News letter july 13
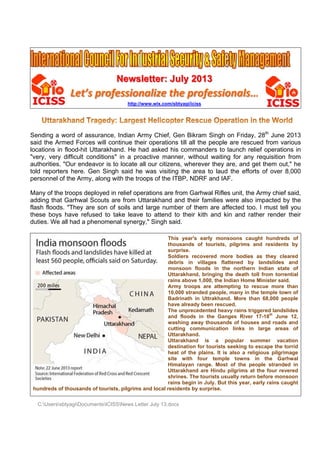
- 1. C:Users Sending a said the A locations "very, ver authorities told repor personnel Many of th adding tha flash flood these boy duties. We hundreds ssbtyagiDoc Let’ a word of a Armed Forc in flood-hit ry difficult s. "Our end rters here. l of the Arm he troops d at Garhwa ds. "They ys have re e all had a of thousand cumentsICIS ’s prof assurance ces will co t Uttarakha conditions deavor is t Gen Sing my, along w deployed in al Scouts a are son of efused to t phenomen ds of tourist SSNews Lett Newsl fession http://w , Indian Ar ontinue the and. He ha " in a pro to locate a gh said he with the tro n relief ope are from Ut f soils and take leave nal synergy ts, pilgrims ter July 13.do letter: J nalize t www.wix.com rmy Chief, eir operatio ad asked h active man ll our citize was visiti ops of the erations are ttarakhand d large num e to attend y," Singh s T th su S de m U ra A 10 B ha T an w cu U U de he si H U sh ra and local re ocx July 20 the pro /sbtyagi/iciss Gen Bikra ons till all th his comma nner, witho ens, where ng the are ITBP, NDR e from Gar d and their mber of the to their k said. his year's housands o urprise. oldiers reco ebris in v monsoon flo ttarakhand, ains above 1 Army troops 0,000 strand Badrinath in ave already he unpreced nd floods i washing awa utting com ttarakhand. ttarakhand estination fo eat of the p ite with fo imalayan ra ttarakhand hrines. The ains begin in esidents by s 013 ofessio s am Singh o he people anders to l out waiting ever they a ea to laud RF and IAF rhwal Rifles families w em are aff kith and ki early mons of tourists, overed mor villages flat oods in the bringing th 1,000, the In s are attemp ded people, Uttrakhand been rescu dented heav in the Gang ay thousand mmunication is a po or tourists s plains. It is our temple ange. Most are Hindu p tourists usu n July. But t surprise. onals… on Friday, are rescue aunch relie g for any are, and ge the efforts F. s unit, the A were also i fected too. n and rath soons caug pilgrims an re bodies a ttened by e northern he death tol dian Home M pting to res many in the d. More tha ed. vy rains trigg ges River 1 ds of houses links in opular sum seeking to e also a relig e towns in of the peo pilgrims at t ually return this year, ea … 28th June ed from va ef operatio requisition et them ou s of over 8 Army chief mpacted b I must te her render ght hundred nd resident as they cle landslides Indian stat ll from torre Minister said scue more e temple tow n 68,000 pe gered lands 17-18th June s and roads large area mmer vac escape the t gious pilgrim n the Gar ople strande the four rev before mon arly rains ca 2013 arious ons in from t," he 8,000 f said, by the ll you r their ds of ts by eared and te of ential d. than wn of eople slides e 12, s and as of ation torrid mage rhwal ed in vered soon aught
- 2. C:Users We s laid d ever stren ssbtyagiDoc alute al down th lasting ngth to b cumentsICIS ll the br heir live peace bereavin SSNews Lett rave hea es to sa to dep ng fami ter July 13.do arts invo ave oth parted s ly mem ocx olved in ers’! W souls a bers to n rescue We also nd pray bear th e opera offer p y to Go he loss! ations w rayers f od to gi who for ive
- 3. C:Users As the rise, co the org need to importa The wo infrastr causing This w Consul poses t the co mechan stateme code a learning Howeve uniform noted t exploite Stuxne infrastr "Contro designe to prote closed expose some ti Organis security environ growth times, o change need to the pote The urg centre running ssbtyagiDoc popularity ompanies a ganisation o ensure ance of wh orm is a ucture and g chaos by worm was ting Servic to SCADA ode compl nisms I've ents. Typic and heavily g how to p er, he said m as there that Stuxne ed, while o t is a worm ucture suc ol systems ed to be ef ect them, a environme ed to the sa ime until th sations cu y for these nment, as witnessed organisatio e with seam o ensure th ential to flo gency of th was a wor g Siemens cumentsICIS of supervi across the with seam that threat ich was rec new form d has alre y slowing d recently b ces at sec A and other exity of t written loo cally, a mo y nested st rogram." d Stuxnet are at lea et did not