Performance Tuning Tool01-Statspack
•
0 likes•375 views
Statspack https://community.oracle.com/people/royalwzy/blog/2016/02/01/performance-tuning-tool01-statspack
Report
Share
Report
Share
Download to read offline
Recommended
Oracle audit and reporting in one hour or less

Answer questions Who, What , When and Where about any database activity by setting up an Oracle audit. The infrastructure is free and available in every database edition.
Stay on top of any possible performance and storage issues by choosing appropriate audit parameters.
Build summary and detail reports to analyze audit events from multiple databases using APEX or SQL*Plus.
Setup a data retention period and cleanup audit records regularly.
Create honeypot to attract hacker’s attention.
Enable alerts and send email notifications using Oracle Enterprise Manager infrastructure.
Creating a physical standby database 11g on windows

This document describes the steps to create a physical standby database including:
1. Configuring the primary and standby databases with the same Oracle version and opening the primary in archive log mode.
2. Setting up Oracle Net components and testing connectivity between the databases.
3. Enabling archive logging and log shipping on the primary and duplicating or copying the primary database to the standby.
4. Recovering the standby database and opening it in read-only mode to synchronize the data.
Oracle Database 11g Product Family

The document provides an overview of the Oracle Database 11g product family, including the Standard Edition, Standard Edition One, and Enterprise Edition. It describes the key features included in each edition. It also outlines several optional features exclusively available for the Enterprise Edition, such as Oracle Active Data Guard, Oracle Advanced Security, Oracle Partitioning, Oracle Real Application Clusters, and various management packs. Finally, it briefly introduces some related Oracle products that can be used to extend the capabilities of the Oracle database, such as Oracle Exadata Storage Server, Oracle Audit Vault, and Oracle Secure Backup.
DBA だってもっと効率化したい!〜最近の自動化事情とOracle Database〜

This document provides an overview of infrastructure automation tools like Chef, Puppet, Ansible, Serverspec, Infrataster and the Infrataster OracleDB plugin. It includes steps to setup the Oracle Instant Client, install necessary Ruby gems, write an Infrataster spec test to query the Oracle database and assert that the db_block_size parameter equals 8192, and execute the spec test with RSpec.
آموزش مدیریت بانک اطلاعاتی اوراکل - بخش پانزدهم

بانک اطلاعاتی اوراکل بی شک یکی از قدرتمندترین نرم افزارها برای مدیریت اطلاعاتی با حجم بسیار بالا می باشد هدف از این آموزش یادگیری مفاهیم پیچیده معماری و چالش های مدیریتی دیتابیس است که به شما کمک خواهد کرد تا به سرعت مطالب را فرا گرفته و به اهداف خود نزدیک شوید .
سرفصل هایی که در این آموزش به آن پرداخته شده است:
معماری دیتابیس اوراکل
آماده سازی محیط بانک اطلاعاتی
ایجاد دیتابیس اوراکل
مدیریت بخش حافظه ای اوراکل
پیکربندی محیط شبکه در اوراکل
...
برای توضیحات بیشتر و تهیه این آموزش لطفا به لینک زیر مراجعه بفرمائید:
http://faradars.org/courses/fvorc9408
Oracle11g suse11 ilker bakir

This document provides instructions for installing Oracle 11gR2 on SUSE Enterprise Linux 11. It outlines the required software, hardware requirements, and installation steps. The key steps include: using SUSE's orarun package to automate Oracle pre-install tasks like setting kernel parameters; enabling the oracle user; downloading and extracting the Oracle software; and running the Oracle Universal Installer as the oracle user.
監査ログをもっと身近に!〜統合監査のすすめ〜

1) The document discusses Oracle database auditing features before and after version 12.1. It describes migrating the audit trail to the unified audit trail and using the SYS.UNIFIED_AUDIT_TRAIL table.
2) It provides steps to configure syslog auditing on Linux for Oracle database audit records. Procedures are created to output messages to syslog and call it from a fine-grained auditing policy handler.
3) An example fine-grained auditing policy is created to audit access to the SECDEMO.CUSTOMER table and call the syslog handler for non-application users.
PostgreSQL High_Performance_Cheatsheet

PostgreSQL High-Performance Cheat Sheets contains quick methods to find performance issues.
Summary of the course so that when problems arise, you are able to easily uncover what are the performance bottlenecks.
Recommended
Oracle audit and reporting in one hour or less

Answer questions Who, What , When and Where about any database activity by setting up an Oracle audit. The infrastructure is free and available in every database edition.
Stay on top of any possible performance and storage issues by choosing appropriate audit parameters.
Build summary and detail reports to analyze audit events from multiple databases using APEX or SQL*Plus.
Setup a data retention period and cleanup audit records regularly.
Create honeypot to attract hacker’s attention.
Enable alerts and send email notifications using Oracle Enterprise Manager infrastructure.
Creating a physical standby database 11g on windows

This document describes the steps to create a physical standby database including:
1. Configuring the primary and standby databases with the same Oracle version and opening the primary in archive log mode.
2. Setting up Oracle Net components and testing connectivity between the databases.
3. Enabling archive logging and log shipping on the primary and duplicating or copying the primary database to the standby.
4. Recovering the standby database and opening it in read-only mode to synchronize the data.
Oracle Database 11g Product Family

The document provides an overview of the Oracle Database 11g product family, including the Standard Edition, Standard Edition One, and Enterprise Edition. It describes the key features included in each edition. It also outlines several optional features exclusively available for the Enterprise Edition, such as Oracle Active Data Guard, Oracle Advanced Security, Oracle Partitioning, Oracle Real Application Clusters, and various management packs. Finally, it briefly introduces some related Oracle products that can be used to extend the capabilities of the Oracle database, such as Oracle Exadata Storage Server, Oracle Audit Vault, and Oracle Secure Backup.
DBA だってもっと効率化したい!〜最近の自動化事情とOracle Database〜

This document provides an overview of infrastructure automation tools like Chef, Puppet, Ansible, Serverspec, Infrataster and the Infrataster OracleDB plugin. It includes steps to setup the Oracle Instant Client, install necessary Ruby gems, write an Infrataster spec test to query the Oracle database and assert that the db_block_size parameter equals 8192, and execute the spec test with RSpec.
آموزش مدیریت بانک اطلاعاتی اوراکل - بخش پانزدهم

بانک اطلاعاتی اوراکل بی شک یکی از قدرتمندترین نرم افزارها برای مدیریت اطلاعاتی با حجم بسیار بالا می باشد هدف از این آموزش یادگیری مفاهیم پیچیده معماری و چالش های مدیریتی دیتابیس است که به شما کمک خواهد کرد تا به سرعت مطالب را فرا گرفته و به اهداف خود نزدیک شوید .
سرفصل هایی که در این آموزش به آن پرداخته شده است:
معماری دیتابیس اوراکل
آماده سازی محیط بانک اطلاعاتی
ایجاد دیتابیس اوراکل
مدیریت بخش حافظه ای اوراکل
پیکربندی محیط شبکه در اوراکل
...
برای توضیحات بیشتر و تهیه این آموزش لطفا به لینک زیر مراجعه بفرمائید:
http://faradars.org/courses/fvorc9408
Oracle11g suse11 ilker bakir

