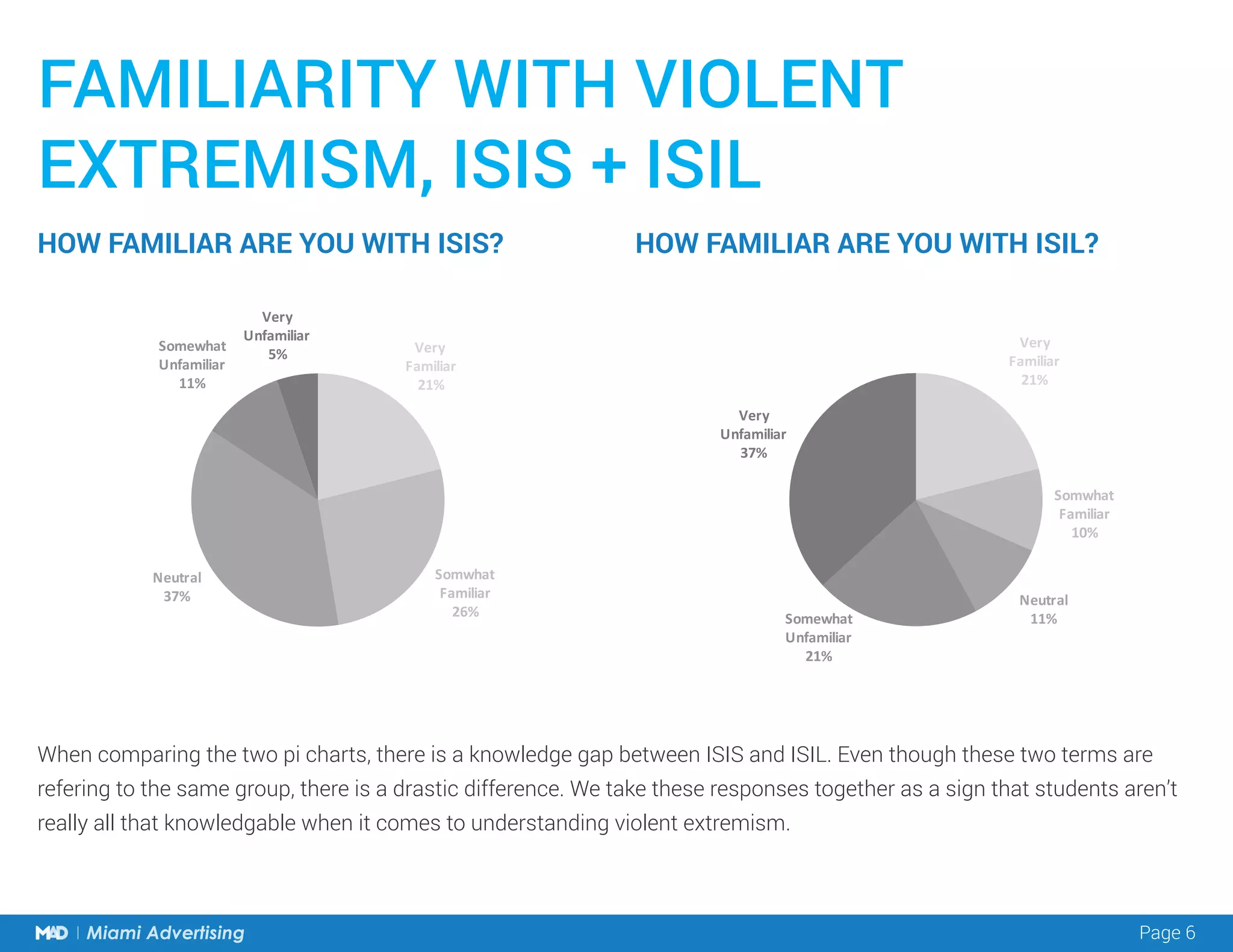
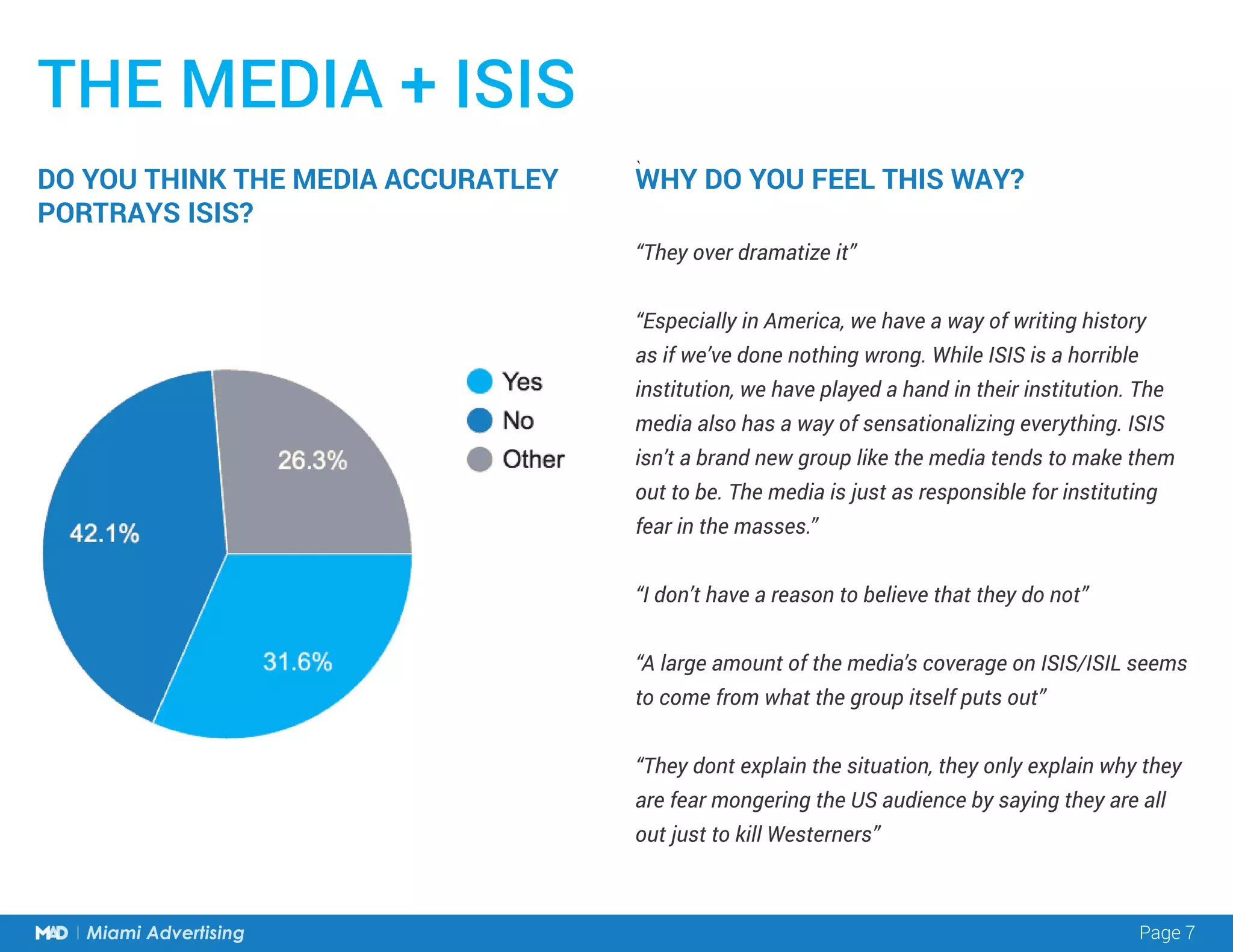
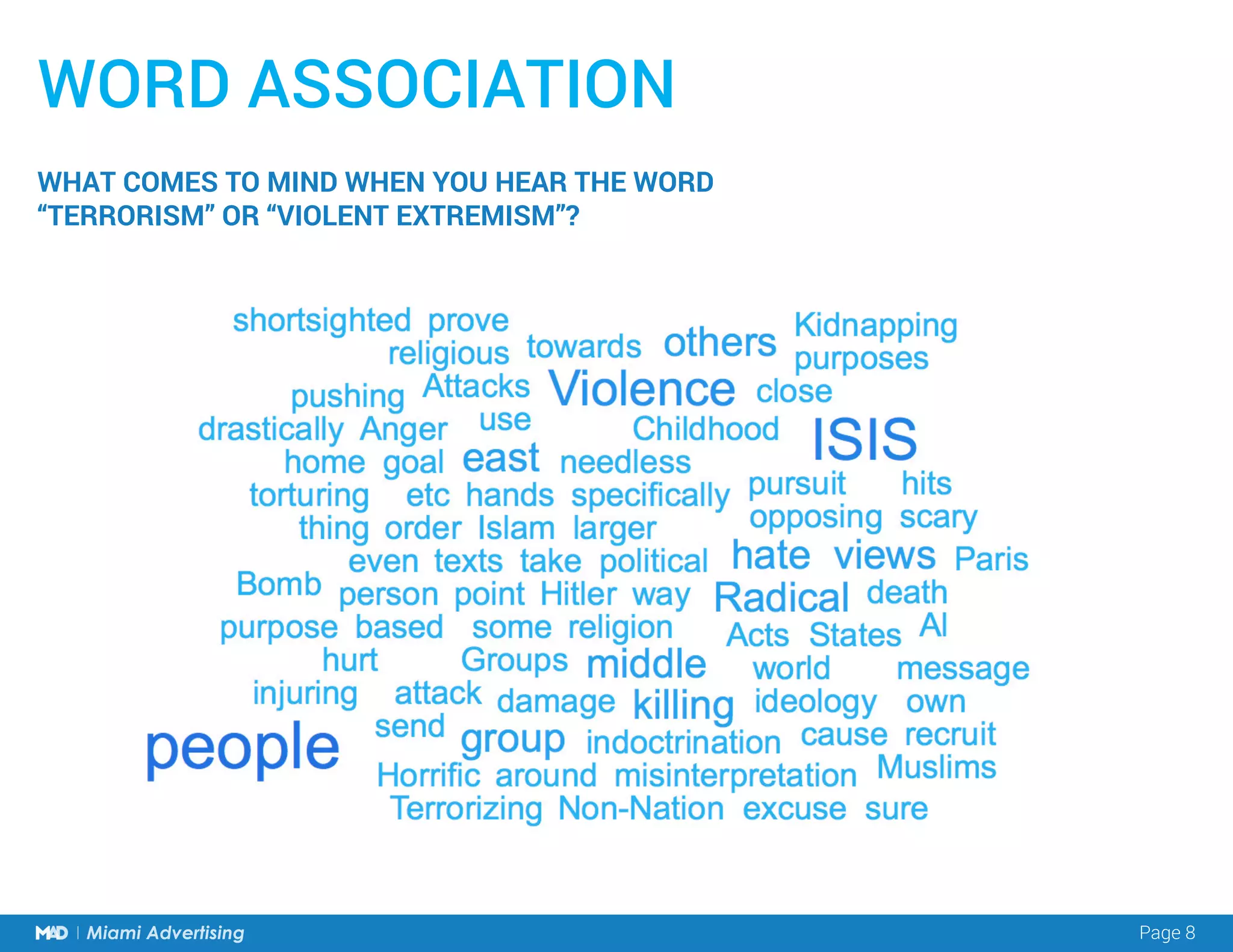
