The document discusses RESTful web services and how to build them using the Mendix platform. Key points include:
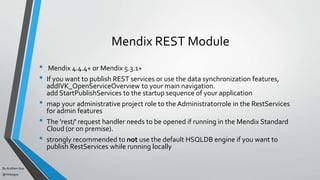
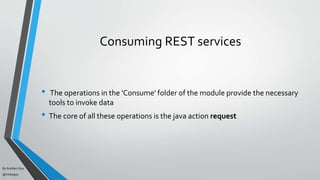
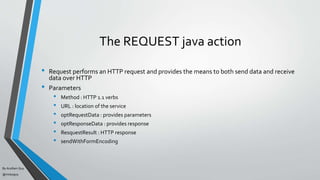
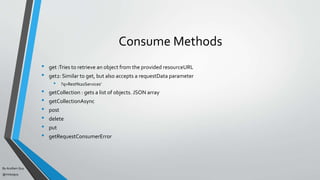
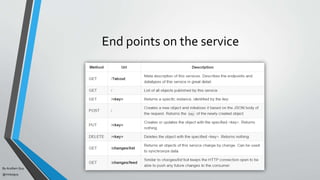
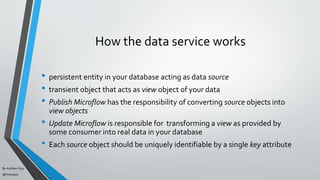
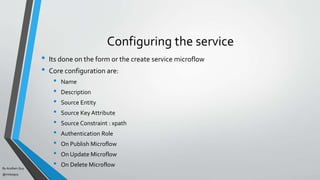
1. The Mendix REST module allows consuming external REST APIs, publishing microflows and data models as REST endpoints, and synchronizing data between Mendix applications in real-time.
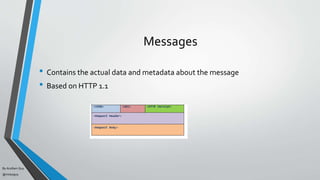
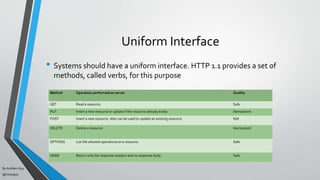
2. Core aspects of RESTful design include using HTTP verbs for CRUD operations, representing resources as JSON or XML, and making services stateless and cacheable through the use of URIs and links.
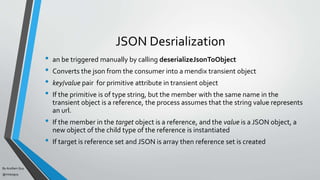
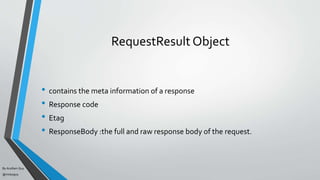
3. The Mendix REST module provides actions and configuration for publishing microflows and data models as REST endpoints, securing services, and serializing data to and from JSON for requests and responses.









![By Acellam Guy
@mistaguy
JSON Serialization
• Converts transient object to JSON
• Nearest json type
• For each owned reference that points to a transient object, another
key/value pair is added to the object
• For each owned referenceset that points to a transient object, the same
approach is taken, except that the value is an array ([])
• Manual serialization process by use of serializeObjectToJson java action.](https://image.slidesharecdn.com/mendixrestservices-150724064701-lva1-app6892/85/Mendix-rest-services-30-320.jpg)