This document provides instructions for installing Oracle 11gR2 on SUSE Enterprise Linux 11. It outlines the required software, hardware requirements, and installation steps. The key steps include: using SUSE's orarun package to automate Oracle pre-install tasks like setting kernel parameters; enabling the oracle user; downloading and extracting the Oracle software; and running the Oracle Universal Installer as the oracle user.
監査ログをもっと身近に!〜統合監査のすすめ〜

1) The document discusses Oracle database auditing features before and after version 12.1. It describes migrating the audit trail to the unified audit trail and using the SYS.UNIFIED_AUDIT_TRAIL table.
2) It provides steps to configure syslog auditing on Linux for Oracle database audit records. Procedures are created to output messages to syslog and call it from a fine-grained auditing policy handler.
3) An example fine-grained auditing policy is created to audit access to the SECDEMO.CUSTOMER table and call the syslog handler for non-application users.
PostgreSQL High_Performance_Cheatsheet

PostgreSQL High-Performance Cheat Sheets contains quick methods to find performance issues.
Summary of the course so that when problems arise, you are able to easily uncover what are the performance bottlenecks.
Developing Information Schema Plugins

The document discusses developing plugins for the MySQL INFORMATION_SCHEMA by creating custom tables. It provides steps to create a simple "Hello World" plugin that defines a table with two columns and fills it with sample data. The document also describes how to build and install the plugin so it can be queried from INFORMATION_SCHEMA like a regular table.
Oracle12c Pluggable Database Hands On - TROUG 2014

The document provides an agenda and overview for a hands-on workshop on Oracle 12c pluggable databases. The agenda includes topics on Oracle history, container databases, pluggable databases, new users and privileges in Oracle 12c, and several hands-on labs for activities like dropping/unplugging pluggable databases, plugging/cloning pluggable databases from remote container databases using database links, and moving a non-container database to a container database using Data Pump transportable export/import. Slides accompany the topics and provide additional technical details on concepts like container databases, pluggable databases, and the new user and role architecture in Oracle 12c.
1.1 sql create and drop database statement

This document discusses the SQL CREATE DATABASE and DROP DATABASE statements. It explains that the CREATE DATABASE statement is used to create a new SQL database and has a syntax of CREATE DATABASE databasename;. The DROP DATABASE statement is used to drop an existing SQL database and has a syntax of DROP DATABASE databasename;. Examples are provided of each statement being used to create and drop the database "testDB".
Startupandshutdown

1. Oracle looks for parameter files in specific locations to start up an Oracle database instance.
2. There are several options for starting up an Oracle database including startup, startup mount, and startup nomount.
3. Similarly, there are options for shutting down an Oracle database including shutdown, shutdown transactional, shutdown immediate, and shutdown abort.
MySQL Monitoring Mechanisms

This document summarizes MySQL's monitoring mechanisms and how they have evolved over time. It discusses tools like SHOW statements, INFORMATION_SCHEMA, slow/general query logs, and EXPLAIN that provided limited visibility in past versions. MySQL 5.5 introduced the Performance Schema framework for detailed instrumentation. Subsequent versions have expanded instrumentation to provide more developer-focused statistics on statements, stages, I/O, locks and more. New INFORMATION_SCHEMA tables in 5.6 provide additional InnoDB statistics on data dictionary, buffer pool, transactions and compression. The optimizer trace exposes query transformations. Enhanced EXPLAIN now supports more statement types and future improvements will provide a structured EXPLAIN output.
MySQL for Oracle DBAs

This document provides an overview of MySQL for Oracle DBAs, covering topics such as MySQL architecture, backup and recovery strategies, managing space and tables, and connecting MySQL to Oracle. The key points discussed include MySQL's product architecture and internal memory structures, filesystem layout for binaries, data and log files, InnoDB and MyISAM storage engines for managing space, and using tools like mysqldump, mysqlhotcopy, and mysqlbinlog for backups and point-in-time recovery.
How To Configure Apache VirtualHost on RHEL 7 on AWS

This document provides instructions on how to configure Apache virtual hosts on RHEL 7 to host multiple websites on different ports with different content folders. It includes steps to configure the Apache listen directive, create virtual host directives, set document roots and ports, create log directories, validate the configuration, and modify security settings. Sample index files are provided to demonstrate the three configured websites.
Schema replication using oracle golden gate 12c

This document provides instructions for configuring asynchronous schema replication between an Oracle source database and target database using Oracle GoldenGate 12c. It outlines the necessary steps which include:
1. Enabling supplemental logging and archivelog mode on both databases.
2. Installing the GoldenGate software and starting the Manager processes on both systems.
3. Configuring the Extract, Data Pump, and Replicate processes to replicate the BASAK schema and tables from the source PDBORCL to the target PRIPDB database.
4. Starting the Extract, Data Pump, and Replicate jobs to begin the replication process and ensure the BASAK schema and tables are synchronized between the source and target databases.
Troubleshooting Tips and Tricks for Database 19c - Sangam 2019

DBA's always have a bunch of scripts to do their daily tasks. How to find that stuck session, how to find who is consuming the most resources, how do I take a stack of multiple processes? This session will focus on troubleshooting tips and tricks for DBA's covering tools from the Oracle Autonomous Health Framework (AHF) like Trace file Analyzer (TFA) to collect , organize and analyze log data , Exachk and orachk to perform mass best practices analysis and automation , Cluster Health Advisor to debug node evictions and calibrate the framework , OSWatcher and its analysis engine , Oratop for pinpointing performance issues and many other native Database features like short stacks, system state summaries, quickly spot hangs across RAC clusters among some of them to make your jobs a lot more efficient and make you look good to your bosses !!
Schedulers

This document provides an overview of different Oracle schedulers, including UC4, USS, DBMS_SCHEDULER, and Cron. It describes each scheduler's features and provides examples of how to use DBMS_SCHEDULER and Cron to schedule jobs. The document aims to help readers understand the schedulers and determine which one is best suited to their requirements.
Performance schema and_ps_helper

The document describes Performance Schema and ps_helper. Performance Schema is a feature in MySQL that collects runtime performance data and ps_helper is a tool that makes Performance Schema data easier to understand. It provides views, functions and stored procedures to summarize Performance Schema data for common use cases like analyzing user activity and statements.
12c installation

The document provides step-by-step instructions to install Oracle Database 12c. It details downloading the software, checking system requirements, installing prerequisite packages and configuring OS parameters like memory, ports and users. The instructions then cover running the installer, configuring the listener using NetCA and creating a database instance using DBCA.
MySQL InnoDB Cluster 미리보기 (remote cluster test)

MySQL Power Group 2017년 1차 오프라인 세미나 발표자료 입니다.
MySQL InnoDB Cluster 에 대한 간단한 설명 및 Remote Cluster 구성하여 테스트한 내용입니다.
Heritrix DecideRules

