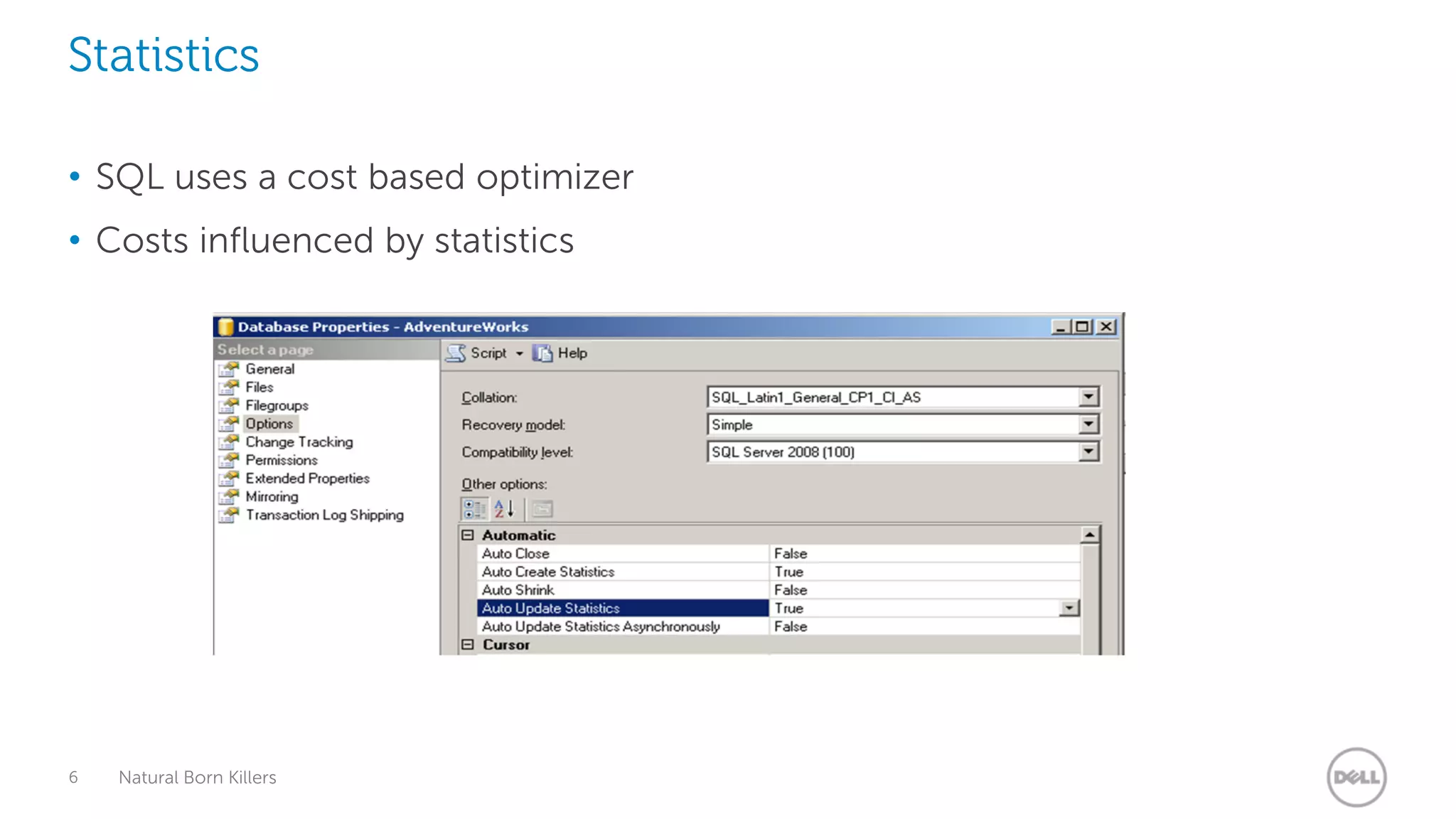
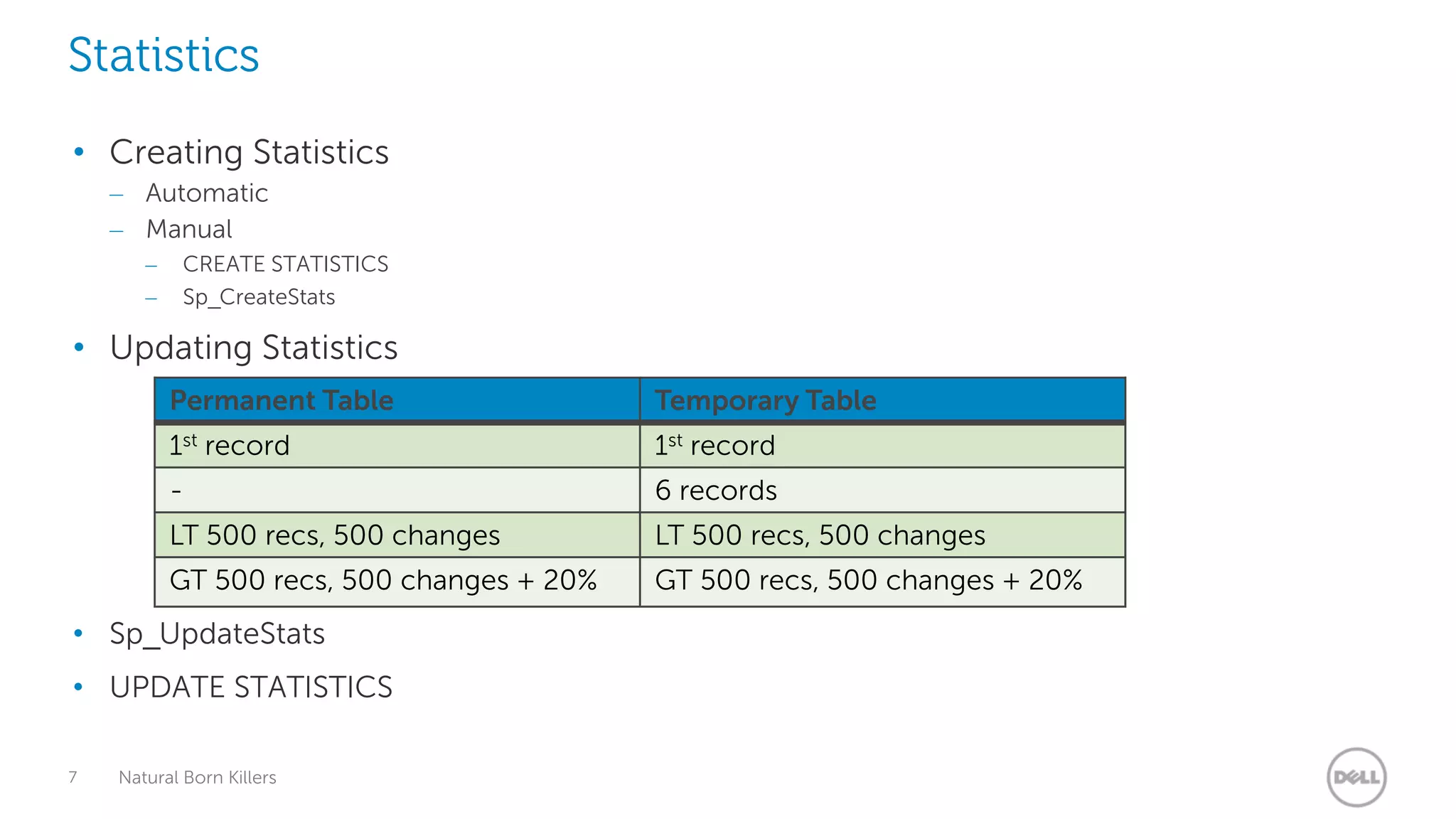
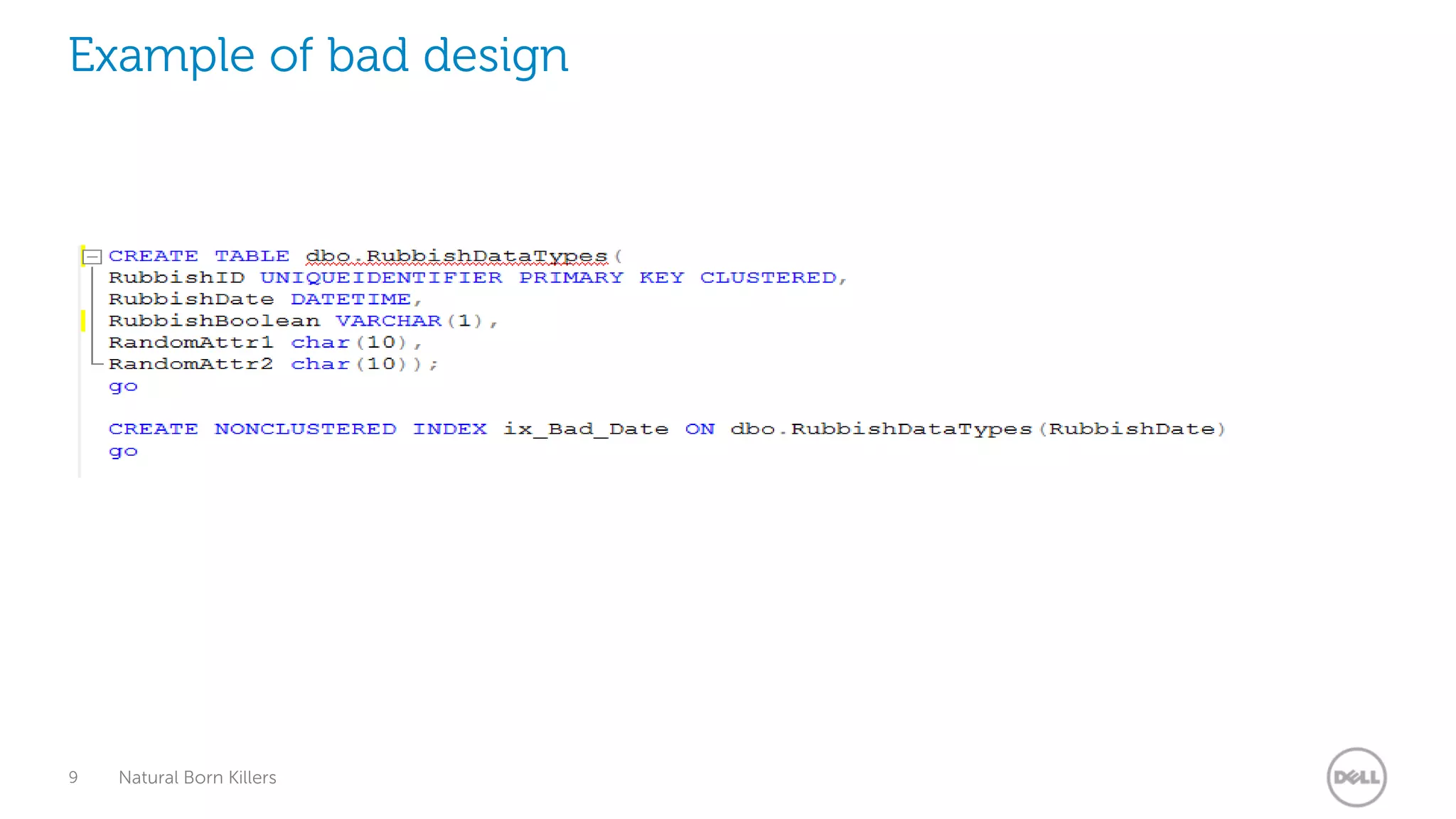