h one of the m with its c ch as powe are desig fficient and and many ents," he to ame types hey can "st rrently util e systems well as im d in supervi ons across mless upgra hat advanc oor nationa his was hig rm by the SCADA s SSNews Lett isory contr globe are mless upgra ts to it are cently high of securit eady made own intern rought und curity vend r control sy the virus, oks for ama ore advanc tatements also has ast four ve have many vulnerabili crosshairs r plants. gned aroun d reliable. A don't even old. The ex of threats and alone" ising SCA and protoc mplementin isory contr the world ades. But a ed security al infrastruc ghlighted la name of S ystems in ter July 13.do rol and dat seeking ho ades. Alon e countere hlighted by ty threat w e waves by al process der the sp dor Securic ystems an and told ateurish mi ced progra is a fairly some very ersions, tw y of the Mi ities was a "targeted" nd having A lot of the n have pas xpert noted that are co " against m ADA system cols and e ng method rol and data are contin as well as y measures cture. ast year by Stuxnet. It manufactu ocx ta acquisiti ow to effec ngside opt ed with ad a global at which repr y affecting ses. potlight by con, who d how to d InternetN stakes in c ammer wil typical mi y advance wo of which icrosoft vu a link short " on SCAD the minim se system ssword ac d that SCA ommon on modern atta ms are ex establishing ds to coun a acquisitio ually findin optimising s are in pla y news of infected te uring and u on (SCAD ctively man imising the dvanced s ttack by a w resents a g Iran's we Tom Park attempted defend aga News.com:" code like he l be aware istake amo ed compon h have sig lnerabilities tcut file iss DA control um require s are relian ccess as th ADA system the interne acks. ploring ho g secure s nter securi on (SCADA ng new wa the SCAD ace to coun a high-pro ens of thou utilities org A) system nage any c e SCADA ecurity me worm know potential eapons pro ker, directo to uncove ainst them " One of eavily nest e of efficie ong people nents and gnificant d s in it that sue. Mr Pa systems, p ed function nt on other hey've bee ms are not et and it wi w they ca systems in ty risks. W A) systems ys to effec DA system, nter extern ofile global usands of W anisations s continue changes wi system, fi easures – wn as Stux risk to crit ogramme or of Secu er the risk . He analy the anal ted conditio ency issue e that are is not enti ifferences. later versi arker said particularly nality - the r infrastruc n operatin used to be ill therefore an standard an integra With the ra s during rec ctively man firms cruc nal threats w attack – a Windows P , most nota es to ithin irms the xnet. tical and urity ks it ysed ysis onal s in just irely He ions that y for ey're cture g in eing e be dise ated apid cent nage cially with at its PCs ably
- 4. C:Users in Iran. an indu Industr distribu and co actuato that led the birt amplifie Writing Ratcliffe lacking for sec variable factorie outside Influenc ago tha Centre urging infrastr a focus As the wherev govern place t system Mr Rat millions group o effort t creating departm The ch carrying Vulnera those t be equ likes of the atta ssbtyagiDoc Stuxnet p ustrial contr ial network uted, integr ontrolling to ors upgrade d to the cre th of new t ed somewh for Publi e, said rec . "Everythi curing the es and cau es and pum e world," he ced by wo at SCADA for the Pr companies ucture und ssed progra BSIA's Mr ver industr ment interv to keep fir ms has give cliffe conti s of pound of cybercrim o attack i g simple e ments wen hallenge fo g them int abilities in S hroughout ually – if no f PayPal a ackers. And cumentsICIS roved that rol network ks have ev rated syste oday's nat ed the bas eation of so technologie hat. cService.c cently that ng was tra data. Afte using the s mp halls an e explained ork underta systems w rotection o s to start m derstand an amme of w r Ratcliffe rial system vention wil rms on the n us an un nued: "Jus ds in ranso minals sho ndustrial n email virus t through w or industry to the futu SCADA sy e-commer ot significa nd Amazo d the battle SSNews Lett it is relativ k. olved from ems linked ional infras sic manual ophisticated es, the pot co.uk, the t as