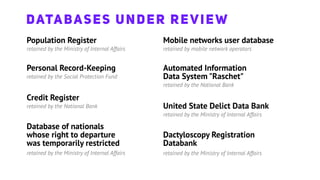
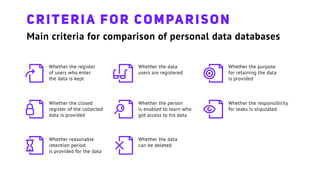
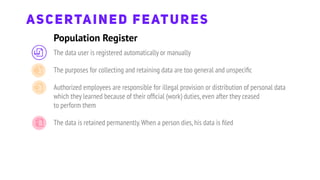
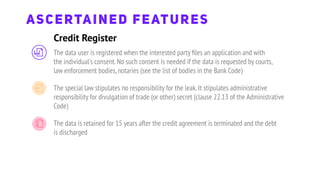
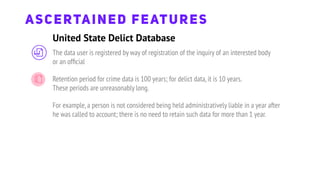
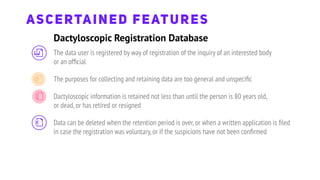
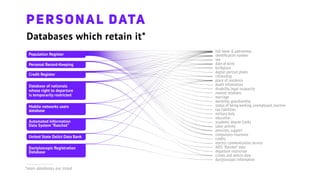
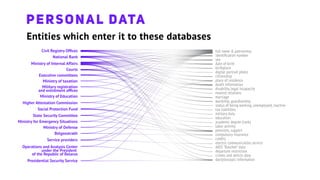
The document discusses issues with personal data protection in Belarusian national databases. It finds that there is no clear definition of personal data, data is retained in several different databases without unified access registration, and individuals have no way of knowing who accesses their data or holding them accountable. It also notes the lack of set retention periods and an inability to delete data on request.