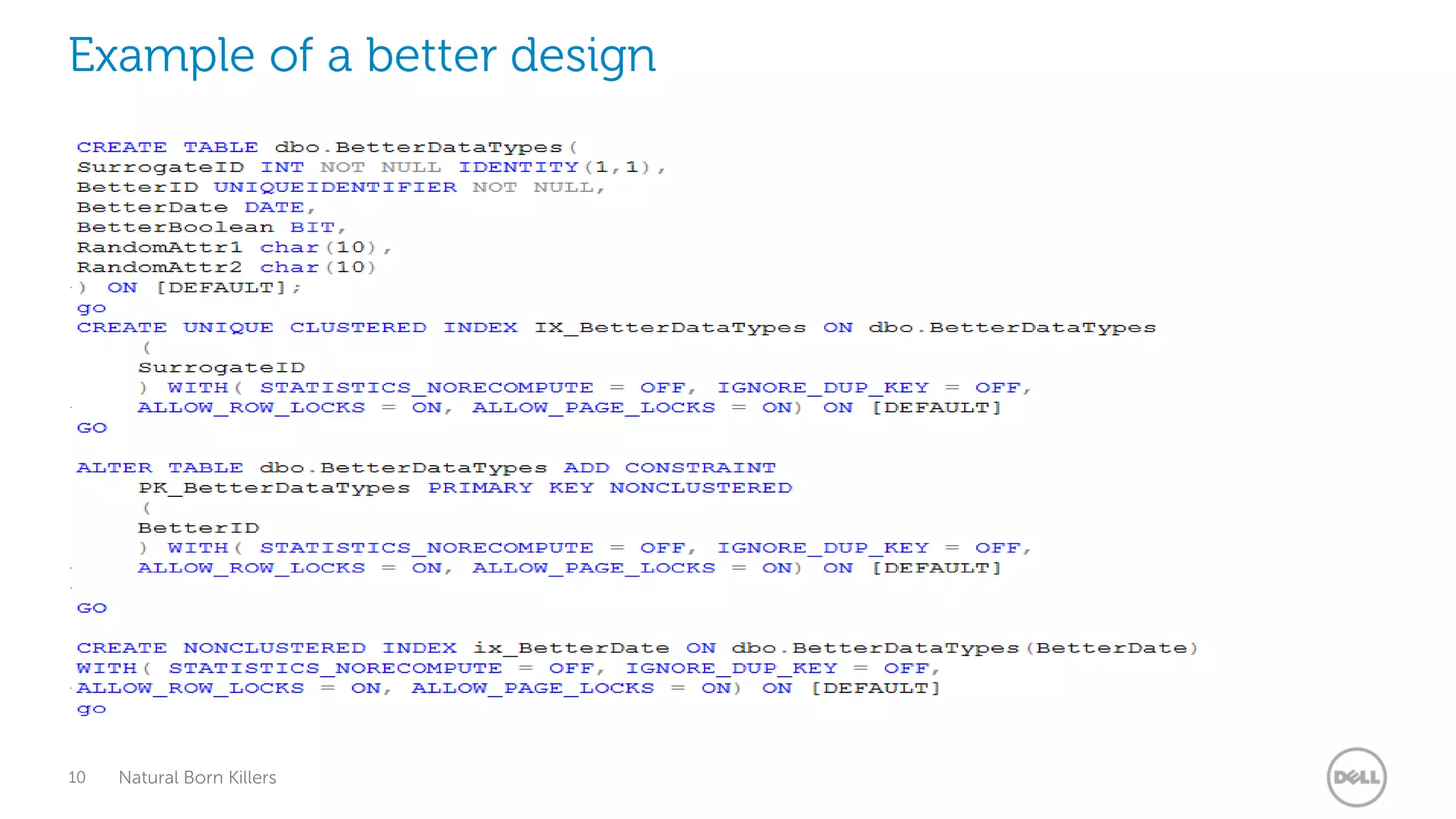
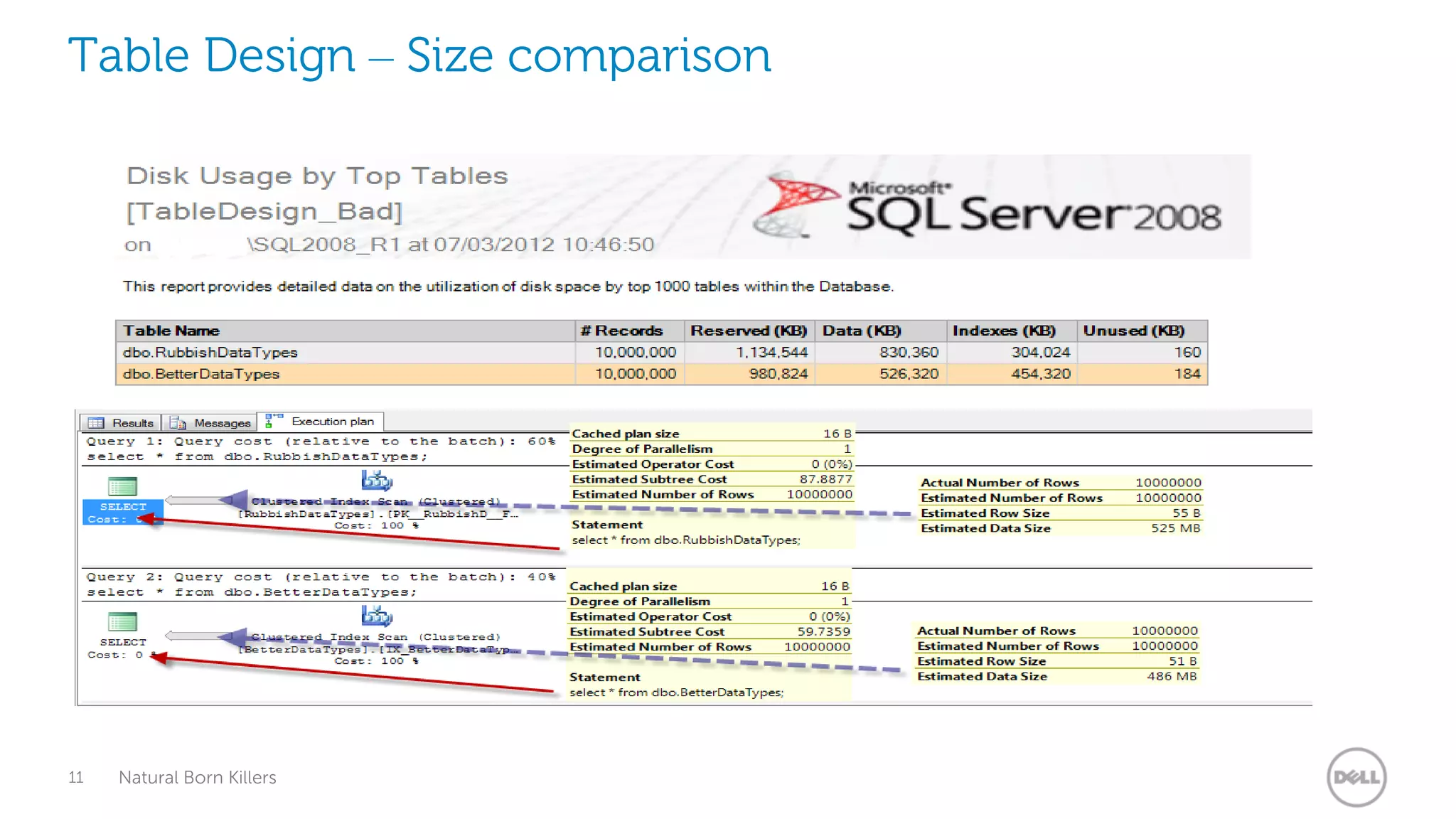
