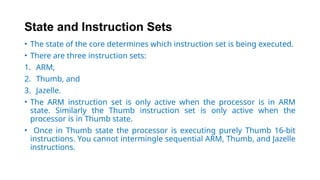
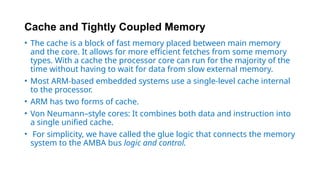
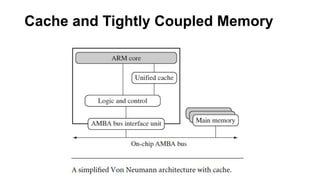
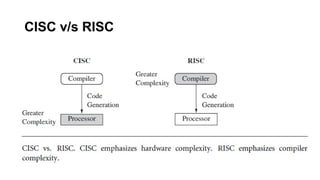
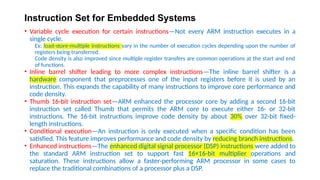
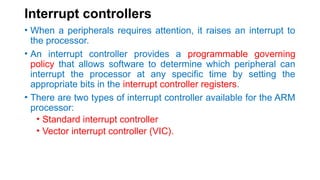
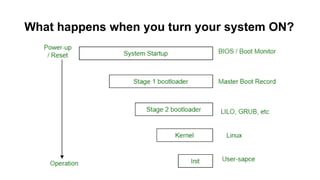
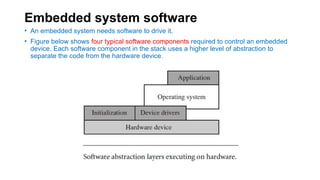
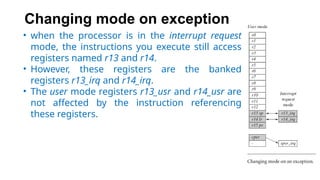
The document serves as a comprehensive guide on ARM embedded systems, detailing the architecture, instruction sets, and programming techniques used in ARM processors. It covers key topics such as firmware, operating systems, memory hierarchies, and peripheral interfacing, aimed at engineers familiar with embedded development but new to ARM architecture. Additionally, it explains the RISC design philosophy in relation to ARM, highlighting the chip's features that cater to efficient embedded system design.
![ARM bus technology
• PCI in X86 PCs [Peripheral Component Interface]
• Connects video cards and hard disk controllers to the x86 processor bus.
• PCI is external/ off-chip technology
• Embedded devices use an on-chip bus that is internal to the chip and that allows
different peripheral devices to be interconnected with an ARM core.
• Two different classes of devices attached to the bus -
1. The ARM processor core is a bus master—a logical device capable of initiating a data transfer with
another device across the same bus.
2. Peripherals tend to be bus slaves—logical devices capable only of responding to a transfer
request from a bus master device.
• A bus has two architecture levels -
1. The first is a physical level that covers the electrical characteristics and bus width (16, 32, or 64
bits).
2. The second level deals with protocol—the logical rules that govern the communication between
the processor and a peripheral.](https://image.slidesharecdn.com/mod1armembeddedsystemsppt202122oddoe-250130022725-7b1fb4eb/85/mod1_arm_embedded_systems_ppt_2021_22_odd_oe-pptx-14-320.jpg)
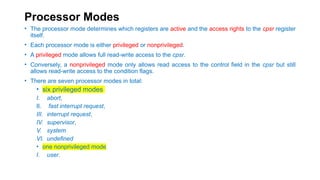

![Modes and mode bit fields in CPSR [0:4]](https://image.slidesharecdn.com/mod1armembeddedsystemsppt202122oddoe-250130022725-7b1fb4eb/85/mod1_arm_embedded_systems_ppt_2021_22_odd_oe-pptx-51-320.jpg)