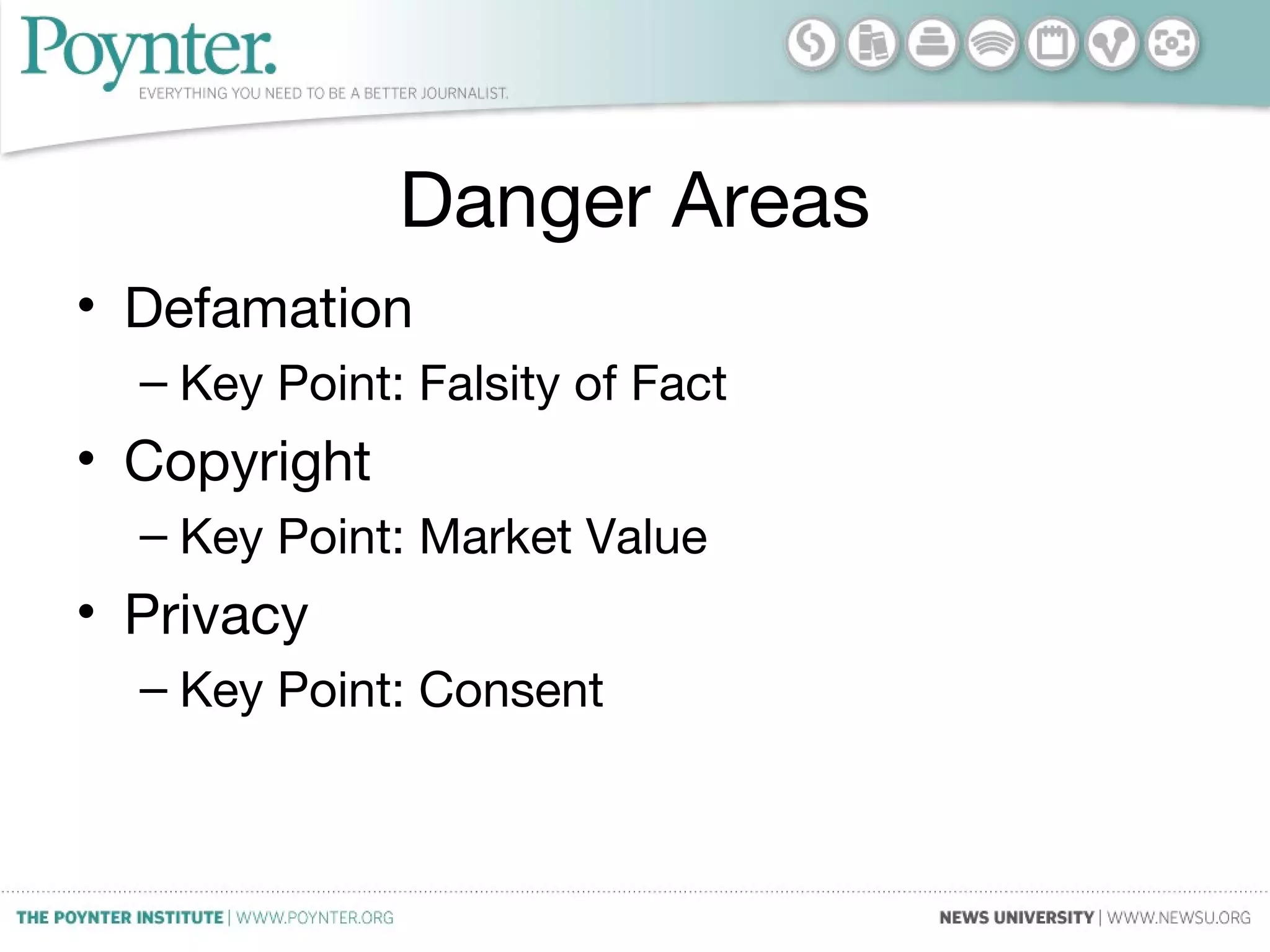
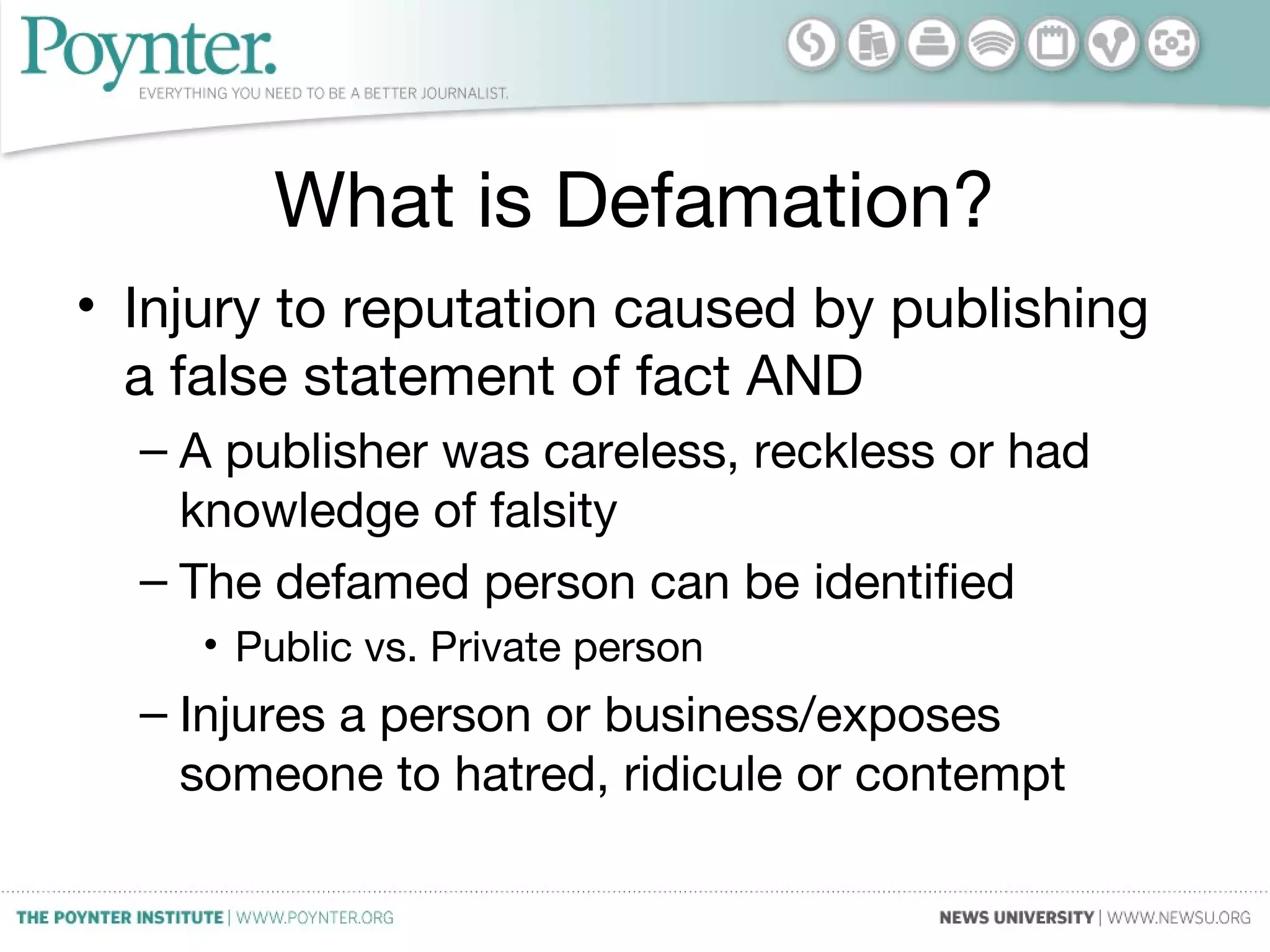
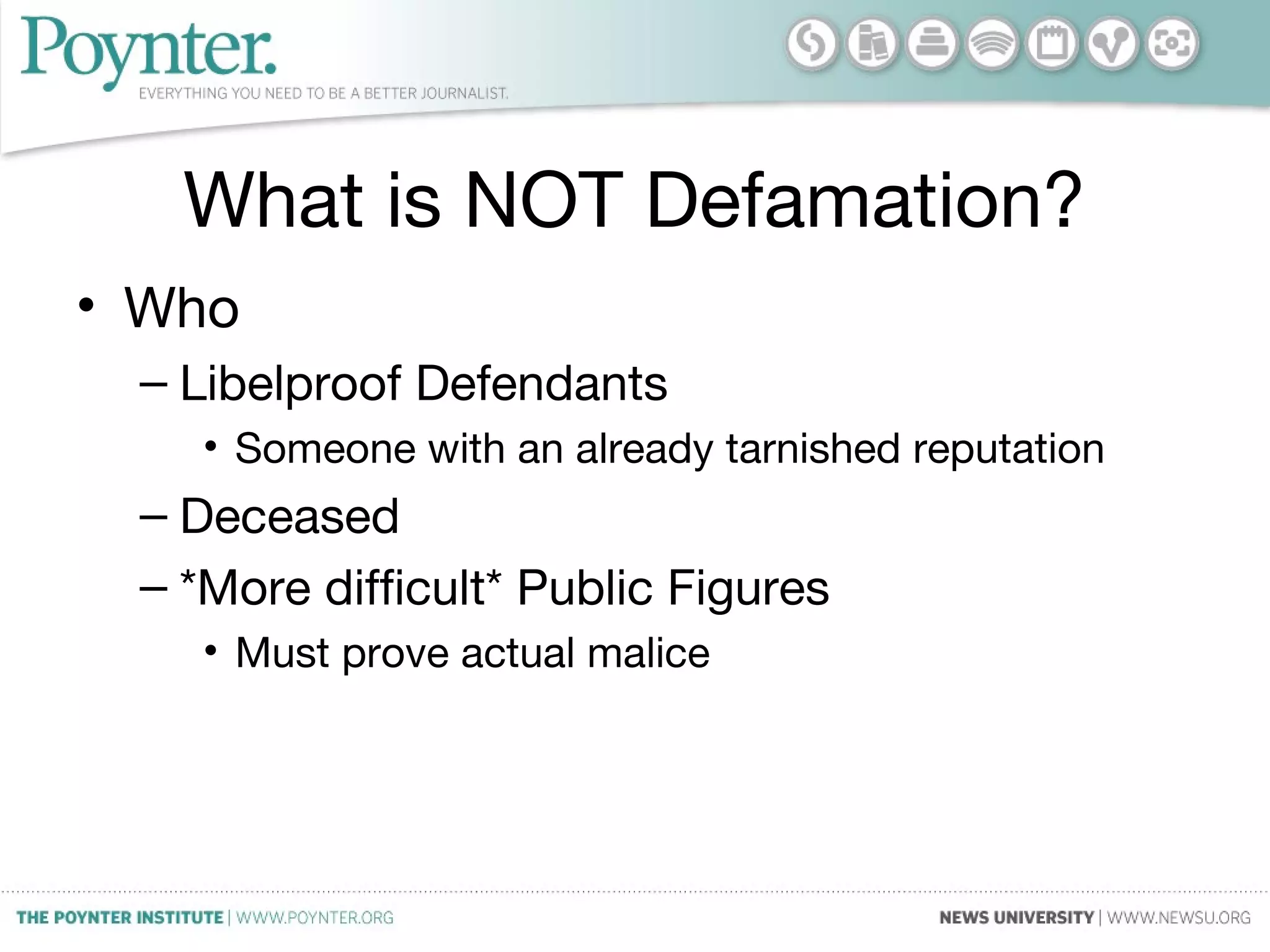