This document describes Heritrix DecideRules, which are used to determine the scope of a web crawl by filtering URIs. DecideRules are processed sequentially and can result in a URI being ACCEPTED, REJECTED, or given a PASS. The UK Domain Crawl 2014 uses various DecideRules like SurtPrefixedDecideRule to ACCEPT UK domains and RejectDecideRule to REJECT everything by default. Experimental rules are also described. DecideRules can be used beyond just scoping to filter content during a crawl.
2011 384 hackworth_ppt

This document outlines the steps to restore a production Oracle database to a development platform for testing purposes, including restoring file system directories, shutting down the development instance, restoring the server parameter file, control file, database files, and opening the database while resetting redo logs. It also discusses modifying memory parameters, building a new Oracle Enterprise Manager repository, dropping the copied database, and the importance of backup and recovery.
how to protect your sensitive data using oracle database vault

- Oracle Database Vault provides powerful security controls to help protect sensitive application data from unauthorized access and comply with privacy regulations. It controls privileged account access and sensitive operations inside the database using multi-factor authorization.
- Database Vault realms prevent privileged accounts from accessing application schemas, sensitive tables, and stored procedures. It also controls database configuration changes and prevents unauthorized changes to database entitlements.
- Database Vault is configured easily and runs transparently with minimal performance impact. It implements duty separation, restricting even DBA users' access and controling database operations. Once enabled, it provides strong protection of applications and data.
Extending MySQL Enterprise Monitor

Talk at the MySQL User Conference 2009 about extending MEM with new data collections, graphs and rules
MySQL Monitoring Mechanisms

The 5.5 and 5.6 releases of MySQL introduce several new mechanisms that provide improved monitoring and performance tuning functionality. Examples are performance schemas, InnoDB metrics tables, optimizer trace, and extended explain functionality. This session outlines the vision for monitoring-related functionality in MySQL and presents an overview of the new mechanisms. It shows how these are integrated with MySQL management tools. Furthermore, it discusses how these mechanisms can be utilized by application developers, DBAs, and production engineers for tracking down performance issues and monitoring production systems.
Step by Step Restore rman to different host

1. Take a backup of the database and archived logs on the source system using RMAN.
2. Copy the backup files to the new target system using the same directory structure.
3. Restore the control file, SPFILE, and database files to the target system using RMAN, changing the data file locations and redo log file locations as needed.
4. Open the database with a resetlogs after restoring the database, control file, and archived redo logs from backup.
How To Install and Configure Log Rotation on RHEL 7 or CentOS 7

Logrotate is used to automatically rotate, compress, and remove log files. It can be configured to run daily, weekly, or monthly, and also based on log file size. The main configuration file is /etc/logrotate.conf, and individual services are configured in files under /etc/logrotate.d/. Logrotate can be run manually with the logrotate command or automatically via cron. Options allow compressing, emailing, and moving old log files. Scripts can be used for tasks like restarting services after rotation.
SQL Tuning04-Interpreting Execution Plans

This document discusses various methods for interpreting SQL execution plans in Oracle databases, including using the PLAN_TABLE, views like V$SQL_PLAN, and tools like DBMS_XPLAN and AUTOTRACE. It also covers gathering plan statistics and interpretation from sources like the Automatic Workload Repository (AWR).
SQL Tuning01-Introduction to SQL Tuning

This document provides an introduction to SQL tuning. It discusses common causes of poor SQL performance such as stale statistics, missing indexes, and suboptimal execution plans. It then describes Oracle tools that can be used for SQL tuning such as the Automatic Database Diagnostic Monitor and SQL Tuning Advisor. Various SQL performance metrics are covered like wait time and how it relates to CPU and I/O times. Common SQL performance problems are also listed like parsing issues, full table scans, and redo log configuration errors. Finally, techniques for SQL tuning are discussed such as query rewrites, materialized views, and cursor sharing.
More Related Content
What's hot
Developing Information Schema Plugins

The document discusses developing plugins for the MySQL INFORMATION_SCHEMA by creating custom tables. It provides steps to create a simple "Hello World" plugin that defines a table with two columns and fills it with sample data. The document also describes how to build and install the plugin so it can be queried from INFORMATION_SCHEMA like a regular table.
Oracle12c Pluggable Database Hands On - TROUG 2014

The document provides an agenda and overview for a hands-on workshop on Oracle 12c pluggable databases. The agenda includes topics on Oracle history, container databases, pluggable databases, new users and privileges in Oracle 12c, and several hands-on labs for activities like dropping/unplugging pluggable databases, plugging/cloning pluggable databases from remote container databases using database links, and moving a non-container database to a container database using Data Pump transportable export/import. Slides accompany the topics and provide additional technical details on concepts like container databases, pluggable databases, and the new user and role architecture in Oracle 12c.
1.1 sql create and drop database statement

This document discusses the SQL CREATE DATABASE and DROP DATABASE statements. It explains that the CREATE DATABASE statement is used to create a new SQL database and has a syntax of CREATE DATABASE databasename;. The DROP DATABASE statement is used to drop an existing SQL database and has a syntax of DROP DATABASE databasename;. Examples are provided of each statement being used to create and drop the database "testDB".
Startupandshutdown

1. Oracle looks for parameter files in specific locations to start up an Oracle database instance.
2. There are several options for starting up an Oracle database including startup, startup mount, and startup nomount.
3. Similarly, there are options for shutting down an Oracle database including shutdown, shutdown transactional, shutdown immediate, and shutdown abort.
MySQL Monitoring Mechanisms

This document summarizes MySQL's monitoring mechanisms and how they have evolved over time. It discusses tools like SHOW statements, INFORMATION_SCHEMA, slow/general query logs, and EXPLAIN that provided limited visibility in past versions. MySQL 5.5 introduced the Performance Schema framework for detailed instrumentation. Subsequent versions have expanded instrumentation to provide more developer-focused statistics on statements, stages, I/O, locks and more. New INFORMATION_SCHEMA tables in 5.6 provide additional InnoDB statistics on data dictionary, buffer pool, transactions and compression. The optimizer trace exposes query transformations. Enhanced EXPLAIN now supports more statement types and future improvements will provide a structured EXPLAIN output.
MySQL for Oracle DBAs

This document provides an overview of MySQL for Oracle DBAs, covering topics such as MySQL architecture, backup and recovery strategies, managing space and tables, and connecting MySQL to Oracle. The key points discussed include MySQL's product architecture and internal memory structures, filesystem layout for binaries, data and log files, InnoDB and MyISAM storage engines for managing space, and using tools like mysqldump, mysqlhotcopy, and mysqlbinlog for backups and point-in-time recovery.
How To Configure Apache VirtualHost on RHEL 7 on AWS