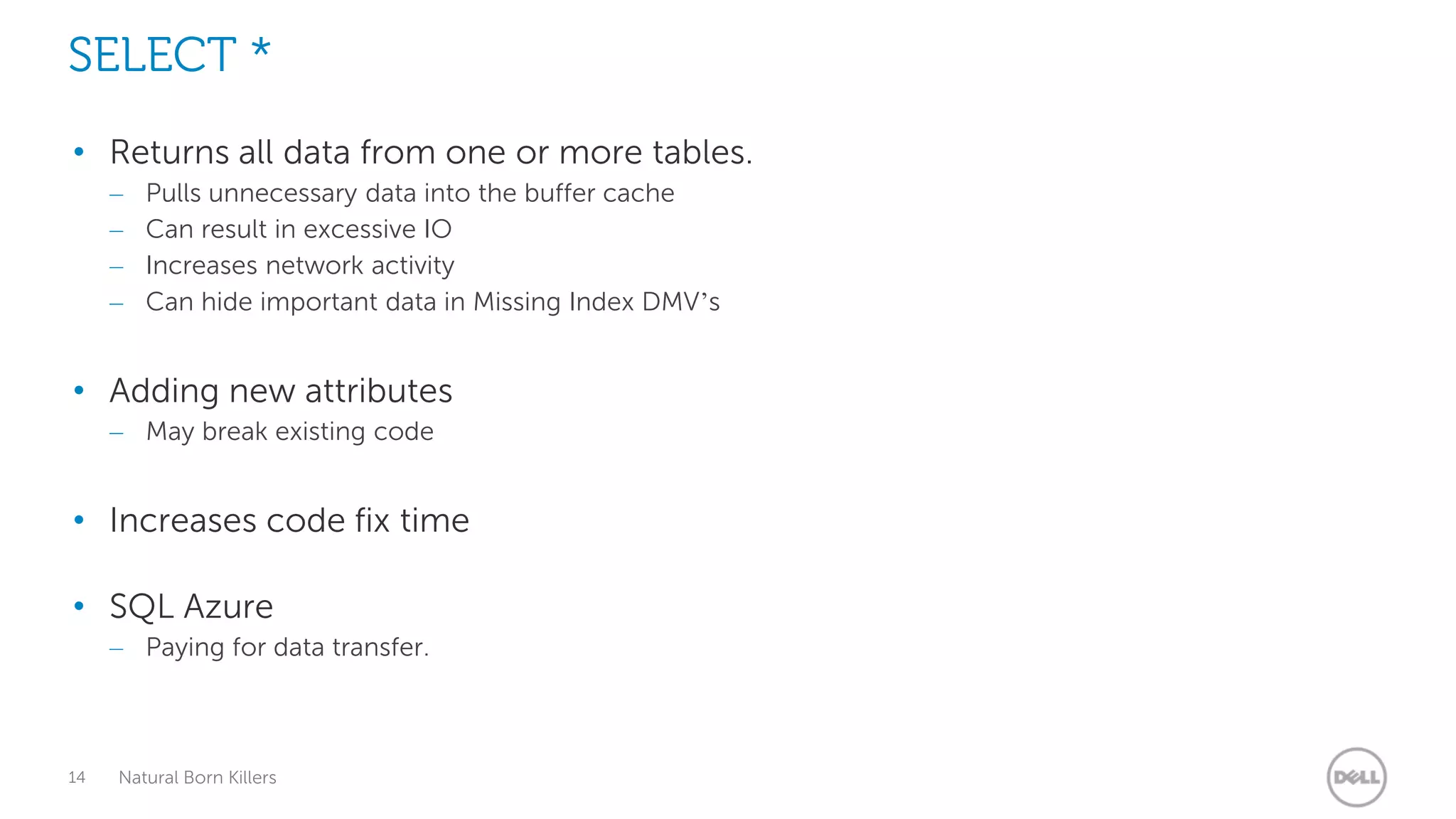
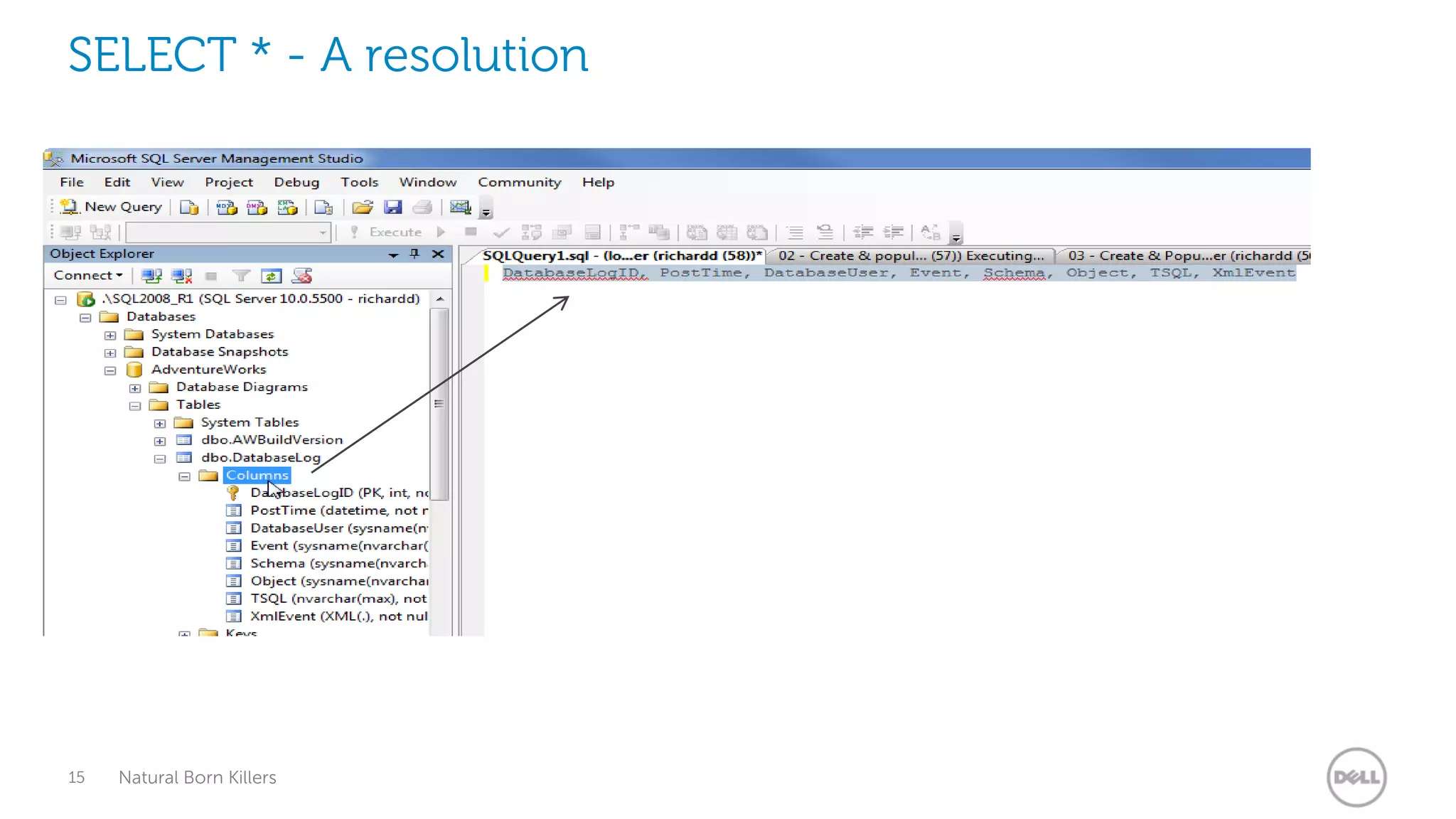
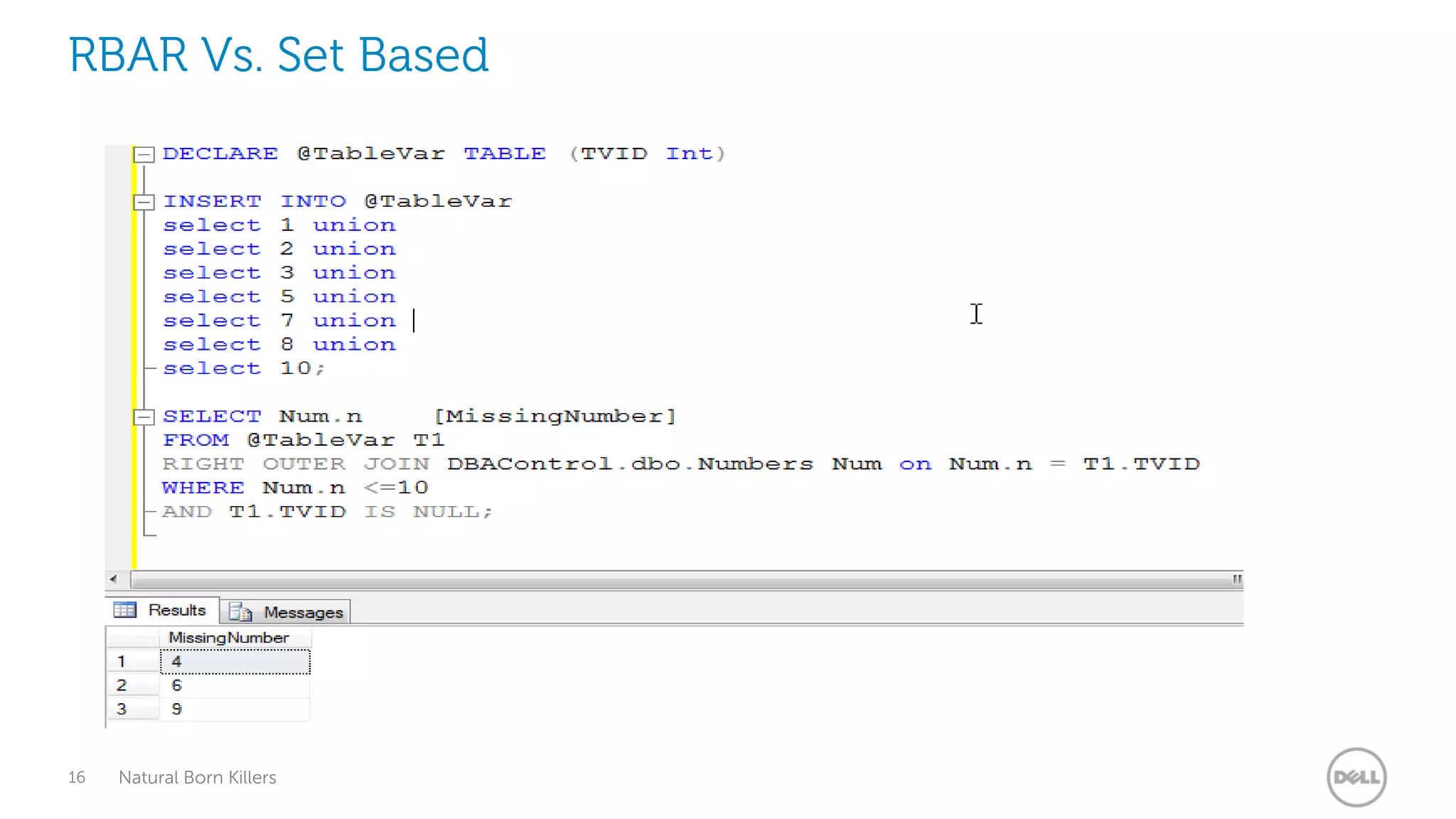