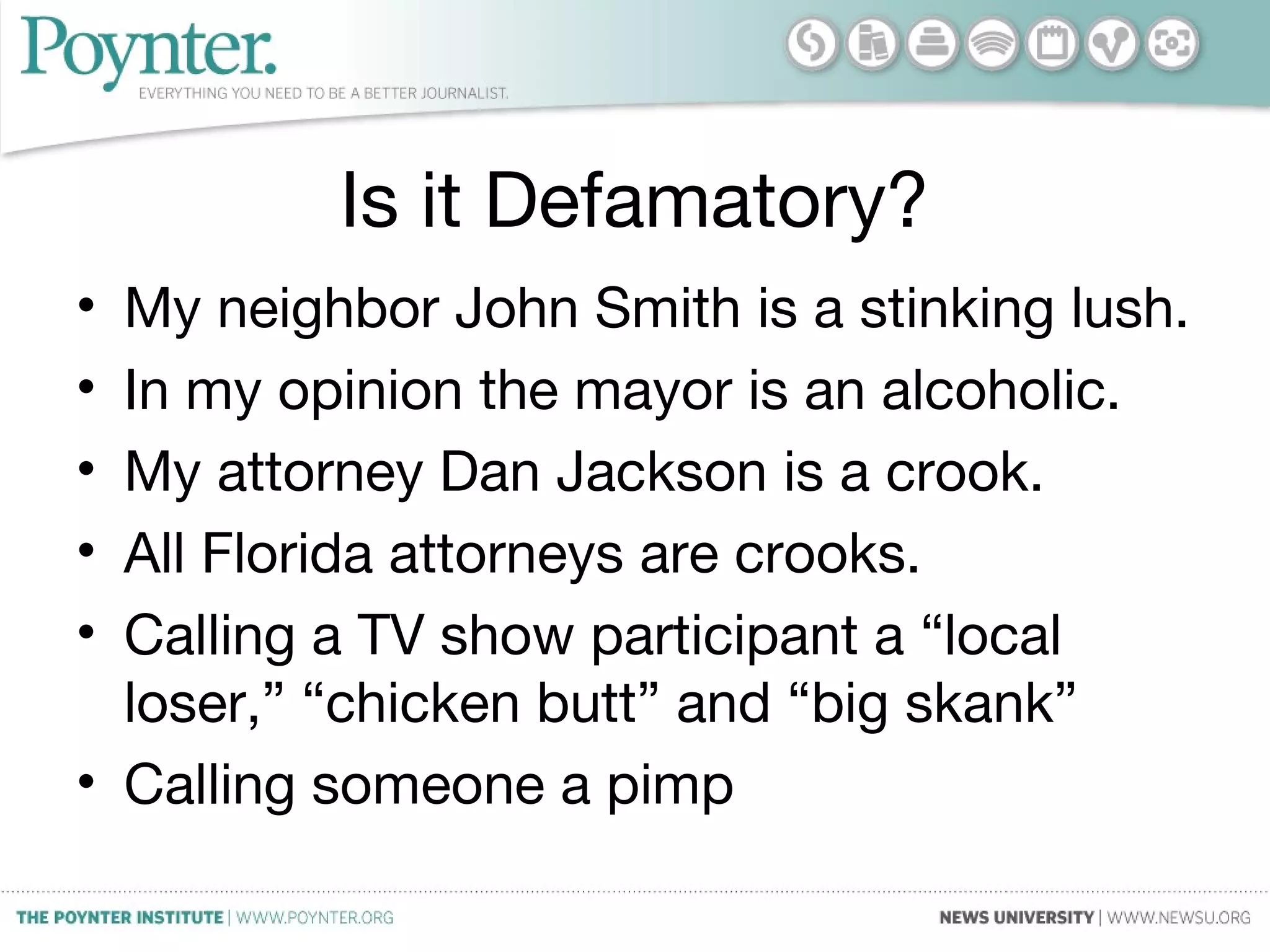
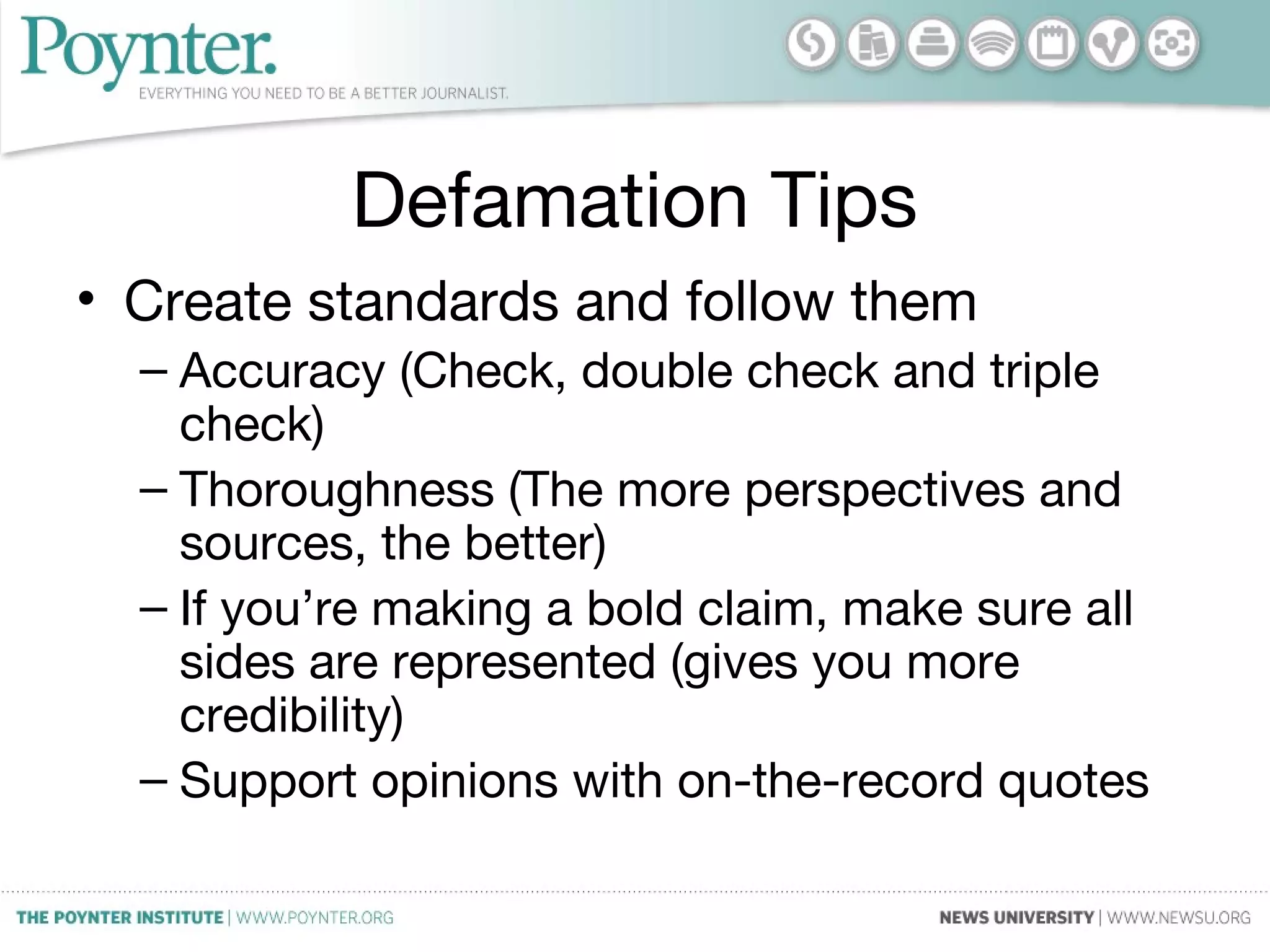