This document provides instructions on how to configure Apache virtual hosts on RHEL 7 to host multiple websites on different ports with different content folders. It includes steps to configure the Apache listen directive, create virtual host directives, set document roots and ports, create log directories, validate the configuration, and modify security settings. Sample index files are provided to demonstrate the three configured websites.
Schema replication using oracle golden gate 12c

This document provides instructions for configuring asynchronous schema replication between an Oracle source database and target database using Oracle GoldenGate 12c. It outlines the necessary steps which include:
1. Enabling supplemental logging and archivelog mode on both databases.
2. Installing the GoldenGate software and starting the Manager processes on both systems.
3. Configuring the Extract, Data Pump, and Replicate processes to replicate the BASAK schema and tables from the source PDBORCL to the target PRIPDB database.
4. Starting the Extract, Data Pump, and Replicate jobs to begin the replication process and ensure the BASAK schema and tables are synchronized between the source and target databases.
Troubleshooting Tips and Tricks for Database 19c - Sangam 2019

DBA's always have a bunch of scripts to do their daily tasks. How to find that stuck session, how to find who is consuming the most resources, how do I take a stack of multiple processes? This session will focus on troubleshooting tips and tricks for DBA's covering tools from the Oracle Autonomous Health Framework (AHF) like Trace file Analyzer (TFA) to collect , organize and analyze log data , Exachk and orachk to perform mass best practices analysis and automation , Cluster Health Advisor to debug node evictions and calibrate the framework , OSWatcher and its analysis engine , Oratop for pinpointing performance issues and many other native Database features like short stacks, system state summaries, quickly spot hangs across RAC clusters among some of them to make your jobs a lot more efficient and make you look good to your bosses !!
Schedulers

This document provides an overview of different Oracle schedulers, including UC4, USS, DBMS_SCHEDULER, and Cron. It describes each scheduler's features and provides examples of how to use DBMS_SCHEDULER and Cron to schedule jobs. The document aims to help readers understand the schedulers and determine which one is best suited to their requirements.
Performance schema and_ps_helper

The document describes Performance Schema and ps_helper. Performance Schema is a feature in MySQL that collects runtime performance data and ps_helper is a tool that makes Performance Schema data easier to understand. It provides views, functions and stored procedures to summarize Performance Schema data for common use cases like analyzing user activity and statements.
12c installation

The document provides step-by-step instructions to install Oracle Database 12c. It details downloading the software, checking system requirements, installing prerequisite packages and configuring OS parameters like memory, ports and users. The instructions then cover running the installer, configuring the listener using NetCA and creating a database instance using DBCA.
MySQL InnoDB Cluster 미리보기 (remote cluster test)

MySQL Power Group 2017년 1차 오프라인 세미나 발표자료 입니다.
MySQL InnoDB Cluster 에 대한 간단한 설명 및 Remote Cluster 구성하여 테스트한 내용입니다.
Heritrix DecideRules

This document describes Heritrix DecideRules, which are used to determine the scope of a web crawl by filtering URIs. DecideRules are processed sequentially and can result in a URI being ACCEPTED, REJECTED, or given a PASS. The UK Domain Crawl 2014 uses various DecideRules like SurtPrefixedDecideRule to ACCEPT UK domains and RejectDecideRule to REJECT everything by default. Experimental rules are also described. DecideRules can be used beyond just scoping to filter content during a crawl.
2011 384 hackworth_ppt

This document outlines the steps to restore a production Oracle database to a development platform for testing purposes, including restoring file system directories, shutting down the development instance, restoring the server parameter file, control file, database files, and opening the database while resetting redo logs. It also discusses modifying memory parameters, building a new Oracle Enterprise Manager repository, dropping the copied database, and the importance of backup and recovery.
how to protect your sensitive data using oracle database vault

- Oracle Database Vault provides powerful security controls to help protect sensitive application data from unauthorized access and comply with privacy regulations. It controls privileged account access and sensitive operations inside the database using multi-factor authorization.
- Database Vault realms prevent privileged accounts from accessing application schemas, sensitive tables, and stored procedures. It also controls database configuration changes and prevents unauthorized changes to database entitlements.
- Database Vault is configured easily and runs transparently with minimal performance impact. It implements duty separation, restricting even DBA users' access and controling database operations. Once enabled, it provides strong protection of applications and data.
Extending MySQL Enterprise Monitor

Talk at the MySQL User Conference 2009 about extending MEM with new data collections, graphs and rules
MySQL Monitoring Mechanisms

The 5.5 and 5.6 releases of MySQL introduce several new mechanisms that provide improved monitoring and performance tuning functionality. Examples are performance schemas, InnoDB metrics tables, optimizer trace, and extended explain functionality. This session outlines the vision for monitoring-related functionality in MySQL and presents an overview of the new mechanisms. It shows how these are integrated with MySQL management tools. Furthermore, it discusses how these mechanisms can be utilized by application developers, DBAs, and production engineers for tracking down performance issues and monitoring production systems.
Step by Step Restore rman to different host

1. Take a backup of the database and archived logs on the source system using RMAN.
2. Copy the backup files to the new target system using the same directory structure.
3. Restore the control file, SPFILE, and database files to the target system using RMAN, changing the data file locations and redo log file locations as needed.
4. Open the database with a resetlogs after restoring the database, control file, and archived redo logs from backup.
How To Install and Configure Log Rotation on RHEL 7 or CentOS 7

Logrotate is used to automatically rotate, compress, and remove log files. It can be configured to run daily, weekly, or monthly, and also based on log file size. The main configuration file is /etc/logrotate.conf, and individual services are configured in files under /etc/logrotate.d/. Logrotate can be run manually with the logrotate command or automatically via cron. Options allow compressing, emailing, and moving old log files. Scripts can be used for tasks like restarting services after rotation.
What's hot (20)
Oracle12c Pluggable Database Hands On - TROUG 2014

Oracle12c Pluggable Database Hands On - TROUG 2014
How To Configure Apache VirtualHost on RHEL 7 on AWS

How To Configure Apache VirtualHost on RHEL 7 on AWS
Troubleshooting Tips and Tricks for Database 19c - Sangam 2019

Troubleshooting Tips and Tricks for Database 19c - Sangam 2019
how to protect your sensitive data using oracle database vault

how to protect your sensitive data using oracle database vault
How To Install and Configure Log Rotation on RHEL 7 or CentOS 7

How To Install and Configure Log Rotation on RHEL 7 or CentOS 7
Similar to Performance Tuning Tool01-Statspack
SQL Tuning04-Interpreting Execution Plans

This document discusses various methods for interpreting SQL execution plans in Oracle databases, including using the PLAN_TABLE, views like V$SQL_PLAN, and tools like DBMS_XPLAN and AUTOTRACE. It also covers gathering plan statistics and interpretation from sources like the Automatic Workload Repository (AWR).
SQL Tuning01-Introduction to SQL Tuning

