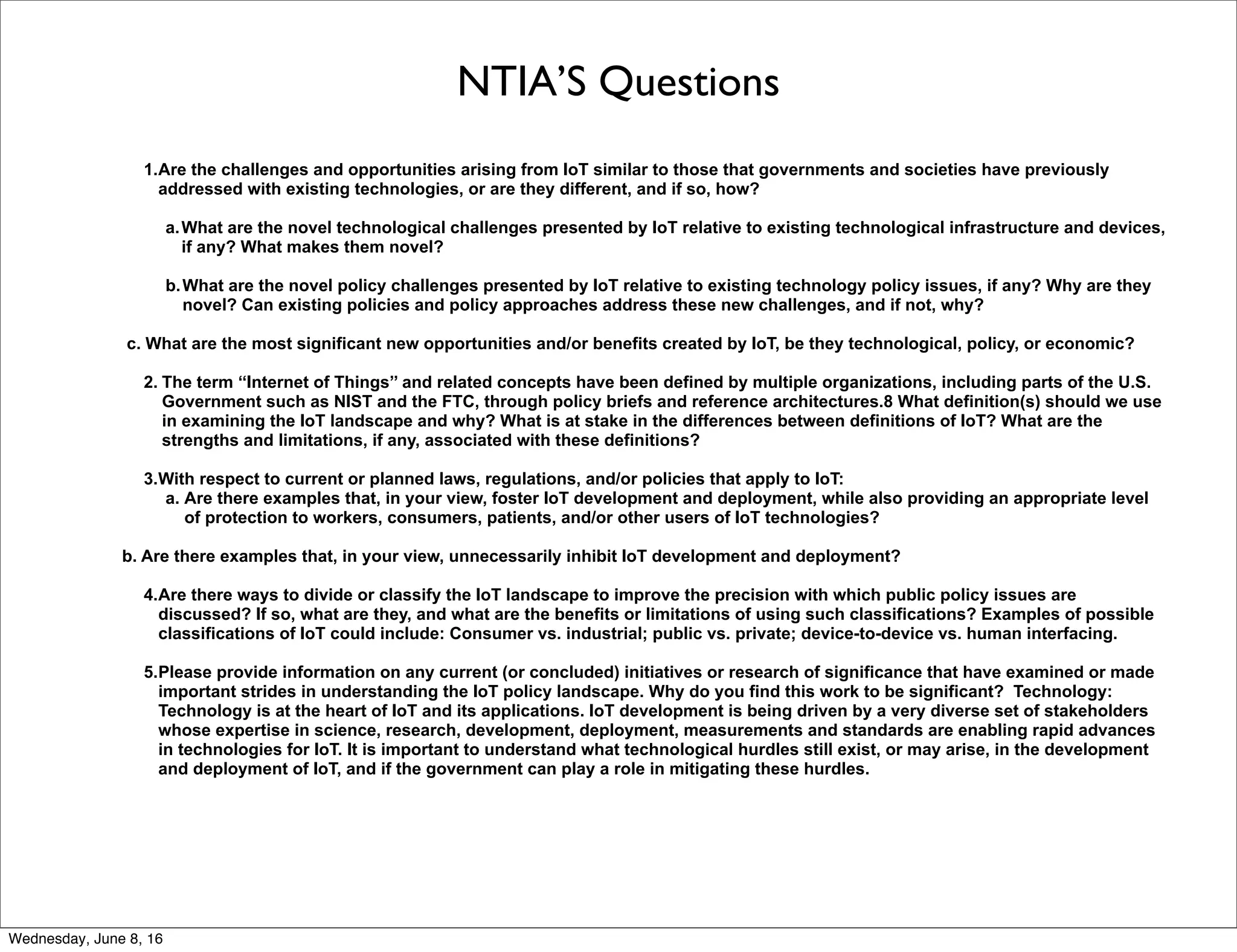
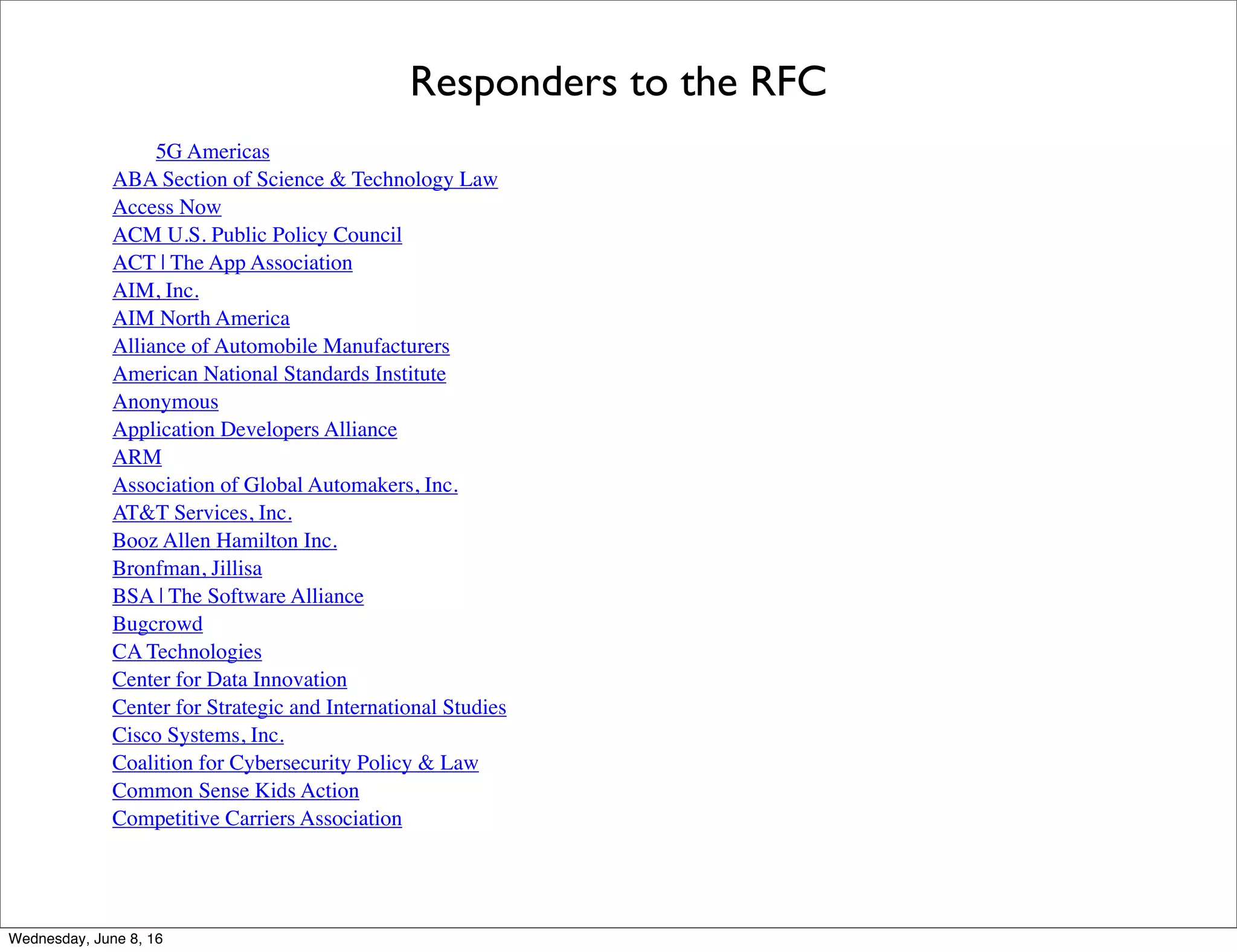
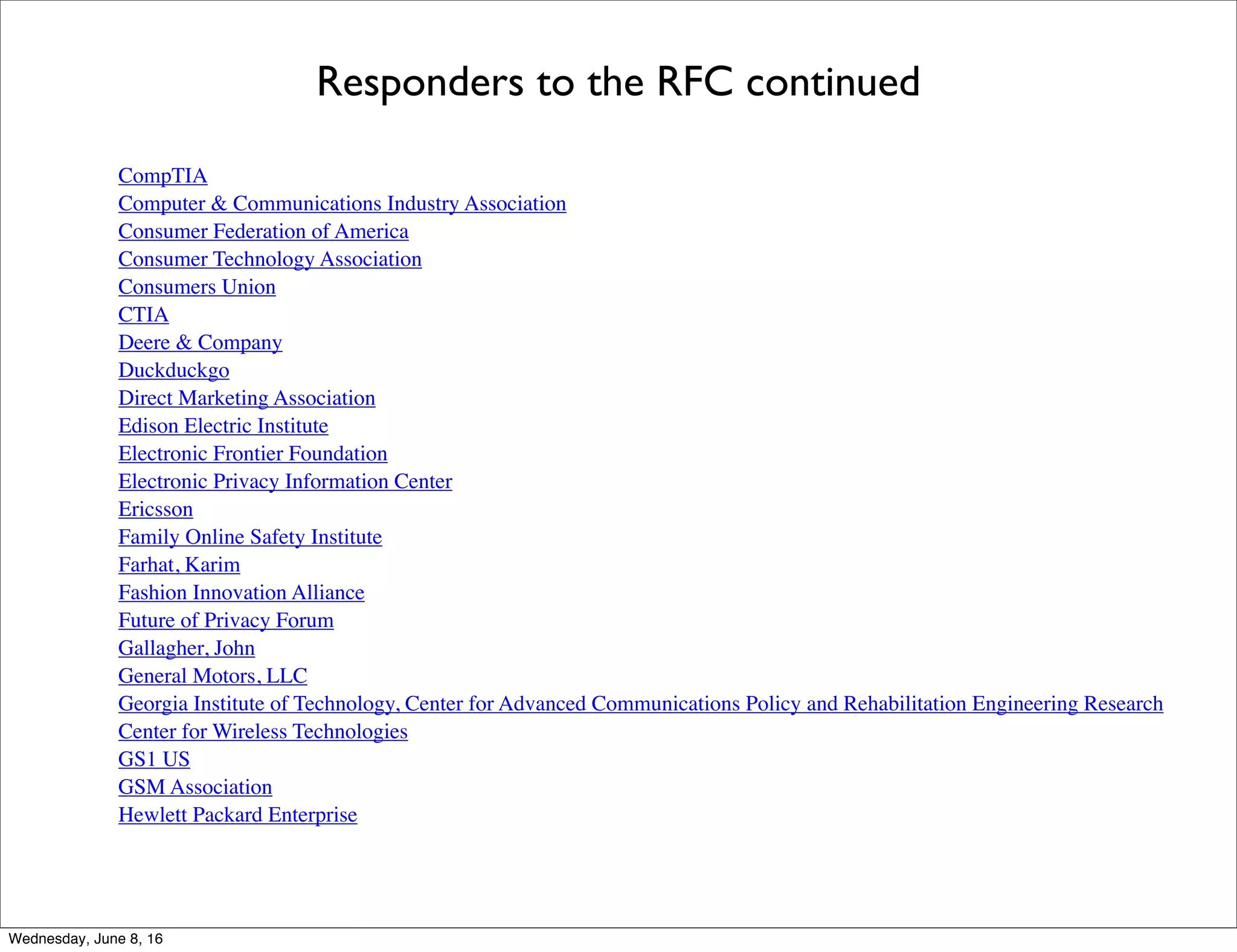
