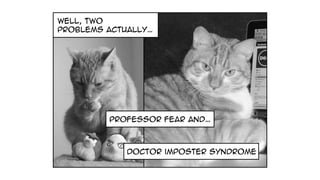
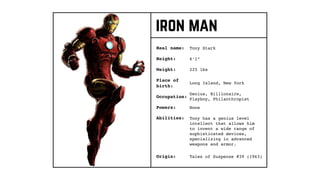
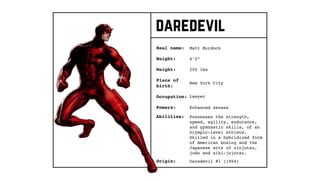
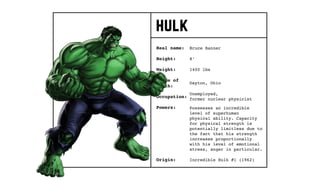
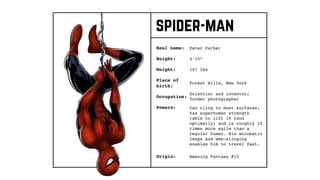
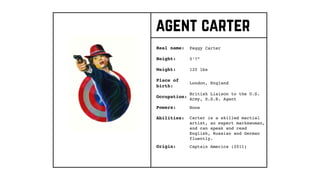
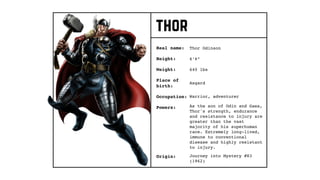
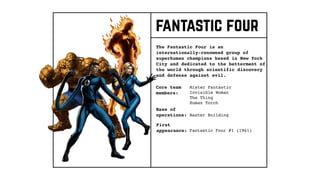
The document presents a narrative of Melinda Seckington, who transforms into 'Miss Geeky' to combat villains like 'Professor Fear' and 'Doctor Imposter Syndrome' in her journey as a developer. It introduces the concept of becoming a 'superhero developer' by embodying extraordinary abilities, a strong moral code, and seeking collaboration with others in the tech community. The piece also outlines key lessons and traits learned from various superhero characters, emphasizing collaboration, resilience, and continuous learning.