This document provides an introduction to SQL tuning. It discusses common causes of poor SQL performance such as stale statistics, missing indexes, and suboptimal execution plans. It then describes Oracle tools that can be used for SQL tuning such as the Automatic Database Diagnostic Monitor and SQL Tuning Advisor. Various SQL performance metrics are covered like wait time and how it relates to CPU and I/O times. Common SQL performance problems are also listed like parsing issues, full table scans, and redo log configuration errors. Finally, techniques for SQL tuning are discussed such as query rewrites, materialized views, and cursor sharing.
Oracle RDBMS Workshop (Part1)

This document provides a summary of the evolution of Oracle Database from 1977 to the present. It discusses key releases and features introduced over time, including supported platforms, database architecture, utilities, SQL features, PL/SQL, and the ability to integrate Java applications into the database.
Using AWR for SQL Analysis

The document discusses using Statspack and AWR (Automatic Workload Repository) to analyze SQL performance and identify poorly performing queries. It provides examples of Statspack reports and how to interpret them to find SQL statements that are doing full table scans, experiencing buffer cache misses, or are inefficient due to lack of bind variables. The document also discusses how to identify SQL statements that are causing excessive sorting.
Adventures in Dataguard

This document summarizes the key aspects of configuring and using Oracle Dataguard for disaster recovery. It discusses setting up a physical standby database, monitoring the replication process, and utilizing the standby for tasks like reporting and testing. Switching the primary and standby roles is also covered.
12c database migration from ASM storage to NON-ASM storage

1. The document describes the process of migrating a database from ASM to non-ASM storage. This involves taking backups, changing initialization parameters, creating new datafiles and redo logs in non-ASM locations, mounting and opening the database.
2. Key steps include taking an ASM backup, creating a pfile with new datafile and logfile locations, restoring the controlfile, copying datafiles to the new locations, renaming datafiles, and adding new redo logs.
3. After completing these steps, the database is successfully migrated from ASM to non-ASM storage, with the datafiles and redo logs now residing in normal filesystem locations instead of ASM.
11thingsabout11g 12659705398222 Phpapp01

The document discusses several new features and enhancements in Oracle Database 11g Release 1. Key points include:
1) Encrypted tablespaces allow full encryption of data while maintaining functionality like indexing and foreign keys.
2) New caching capabilities improve performance by caching more results and metadata to avoid repeat work.
3) Standby databases have been enhanced and can now be used for more active purposes like development, testing, reporting and backups while still providing zero data loss protection.
11 Things About11g

The document discusses new features in Oracle Database 11g Release 1. Key points include:
1. Encrypted tablespaces allow encryption of data at the tablespace level while still supporting indexing and queries.
2. New caching capabilities improve performance by caching more results in memory, such as function results and query results.
3. Standby databases have enhanced capabilities and can now be used for more active purposes like development, testing and reporting for increased usability and value.
Refresh development from productions

This document outlines steps to refresh a development database from a production database. It describes copying backup files including data files, redo logs, and archive logs from the production environment to the development environment. It then details replacing the development control file with the production control file, recovering the development database using the backup files, and opening the development database with a resetlogs option to synchronize it with the current state of the production database. The goal is to ensure the development database accurately reflects the current state of the production database for testing purposes.
ASH and AWR on DB12c

This document provides an overview of the Automatic Workload Repository (AWR) and Active Session History (ASH) features in Oracle Database 12c. It discusses how AWR and ASH work, how to access and interpret their reports through the Oracle Enterprise Manager console and command line interface. Specific sections cover parsing AWR reports, querying ASH data directly, and using features like the SQL monitor to diagnose performance issues.
SafePeak Configuration Guide

This document provides instructions for configuring SafePeak Technologies' caching software. It outlines several key configuration steps:
1. Eliminate all "Cache=Disable" events by configuring dynamic objects and ignoring certain SQL commands that would otherwise disable caching.
2. Optimize inactive and non-cacheable SQL patterns by reviewing them and modifying their settings if possible to enable caching.
3. Use configuration tools like the SafePeak dashboard to review analytics on SQL traffic and caching performance, identify optimization opportunities, and configure caching rules for SQL patterns.
The overall process involves running application traffic through SafePeak, analyzing the results to identify patterns for optimization, configuring caching settings, and repeating in iterative cycles until desired performance
Rmoug ashmaster

This document discusses using Active Session History (ASH) to analyze and troubleshoot performance issues in an Oracle database. It provides an example of using ASH to identify the top CPU-consuming session over the last 5 minutes. It shows how to group and count ASH data to calculate metrics like average active sessions (AAS) and percentage of time spent on CPU. The document also discusses using ASH to identify top waiting sessions and analyze specific wait events like buffer busy waits.
Oracle goldengate 11g schema replication from standby database

GoldenGate can replicate database schemas between an Oracle source and target database. It was configured to replicate the SCOTT schema from a source Oracle 11gR2 database in standby mode to a target Oracle 11gR2 database. The key steps included enabling supplemental logging on the source, setting up the GoldenGate user and processes on both databases, and defining the extract, pump and replicate processes to copy data and DDL changes from the source to the target schema.
Publishing a Perl6 Module

The document discusses how to publish a Perl 6 module. It covers creating modules, writing tests, documenting metadata, installing modules locally or via package managers like panda, and releasing modules to the ecosystem. Key steps include writing Perl 6 code and tests, adding metadata, testing the metadata, pushing to GitHub, and publishing releases to the ecosystem.
PGDay.Amsterdam 2018 - Stefan Fercot - Save your data with pgBackRest

Ever heard of Point-in-time recovery? pgBackRest is an awsome tool to handle backups, restores and even helps you build streaming replication ! This talk will introduce the tool, its basic features and how to use it.
Okuyama Summary

Okuyama is a distributed key-value storage system implemented completely in Java that allows for scalability without single points of failure. It offers three options for data persistence and allows data to be stored redundantly across multiple data nodes for fault tolerance. As more nodes are added, the load is distributed automatically for increased performance. Unique features include using tag-based metadata to group related data entries.
MySQL Audit using Percona audit plugin and ELK

This document discusses setting up MySQL auditing using the Percona Audit Plugin and ELK (Elasticsearch, Logstash, Kibana) stack to retrieve and analyze MySQL logs. Key steps include installing the Percona Audit Plugin on MySQL servers, configuring it to log to syslog, installing and configuring rsyslog/syslog-ng on database and ELK servers to forward logs, and installing and configuring the ELK stack including Elasticsearch, Logstash, and Kibana to index and visualize the logs. Examples are provided of creating searches, graphs, and dashboards in Kibana for analyzing the MySQL audit logs.
Sqladria 2009 SRC

SQLAdria 2009 presentation's slides about our experience with Maven and SQLJ. It delves in some details about SQLJ and performance comparion between SQLJ and JDBC with prepared statements. It also shows surprising results for what concerns performances of (DB2) SQL PL procedures
07 Using Oracle-Supported Package in Application Development

This document discusses using Oracle-supplied packages for application development. It describes the UTL_MAIL package for managing email, including procedures for sending messages with and without attachments. It also covers the DBMS_SCHEDULER package for automating jobs, including how to create, run, stop, and drop jobs. Finally, it discusses dynamic SQL and executing SQL statements programmatically using native dynamic SQL statements or the DBMS_SQL package.
Migrate database to Exadata using RMAN duplicate

