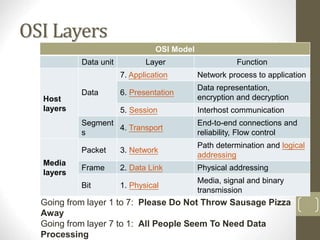
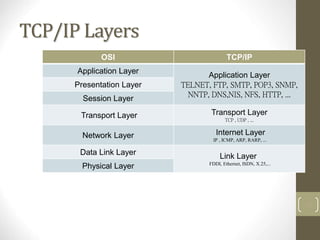
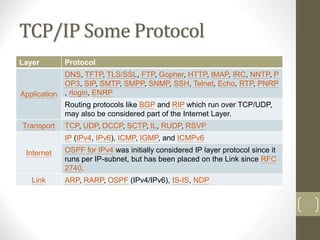
The document provides an overview of the OSI model and TCP/IP model for networking. It describes the seven layers of the OSI model from the physical layer to the application layer. It also outlines the four layers of the TCP/IP model from the link layer to the application layer. Key aspects like protocols, functions, and examples are provided for each layer of both models.