This document provides queries and explanations to troubleshoot advanced Oracle E-Business Suite topologies, such as DMZ configurations. It begins with the important FND_NODES query, which lists all nodes and their configuration. Understanding the results requires comparing them to a topology diagram. Other queries examine trust levels for nodes and responsibilities, which determine external access. Setting all nodes to external could lock one out, but the queries provide solutions. Overall this provides critical tools and guidance for debugging complex Oracle EBS environments.
![Tips and Queries for Troubleshooting Advanced Topologies (Doc ID 364439.1)
In this Document
Purpose
Troubleshooting Steps
The Importance of Topology Diagrams
-
The FND_NODES query
Understanding the FND_NODES Query Results
-
The Trust Query
Understanding the Trust Query Results
Accidentally Locking Oneself Out
-
A Responsibility Query
Understanding the Responsibility Query Results
-
The Enabled Query
Understanding the Enabled Query Results
-
Understanding the Server and ServResp Hierarchy
Server Hierarchy
ServResp Hierarchy
-
The Profile Options Query
Understanding the Profiles Query
Setting ServResp Profile Options Manually
-
Orphaned Profile Options
Understanding the Orphans Query
-
Checking the Patch Requirements on each Appl_Top
Patch Query Caveats
-
Summary
References
APPLIES TO:
Oracle Applications Technology Stack - Version 11.5.10.2 to 12.2.2 [Release 11.5.10 to 12.2]
Information in this document applies to any platform.
PURPOSE
The Troubleshooting Guide is provided to assist in debugging advanced topologies and configurations as described in the following
notes that are recommended prerequisites for this note:
Note:287176.1-DMZ Configuration with Oracle E-Business Suite 11i
Note:217368.1-Advanced Configurations and Topologies for Enterprise Deployments of E-Business Suite 11i
Note:380489.1-Using Load-Balancers with Oracle E-Business Suite Release 12
Note:380490.1-Oracle E-Business Suite Release 12 Configuration in a DMZ
Document 364439.1 https://support.oracle.com/epmos/faces/DocumentDisplay?_adf.ctrl-state...
1 of 17 8/12/2014 6:54 PM](https://image.slidesharecdn.com/oracleapplicationtechstacktipsandqueriesfortroubleshootingadvancedtopologies-140812111124-phpapp01/85/Oracle-application-tech-stack-tips-and-queries-for-troubleshooting-advanced-topologies-1-320.jpg)


![spool trust
set linesize 132
set pagesize 100
col "Level Where Option Is Set" format a60
col "Profile Name" format a30
col value format a10
break on "Profile Name";
select
p.user_profile_option_name "Profile Name",
decode(v.profile_option_value,
1, 'Admin',
2, 'Normal',
3, 'External',
'Unknown') Value,
decode(v.level_id,
10001, 'SITE',
10002, (select 'App:'||a.application_short_name from fnd_application a
where a.application_id = v.level_value),
10003, (select 'Resp:'||f.RESPONSIBILITY_name||' ('||responsibility_key||')' from
fnd_responsibility_vl f
where f.responsibility_id = v.level_value),
10004, (select 'User:'||u.user_name from fnd_user u
where u.user_id = v.level_value),
10005, (select 'Server:'||n.node_name from fnd_nodes n
where n.node_id = v.level_value),
10006, (select 'Org:'||org.name from hr_operating_units org
where org.name = v.level_value),
'NOT SET') "Level Where Option Is Set"
from
fnd_profile_options_vl p,
fnd_profile_option_values v
where
p.profile_option_id = v.profile_option_id (+)
and p.application_id = v.application_id (+)
and p.profile_option_name like upper('%TRUST%')
order by 1,2,3 desc;
Example Output of Trust Query
Profile Name VALUE Level Where Option Is Set
--------------------------- ---------- --------------------------------------------------------
Node Trust Level Normal SITE
Admin Server:OTHERMT
External Server:DCOLLIEREMT
Responsibility Trust Level Normal SITE
External Resp:iRecruitment External Candidate (IRC_EXT_CANDIDATE)
Admin Resp:System Administration (SYSTEM_ADMINISTRATION)
Admin Resp:System Administrator (SYSTEM_ADMINISTRATOR)
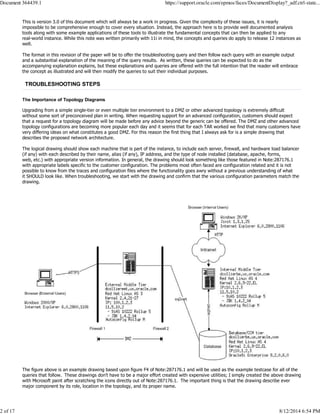
Understanding the Trust Query Results
In the above example, the external server sitting in the DMZ is defined to be DCOLLIEREMT because the Node_Trust_Level is set to
External at the server level for the server named DCOLLIEREMT. Similarly, the only responsibility that will be available to users logging
into DCOLLIEREMT is iRecruitment External Candidate.
On a new tier identified as "OTHERMT", which didn't make it to the topology diagram yet, is an example of an Administrative tier. It is
possible to restrict Administrative responsibilities to a specific tier. In this example, if a user logs in to one of the normal tiers, neither
the responsibility "System Administration" nor "System Administrator" will appear in the responsibility list even if the user has those
responsibilities assigned. As setup in this example, the user must have these responsibilities AND be logged in on the server named
"OtherMT" to see and use them.
There is currently a bug open on the ADMIN trust level. While it is proper that the Admin responsibilities (such as in this example)
will not appear on a normal or external tier, they will appear on the admin tier, but an attempt to make use of a forms-based admin
responsibility (such as System Administrator) will fail shortly after forms is launched with the error of "Sorry, no valid responsibilities
are available [OK]".
Bug:7699618-ISSUE WHEN SETTING RESPONSIBILITY TRUST LEVEL (FORMS BASED)
Document 364439.1 https://support.oracle.com/epmos/faces/DocumentDisplay?_adf.ctrl-state...
5 of 17 8/12/2014 6:54 PM](https://image.slidesharecdn.com/oracleapplicationtechstacktipsandqueriesfortroubleshootingadvancedtopologies-140812111124-phpapp01/85/Oracle-application-tech-stack-tips-and-queries-for-troubleshooting-advanced-topologies-5-320.jpg)