syste ansmitted a r all, the i system to f nd the proto d. aken in the were poten of National making sec nd mitigate work. pointed ou ms are con l be neede e right tra nhealthy co st like pirat om, the ide ould not be networks b es are als will eventua now is to ure with ro ystems may rce activity antly more n. Govern e to protect ter July 13.do vely simple m humble b directly int structure. A interface, d networks tential for t British Se ems becam across the idea of so fail or crash ocols were e US, Euro ntially vuln Infrastruct curity a ke e electronic ut, security ncerned. K ed continua ck. "The i onfidence," tes in 2010 ea of a pow e considere by organis o looking ally come t o keep inv bust layer y not be as y, for exam – devasta ments are t national in ocx to cause p beginnings to business As techno though it w s that servic things to g ecurity Ind me more c wire in cle omeone int h was unth e obscure a opean gove nerable to e ture (CPN y priority. c attack risk is and wil Key to ens ally, with th increase in he sugges 0 can hold wer plant b ed absurd. ed groups for a new towards ou vesting in a rs of ideall s headline- ple, but the ating than increasing nfrastructu potentially at standalo ses and re ology has d was the ad ce the indu o wrong a dustry Ass complex, th ear text, as tercepting hinkable, a and proprie ernments b external th I) in the U The CPNI ks, facilitat ll remain o suring that horough reg n IT-type sted. ships off being disa Not only is s, but indiv challenge ur industria and securi y impenet -grabbing a e fact rema cybercrimi gly recogni re rages o catastroph one plants esponsible developed dvent of mi ustry to this lso seems ociation's heir securi s there was the data, s these we etary, with began to r hreats. For UK has iss is helping ting these e of paramou t requireme gulation an architectur the coast o abled or tak s there now viduals no . The virtu l networks. ing its cru rable laye as other th ains that a nals' interf ising this, b n. hic damage , into the fu for monito , sensors croprocess s day. But w to have b (BSIA) Da ity was ra s no real n altering so ere installe no links to recognise l r example, ued direct g Britain's c efforts thro unt importa ents are m nd guidanc re for SCA of Somalia ken over b w a conce ow bored w ual war tha ." cial netwo rs of secu reats, such an attack co fering with but so too e" to ully- oring and sors with been avid ther need ome ed in o the long the ives core ough ance met, ce in ADA a for by a rted with at IT orks, urity. h as ould the are
- 5. C:Users Large n terroris location death r weapon high pr years. Airport arising any da greatly country protect Securit since th until mo though the Inte regulate Followi aircraft proposa the ado ssbtyagiDoc numbers o m and oth n.[2] Simila rate with a n may prov rofile natur security a or enterin ngerous si reduced. A y from any the countr ty has been he bombin ore recentl for some ernational ed by a bin ng the terr were use al to bring option of fra cumentsICIS of people p her forms o arly, the hi attacks on vide an all re followin attempts to g the coun ituations, il As such, a threatenin ry and their n a matter ng of a flig ly, been ad e time Stan Civil Aviat nding mech rorist attac ed as wea aviation s amework R SSNews Lett ass throug of crime be igh concen aircraft, a luring targe g the vario o prevent ntry. If airp llegal items irport secu g events, t r people. of concer ght above L ddressed o ndards an ion Organ hanism to g ks in the U apons of m security un Regulation ter July 13.do gh airports ecause of ntration of and the ab et for terro ous attack any threa port securit s or threat urity serves to reassure n for civil a Lockerbie on essentia d Recomm ization (IC guarantee United Stat mass destr nder the EU (EC) No 2 ocx every day the numbe people on bility to us orism, whet ks and atte ats or pote ty does su ts entering s several p e the travel aviation for in 1988. H ally a natio mended P CAO) for St their full an tes on 11 S ruction, the U's regulat 2320/2002 y, this prese er of peopl n large airl se a hijack ther or not empts arou entially dan cceed in th into aircra urposes: T ling public r several d However, a nal level. A ractices ha