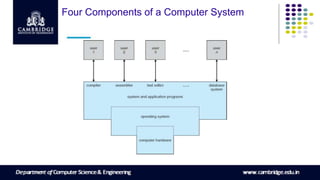
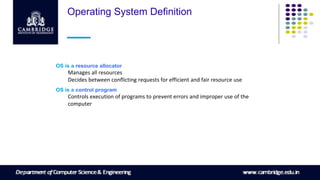
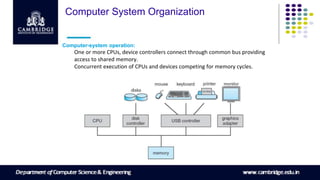
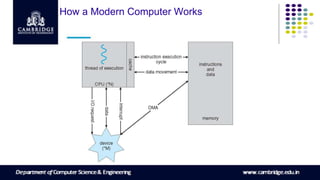
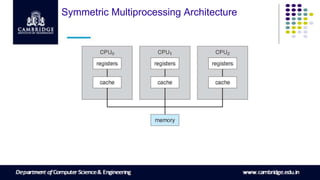
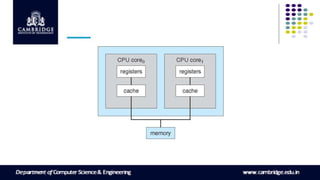
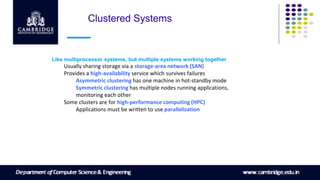
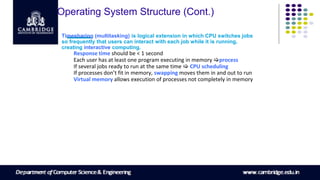
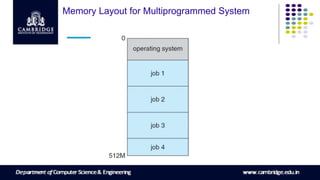
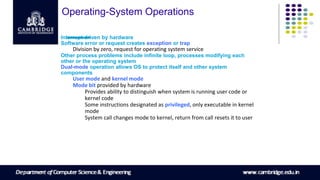
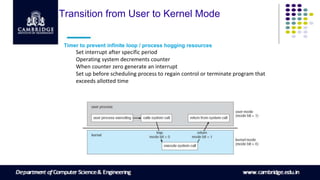
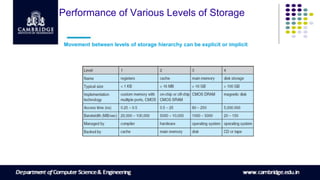
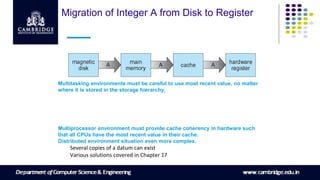
This document provides an overview of operating system concepts across 3 chapters. It describes the core functions of an operating system including process management, memory management, storage management, protection and security. It also discusses computer system organization including hardware components, multiprocessing, and storage hierarchies. Key operating system structures are explained such as interrupt handling, I/O processing, and virtual memory. Different computing environments like client-server, peer-to-peer, and web-based systems are also introduced.