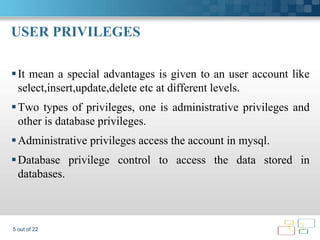
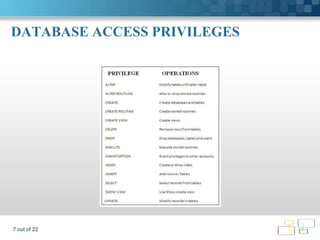
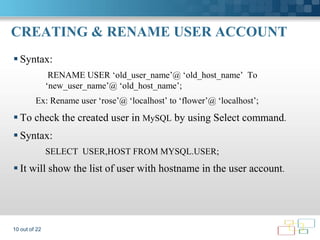
The document provides an overview of MySQL user management, detailing procedures related to user account creation, privilege management, and the use of routines and triggers. It emphasizes the importance of user privileges at various levels, including administrative, database, table, and column levels. Additionally, it describes how stored procedures and triggers automate database operations and respond to table events.

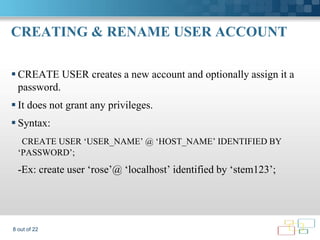

![CREATING & RENAME USER ACCOUNT
How to set password for a user and change the password for a user.
Syntax:
SET PASSWORD for [‘USER_NAME’@ ‘HOST_NAME’]=PASSWORD(‘12345’);
After change the password to get update in that user account we
need to do flush privileges to get update.
Syntax:
FLUSH PRIVILEGES;
11 out of 22](https://image.slidesharecdn.com/mysqlusermanagement1-130126043301-phpapp01/85/MySQL-USER-MANAGEMENT-ROUTINES-TRIGGERS-11-320.jpg)
![REVOKE PRIVILEGES
It enables system administrators to revoke privileges from MySQL
accounts(Break the rules and regulations that given by GRANT to the
user account).
Syntax: REVOKE privilege_type [(column_list)] ,[priv_type
[(column_list)]]...ON [object_type] privilege_level FROM user [‘user’]
Ex: revoke all privileges, grant option from‘rose’@‘localhost’;
18 out of 22](https://image.slidesharecdn.com/mysqlusermanagement1-130126043301-phpapp01/85/MySQL-USER-MANAGEMENT-ROUTINES-TRIGGERS-18-320.jpg)