Umair Mansoob discusses migrating a database from a Linux system to an Oracle Exadata system using RMAN duplicate. The key steps are:
1. Create a static local listener on the Exadata target and copy the password file.
2. Add TNS entries and test connections on source and target.
3. Create a pfile on the target and start it in nomount mode.
4. Run the RMAN duplicate command to copy the database, then optionally convert it to a RAC database and register it with CRS.
Similar to Performance Tuning Tool01-Statspack (20)
12c database migration from ASM storage to NON-ASM storage

12c database migration from ASM storage to NON-ASM storage
Oracle goldengate 11g schema replication from standby database

Oracle goldengate 11g schema replication from standby database
PGDay.Amsterdam 2018 - Stefan Fercot - Save your data with pgBackRest

PGDay.Amsterdam 2018 - Stefan Fercot - Save your data with pgBackRest
07 Using Oracle-Supported Package in Application Development

07 Using Oracle-Supported Package in Application Development
More from Zhaoyang Wang
New awesome features in MySQL 5.7

MySQL 5.7 includes several new features that improve performance, replication, and high availability. Key features include performance improvements from the performance schema and optimizer enhancements, replication improvements like multi-source replication and transaction-based parallel replication, and InnoDB improvements such as online operations and general tablespaces.
SQL Tuning02-Intorduction to the CBO Optimizer

This document provides an introduction to the Cost-Based Oracle Optimizer (CBO). It describes the main components of the CBO including the estimator, plan generator, and OPTIMIZER_MODE. It also discusses important CBO concepts like selectivity, cardinality, cost and how they are estimated. The document provides examples of how to view CBO statistics and use 10053 tracing to analyze plans.
MySQL Fulltext Search Tutorial

This document provides an overview of MySQL full-text search capabilities. It discusses the three types of full-text searches supported: natural language, boolean, and query expansion searches. It also covers stopwords, relevance ranking calculations, and techniques for fine-tuning full-text search performance such as configuring minimum/maximum word lengths and optimizing indexes. The document concludes with some restrictions and best practices for MySQL full-text search.
Data Organization in InnoDB

The document summarizes the key data structures used to organize data in InnoDB:
- InnoDB stores data in tablespaces which consist of data files. A tablespace header tracks free/used extents within these files.
- Data files contain fixed-size pages which are organized into extents of 1MB each. Page headers identify page types like interior, leaf, etc.
- File segments allocate ranges of pages to index trees. The root node of each index references two segment headers to allocate leaf/non-leaf pages separately.
Oracle enterprise manager cloud control 12c release 5 installation on oracle ...

Oracle enterprise manager cloud control 12c release 5 installation on oracle linux 6.6
Oracle enterprise manager cloud control 12c r5 agent installation

Oracle enterprise manager cloud control 12c r5 agent installation
MYSQLCLONE Introduction

MYSQLCLONE is a free and simple tool used to clone MySQL databases from one server to another. It can transfer the entire database including data, schemas, stored procedures, functions and events. The tool connects to the source and destination databases using connection parameters and then transfers the database objects and data in either LOAD or INSERT mode. Quick usage examples are provided to demonstrate transferring the full database, schema objects only, and row data in INSERT mode.
Oracle security 08-oracle network security

The document discusses securing Oracle Network services. It provides checklists and procedures for securing clients, the network, and the listener. It recommends configuring clients and browsers with authentication and encryption. It also recommends restricting network access through firewalls and IP address validation. For the listener, it suggests restricting privileges, password protecting administration, and monitoring logs to analyze activity and potential attacks. The goal is to describe how to securely administer the network and listener to restrict access and analyze logs for security.
Oracle security 02-administering user security

This document discusses administering user security in an Oracle database. It covers how to create and manage database user accounts, including authenticating users and assigning privileges. It also covers creating and managing roles to simplify privilege management, and creating profiles to implement password security and control resource usage. Profiles allow enforcing standards for password complexity, aging, locking accounts, and limiting resource consumption. The document stresses applying the principle of least privilege and separating administrative duties for security.
More from Zhaoyang Wang (20)
Oracle enterprise manager cloud control 12c release 5 installation on oracle ...

Oracle enterprise manager cloud control 12c release 5 installation on oracle ...
Oracle enterprise manager cloud control 12c r5 agent installation

Oracle enterprise manager cloud control 12c r5 agent installation
Recently uploaded
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift
Overview
Dive into the world of anomaly detection on edge devices with our comprehensive hands-on tutorial. This SlideShare presentation will guide you through the entire process, from data collection and model training to edge deployment and real-time monitoring. Perfect for those looking to implement robust anomaly detection systems on resource-constrained IoT/edge devices.
Key Topics Covered
1. Introduction to Anomaly Detection
- Understand the fundamentals of anomaly detection and its importance in identifying unusual behavior or failures in systems.
2. Understanding Edge (IoT)
- Learn about edge computing and IoT, and how they enable real-time data processing and decision-making at the source.
3. What is ArgoCD?
- Discover ArgoCD, a declarative, GitOps continuous delivery tool for Kubernetes, and its role in deploying applications on edge devices.
4. Deployment Using ArgoCD for Edge Devices
- Step-by-step guide on deploying anomaly detection models on edge devices using ArgoCD.
5. Introduction to Apache Kafka and S3
- Explore Apache Kafka for real-time data streaming and Amazon S3 for scalable storage solutions.
6. Viewing Kafka Messages in the Data Lake
- Learn how to view and analyze Kafka messages stored in a data lake for better insights.
7. What is Prometheus?
- Get to know Prometheus, an open-source monitoring and alerting toolkit, and its application in monitoring edge devices.
8. Monitoring Application Metrics with Prometheus
- Detailed instructions on setting up Prometheus to monitor the performance and health of your anomaly detection system.
9. What is Camel K?
- Introduction to Camel K, a lightweight integration framework built on Apache Camel, designed for Kubernetes.
10. Configuring Camel K Integrations for Data Pipelines
- Learn how to configure Camel K for seamless data pipeline integrations in your anomaly detection workflow.
11. What is a Jupyter Notebook?
- Overview of Jupyter Notebooks, an open-source web application for creating and sharing documents with live code, equations, visualizations, and narrative text.
12. Jupyter Notebooks with Code Examples
- Hands-on examples and code snippets in Jupyter Notebooks to help you implement and test anomaly detection models.
What is an RPA CoE? Session 1 – CoE Vision

In the first session, we will review the organization's vision and how this has an impact on the COE Structure.
Topics covered:
• The role of a steering committee
• How do the organization’s priorities determine CoE Structure?
Speaker:
Chris Bolin, Senior Intelligent Automation Architect Anika Systems
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Inconsistent user experience and siloed data, high costs, and changing customer expectations – Citizens Bank was experiencing these challenges while it was attempting to deliver a superior digital banking experience for its clients. Its core banking applications run on the mainframe and Citizens was using legacy utilities to get the critical mainframe data to feed customer-facing channels, like call centers, web, and mobile. Ultimately, this led to higher operating costs (MIPS), delayed response times, and longer time to market.
Ever-changing customer expectations demand more modern digital experiences, and the bank needed to find a solution that could provide real-time data to its customer channels with low latency and operating costs. Join this session to learn how Citizens is leveraging Precisely to replicate mainframe data to its customer channels and deliver on their “modern digital bank” experiences.
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...

