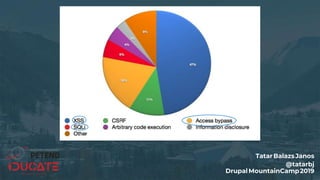
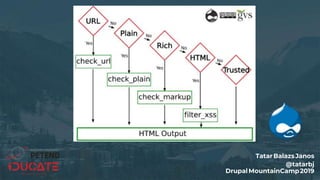
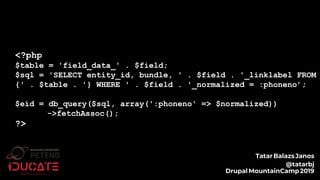
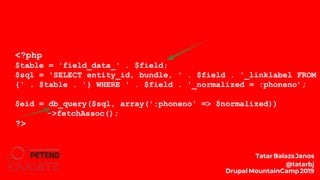
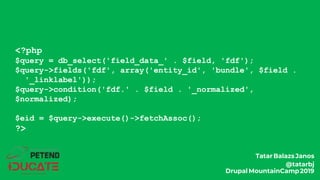
This document summarizes a presentation on secure Drupal coding given by Balazs Janos Tatar at the Drupal Mountain Camp 2019 conference. The presentation covered common types of vulnerabilities like cross-site scripting, access bypass, SQL injection, and discussed ways to prevent them, such as sanitizing user input, using the database API, and implementing access controls correctly. Code snippets were presented and the audience was asked to identify any issues. The goal was to help developers write more secure Drupal code.















![function custom_field_formatter_view(...) {
foreach ($items as $key => $value) {
//...
$element[$key] = array(
'#type' => 'markup',
'#markup' => t('<img src="!src" alt="@alt" />',
array('!src' => $value['src'], ‚$alt’ => $value['alt'])),
);
//...
}
return $element;
}
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-26-320.jpg)
![function custom_field_formatter_view(...) {
foreach ($items as $key => $value) {
//...
$element[$key] = array(
'#type' => 'markup',
'#markup' => t('<img src="!src" alt="@alt" />',
array('!src' => $value['src'], ‚$alt’ => $value['alt'])),
);
//...
}
return $element;
}
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-27-320.jpg)
![function custom_field_formatter_view(...) {
foreach ($items as $key => $value) {
//...
$element[$key] = array(
'#type' => 'markup',
'#markup' => t('<img src="@src" alt="@alt" />',
array('@src' => $value['src'], ‚$alt’ => $value['alt'])),
);
//...
}
return $element;
}
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-28-320.jpg)
![foreach ($items as $delta => $item) {
$id = $item->getValue()['target_id'];
$content = Drupal::entityTypeManager()
->getStorage($entity_type_id)
->load($id);
$body = $content->get('body_field')->getValue()[0]['value'];
}
$elements[$delta] = array(
'#theme' => 'something_custom',
'#body' => $body,
);
return $elements;
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-31-320.jpg)
![foreach ($items as $delta => $item) {
$id = $item->getValue()['target_id'];
$content = Drupal::entityTypeManager()
->getStorage($entity_type_id)
->load($id);
$body = $content->get('body_field')->getValue()[0]['value'];
}
$elements[$delta] = array(
'#theme' => 'something_custom',
'#body' => $body,
);
return $elements;
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-32-320.jpg)
![foreach ($items as $delta => $item) {
$id = $item->getValue()['target_id'];
$content = Drupal::entityTypeManager()
->getStorage($entity_type_id)
->load($id);
$body = [
'#type' => 'processed_text',
'#text' => $content->get('body_field')->getValue()[0]['value'],
'#format' => $content->get('body_field')->getValue()[0]['format'], ];
}
$elements[$delta] = array(
'#theme' => 'something_custom',
'#body' => $body,
);
return $elements;
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-33-320.jpg)










![<?php
function _generate_password($length = 8) {
$pass = ’’;
for ($i = 0; $i < $length; $i++) {
// Each iteration, pick a random character from the
// allowable string and append it to the password:
$pass .= $allowable_characters[mt_rand(0, $len)];
}
}
?>
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-55-320.jpg)
![<?php
function _generate_password($length = 8) {
$pass = ’’;
for ($i = 0; $i < $length; $i++) {
// Each iteration, pick a random character from the
// allowable string and append it to the password:
$pass .= $allowable_characters[mt_rand(0, $len)];
}
}
?>
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-56-320.jpg)
![<?php
function _generate_password($length = 8) {
$pass = ’’;
for ($i = 0; $i < $length; $i++) {
do {
// Find a secure random number within the range needed.
$index = ord(drupal_random_bytes(1));
} while ($index > $len);
$pass .= $allowable_characters[$index];
}
}
?>
TatarBalazsJanos
@tatarbj
DrupalMountainCamp2019](https://image.slidesharecdn.com/letswritesecuredrupalcodedavos2019-190308133345/85/Let-s-write-secure-Drupal-code-Drupal-MountainCamp-2019-57-320.jpg)