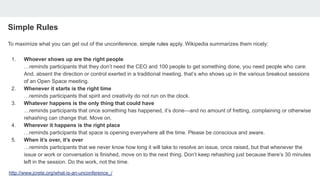
Melissa McKay is an advocate for unconference events and discusses the simple rules that maximize their value: whoever attends are the right people, timing is flexible, accepting what happens, location doesn't matter, and sessions end naturally. She summarizes an unconference as allowing people who care about a topic to self-organize discussions without traditional meeting controls. The document then provides links to various unconference events organized by McKay.