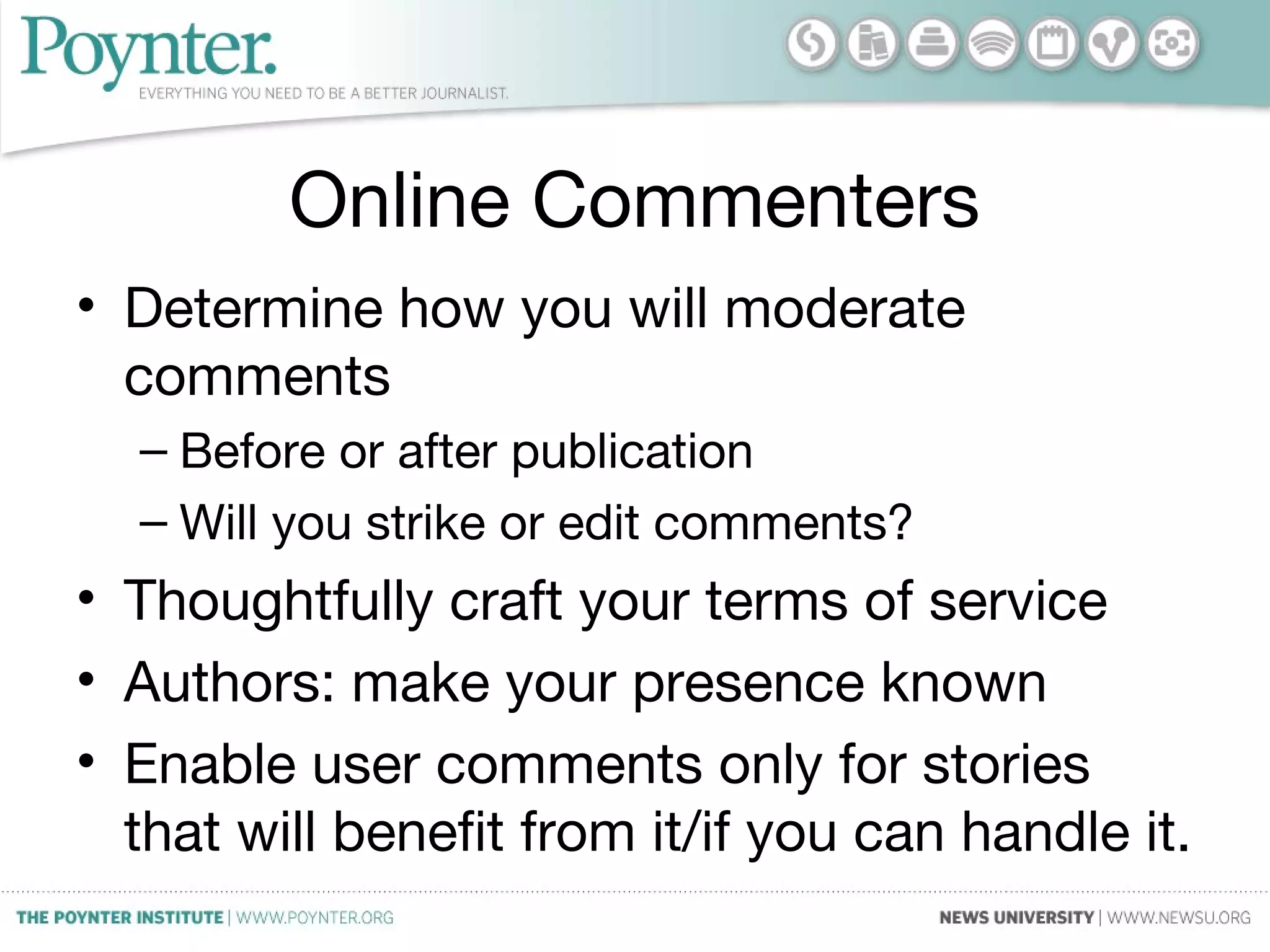
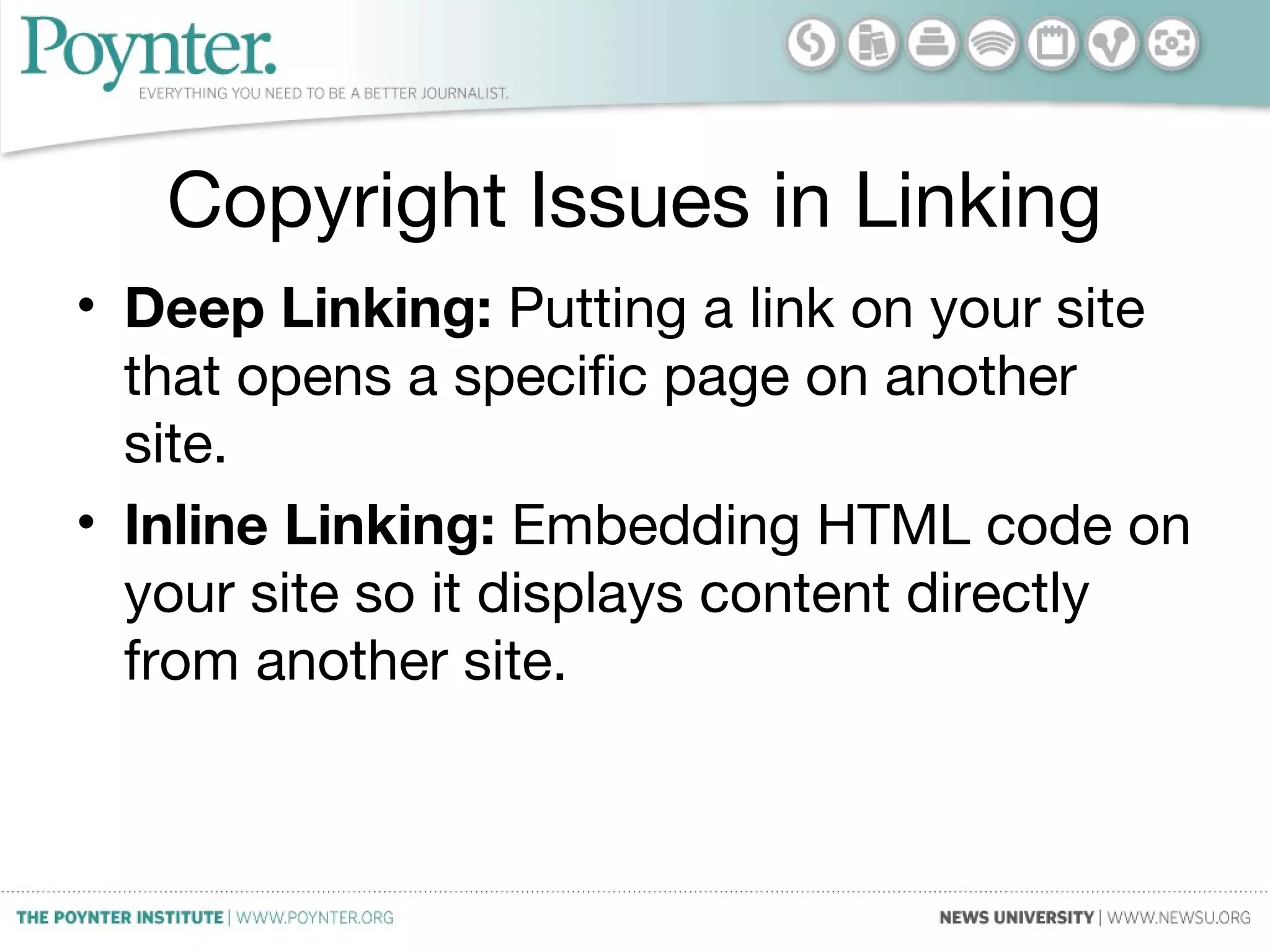
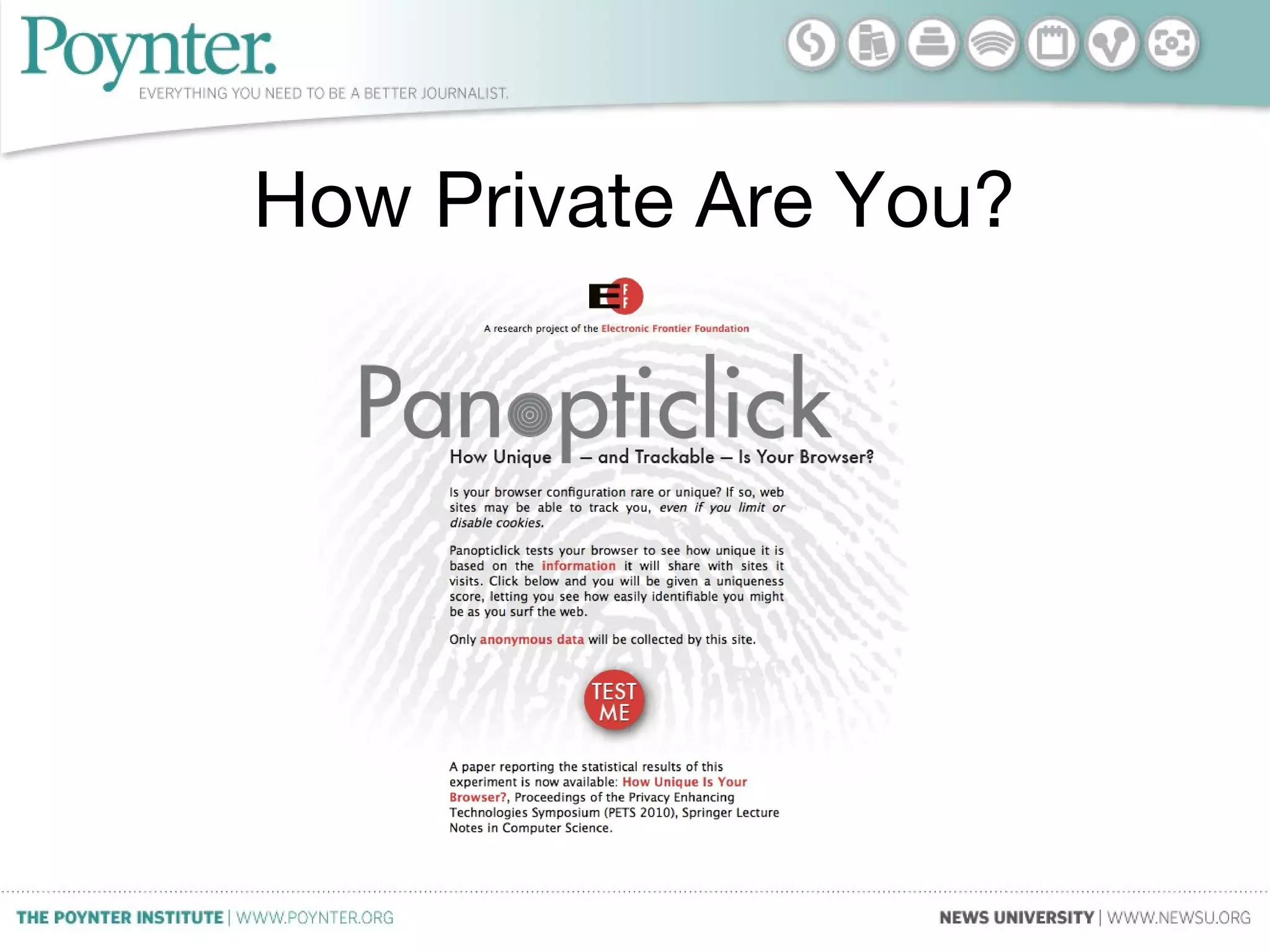
