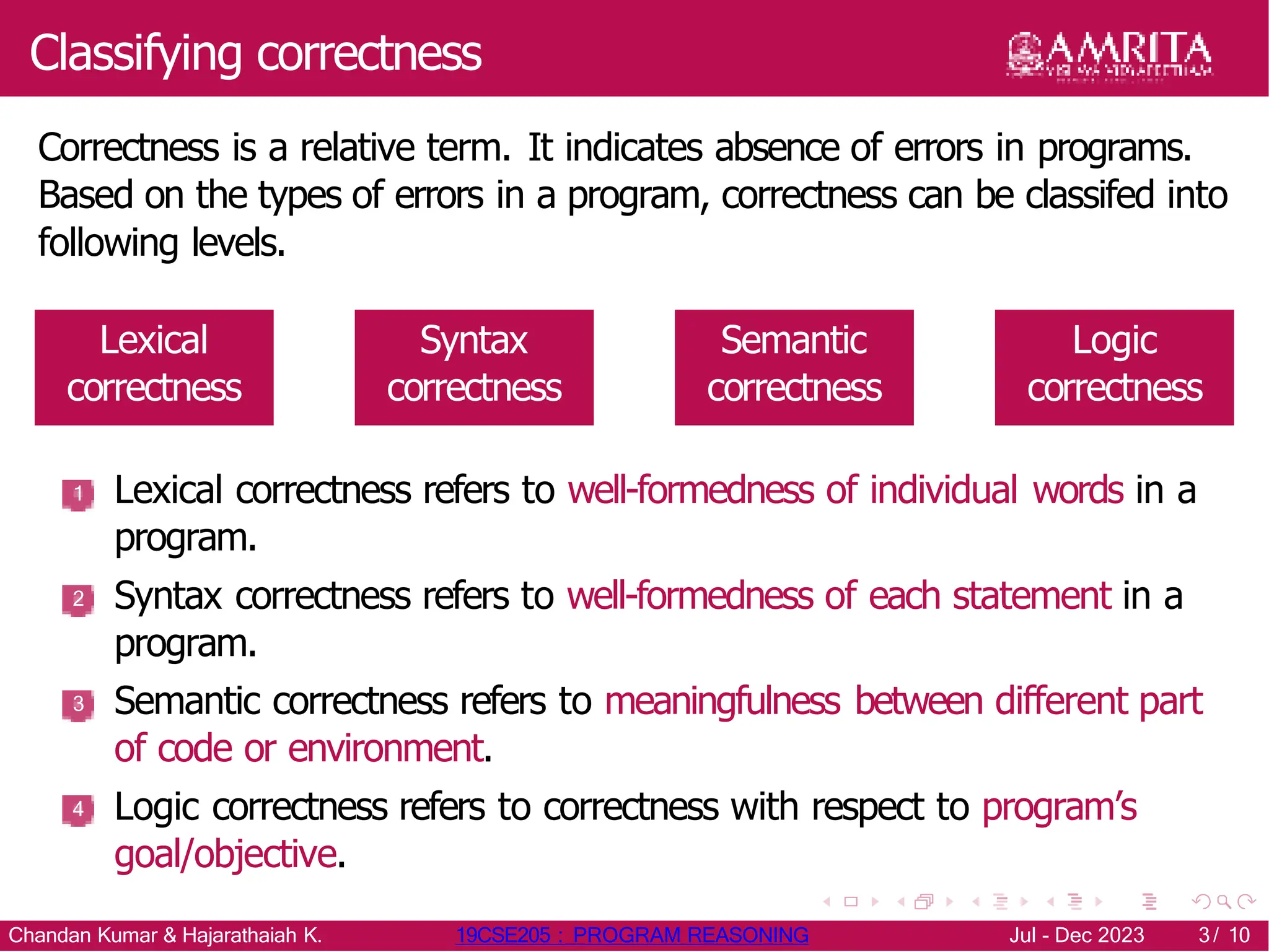
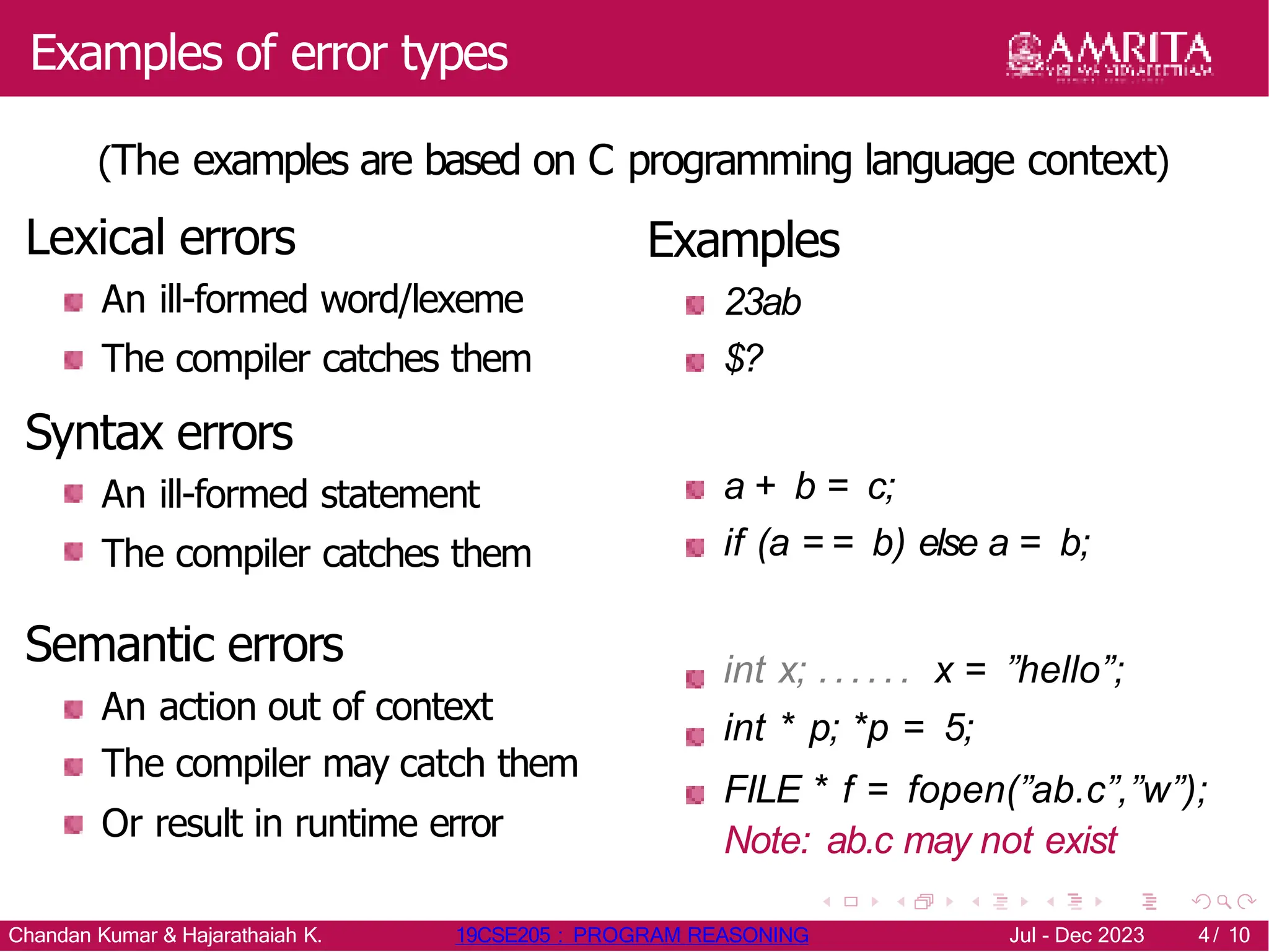
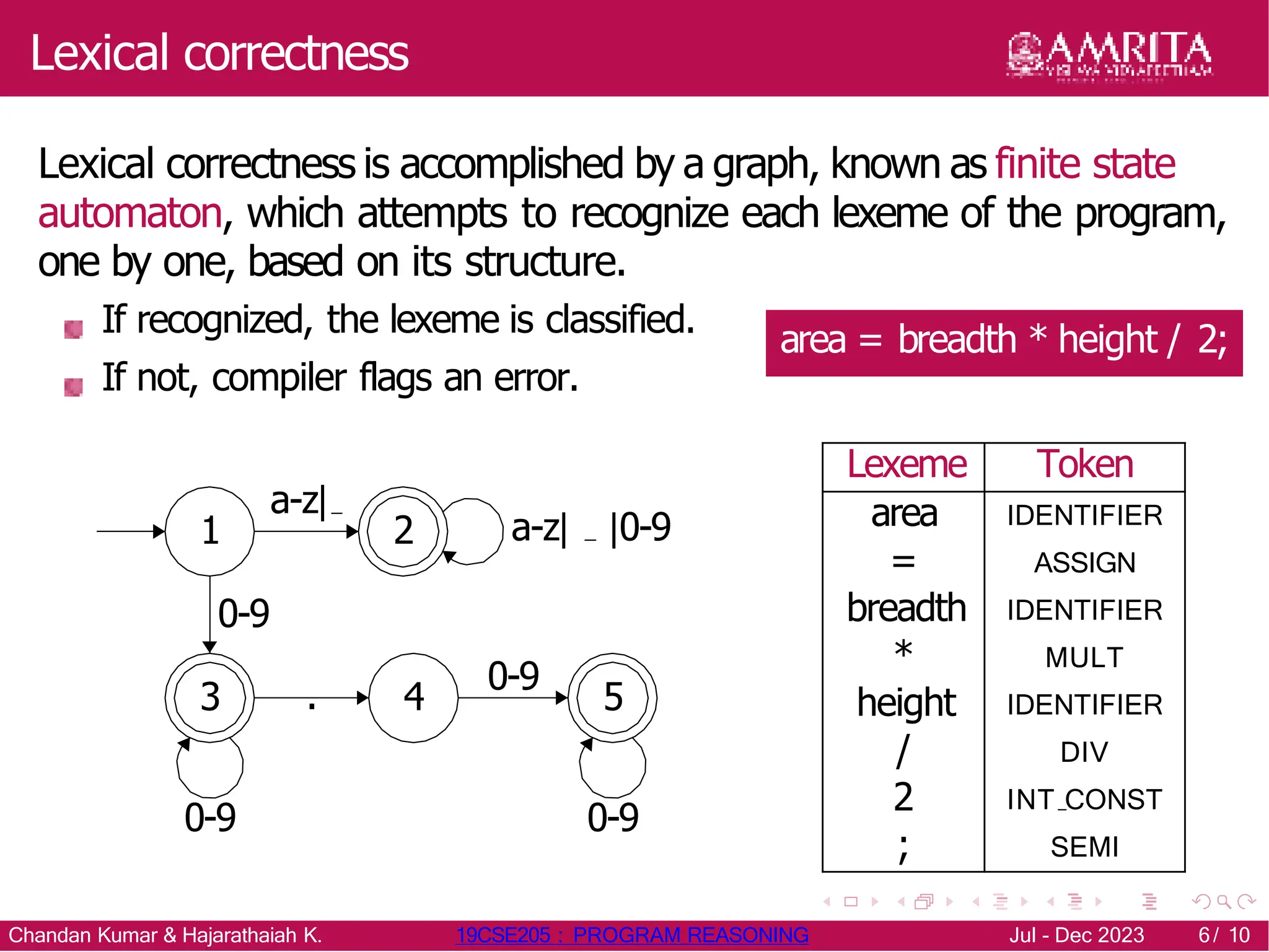