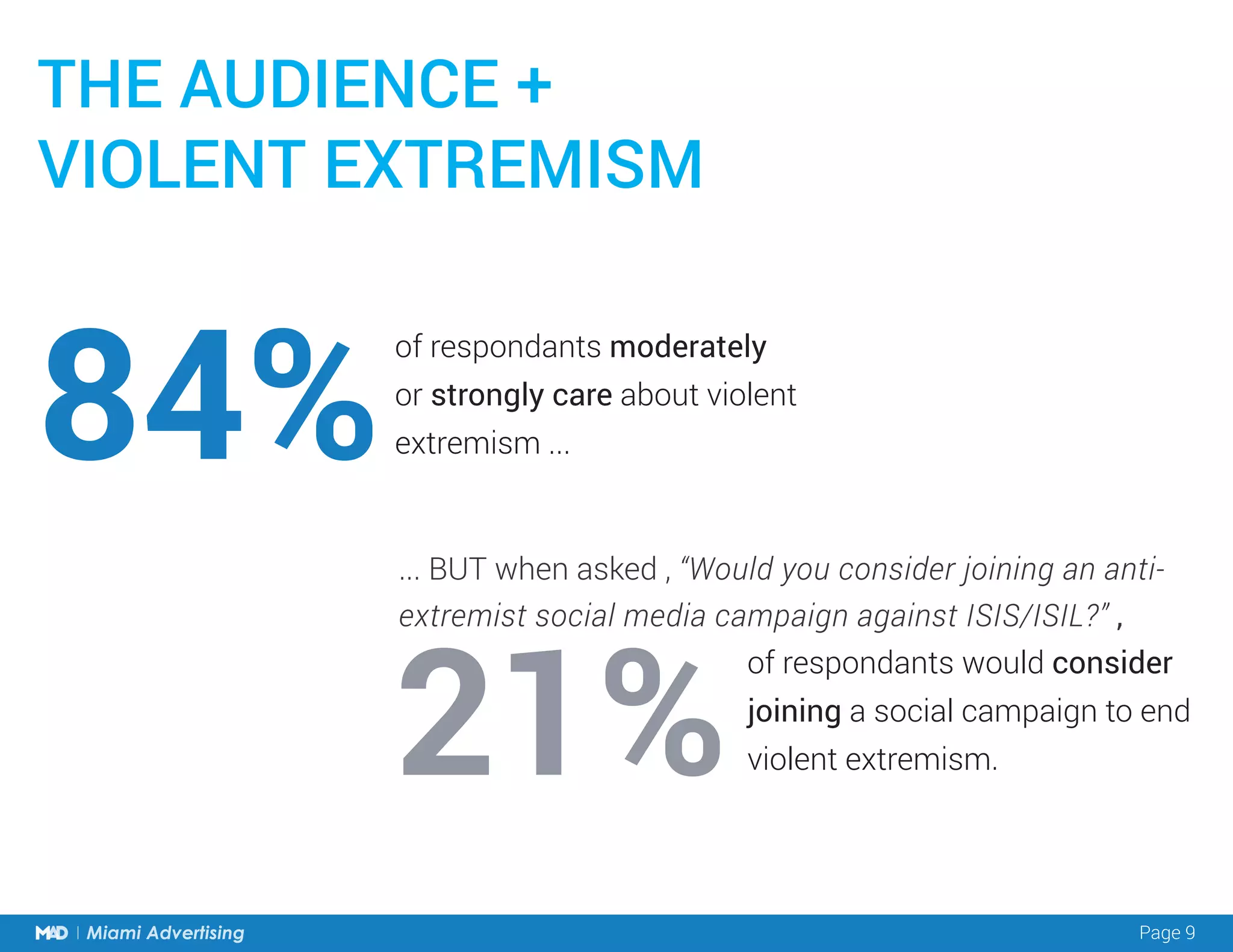
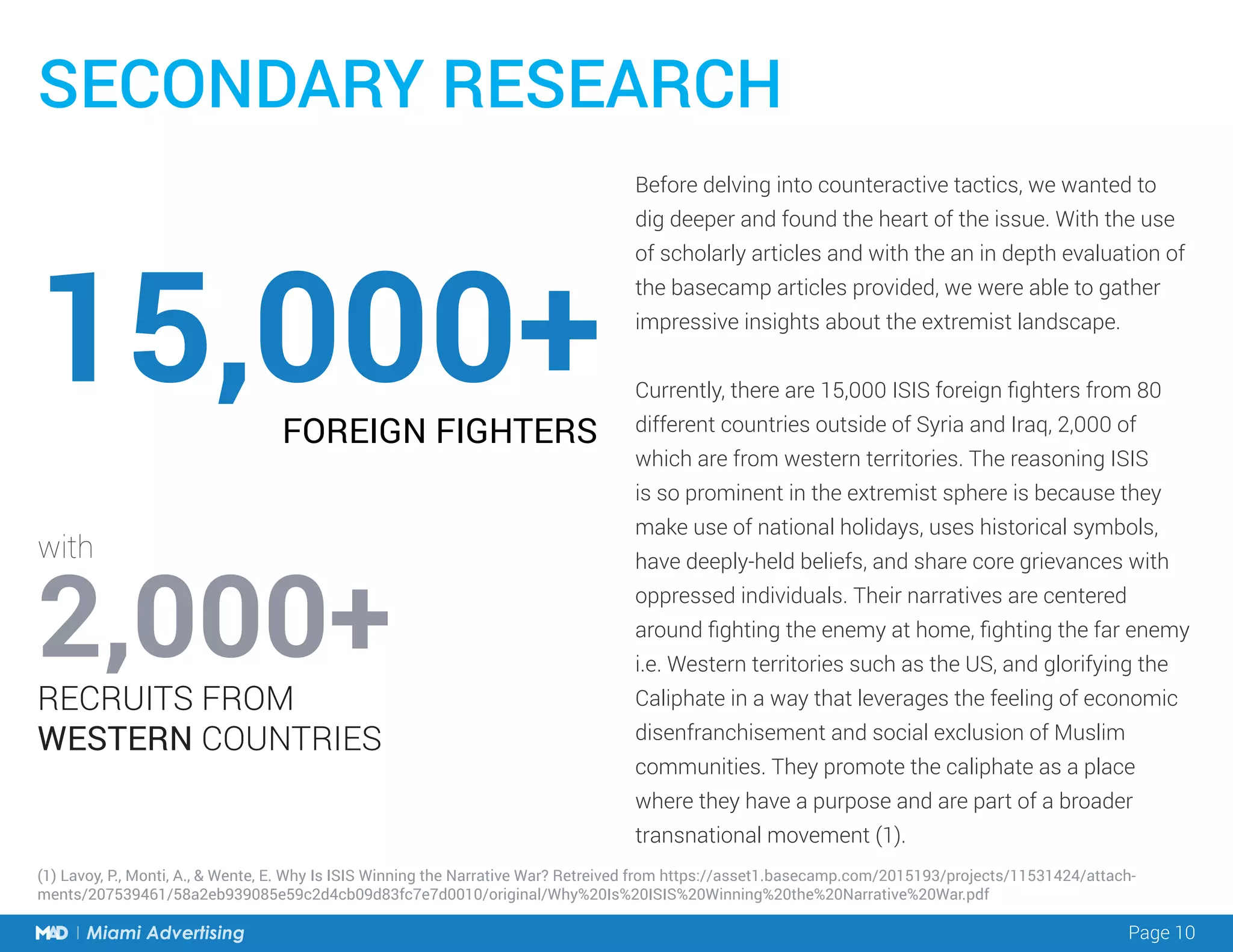
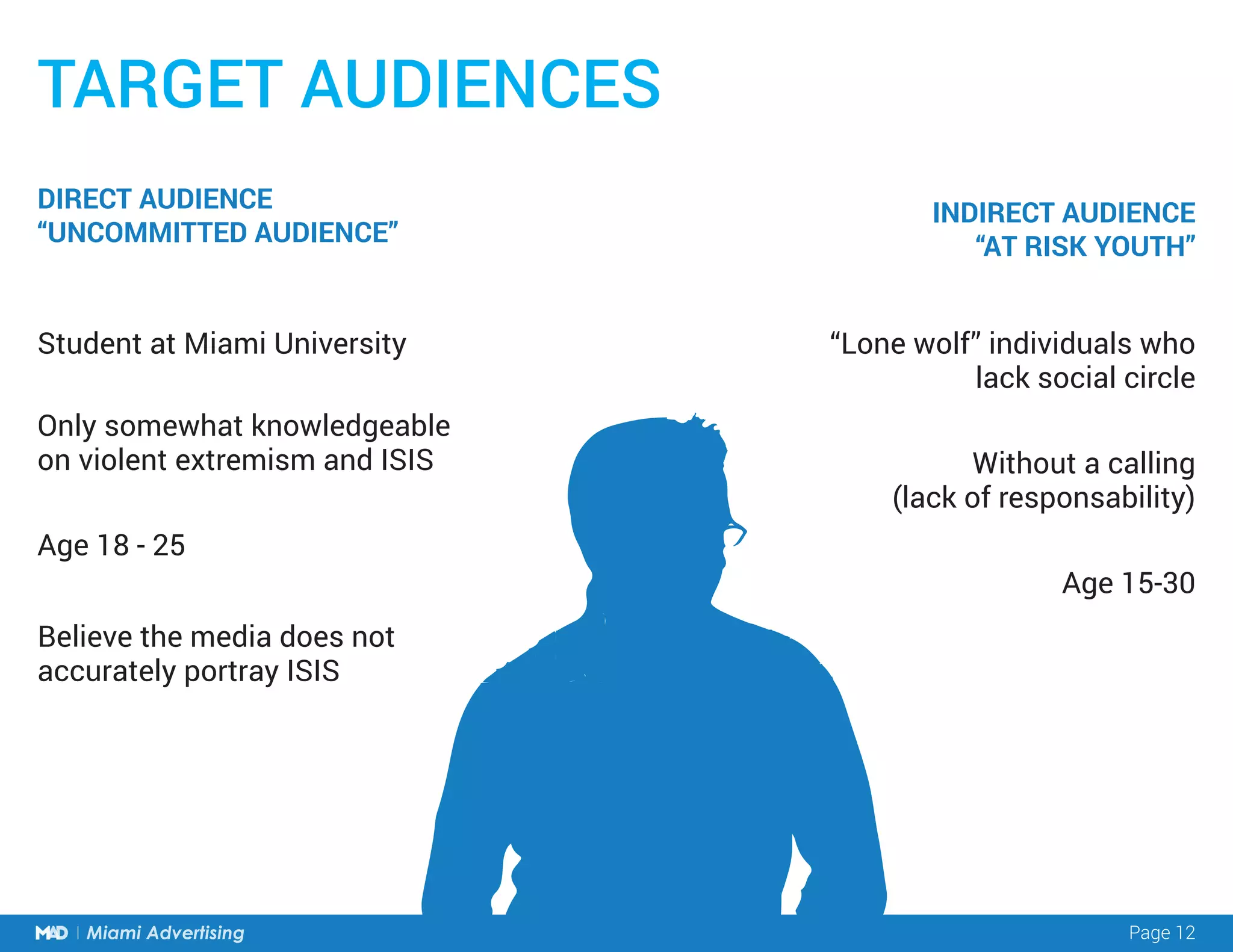
