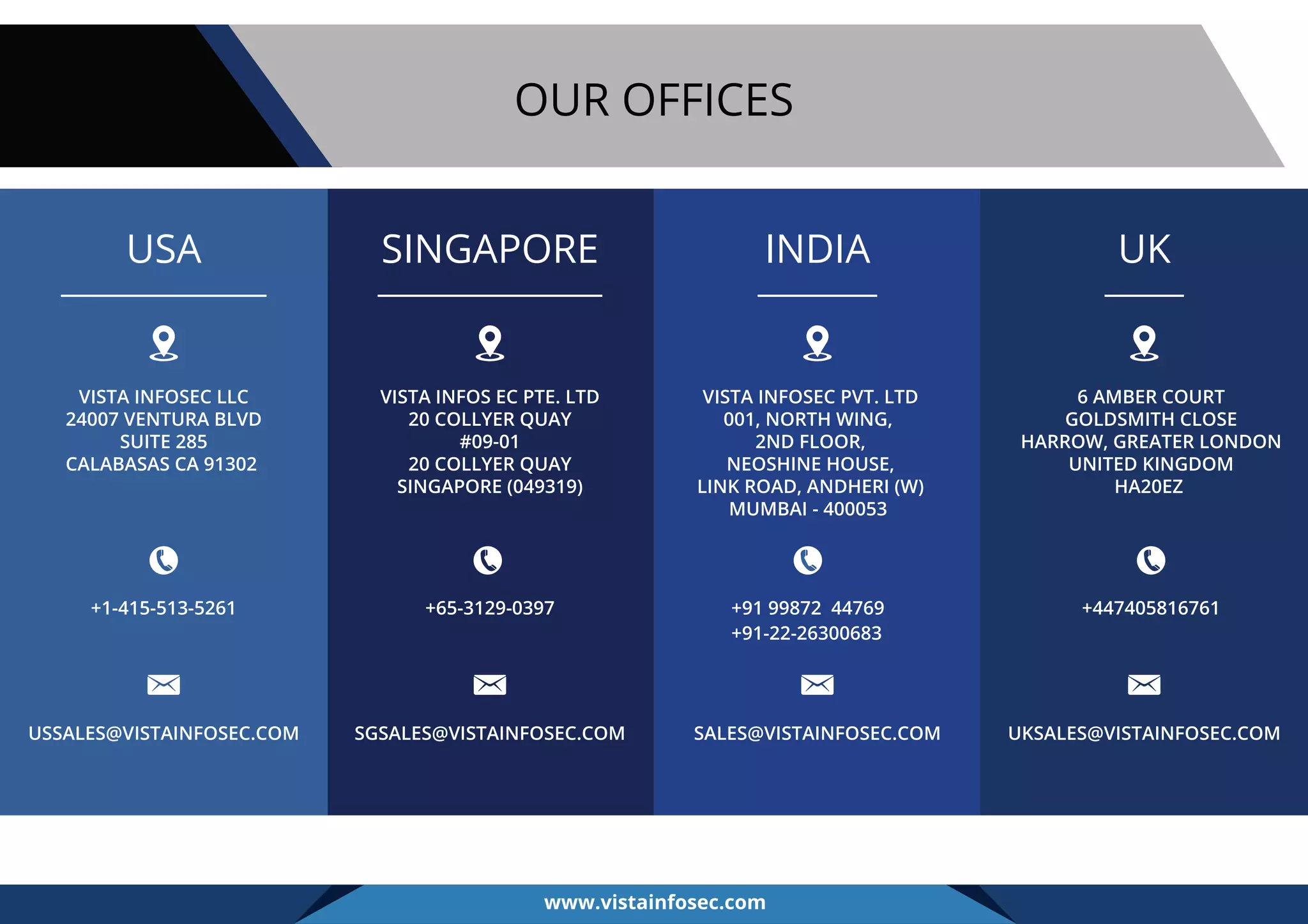
The document discusses the intersection of PCI DSS standards and virtualization in payment card environments, identifying significant security risks and compliance challenges introduced by virtualization. These include vulnerabilities linked to hypervisors, increased complexity in systems, and risks associated with multiple functions on a single physical system. It emphasizes the necessity for thorough risk assessments, proper implementation of security controls, and stringent compliance measures to mitigate these risks in virtualized environments.