tates to im nd proper a September e Commis tory umbre of the Euro ents poten le located liners, the ked airplan t they succ und the gl ngerous s his, then th aft, country To protect t that they a ecades, bu aviation se At the inter ave been mplement, application r 2001 whe ssion made ella. This in opean Par ntial targets in a partic potential h ne as a le ceed due t lobe in rec ituations f he chance y or airport the airport are safe an ut in partic ecurity has rnational le laid down these are n. en commer e a legisla nitiative led liament an s for cular high ethal their cent from es of are and nd to cular , up evel, n by not rcial ative d to d of
- 6. C:UserssbtyagiDocumentsICISSNews Letter July 13.docx the Council of 16 December 2002 establishing common rules in the field of civil aviation security and thus provided the basis for allowing harmonization of aviation security rules across the European Union with binding effect. That regulatory framework has since been overhauled by a new framework, in full effect from 29 April 2010, as laid down by Regulation (EC) No 300/2008 of the European Parliament and of the Council of 11 March 2008 on common rules in the field of civil aviation security and repealing Regulation (EC) No 2320/2002. Rescinding the limitations on the carriage of small pocketknives on board aircraft was always going to be a challenge. Like so many other measures that the industry has introduced over the years, it is always easy to add security measures, yet far harder to take them away. The brouhaha that was initiated by the Transportation Security Administration’s (TSA) recent announcement that knives with blades shorter than 6cms, of a width less than 1.27cms at their widest point, without locking or fixed blades and without moulded handgrips will, from 25 April, be permitted in carryon baggage was to be expected, especially in the United States in light of the fact that box cutters (which will remain banned) were used in the perpetration of the attacks on 11th September 2001. The debate, which has become a huge political issue, emphasises three things. Firstly the problem with knee-jerk procedures being implemented as a response to a terrorist attack; secondly, the extent to which intelligent people fail to deploy common sense and allow their emotions to rule their decision-making processes; and thirdly, the frightening willingness of certain groups to hold onto politically acceptable security measures, such as the ban on knives, whilst rejecting effective, yet politically sensitive, security measures, such as profiling, whilst arguing the case that they are speaking on behalf of those who died in 2001. Some incidents have been the result of travellers being permitted to carry either weapons or items that could be used as weapons on board aircraft so that they could hijack the plane. Travellers are screened by metal detectors. Explosive detection machines used include X-ray machines and explosives trace-detection portal machines (a.k.a. "puffer machines"). In the United States the TSA is working on new scanning machines that are still effective searching for objects that aren't allowed in the airplanes but that don't depict the passengers in a state of undress that some find embarrassing. Explosive detection machines can also be used for both carry on and checked baggage. These detect volatile compounds given off from explosives using gas chromatography. A recent development is the controversial use of backscatter X-rays to detect hidden weapons and explosives on passengers. These devices, which use Compton scattering, require that the passenger stand close to a flat panel and produce a high resolution image. A technology released in Israel in early 2008 allows passengers to pass through metal detectors without removing their shoes, a process required as walk-though gate detectors are not reliable in detecting metal in shoes or on the lower body extremities. Alternately, the passengers step fully shoed onto a device which scans in under 1.2 seconds for objects as small as a razor blade. In some countries, specially trained individuals may engage passengers in a conversation to detect threats rather than solely relying on equipment to find threats.