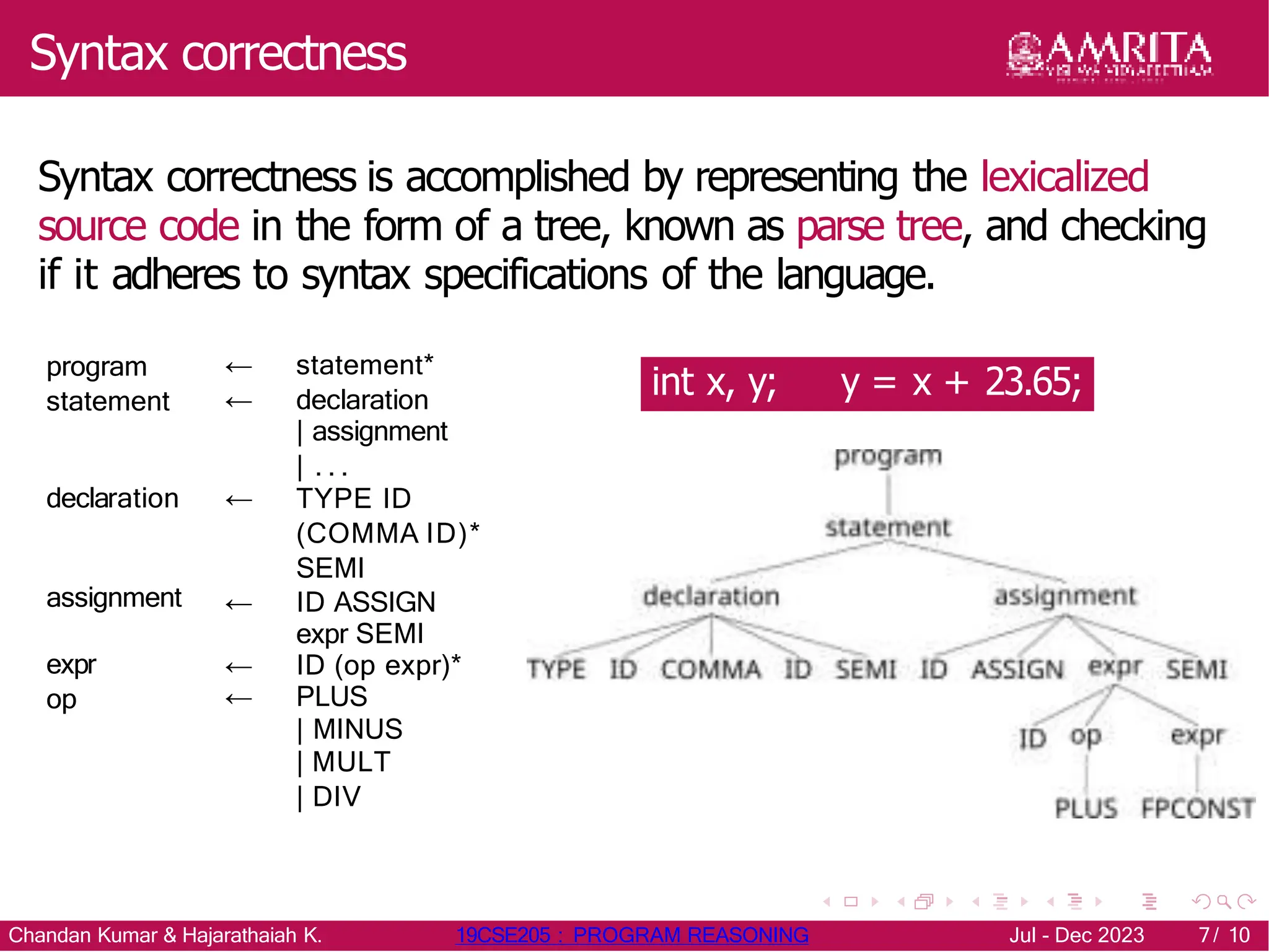
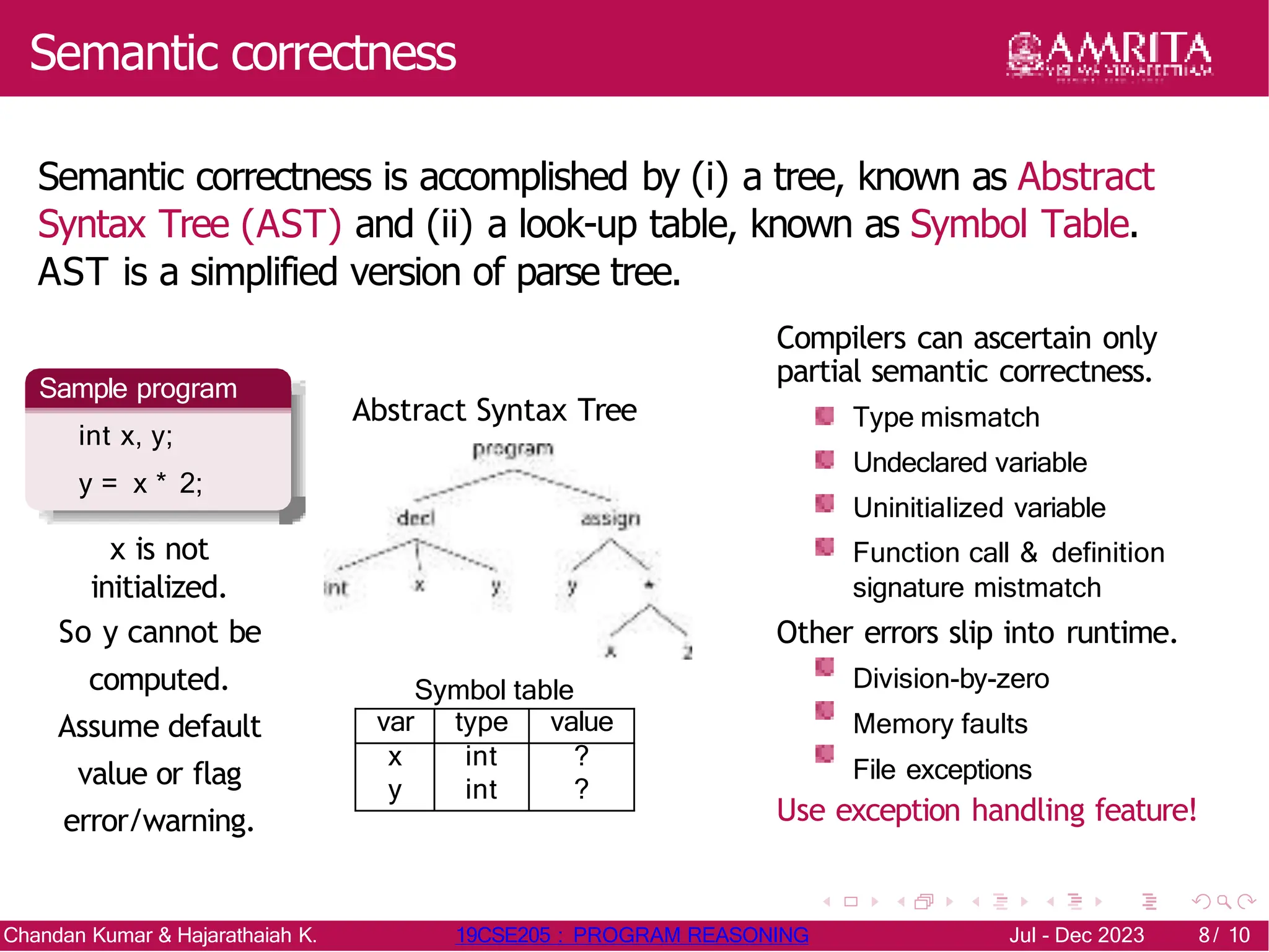
