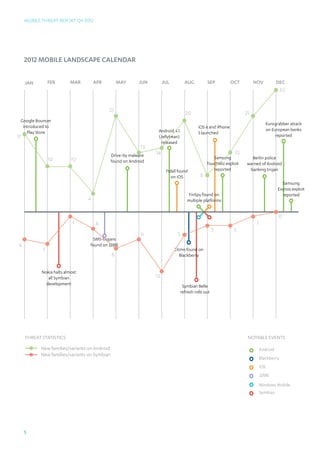
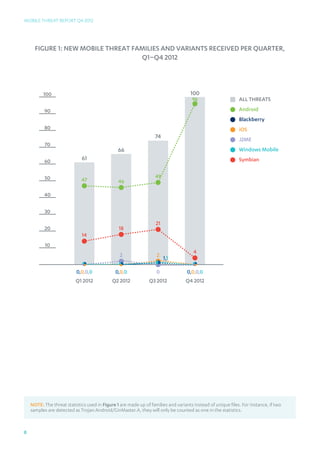
The Q4 2012 Mobile Threat Report from F-Secure Labs provides an overview of the mobile threat landscape, highlighting an increase in Android malware with 96 new families and variants identified in the quarter alone. It discusses various types of threats, including banking trojans like citmo.a that steal transaction authentication numbers, and shows Android's growing market share while Symbian continues to decline. The report emphasizes the need for continuous vigilance against evolving mobile threats as criminals exploit vulnerabilities for profit.






















![Mobile Threat Report Q4 2012
Different icons used by Temai.A
In addition to collecting and forwarding device information, the malware also
downloads and installs potentially malicious APKs and script files onto the infected
device. Users may also be exposed to other risk resulting from the various
permissions granted to the malware during the installation process.
Permissions requested by Temai.A during installation
Trojan:Android/Tesbo.A
Tesbo.A establishes connection to a couple of remote servers, to which it forwards
details such as the device’s International Mobile Subscriber Identity (IMSI) number
and application package name.
Furthermore, the malware will also send out SMS messages with the content
“[IMSI]@[random from 1-10]” to the number 10658422.
26](https://image.slidesharecdn.com/mobilethreatreportq42012-130307070659-phpapp02/85/F-Secure-Labs-Mobile-Threat-Report-Q4-2012-26-320.jpg)