- 7. C:Users Genera aircraft are dis screene any tim glasses items a A must reduce Do N Refra alarm Shoe detec includ Put bagg Carry includ Place com Refra you h proce have Decla bagg Prote Your C Carry mobi Take secu Place and b Do n Do n good ssbtyagiDoc ally people are locate charged fr ed if disem me. Airport s made ou as weapons read for an your wait t NOT pack o ain from c ms, screene es, clothin ctor. As a de pat dow all unde gage. Chec y-on bagga de laptops e identific puter. The ain from p hand your ess the ba e limited lia are fire arm gage. ect yoursel Cabin / Ca y all metal ile phones, e your lapto rity checkp e your ove blazers nee not leave y not accept ds. cumentsICIS are screen ed. These rom airliner mbarking fr food outle t of glass s. nyone trave time at the or bring pro carrying un er will need ng items a result the wn frisking. eveloped cked bagga age is limit , purses, s ation tags ese are on acking val baggage t ggage in t bility for los ms and am f and do no arry-on Ba l items in , pagers, a op and vid point. ercoat or ja ed not be r your bagga t baggage SSNews Lett ned throug areas are rs into the rom a dom ets have st and utensi eling by air security ch ohibited ite nverified gi d to unwra and other screener films and age screen ted to one small backp s on all yo ne of the m luable item to your air he prescrib st, damage mmunition t ot pack val ggage your carry nd persona eo camera cket in the removed, u age unatte e from stra ter July 13.do gh airport s often calle sterile are mestic flight arted using ils made o r! Followin heckpoint. ms to the a ifts or pres p it to inve accessor will require d camera ning equipm carry-on b packs, brie our bagga ost forgotte ms in your r carrier, se bed manne ed, or stole to your airl luables in y y-on bag. T al data ass a out of the e tray at the unless requ ended angers. It ocx security into ed "secure" ea so that t t; however g plastic g out of meta g tips will h airport. sents in w stigate the ries that c e you to u as with f ment may d bag plus o fcases, or ge. Don' en items at checked b ecurity staf er Please en items. line and pl your check This includ sistants (PD eir case an e security s uested by t t may cont o areas wh ", "sterile" they usuall r they are lasses and al to reduce help you wrapped pa e source of contain m undergo fu film in y damage un one person camera ca 't forget t Screening baggage ( ff of the ai keep in mi ace it in yo ked baggag des jewelle DAs). nd place in screening the screene tain prohib here the ex and airside ly will not h still subjec d utensils a e the usefu ackage. If the alarm. etal will al rther chec your Cabi ndeveloped nal item. P ases. Reme to label g Checkpo Regd. Bag ir carrier w ind that mo our checke ge. ery, loose the tray p Checkpoin er. ited items xit gates to e. Passeng have to be ct to searc as oppose ulness of s f the pack arm the m cks which m in (carry- d films. Personal ite ember, 1+1 your lap oints. ggage). O will handle ost air carr ed / registe change, ke provided at nt. Suit jack or danger o the gers e re- h at d to such kage metal may -on) ems 1. ptop Once and riers ered eys, t the kets rous
- 8. C:Users Prepar Necess airport the sec to pack smart. Dr Securit and ac through P There a All of y measur you wi F You're travel s or trave A You ca journey the term of the te S Familia active r ssbtyagiDoc rations sary prepa which will curity proce k for your ress ty does no ccessories h the scree Pack Smar are restrict your bagga res. This in ll find tips Final Chec dressed, safe and s el agent for Access Re an enter in y or a valid minal. Wait erminal for Security Pr arise yourse role in ensu cumentsICIS arations ca help you t esses. Here trip. We've ot require a can set o ening points rt tions on wh age will be nspection m s to help y klist packed an smart. Rea r additiona quirements to the pas airport ent tlisted pas r confirmat rocess and elf with th uring your SSNews Lett an be mad o move mo e you will f e also inclu any particu off an alarm s. Here yo hat you ca e screened may includ you pack. nd ready t ad the instr l informatio s ssenger ter try permit. sengers ar ion of their d Procedure e Security own safety ter July 13.do de by you ore quickly find sugges uded a pre ular style o m on the m ou will find an pack in y d and pos de emptying to go. Here ructions pr on. rminal if yo Visitors ca re advised r tickets. es y Process y and avoid ocx u before a y and effici stions on w e-flight che or type of c metal dete d tips to he your hand ssibly hand g most or a e is a pre inted on th ou have e an buy ticke to contact and Proce d inconven arrival at t ently throu what to wea ecklist to h clothing. H ector and m elp you baggage a d-searched all of the a e-flight ch he air ticket ither a con et to enter t the airline edures. It w ience to yo the ugh ar to the ai help you to However, ce may affect and registe d as part o articles in y hecklist to t and conta nfirmed air into the vi es office o will help y ourself. irport and h o travel saf ertain cloth t the pax f ered bagga of the secu your bag. H o help you act your air r ticket for isitor’ s are n the lands ou to play how fe & hing flow age. urity Here u to rline the ea in side y an