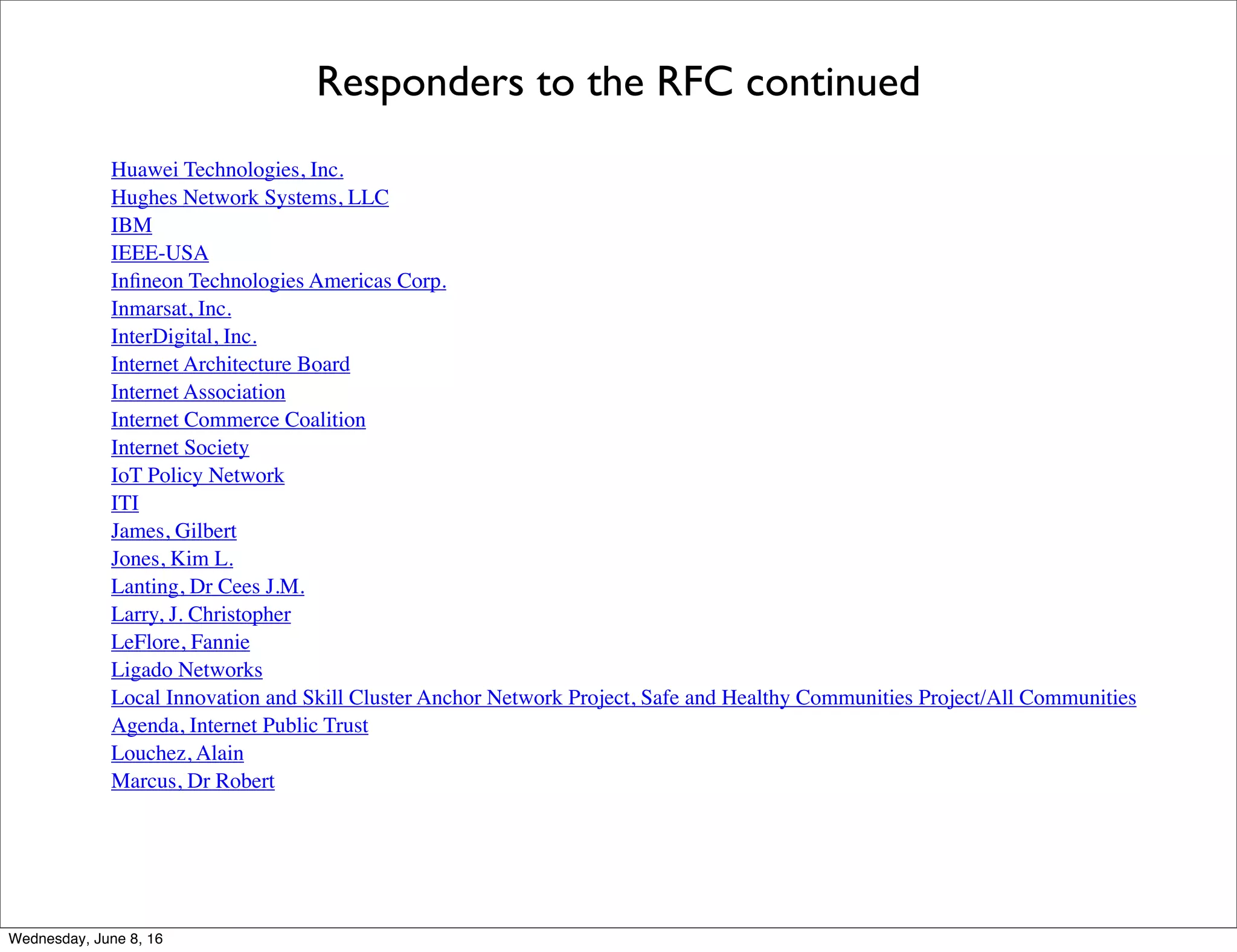
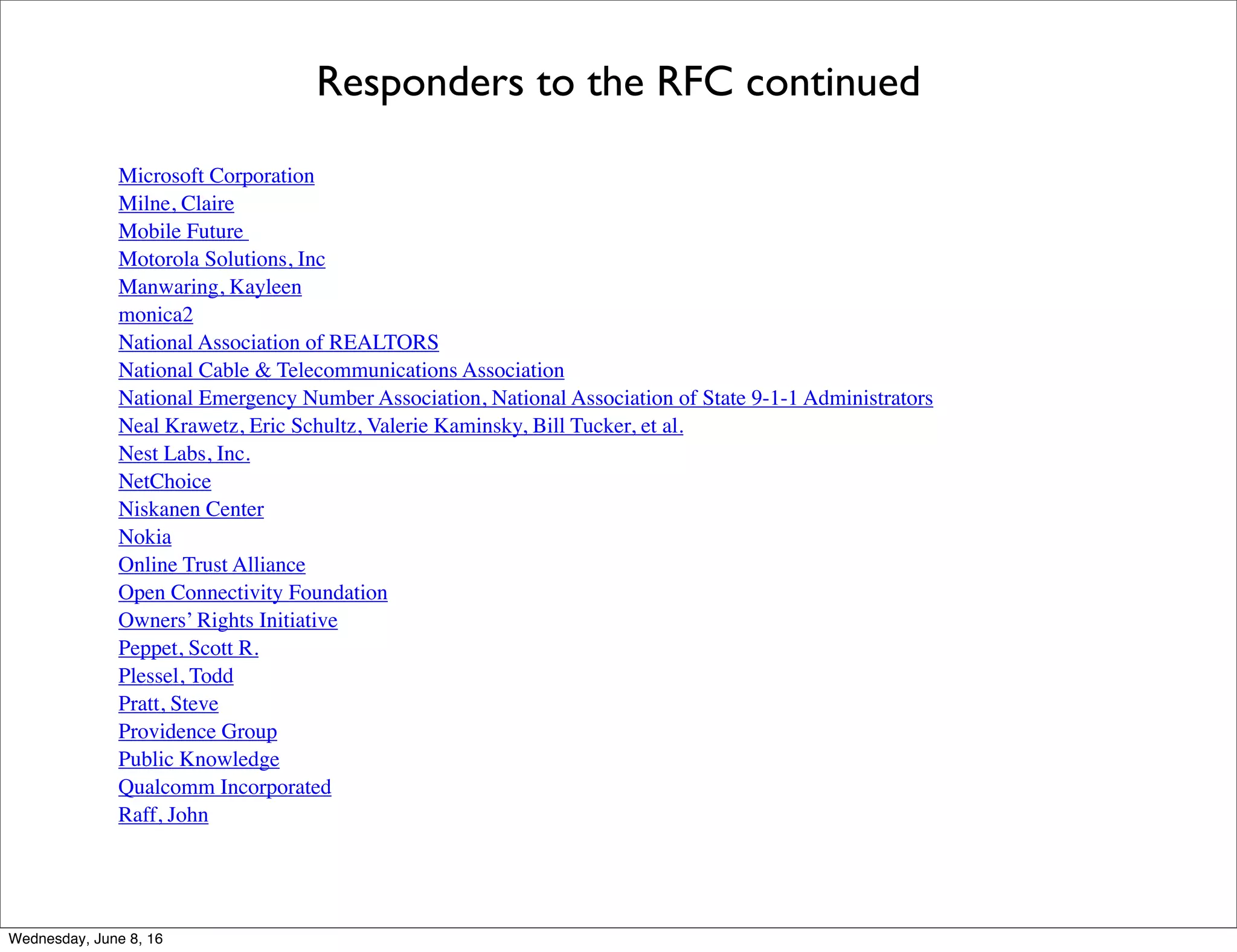
