Most expensive IT Security Incidents
•
0 likes•42 views
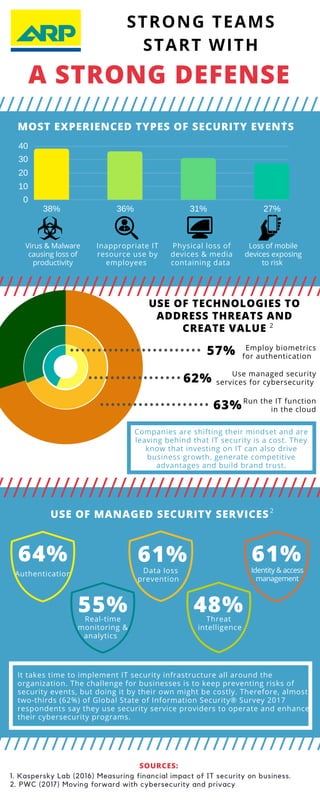
IT Security is an important Topic for businesses, especially in the times of digitalization. Our infographic Shows where businesses should start to invest.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
Solving the Asset Management Challenge for Cybersecurity (It’s About Time)

Solving the Asset Management Challenge for Cybersecurity (It’s About Time)Enterprise Management Associates
More Related Content
What's hot
Solving the Asset Management Challenge for Cybersecurity (It’s About Time)

Solving the Asset Management Challenge for Cybersecurity (It’s About Time)Enterprise Management Associates
What's hot (20)
Rethinking the Enterprise Perimeter | SnowFROC Presentation

Rethinking the Enterprise Perimeter | SnowFROC Presentation
Infographic: Bringing Your Cloud Visibility Back Into Focus

Infographic: Bringing Your Cloud Visibility Back Into Focus
Adapted from an ESG report - Outnumbered, Outgunned. 

Adapted from an ESG report - Outnumbered, Outgunned.
Reinforcing the Revolution: The Promise and Perils of Digital Transformation

Reinforcing the Revolution: The Promise and Perils of Digital Transformation
Solving the Asset Management Challenge for Cybersecurity (It’s About Time)

Solving the Asset Management Challenge for Cybersecurity (It’s About Time)
Security Software Supply Chains - Sonatype - DevSecCon Singapore March 2019

Security Software Supply Chains - Sonatype - DevSecCon Singapore March 2019
Similar to Most expensive IT Security Incidents
Responding to Cybersecurity Threats: What SMEs and Professional Accountants N...

Responding to Cybersecurity Threats: What SMEs and Professional Accountants N...International Federation of Accountants
Similar to Most expensive IT Security Incidents (20)
kaspersky presentation for palette business solution June 2016 v1.0.

kaspersky presentation for palette business solution June 2016 v1.0.
“The Impact of Mobile Devices on Information Security: A Survey of IT and Sec...

“The Impact of Mobile Devices on Information Security: A Survey of IT and Sec...
Digital Technology in Mining: Progress and Opportunity

Digital Technology in Mining: Progress and Opportunity
The impact of mobile devices on information security

The impact of mobile devices on information security
Scale vp wisegate-investing-in_security_innovation_aug2014-gartner_catalyst

Scale vp wisegate-investing-in_security_innovation_aug2014-gartner_catalyst
trellix-mind-of-the-ciso-report-ebook-behind-the-breach.pdf

trellix-mind-of-the-ciso-report-ebook-behind-the-breach.pdf
Protect your hybrid workforce across the attack chain

Protect your hybrid workforce across the attack chain
Global Megatrends in Cybersecurity – A Survey of 1,000 CxOs

Global Megatrends in Cybersecurity – A Survey of 1,000 CxOs
Responding to Cybersecurity Threats: What SMEs and Professional Accountants N...

Responding to Cybersecurity Threats: What SMEs and Professional Accountants N...
CSE 2016 Future of Cyber Security by Matthew Rosenquist

CSE 2016 Future of Cyber Security by Matthew Rosenquist
Cyber Security Trends - Where the Industry Is Heading in an Uncertainty

Cyber Security Trends - Where the Industry Is Heading in an Uncertainty
Top 10 cybersecurity predictions for 2016 by Matthew Rosenquist

Top 10 cybersecurity predictions for 2016 by Matthew Rosenquist
Recently uploaded
Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx

Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptxnull - The Open Security Community
Recently uploaded (20)
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
SQL Database Design For Developers at php[tek] 2024![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![SQL Database Design For Developers at php[tek] 2024](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
SQL Database Design For Developers at php[tek] 2024
Next-generation AAM aircraft unveiled by Supernal, S-A2

Next-generation AAM aircraft unveiled by Supernal, S-A2
Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

Transcript: #StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service

WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx

Making_way_through_DLL_hollowing_inspite_of_CFG_by_Debjeet Banerjee.pptx
Breaking the Kubernetes Kill Chain: Host Path Mount

Breaking the Kubernetes Kill Chain: Host Path Mount
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Enhancing Worker Digital Experience: A Hands-on Workshop for Partners

Enhancing Worker Digital Experience: A Hands-on Workshop for Partners
Artificial intelligence in the post-deep learning era

Artificial intelligence in the post-deep learning era
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Kotlin Multiplatform & Compose Multiplatform - Starter kit for pragmatics

Kotlin Multiplatform & Compose Multiplatform - Starter kit for pragmatics
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Azure Monitor & Application Insight to monitor Infrastructure & Application

Azure Monitor & Application Insight to monitor Infrastructure & Application
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Most expensive IT Security Incidents
- 1. A STRONG DEFENSE MOST EXPERIENCED TYPES OF SECURITY EVENTS Virus & Malware causing loss of productivity Inappropriate IT resource use by employees Physical loss of devices & media containing data Loss of mobile devices exposing to risk STRONG TEAMS START WITH 43% 57% SOURCES: 1. Kaspersky Lab (2016) Measuring financial impact of IT security on business. 2. PWC (2017) Moving forward with cybersecurity and privacy 1 10 20 30 40 38% 36% 31% 27% 0 USE OF TECHNOLOGIES TO ADDRESS THREATS AND CREATE VALUE 2 31% 69% 70%Companies are shifting their mindset and are leaving behind that IT security is a cost. They know that investing on IT can also drive business growth, generate competitive advantages and build brand trust. 62% Run the IT function in the cloud Use managed security services for cybersecurity Employ biometrics for authentication 57% 63% It takes time to implement IT security infrastructure all around the organization. The challenge for businesses is to keep preventing risks of security events, but doing it by their own might be costly. Therefore, almost two-thirds (62%) of Global State of Information Security® Survey 2017 respondents say they use security service providers to operate and enhance their cybersecurity programs. USE OF MANAGED SECURITY SERVICES Authentication Data loss prevention Identity & access management Real-time monitoring & analytics Threat intelligence 64% 61% 61% 55% 48% 2