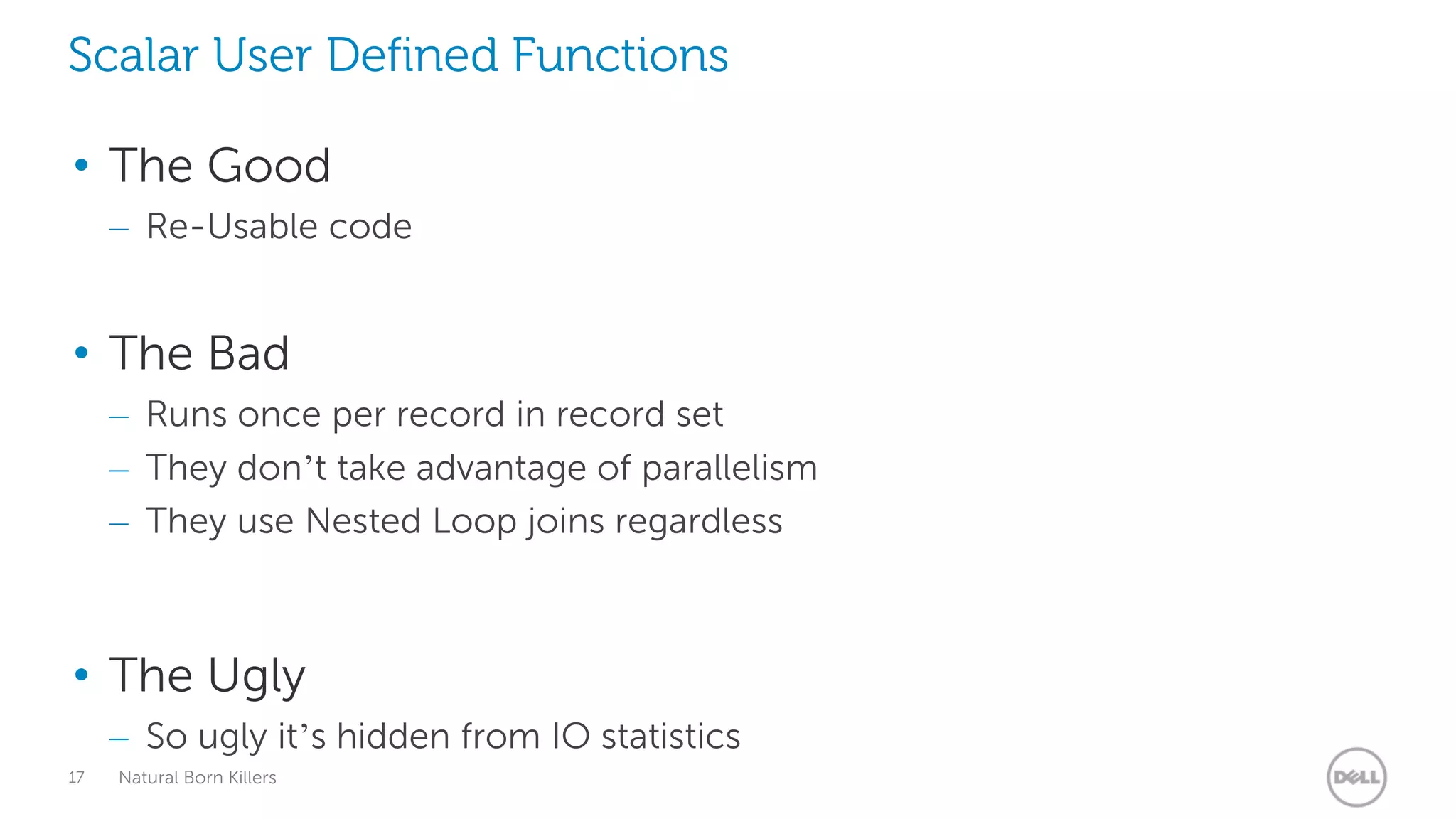
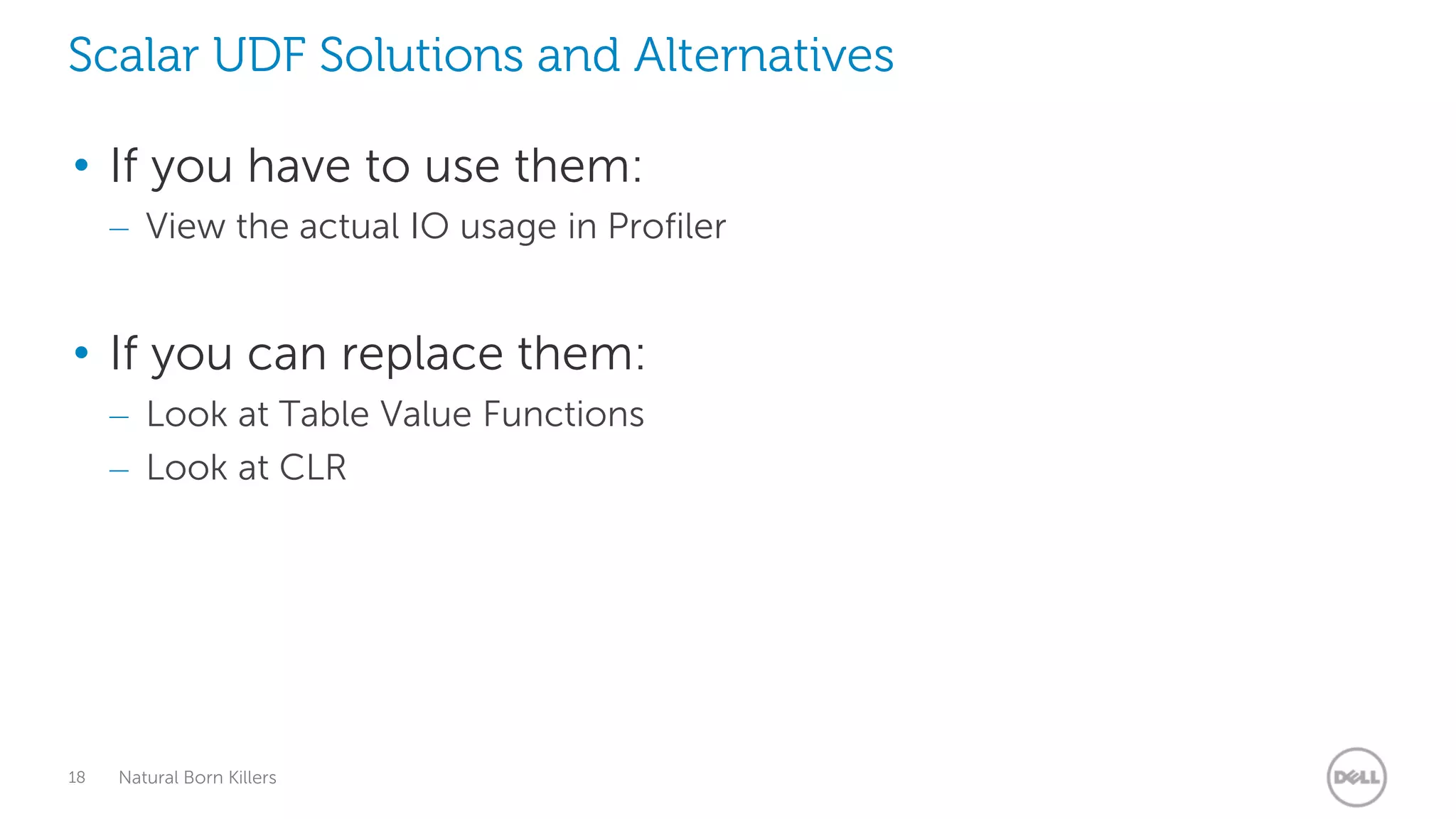
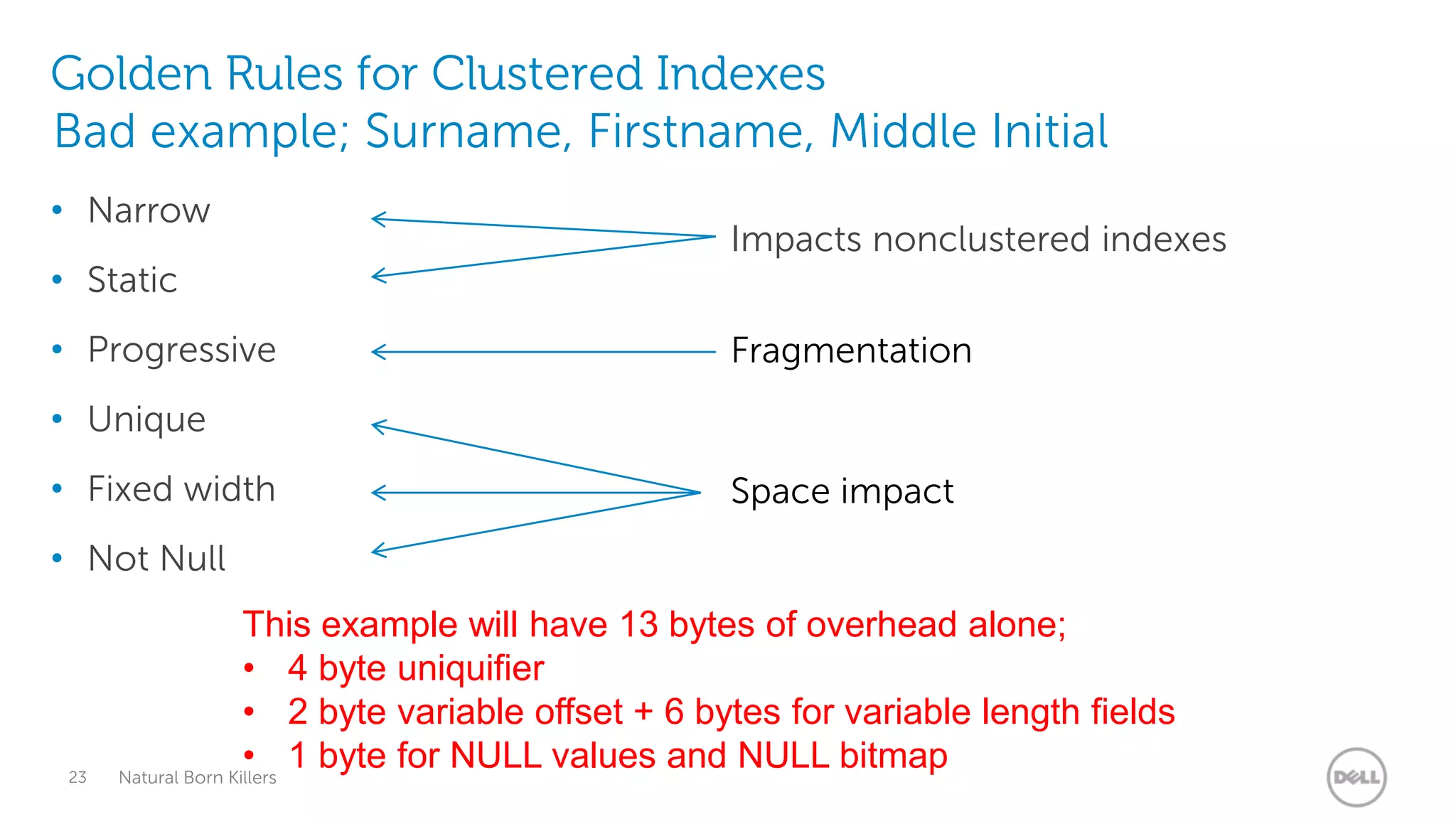
