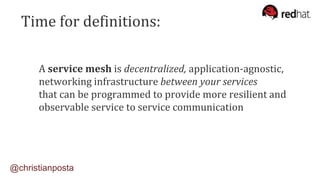
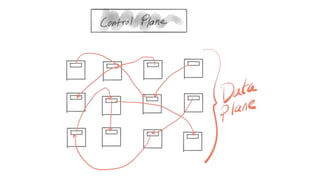
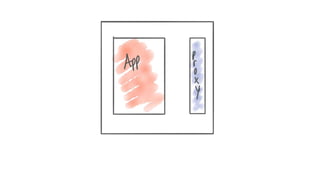
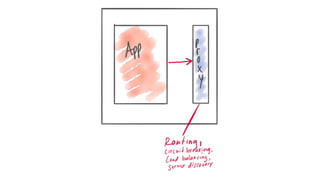
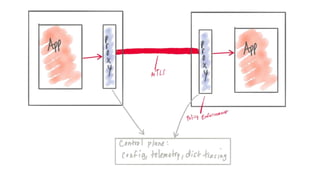
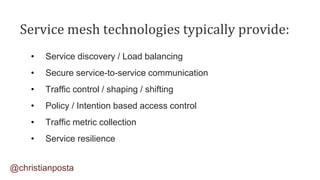
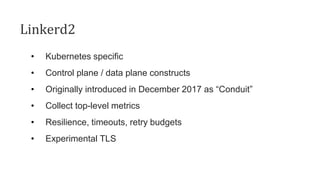
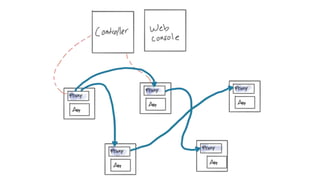
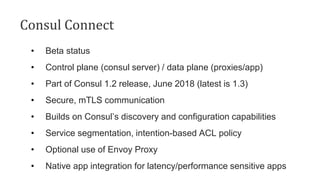
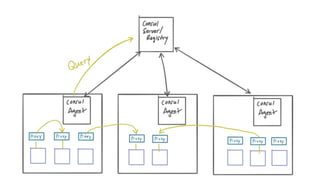
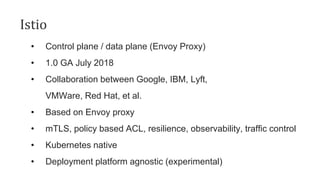
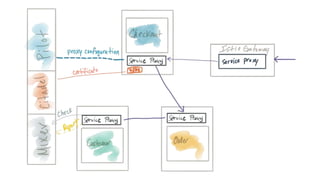
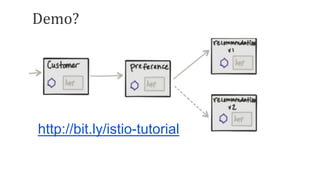
The document discusses the complexities of microservices architecture and the challenges it presents, emphasizing the need for effective service communication. It outlines the concept of service meshes as a decentralized, application-agnostic infrastructure that enhances service-to-service communication through various functionalities like service discovery and traffic control. Additionally, it reviews several open-source service mesh projects, including Linkerd, Consul Connect, and Istio, highlighting their features and use cases.