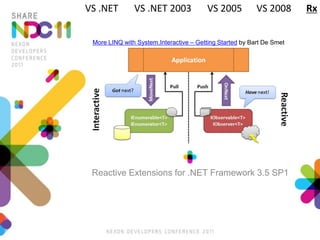
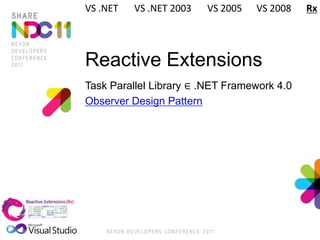
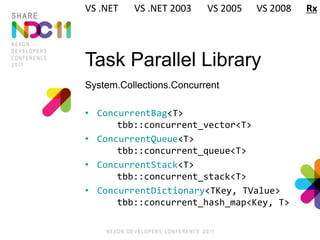
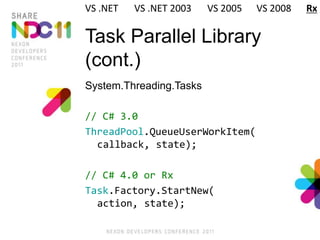
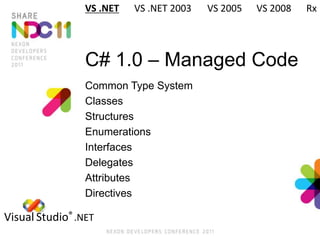
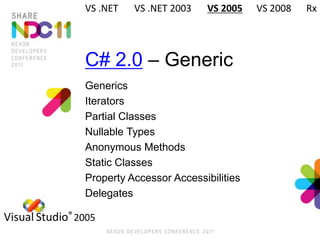
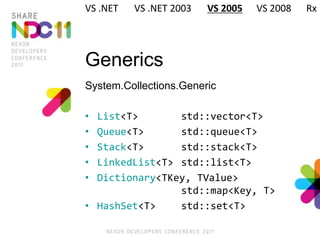
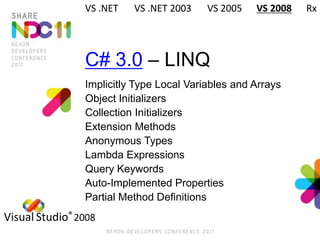
This document summarizes the history of C# and .NET Framework versions from Visual Studio .NET Rainer in 2002 to Visual Studio 2010 Dev10. It covers features introduced in each new version of C# and .NET Framework including generics, LINQ, lambda expressions, extension methods, and more. It also briefly discusses the Reactive Extensions for .NET Framework 3.5 which added asynchronous programming capabilities using an observer pattern.
![책임연구원
2010/2011, 마비노기2
2006/2009, 마비노기 영웅전
테크니컬 디렉터
2004/2005, 마비노기
2003/2004, 프로젝트 T2
2001/2003, Oz World
[ɡ̊ɪm̚ ʨæːsɤk̚]
/ɡim ɟɛːzʌɡ/](https://image.slidesharecdn.com/ndc11cc-130522011025-phpapp01/85/NDC-2011-C-C-4-320.jpg)
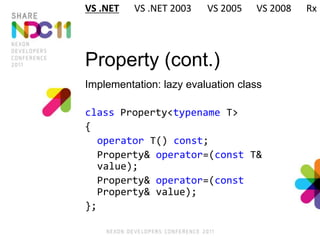
![Property (cont.)
Indexed property ≠ index operator []
int this[int index]
{
get { return array[index]; }
set { array[index] = value; }
}
VS .NET VS .NET 2003 VS 2005 VS 2008 Rx](https://image.slidesharecdn.com/ndc11cc-130522011025-phpapp01/85/NDC-2011-C-C-15-320.jpg)

![Enumerations
Value types
string[] Enum.GetNames()
TEnum[] Enum.GetValues()
TEnum Enum.Parse(string s)
bool Enum.TryParse(
string s, out TEnum @enum)
TEnum TEnum.MaxValue { get; }
TEnum TEnum.MinValue { get; }
VS .NET VS .NET 2003 VS 2005 VS 2008 Rx](https://image.slidesharecdn.com/ndc11cc-130522011025-phpapp01/85/NDC-2011-C-C-24-320.jpg)
![Partial Classes
// Generated.Designer.cs
[CLSCompliant]
partial class Generated : ICloneable
{ … }
// Generated.cs
[Serializable]
partial class Generated : IDisposable
{ … }
VS .NET VS .NET 2003 VS 2005 VS 2008 Rx](https://image.slidesharecdn.com/ndc11cc-130522011025-phpapp01/85/NDC-2011-C-C-36-320.jpg)
![Implicitly Type Local
Variables and Arrays
// C# 2.0
Dictionary<string, object> dict =
new Dictionary<string, object>();
Type[] types = new Type[]
{ typeof(int) };
// C# 3.0
var dict =
new Dictionary<string, object>();
var types = new[] { typeof(int) };
VS .NET VS .NET 2003 VS 2005 VS 2008 Rx](https://image.slidesharecdn.com/ndc11cc-130522011025-phpapp01/85/NDC-2011-C-C-45-320.jpg)