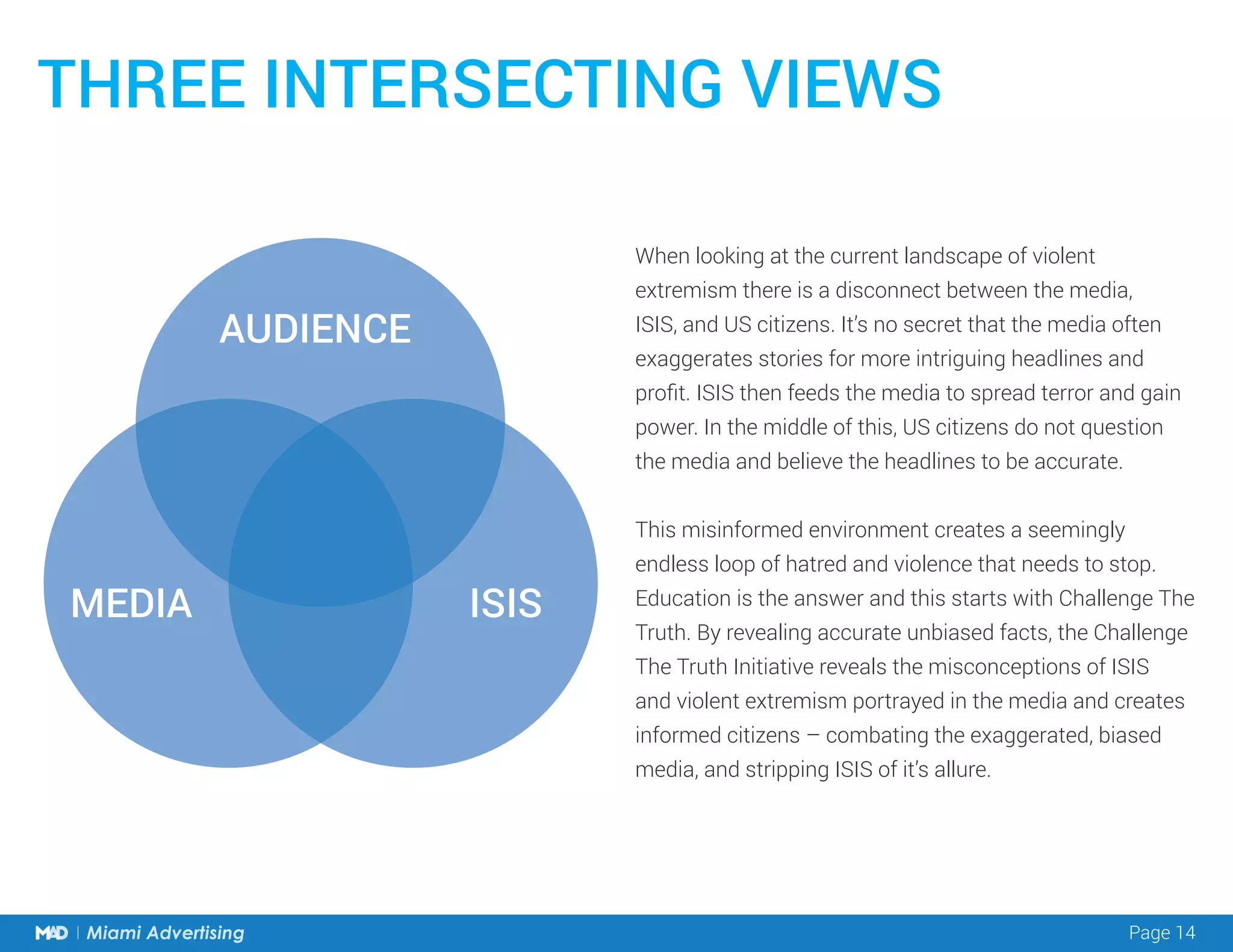
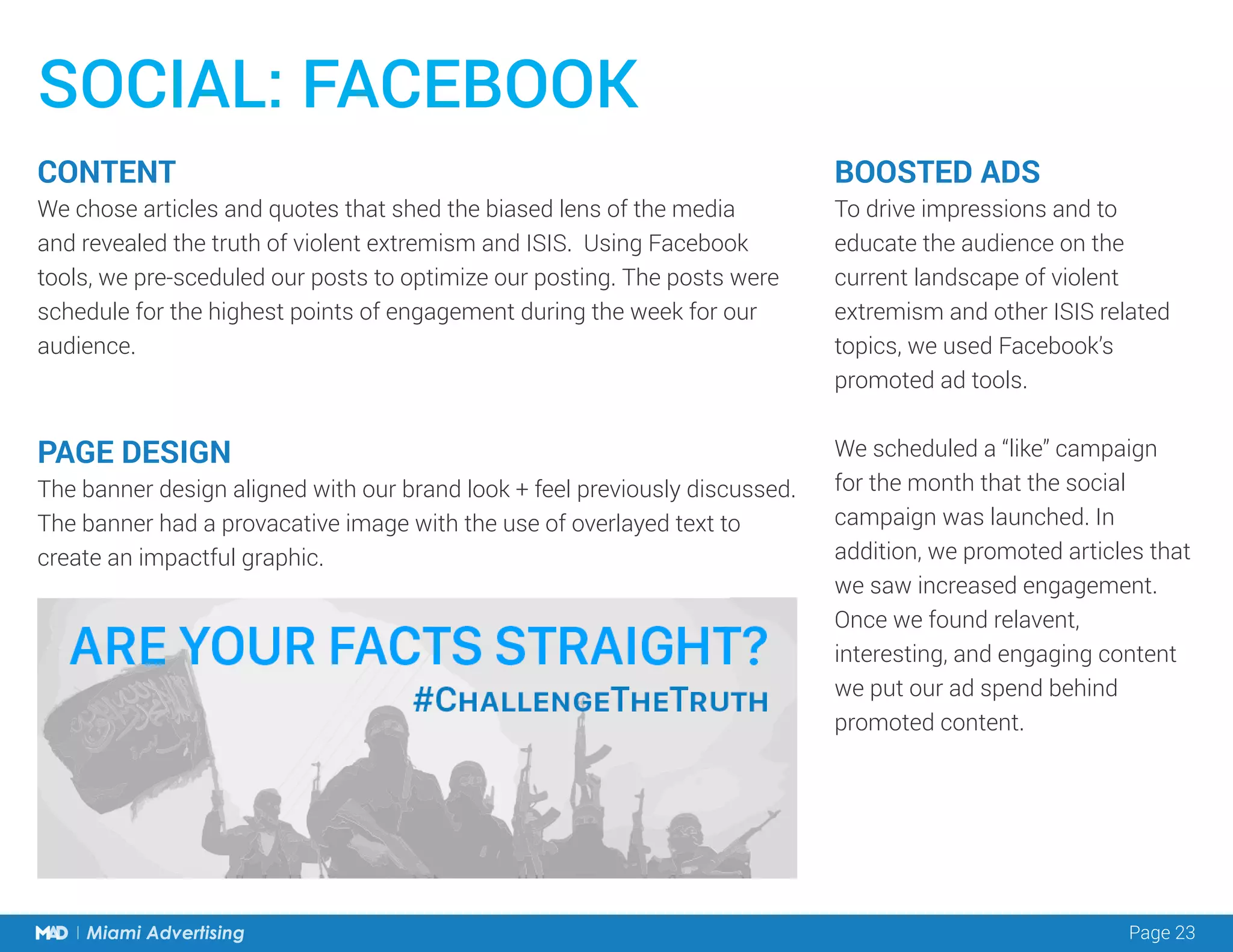
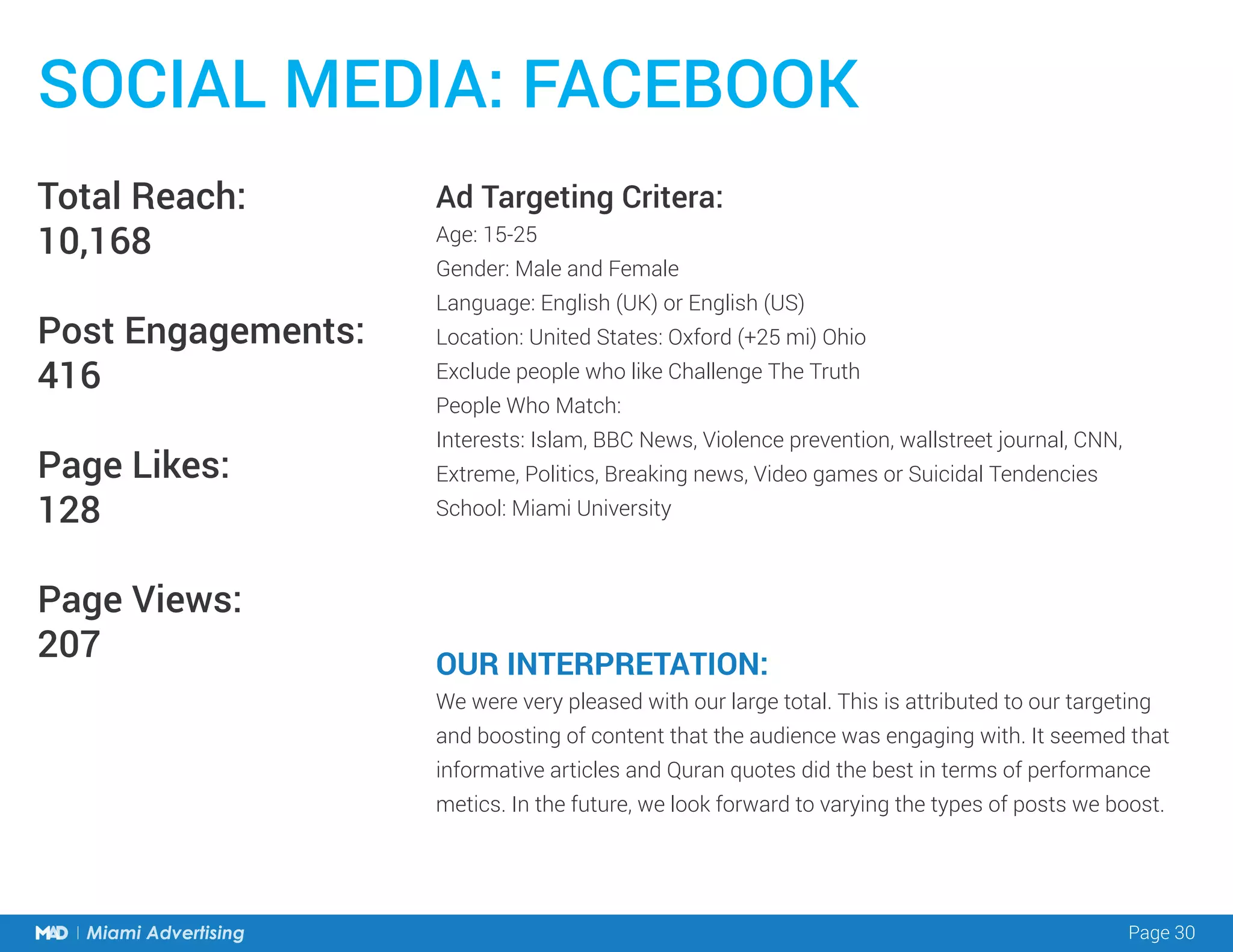