“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/how-axelera-ai-uses-digital-compute-in-memory-to-deliver-fast-and-energy-efficient-computer-vision-a-presentation-from-axelera-ai/
Bram Verhoef, Head of Machine Learning at Axelera AI, presents the “How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-efficient Computer Vision” tutorial at the May 2024 Embedded Vision Summit.
As artificial intelligence inference transitions from cloud environments to edge locations, computer vision applications achieve heightened responsiveness, reliability and privacy. This migration, however, introduces the challenge of operating within the stringent confines of resource constraints typical at the edge, including small form factors, low energy budgets and diminished memory and computational capacities. Axelera AI addresses these challenges through an innovative approach of performing digital computations within memory itself. This technique facilitates the realization of high-performance, energy-efficient and cost-effective computer vision capabilities at the thin and thick edge, extending the frontier of what is achievable with current technologies.
In this presentation, Verhoef unveils his company’s pioneering chip technology and demonstrates its capacity to deliver exceptional frames-per-second performance across a range of standard computer vision networks typical of applications in security, surveillance and the industrial sector. This shows that advanced computer vision can be accessible and efficient, even at the very edge of our technological ecosystem.Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Programming Foundation Models with DSPy - Meetup Slides

Prompting language models is hard, while programming language models is easy. In this talk, I will discuss the state-of-the-art framework DSPy for programming foundation models with its powerful optimizers and runtime constraint system.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Introduction of Cybersecurity with OSS at Code Europe 2024

I develop the Ruby programming language, RubyGems, and Bundler, which are package managers for Ruby. Today, I will introduce how to enhance the security of your application using open-source software (OSS) examples from Ruby and RubyGems.
The first topic is CVE (Common Vulnerabilities and Exposures). I have published CVEs many times. But what exactly is a CVE? I'll provide a basic understanding of CVEs and explain how to detect and handle vulnerabilities in OSS.
Next, let's discuss package managers. Package managers play a critical role in the OSS ecosystem. I'll explain how to manage library dependencies in your application.
I'll share insights into how the Ruby and RubyGems core team works to keep our ecosystem safe. By the end of this talk, you'll have a better understanding of how to safeguard your code.
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The typical problem in product engineering is not bad strategy, so much as “no strategy”. This leads to confusion, lack of motivation, and incoherent action. The next time you look for a strategy and find an empty space, instead of waiting for it to be filled, I will show you how to fill it in yourself. If you’re wrong, it forces a correction. If you’re right, it helps create focus. I’ll share how I’ve approached this in the past, both what works and lessons for what didn’t work so well.
AppSec PNW: Android and iOS Application Security with MobSF

Mobile Security Framework - MobSF is a free and open source automated mobile application security testing environment designed to help security engineers, researchers, developers, and penetration testers to identify security vulnerabilities, malicious behaviours and privacy concerns in mobile applications using static and dynamic analysis. It supports all the popular mobile application binaries and source code formats built for Android and iOS devices. In addition to automated security assessment, it also offers an interactive testing environment to build and execute scenario based test/fuzz cases against the application.
This talk covers:
Using MobSF for static analysis of mobile applications.
Interactive dynamic security assessment of Android and iOS applications.
Solving Mobile app CTF challenges.
Reverse engineering and runtime analysis of Mobile malware.
How to shift left and integrate MobSF/mobsfscan SAST and DAST in your build pipeline.
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians

Dmitrii Kamaev, PhD
Senior Product Owner - QIAGEN
Recently uploaded (20)
9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...

9 CEO's who hit $100m ARR Share Their Top Growth Tactics Nathan Latka, Founde...
Monitoring and Managing Anomaly Detection on OpenShift.pdf

Monitoring and Managing Anomaly Detection on OpenShift.pdf
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...

Deep Dive: AI-Powered Marketing to Get More Leads and Customers with HyperGro...
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...

“How Axelera AI Uses Digital Compute-in-memory to Deliver Fast and Energy-eff...
Programming Foundation Models with DSPy - Meetup Slides

Programming Foundation Models with DSPy - Meetup Slides
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
Introduction of Cybersecurity with OSS at Code Europe 2024

Introduction of Cybersecurity with OSS at Code Europe 2024
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[OReilly Superstream] Occupy the Space: A grassroots guide to engineering (an...
AppSec PNW: Android and iOS Application Security with MobSF

AppSec PNW: Android and iOS Application Security with MobSF
Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians