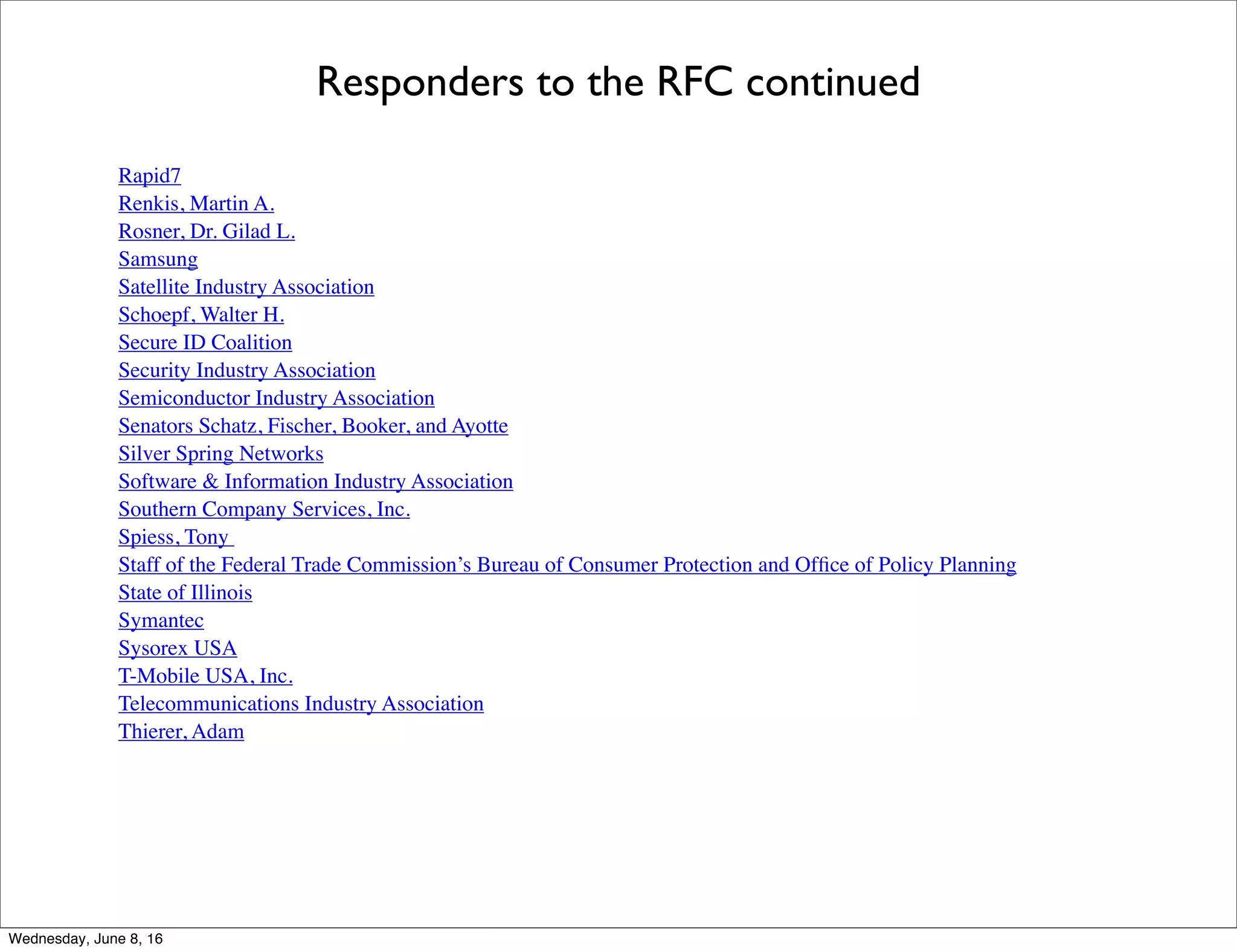
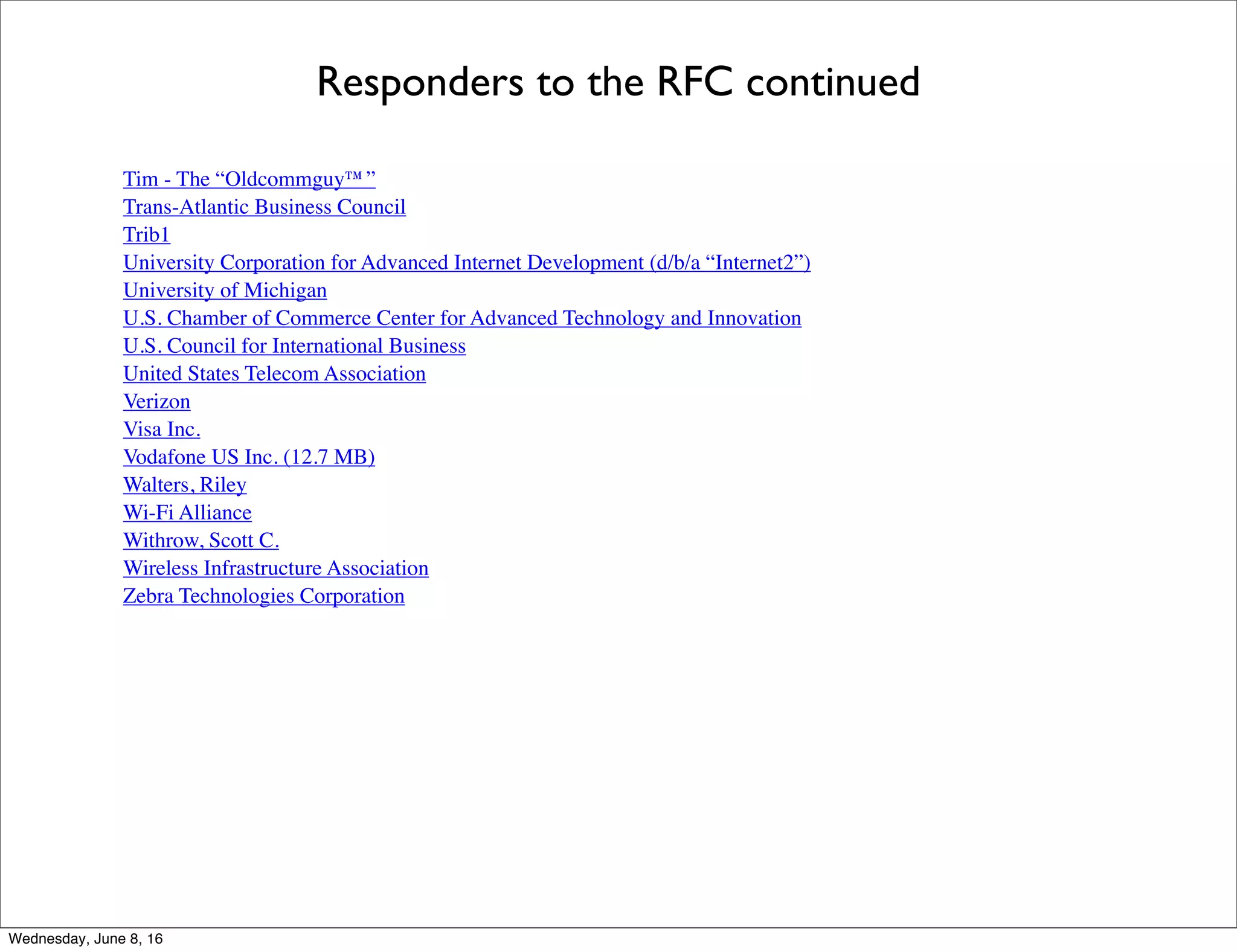
The document outlines questions posed by the National Telecommunications and Information Administration (NTIA) regarding the Internet of Things (IoT) landscape. Specifically, it discusses 27 questions across various topics such as technology, infrastructure, economy, policy issues, international engagement, and additional issues. It also lists 132 organizations that responded to NTIA's request for comment on developing an IoT strategy and policy.