- 9. C:Users On 30 M Gaurav Chenna Inspecto from Mo him (Ca My son complai compan cheated Governm was to b non-bai Chenna cancelle My son, been st was ver of the c House C the RB against there wa or letter one of u could no Kumar case. H by me in him befo against After re initially s 10 minu Narinde Narinde as he h meet hi him aro should c Mr. Ran in that c contact was to b he said Sudhir W ssbtyagiDoc May 2013 a Bhatia (Mo ai on 3 May or Rana fro ob. No. 088 apt Gaurav n asked hi int and how ny only a fe d RBI and fo ment Lawye be present l able arres ai Police. O ed and he w , quite worr ated in Par ry upset and ase. He sai Court at 11 I failing wh him and se as a proced r to this effe us. He told ot read and (Mob No 0 e also warn n next 10 m ore 1150 hr Gaurav Bha peated ring said he cou utes. In bet er Kumar h er Kumar an has not paid m in Patiala ound 4 pm. come to Ga na had said case, I shou him and he be deposite I should b Walia, Senio cumentsICIS around 1115 ob No 0994 y 2013, stat om the Spe 800879719. Bhatia) und m what cr w he got his ew days bac or more det er at Patiala in the court st warrant w Once he w would lose h ried, rang m ra one abov d rang Mr. R id Gaurav B 50 hrs. on hich non-ba ent to Chen dure on reco ect has eve me that sin d tell me the 0954026321 ned me repe minutes after rs. or else h atia. ing, I was f uld not reco tween I got has issued nd he said R d the bank a House & I asked him ate No 2 an that the de uld rush to n e would giv ed. I told him etter rush t or Lawyer o SSNews Lett Co Industr 5 hrs. I got 046xxxx), w ting that on ecial Branch He told him der IPC Sec rime he ha s new Chen ck? Mr. Ran tails he sho a House imm t at 1150 hr would be is was arreste his job too. me immediat ve and SMS Rana immed Bhatia was r 30 May 20 ailable warr nnai Police overy of due er been rec nce the cas e details an 18), Govern eatedly that r talking with he would is finally throu llect the cas t again call ‘hold’ ord RBI has file Rs 76200.0 he said he m his cham d ask anyo adline was nearest ICIC ve the accou m what deta to the bank of the Supre ter July 13.do ol N N Bha rial Securi mobile call who has join e person w h (Crime) D m that there ctions 406, ad done, w nnai number na said he uld contact mediately a rs. on 30 Ma ssued agai ed his pass tely and app Sed me Mr. diately and a required to 13 in cheat rant of arre for his arre es by gover ceived by G e file was 1 d that I sho nment Lawy required ac h Narinder K sue non-ba gh to I Mr. se and I sho from Rana er on the ed a case ag 00 dues sin was very b mber /office ne for him. 1150 hrs. o CI Bank with unt number ails I need t first & ring eme Court w ocx atia (Retd) ty Consul l from my s ned new co who said he Delhi Police e was a cas 420, 468 a who has lo r given to h (Gaurav Bh Mr. Narinde s he (Gaura ay 2013 fail nst him an sport etc. w praised me Rana’s mo asked him t be present ting case re est would b est. I asked rnment and Gaurav Bhat 12-13 pages ould contact yer dealing ction should Kumar and ail-able arres Narinder Ku ould ring hi a wanting t case. I ag gainst Gaur nce long. I d busy & I sho location & When I told on 30 May, h h a cheque r in which th to fill in the g him from t who lives in tant son - Capt ompany in was Sub rang him se against and so on. odged the him by his hatia) had er Kumar, av Bhatia) ling which nd sent to would be what has obile No. I the details in Patiala eported by be issued d him that no notice tia or any s long, he t Narinder g with the d be taken I must tell st warrant umar who m after 5- to know if gain rang rav Bhatia desired to ould meet he said I d him that he replied book and he money challan & there. Mr. n Noida, is The aut veteran than thre colourful various c staff func had a v mentiona with Bureau w associate inspectio of indus measure by P governm establish An avid prolific Bhatia freelance the field Security Managem passiona in efforts Indian P Pakistan reached narindra_ mail.com thor is a having m ee decades service command ctions. He a very long able ten Intellige where he w ed on and au strial secu s underta PSU ent ments. reader writer, is n e consultan of Indus & Sa ment. He ately invol for releas POWs held . He can by e-mail _bhatia@h m army more s of in and also and nure ence was in udits urity aken and and Col now nt in strial afety is lved e of d in be at - hot