Biomedical Knowledge Graphs for Data Scientists and Bioinformaticians
Performance Tuning Tool01-Statspack
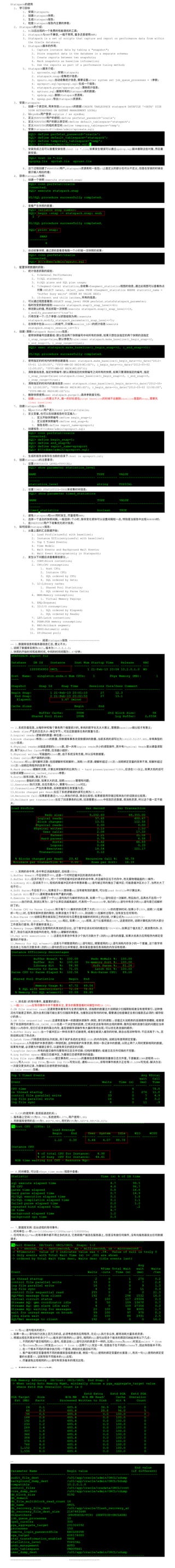
- 1. Statspack 1. 1. Statspack; 2. Statspack ; 3. Statspack ; 4. Statspack ; 2. Statspack : 1. 8i ; 2. Statspack AWR , , AWR; 3. Statspack is a set of scripts that capture and report on performance data from within the Oracle database; 4. Statspack : 1. Capture instance data by taking a "snapshot"; 2. Store snapshot data in the database in a separate schema; 3. Create reports between two snapshots; 4. Mark snapshots as baseline information; 5. Use the reports as part of a performance tuning method; 5. Statspack : 1. spcreate.sql: Statspack; 2. statspack.snap: ; 3. spauto.sql: , alter system set job_queue_processes = 5 ; 4. spreport.sql/sprepsql.sql: ; 5. statspack.purge/sppurge.sql: ; 6. sptrunc.sql: Statspack ; 7. spdrop.sql: Statspack ; 8. spexp.par: Statspack ; 3. Statspack: 1. , statspack :CREATE TABLESPACE statspack DATAFILE '+DATA' SIZE 500M AUTOEXTEND ON EXTENT MANAGEMENT LOCAL; 2. sysdba :sqlplus / as sysdba; 3. PERFSTAT :define perfstat_password='oracle'; 4. PERFSTAT :define default_tablespace='statspack'; 5. PERFSTAT :define temporary_tablespace='temp'; 6. Statspack:@?/rdbms/admin/spcreate.sql; 7. :host ls *.lis; spdrop.sql , ; 8. PERFSTAT ,Statspack ;( , ) 4. Statspack : 1. :execute statspack.snap; 2. : 3. , : 5. : 1. : 1. 0:General Performance; 2. 5:SQL statments; 3. 6:SQL plans and SQL plan usage; 4. 7:Segment-level statistics, v$segment_statistics , :SELECT owner, object_name FROM v$segment_statistics WHERE statistic_name = 'buffer busy waits' ORDER BY VALUE DESC; 5. 10:Parent and child latches, ; 2. :SELECT snap_level FROM perfstat.stats$statspack_parameter; 3. :execute statspack.snap(i_snap_level=>6); 4. , :execute statspack.snap(i_snap_level=>10, i_modify_parameter=>'true'); 5. / ( ):execute statspack.modify_statspack_parameter(i_snap_level=>7); 6. session , session_id=3 :execute statspack.snap(i_session_id=>3); 6. / Statspack Baselines : 1. ( , i_snap_range=false, ture):exec statspack.make_baseline(i_begin_snap=>2, i_end_snap=>5, i_snap_range=>true); 2. :exec statspack.make_baseline(i_begin_date=>to_date('2012- 05-01 12:00:00', 'YYYY-MM-DD HH24:MI:SS'), i_begin_date=>to_date('2012-05-02 12:00:00', 'YYYY-MM-DD HH24:MI:SS')); 3. , ( , , i_snap_range=false):statspack.clear_baseline(i_begin_snap=>2, i_end_snap=>5, i_snap_range=>true); 4. :exec statspack.clear_baseline(i_begin_date=>to_date('2012-05- 01 12:00:00', 'YYYY-MM-DD HH24:MI:SS'), i_begin_date=>to_date('2012-05-02 12:00:00', 'YYYY-MM-DD HH24:MI:SS')); 5. exec statspack.purge(); ; 6. baseline , purge baseline baseline snap, clear baseline; 7. Statspack : 1. perfstat :conn perfstat/oracle; 2. , : 1. :define begin_snap=1; 2. :define end_snap=4; 3. :define report_name=spreport; 3. :@?/rdbms/admin/spreport.sql; 4. :host ls spreport.lst; 8. Statspack : 1. STATISICS_LEVEL=TYPICAL; 2. TIMED_STATISTICS=TRUE ; 3. Statspack AWR , AWR; 4. , 1 , , ###### ; 5. PREFSTAT ; 9. Statspack : 1. : 1. Load Profile(useful with baseline); 2. Instance Efficiency(useful with baseline); 3. Top 5 Timed Events; 4. Time Model; 5. Wait Events and Background Wait Events; 6. Wait Event Histogram(only in Statspack); 2. ,: 1. CONT:Block contention; 2. CPU:CPU consumption; 1. Host CPU; 2. Instance CPU; 3. SQL ordered by CPU; 4. SQL ordered by Gets; 3. LC:Library cache; 1. Shared Pool Statistics; 2. SQL ordered by Parse Calls; 4. MEM:Memory consumption; 1. Virtual Memory Paging; 5. ENQ:Enqueue; 6. IO:I/O consumption; 1. SQL ordered by Elapsed; 2. SQL ordered by Reads; 7. LAT:Latch contention; 8. PGAM:PGA memory consumption; 9. RBS:Rollback segment; 10. UNDO:Automatic undo; 11. SP:Shared pool; ------------------- Statspack ------------------- -- 1. , ; 1. ORCL, 10.2.0.1.0; 2. , 1.67 ; -- 2. , , , baseline ; 1.Redo size: ( ), ; 2.Logical reads: ( block); 3.block changes: block , , 1:4(13.51:57.68), OLTP ; 4.Physical reads: block , Logica reads , Physical Reads , Buffer Cache , ; 5.Physical writes: block , , ; 6.User calls: ; 7.Parses: sql ( ), CPU ; 100 /s , 300 /s ; 8.Hard parses: , (1 - hard prases/parses)*100%, 95% , session_cached_cursors ; 9.Sorts: , ; 10.Logons: , , session ; 11.Executes: , , baseline ; 12.Transactions: , ; 13.Blocks changed per Read: 23.42%; 14.Recursive Call: PL/SQL , ; ; 15.Rollback per transaction: , undo , , ; -- 3. , , 100%; 1.Buffer Nowait: 99%, ; 2.Buffer Hit: 99%, , , IO ; 3.Library Hit: 95%, sql ( , ); 4.Soft Parse: 95%, 80% sql , Load Profile ; 5.Latch Hit: 95% ; 6.Execute to Parse: SQL , SQL , , session , 0. , session , SQL SQL ; 7.Parse CPU to Parse Elapsd: CPU 100/102.56 ; 100%, CPU SQL , ; 100%, CPU , ; 8.Non-Parse CPU , round(100*(1- parse_cpu/tot_cpu),2). parse_cpu , tot_cpu , 100%, , , ; 9.Memory Usage: , 75% 90%; , ; , , SQL ; 10.Sql with executions > 1: 1 SQL , ; 11.Memory for SQL w/exec>1: SQL , SQL , 1 SQL , ; -- 4. 5 , ; 1. CPU time , DB CPU; 2.DB file scatter read: , ; , , , ( ); 3.DB file sequential read: ( , ); , ;DB_CACHE_SIZE , ; PGA , , ; ; 4.Buffer busy wait: , , ; 1 , ; 5.Latch free: , (SGA) , ; 6.Enqueue: , ; , , , , ; 7.Logfile Switch: ( ) ; 8.Log buffer space: , ; 9.Log file sync: session ,session , LGWR redo entry redo log file, redo log file , session, 10.LGRW ; : , ; 11.Ldle event: ; -- 5.CPU ( ); 1. CPU 88.78%, 4.07%, 5.44; 2. CPU 5.44%*4.98%, CPU 5.44%*4.98%*44.41%; -- 6. , v$sys_time_model ; -- 7. / ; 1. :s- ;cs-1/100s;ms-1/1000s;us-1/1000000s; 2. SQL*Net , , , ; -- 8: sql ; 1. sql , , SQL , ; 2. SQL SQL , SQL : 1. SQL , SQL , schema user1 select * from t; schema user2 select * from t; SQL , schema , ; 2. , ; 3. , SQL 10, SQL 50, SQL ; 4. SQL ; -- 9. , PGA ; 1. , pga_aggregate_target=96 100% ; 2. V$PGA_TARGET_ADVICE ; -- 10. , , ; ------------------- Statspack -------------------