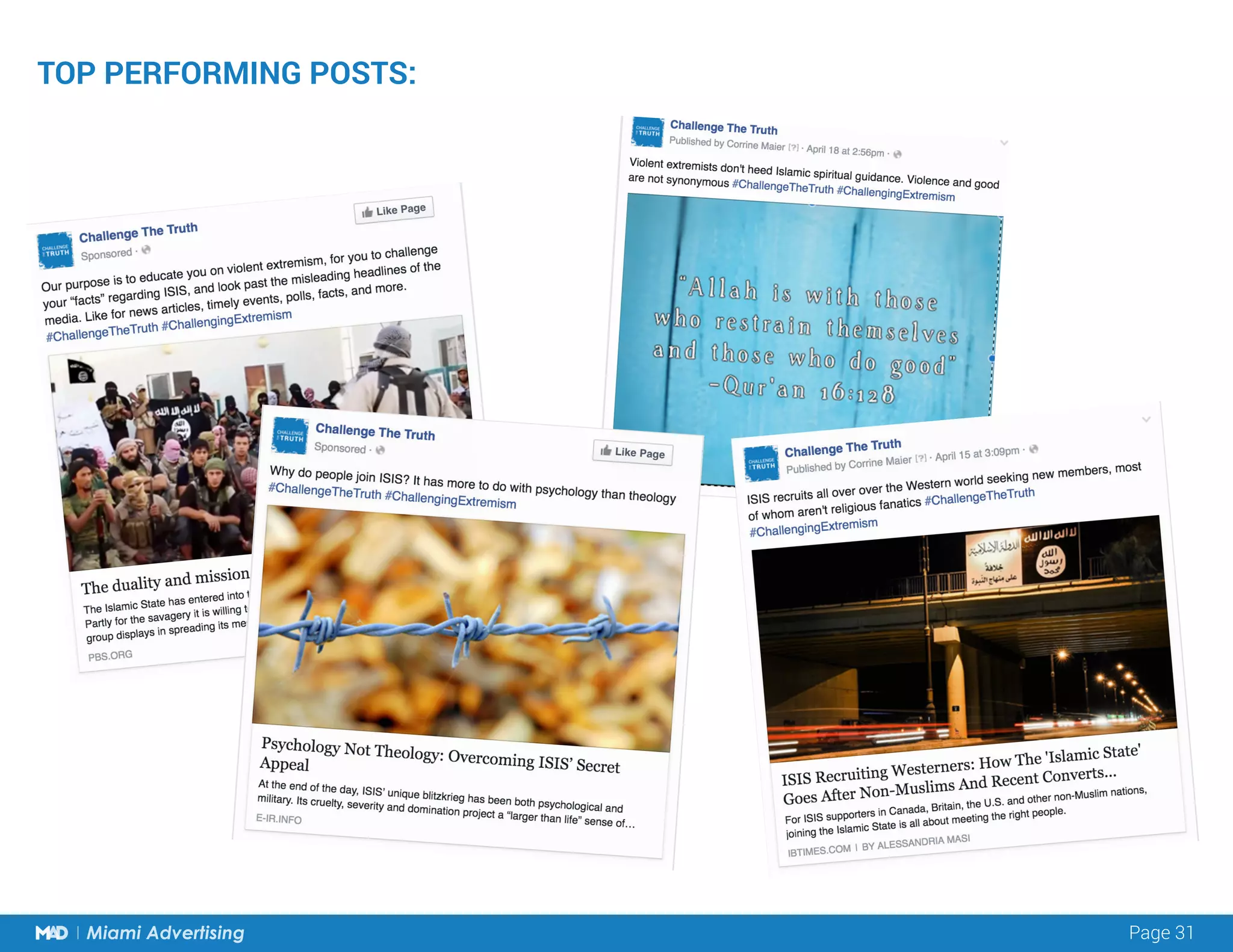
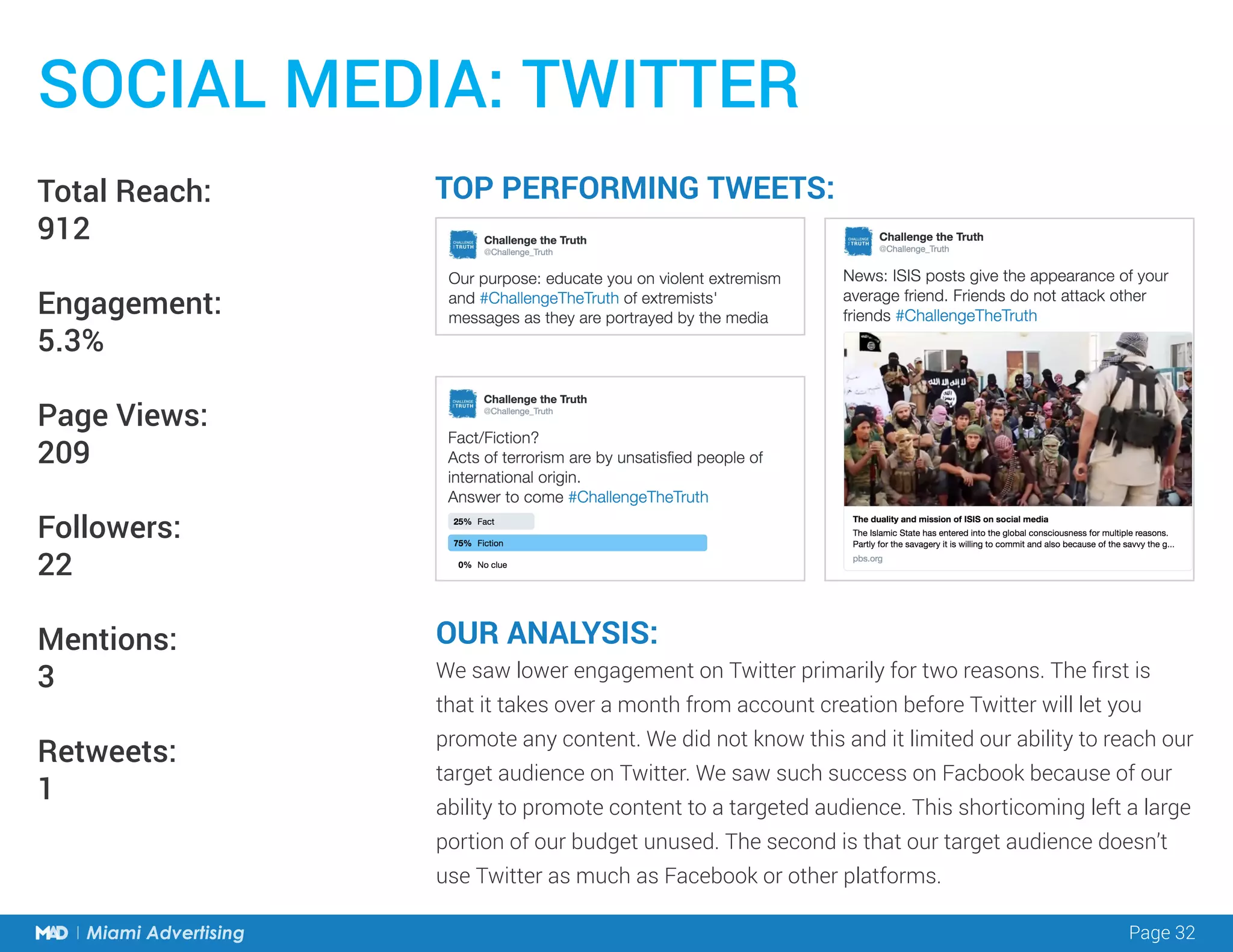
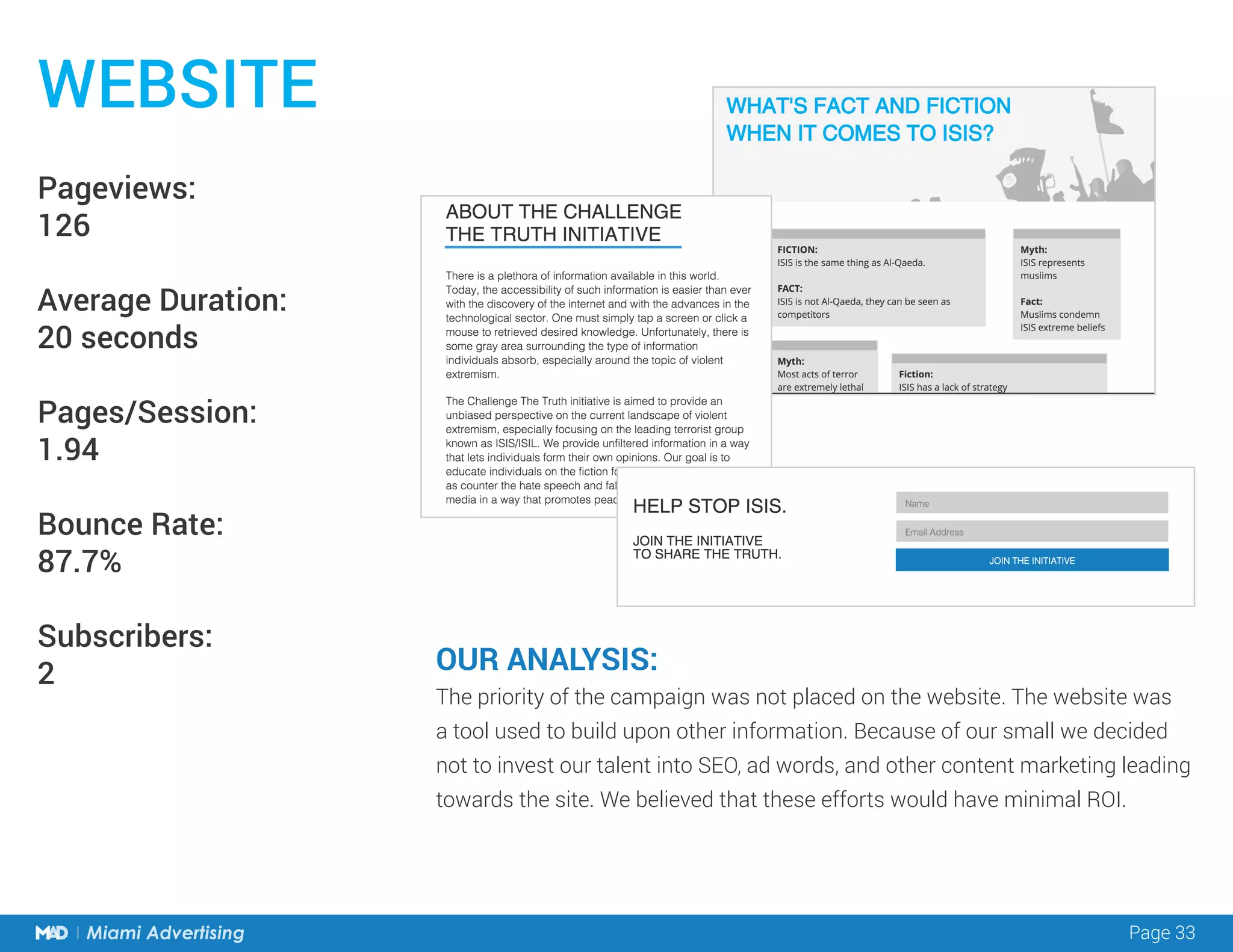
This document summarizes the research and strategy behind a social media campaign called "Challenge The Truth" aimed at countering violent extremism at Miami University. Research found that students lacked knowledge about violent extremism and ISIS. The strategy was to provide accurate, unbiased information on social media platforms to educate students and counter the exaggerated portrayals in the media. The campaign would create informative articles and use polls to engage students while revealing the facts about violent extremism.