Embed presentation
Downloaded 14 times
![Contact Information John S. Quarterman [email_address] Gretchen K. Phillips www.internetperils.com book: Risk Management Solutions](https://image.slidesharecdn.com/no-substitute-for-ongoing-data-quantification-visualization-and-storytelling-29557/75/No-Substitute-for-Ongoing-Data-Quantification-Visualization-and-Story-Telling-7-2048.jpg)
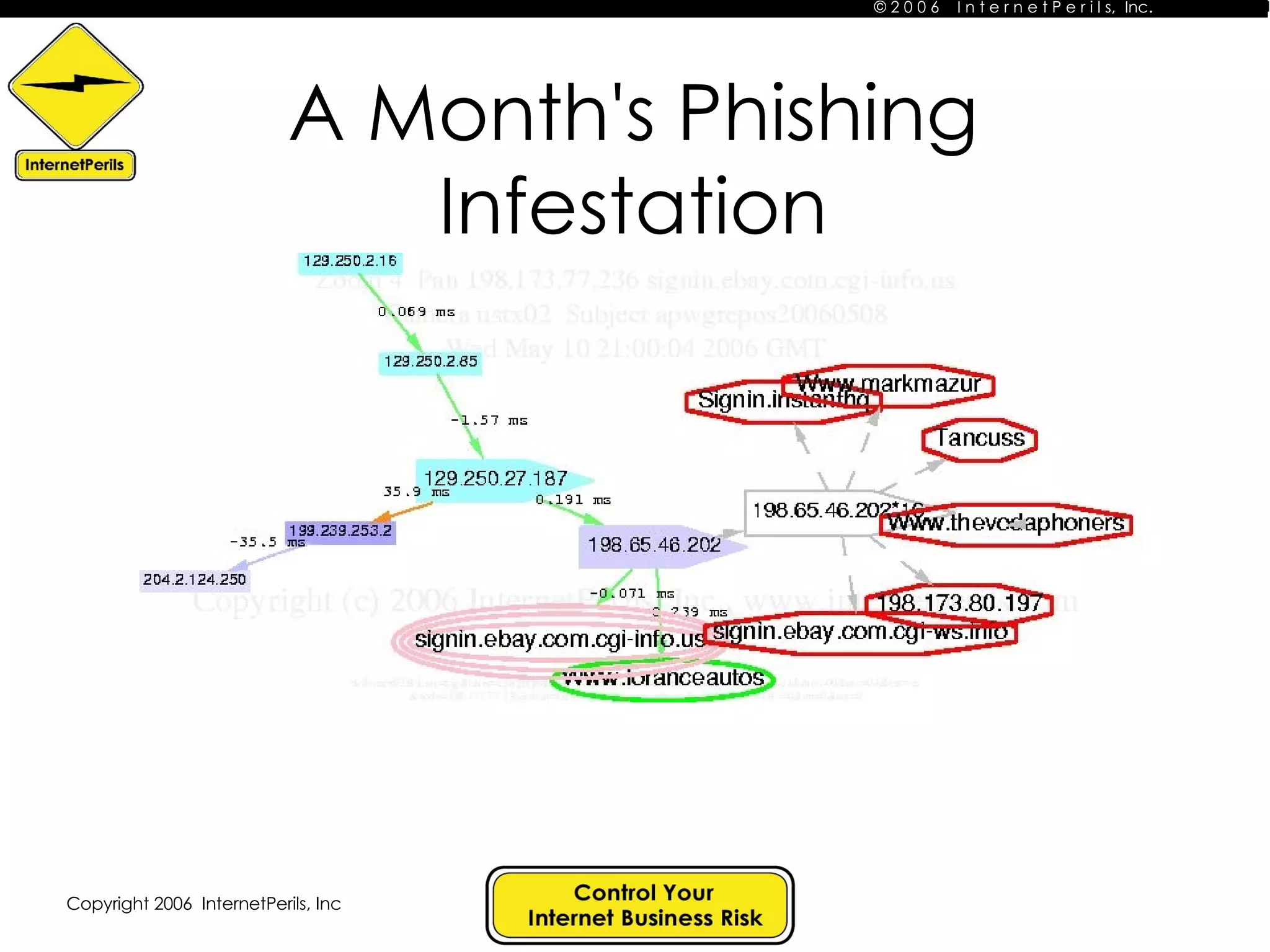
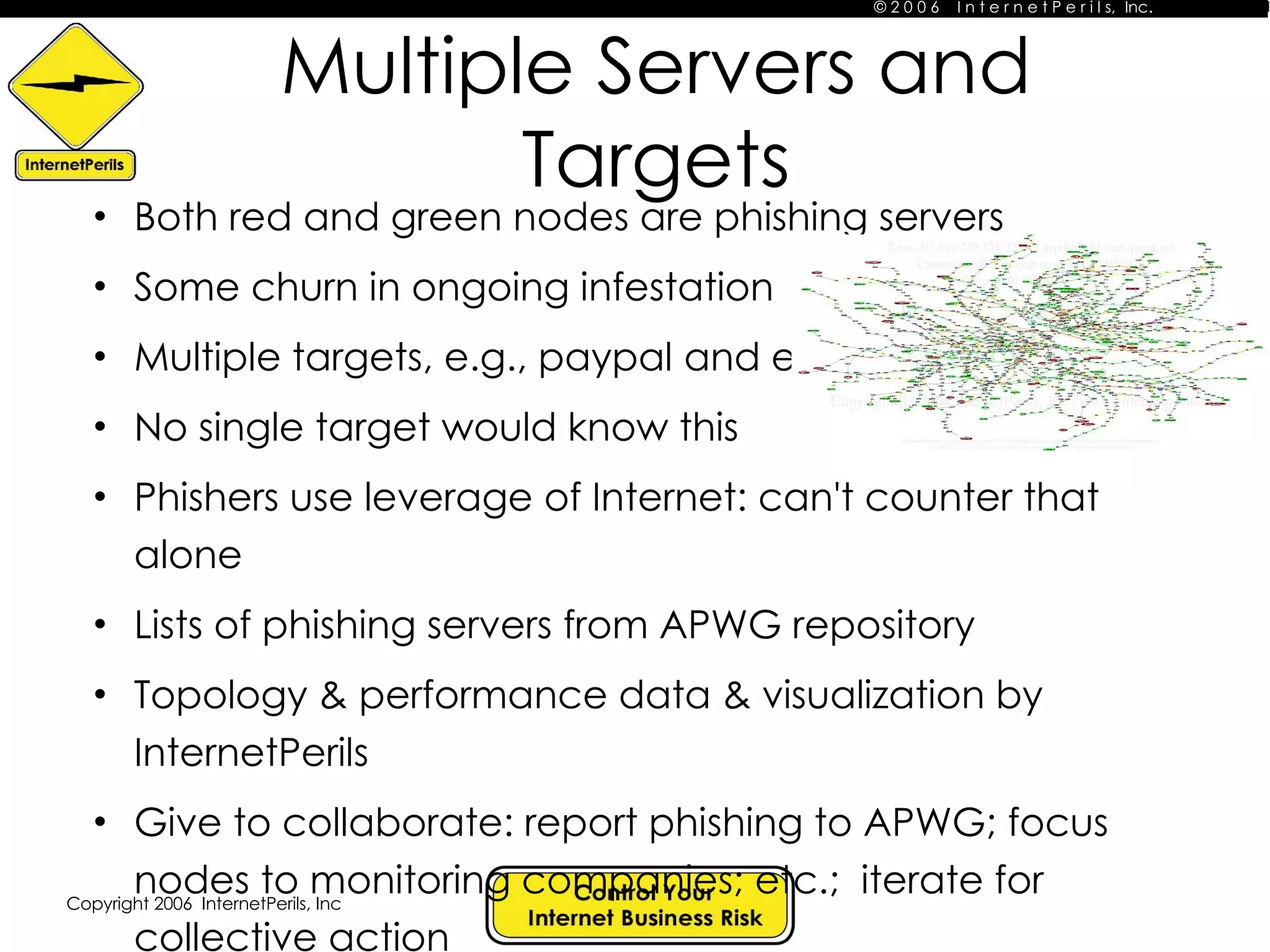
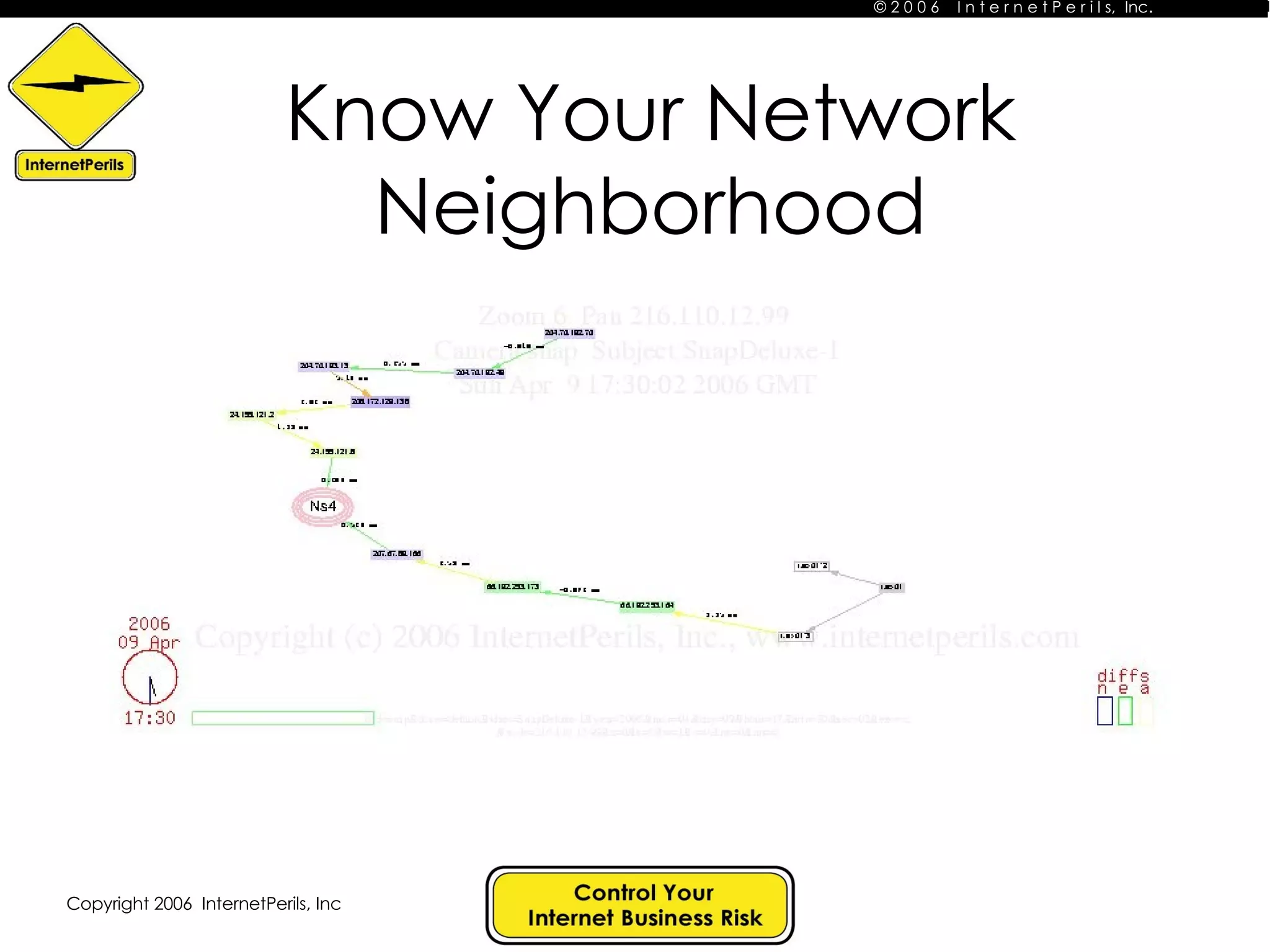
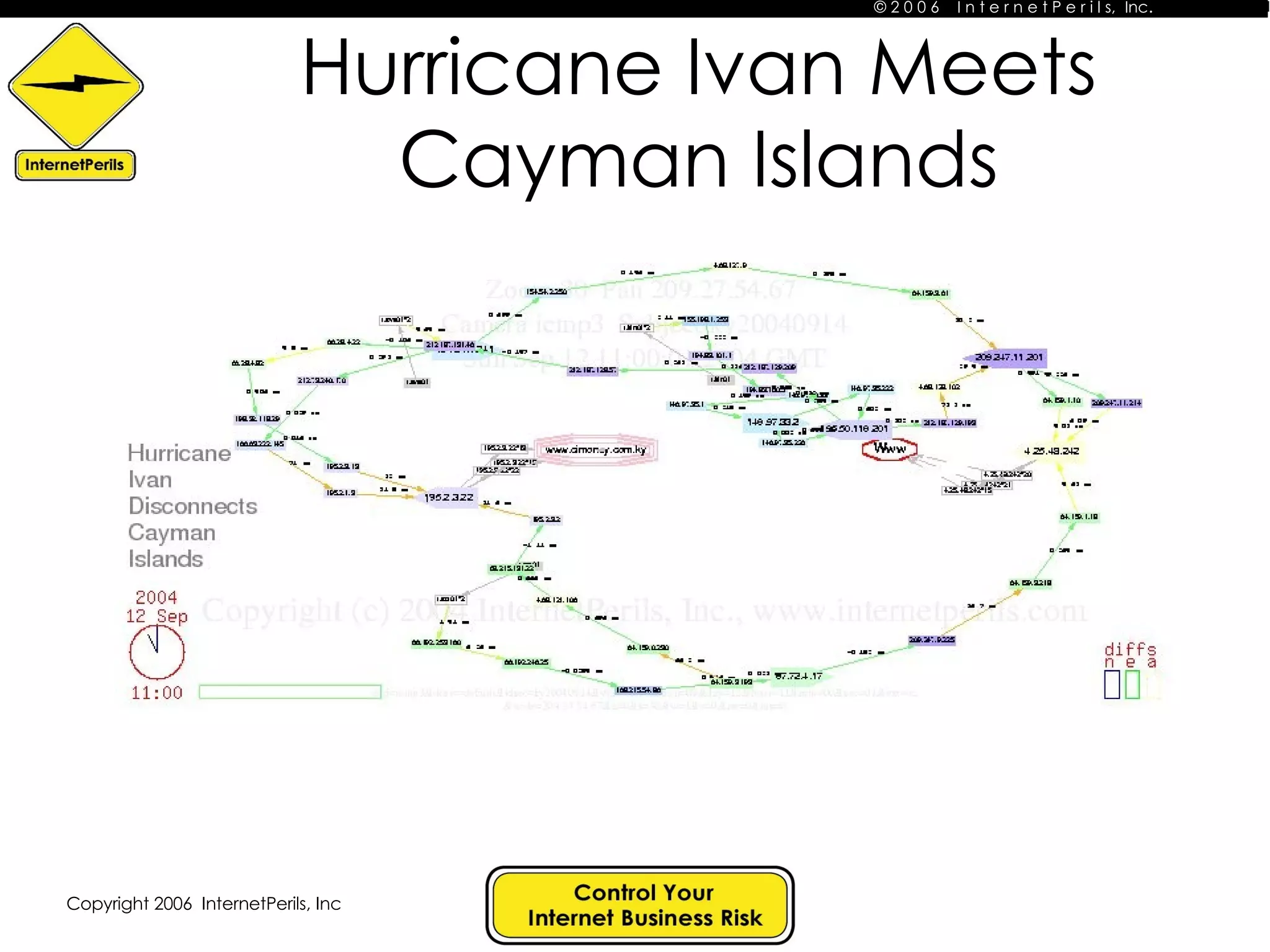
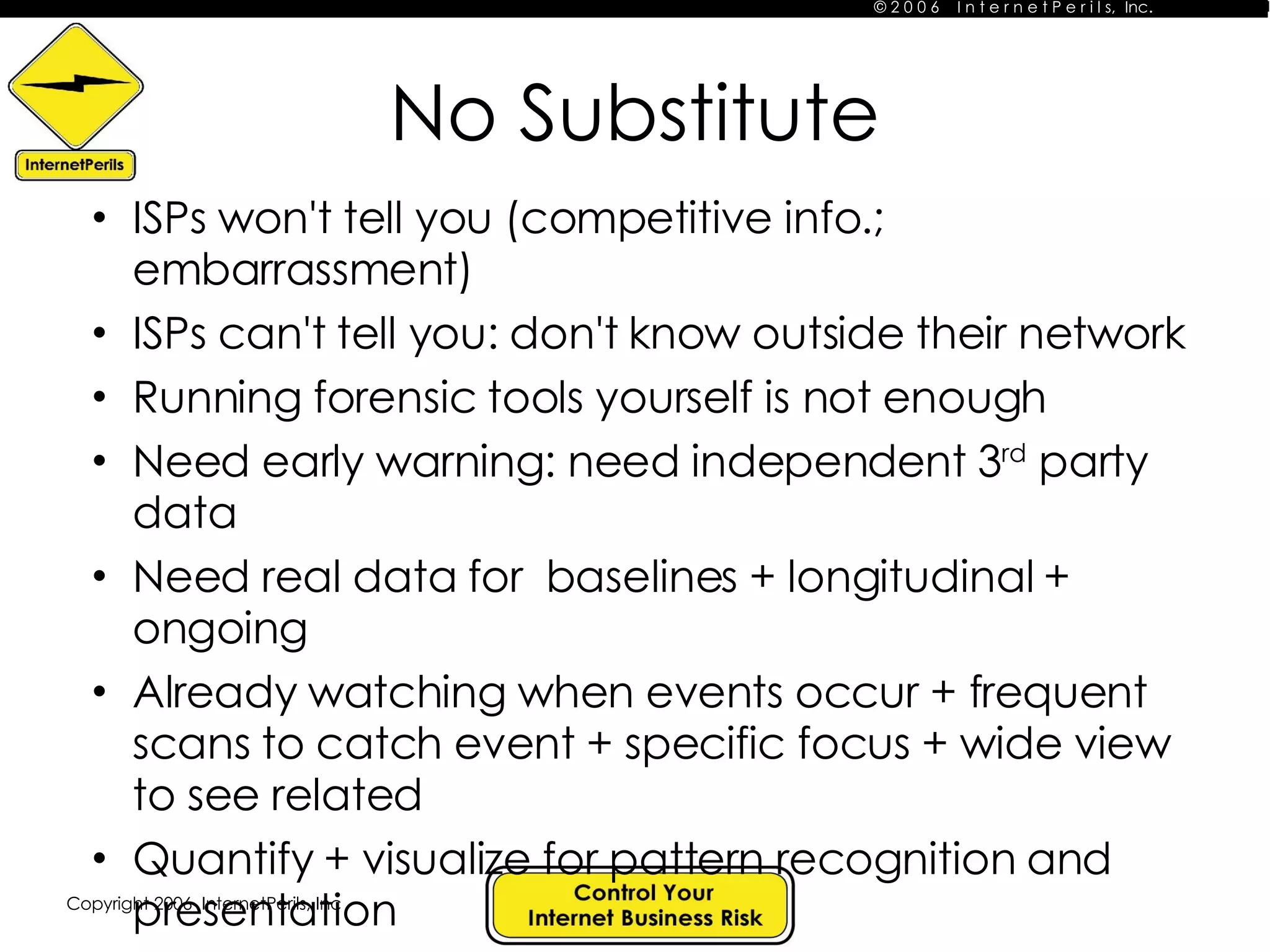