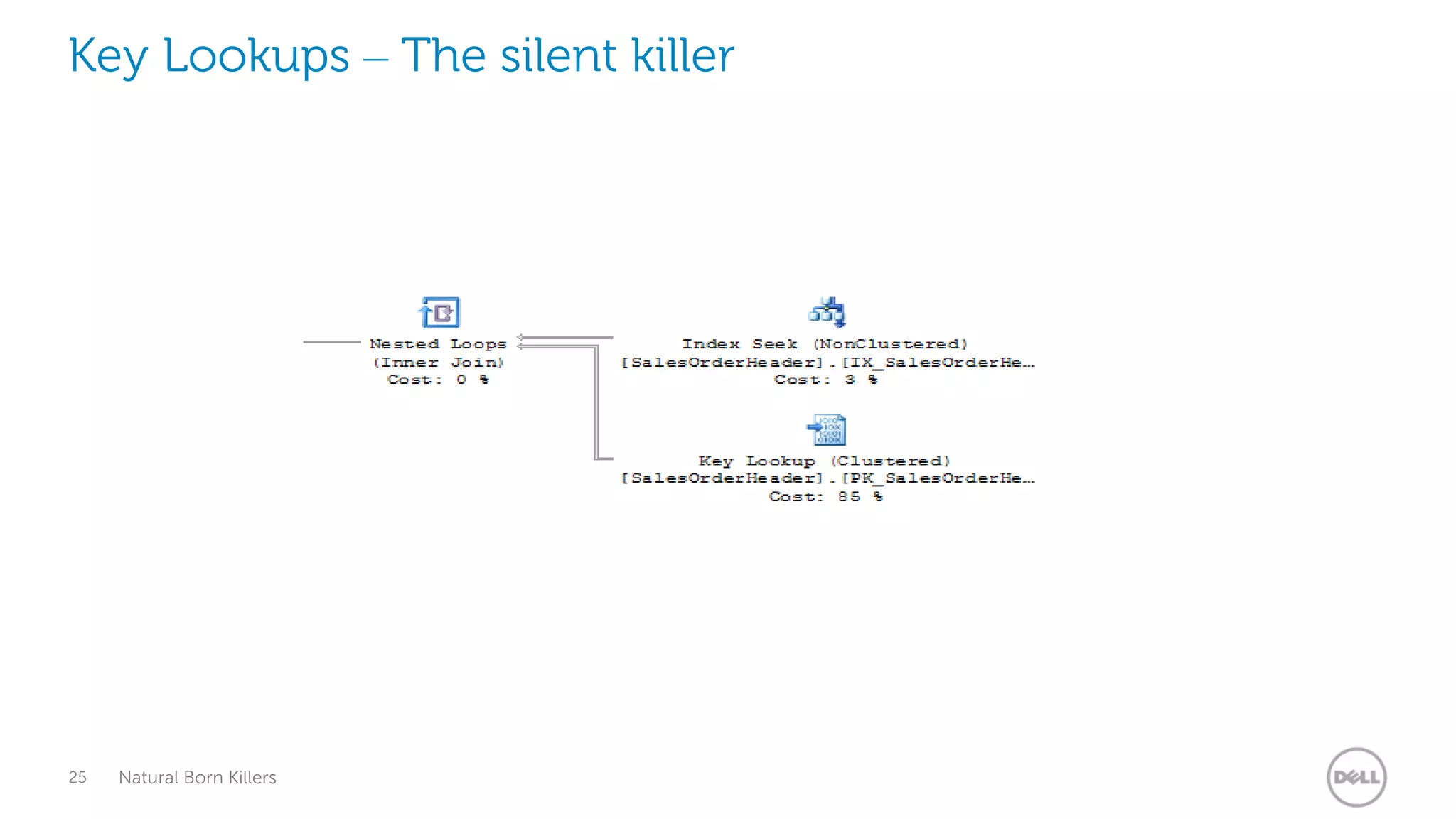
This document provides an overview of performance issues to avoid when working with SQL Server. It discusses topics like statistics and table design, avoiding SELECT *, scalar user defined functions, indexing strategies, key lookups, parameter sniffing and more. The presentation aims to educate attendees on best practices for writing efficient queries and managing database performance.