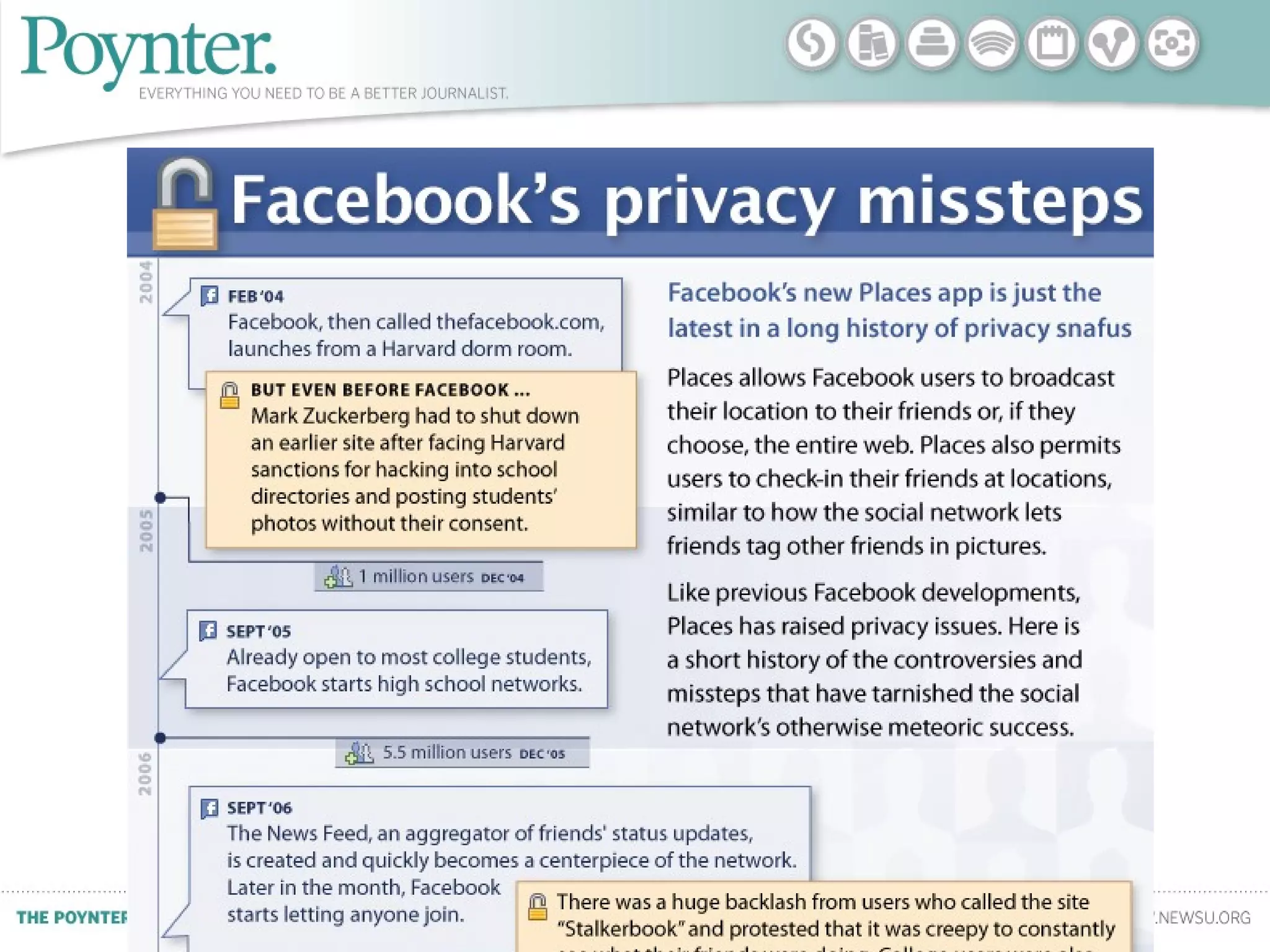
This document provides an overview of key legal issues to consider when using social media, including defamation, copyright, and privacy. It discusses how the law applies to different types of content and offers tips for minimizing risks. The main points are that context is important, factual accuracy is essential to avoid defamation claims, fair use and attribution principles apply to copyrighted content, and consent should be obtained when sharing private information. Resources for further information are also listed.