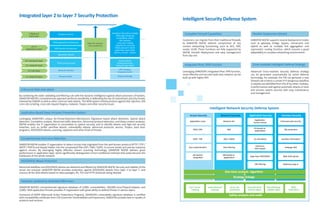
SANGFOR provides next-generation firewalls (NGFWs) that offer several key advantages over traditional firewalls:
1) NGFWs provide deep packet inspection and bidirectional traffic analysis to defend against modern application layer attacks.
2) They leverage single-pass analysis algorithms and multi-core parallel processing to achieve high 10G throughput while introducing low latency.
3) In addition to application layer defenses, NGFWs also include traditional firewall capabilities like stateful inspection, IPS, and integrated IPsec VPN.