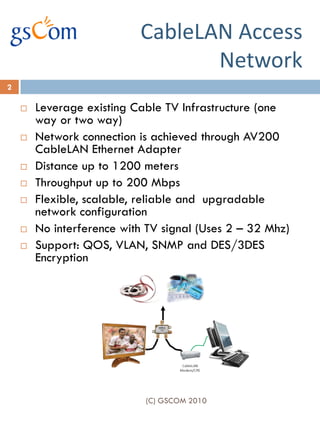
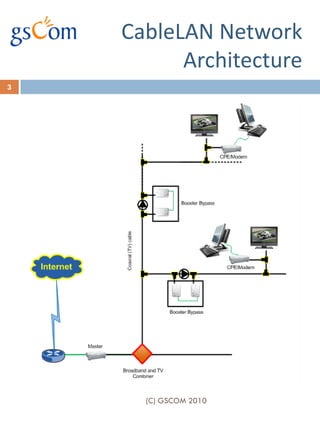
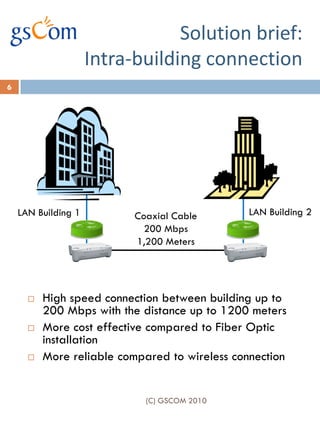
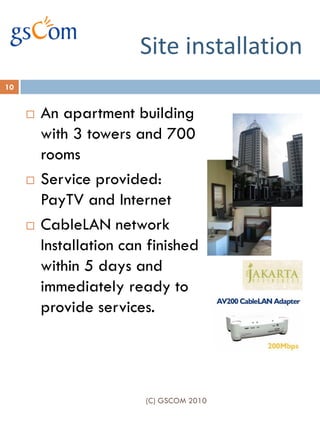
The document outlines the benefits of leveraging existing cable TV infrastructure for triple-play broadband services using CableLAN technology, which allows high-speed data transmission of up to 200 Mbps over distances of up to 1200 meters. It highlights key features such as flexibility, scalability, and the ability to support voice, data, and video applications without interfering with TV signals. Additionally, it provides cost-effective installation options compared to fiber optics and emphasizes the quick deployment of services.