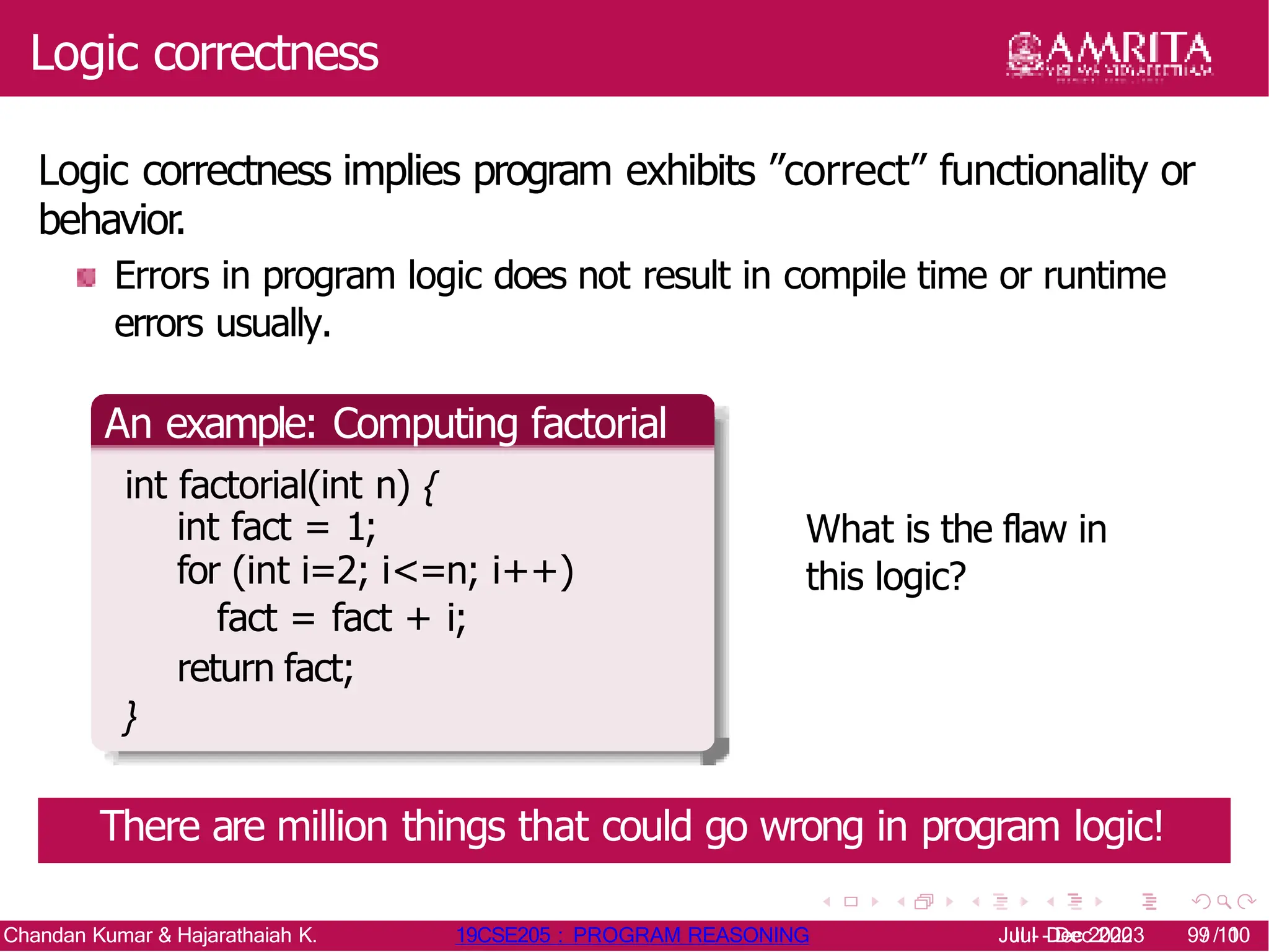
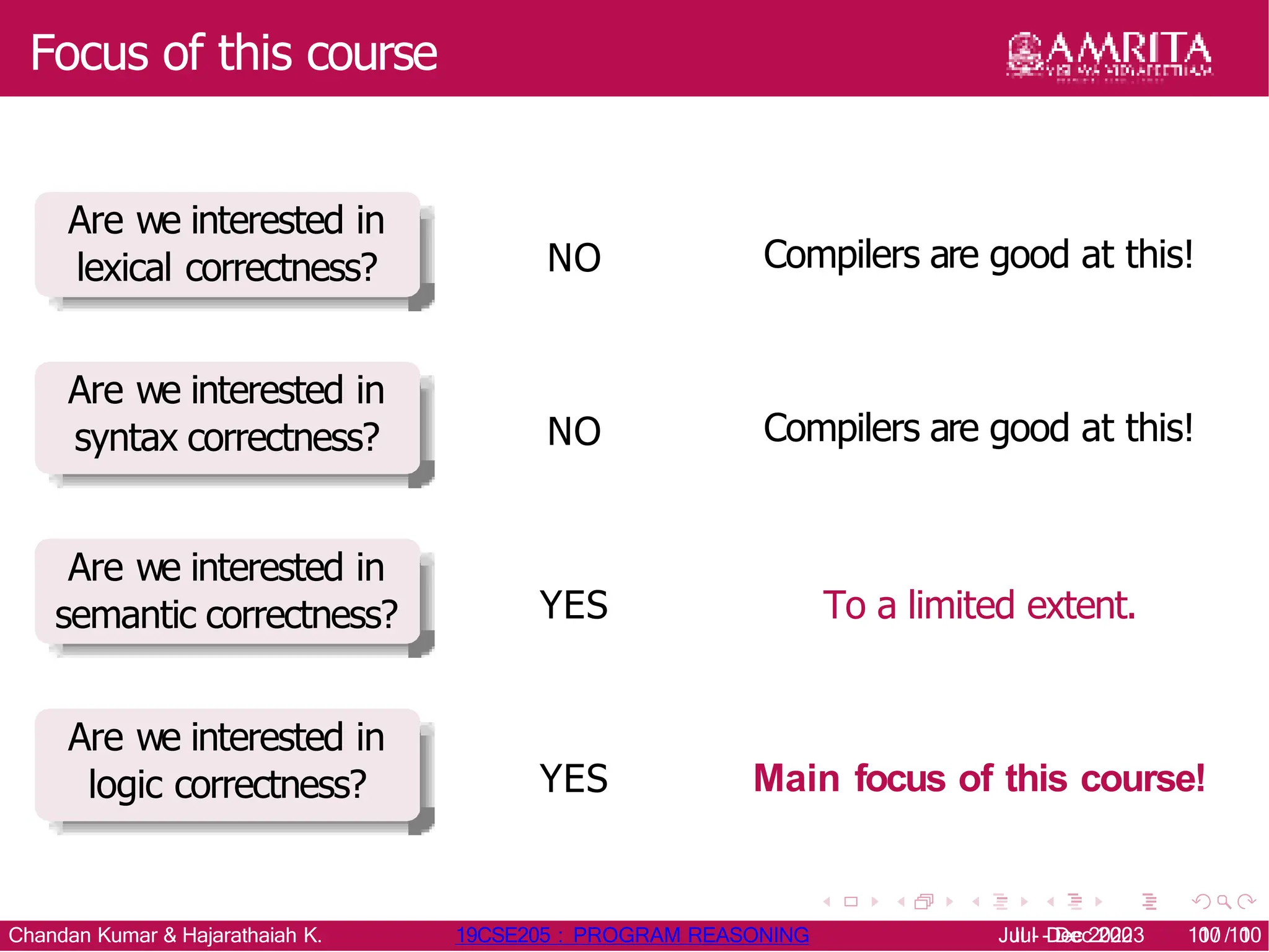
The document discusses levels of program correctness, categorizing it into lexical, syntax, semantic, and logic correctness, with examples of errors associated with each. It highlights the role of static analyzers in detecting errors and explains how they work, including the use of finite state automata, parse trees, and abstract syntax trees. The focus of the course is primarily on logic correctness, emphasizing the importance of ensuring that a program meets its intended functionality.