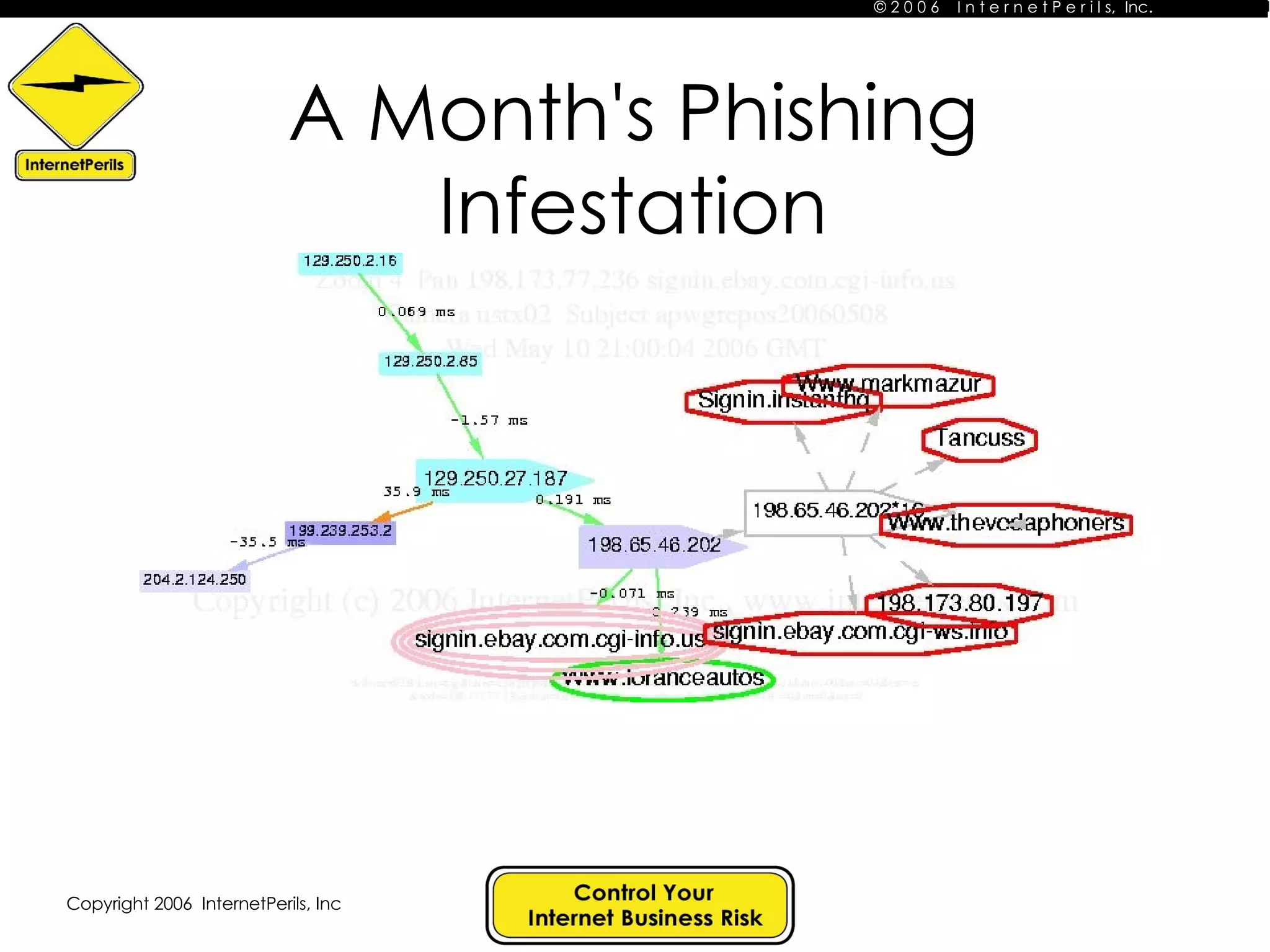
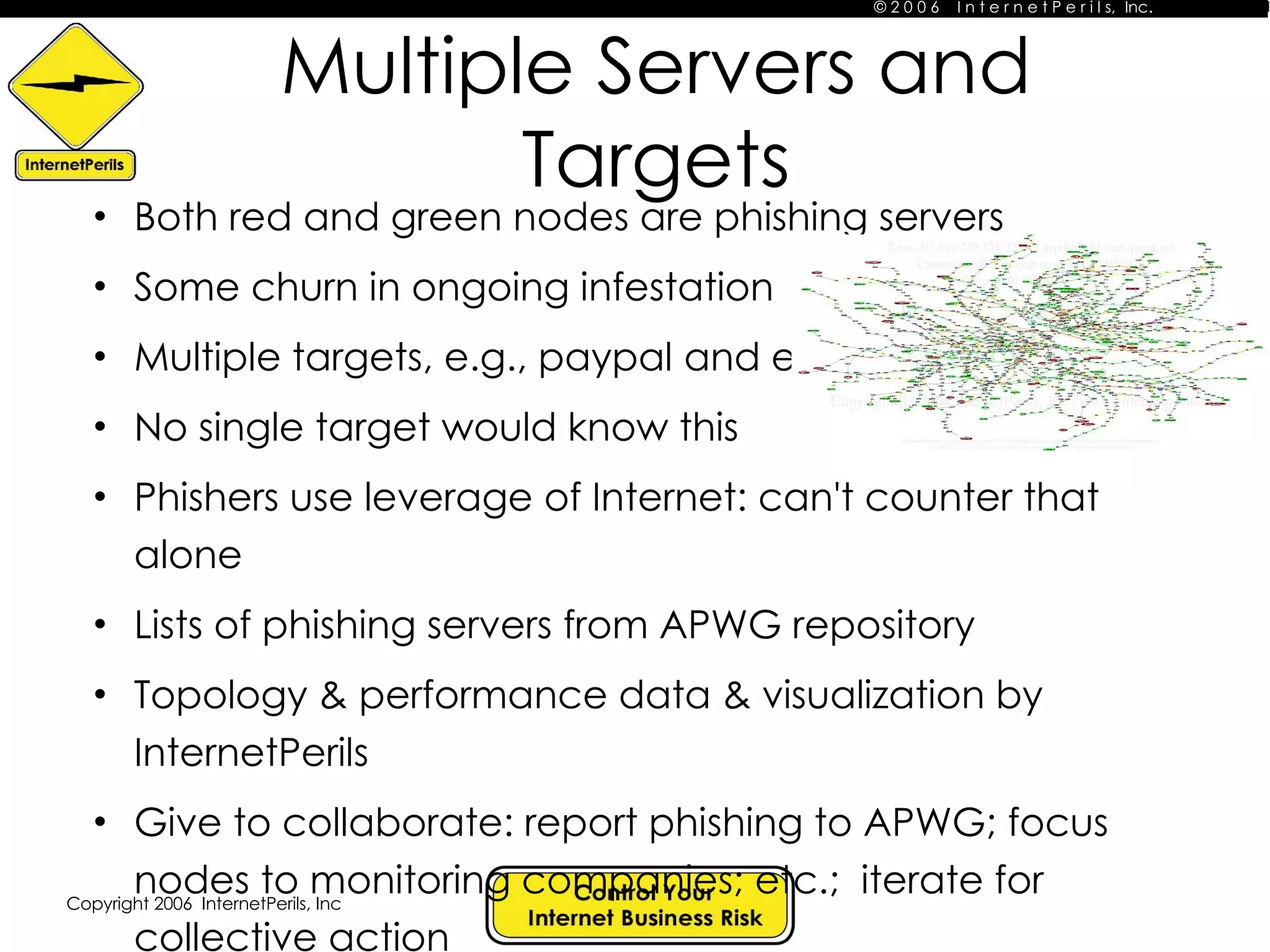
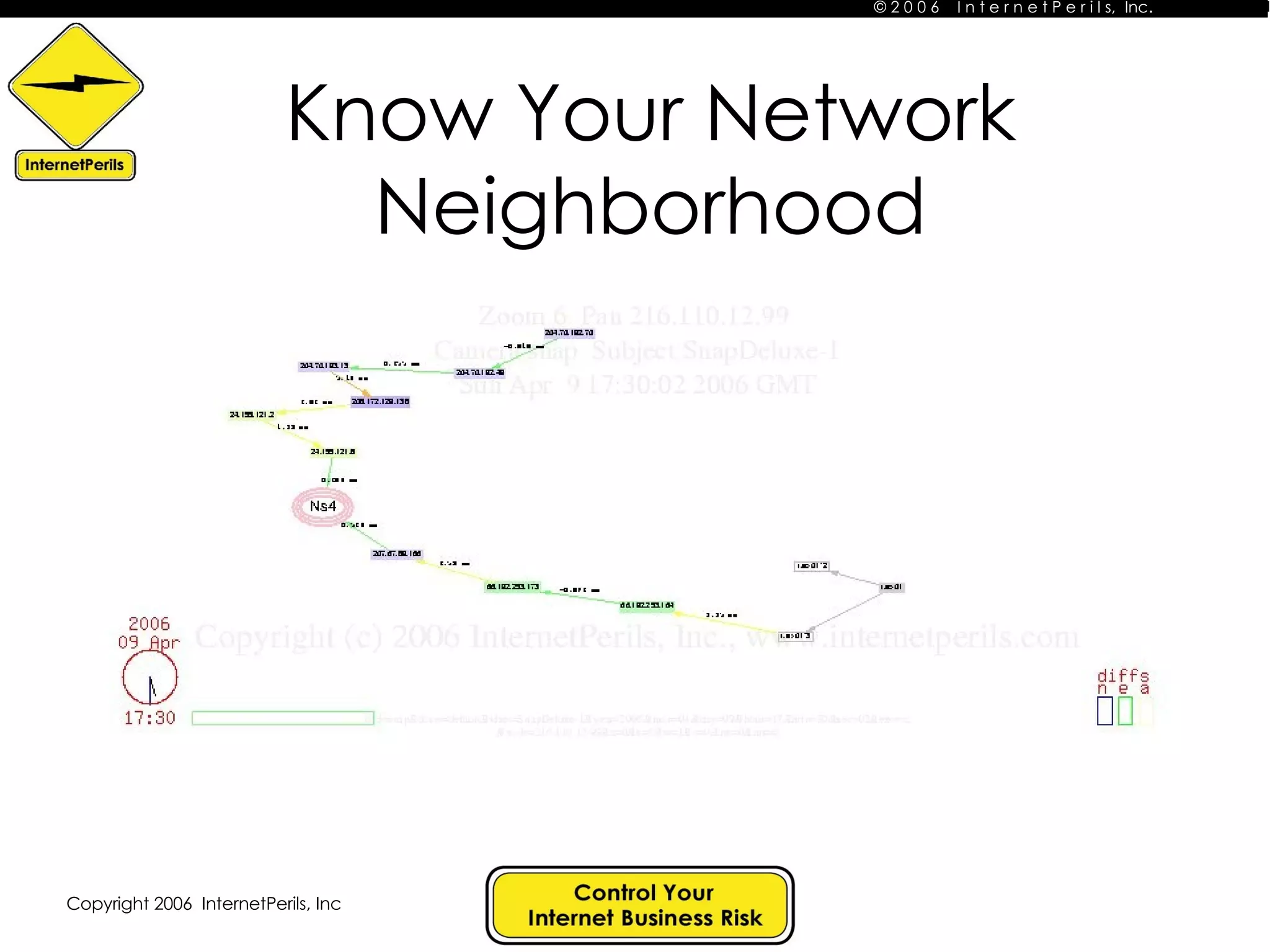
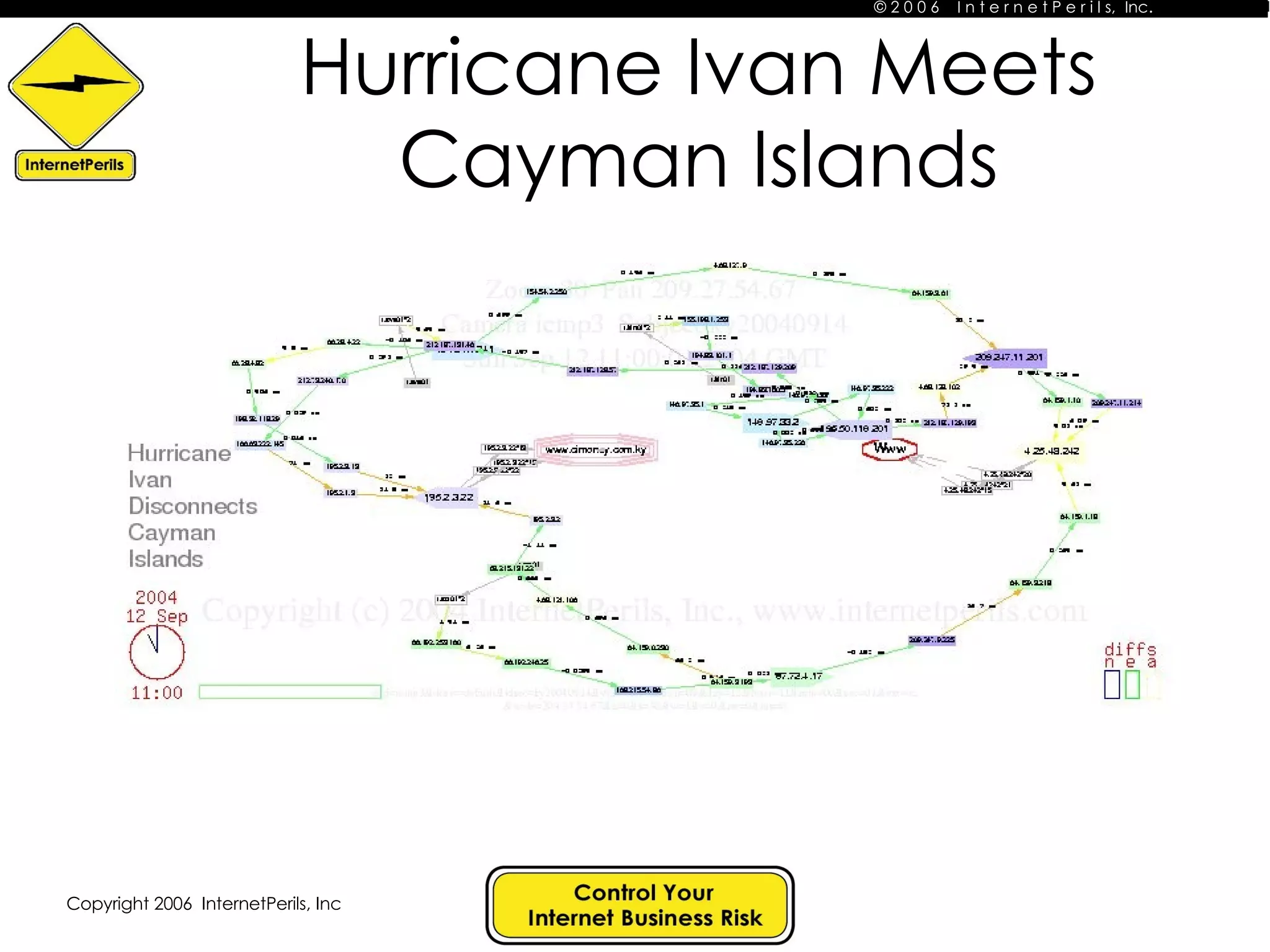
The document discusses the importance of ongoing data collection, quantification, visualization, and storytelling to monitor and address issues on the internet. It provides examples of how phishing attacks can involve multiple servers targeting different organizations over time. It also stresses that internet service providers cannot provide a full picture on their own due to competitive and other limitations, highlighting the need for independent third party monitoring to detect patterns and events.
![Contact Information John S. Quarterman [email_address] Gretchen K. Phillips www.internetperils.com book: Risk Management Solutions](https://image.slidesharecdn.com/no-substitute-for-ongoing-data-quantification-visualization-and-storytelling-29557/75/No-Substitute-for-Ongoing-Data-Quantification-Visualization-and-Story-Telling-7-2048.jpg)