- 10. C:Users my relat both Mr I had ta Bosses’ wahi sh Meanwh checked on 30 M name N number Kumar practicin there is avoidab to be in years af mobile referred A piece persona number Anirud Dear Si which to identifie property their live On 21st employe recovere and bur from se The wh 22nd Feb The abo worker Marxism Thanks Anirudh ssbtyagiDoc tive and wa r. Rana & M aken. I told ’ and would uru karta hu hile, Mr. W d from the P May 2013. H Narinder Ku r of times to once lifted ng in Supre no commu ble tension a nvestigated fter retiring numbers of d to Special of advice-p al details lik rs, car numb dha Singh r, Thanks ook place on ed and pun y of owner elihood and Feb 2013, ees of an i ed on 21st i ried in jung rvice due to ole busines b, too. ove two inc relations an m. & Regards ha Singh, D cumentsICIS s away to C r. Narinder him I was act on wha un’ or words alia told me Patiala Hous He also got mar and no o Rana and the phone me Court he nication wit and appears and crimina from the A f Rana and Branch Del please ensu ke mobile n bers etc. so <anirudhs s for News n 20th Feb i nished, con on fire, but they suppo when Bhara industrialist n a jungle. le near Ran o dereliction ss world in cidents com nd role of G , Director SSNews Lett Chandigarh, Kumar. Soo s a former at they and M s to that effe e that it ap se Courts a t it checked one of them Narinder K e and whe e fumbled a th both Mr. R s to be part als punishe rmy, I conta Kumar are lhi Police fo ure you and numbers, re that the uns ingh@rsec Letter. I ha n Noida dur cerned trad t they have ort their fam at band was , had kidna They had k nchi. The c n on duty. H Ranchi and mpel us to Govt. There ter July 13.do I rang him on after Mr. Intelligence Mr. Walia w ect and han ppears to be and no case d that there m had Mobil Kumar. Whil en Mr. Wali answering M Rana and M of organise ed. Since I h acted some e fake and f r further inv d your family esidential / scrupulous curity.in> ave gone th ring trade u de unions put their o ily by earnin s going on, apped the o killed bruta conspirator w He apologize d Jharkhand rethink abo is need to r ocx for consulta Rana again e Bureau O would advise ged up. e well orga e RBI versus were 5 law e number a e Mr. Rana ia told him Mr. Walia’s q Mr. Narinder ed cyber / w had served e of my retir from area a vestigation a y, specially /official add elements d hrough the nion strike, must be pe own property ng from it. one shocki owner on 1 ally 70 years was his driv ed and had d was in tur out the philo redefine the ation and ga n rang me a Officer, I wo e me. He sa anised synd s Gaurav Bh wyers regist as 0954026 a never lifte m he was h queries and r Kumar. W white collar / in the Inte red senior c around Gha and to catch the children resses, fam o not misus important a I should sa enalized. W y on fire. F ng incident 14th Feb 13 s old indust ver Mukesh rejoined th rmoil and ha osophy of i e doctrine o ave him Mo and asked m ould contact aid, ‘phir, me icate worki hatia was lis tered in the 63218. Mr. W d the mobil his professi left the pho Whole incide / financial cr lligence Bu colleagues. aziabad. Th h the culprits n on Facebo mily details, se them. Date articles. Abo ay that the c Workers hav Factories are occurred in , and his d trialist Mr. G h, who was e service fe ad called a ndustrial re of socialism, bile numbe me what act t my forme ein apni kaa ng as he g sted for hea e Patiala by Walia also r e, Mr. Narin ional collea one. Therea nt has put u rimes that n reau for ov The analys e case may s. ook do not , bank acco e: 8.06.201 out the incid culprits mus ve not put e the mean n Ranchi. Th dead body Gyanchand once remo ew months a nother bund elations, ow capitalism rs of tions r ‘IB arrya got it aring y the rang nder ague after, us in need ver 8 is of y be give ount 13 dent st be the ns of hree was Jain oved ago. d on wner- and
- 11. C:Users Ira Win issues reliable S ssbtyagiDoc nkler, a to that tech e security m uggestion cumentsICIS p security nology ca measures ns & feedb SSNews Lett y professio an't...you w available." back may b ter July 13.do onal), wrot will find th " (Winkler, be sent to ocx te that "aw hat securit , 2012) us on e-m wareness ty awarene mail: sbtya mitigates ess is one agi1958@g non-techn e of the m gmail.com nical most m
