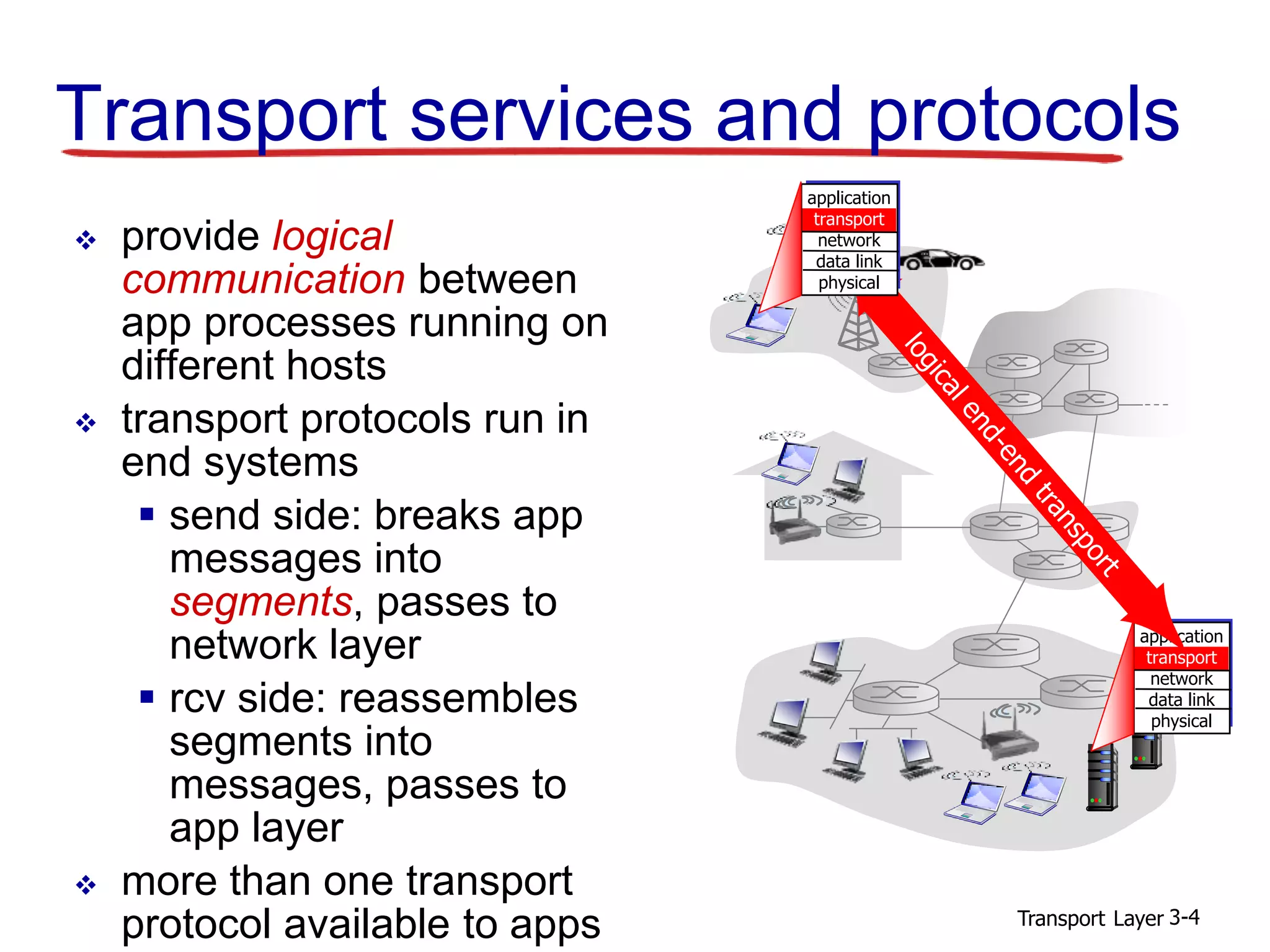
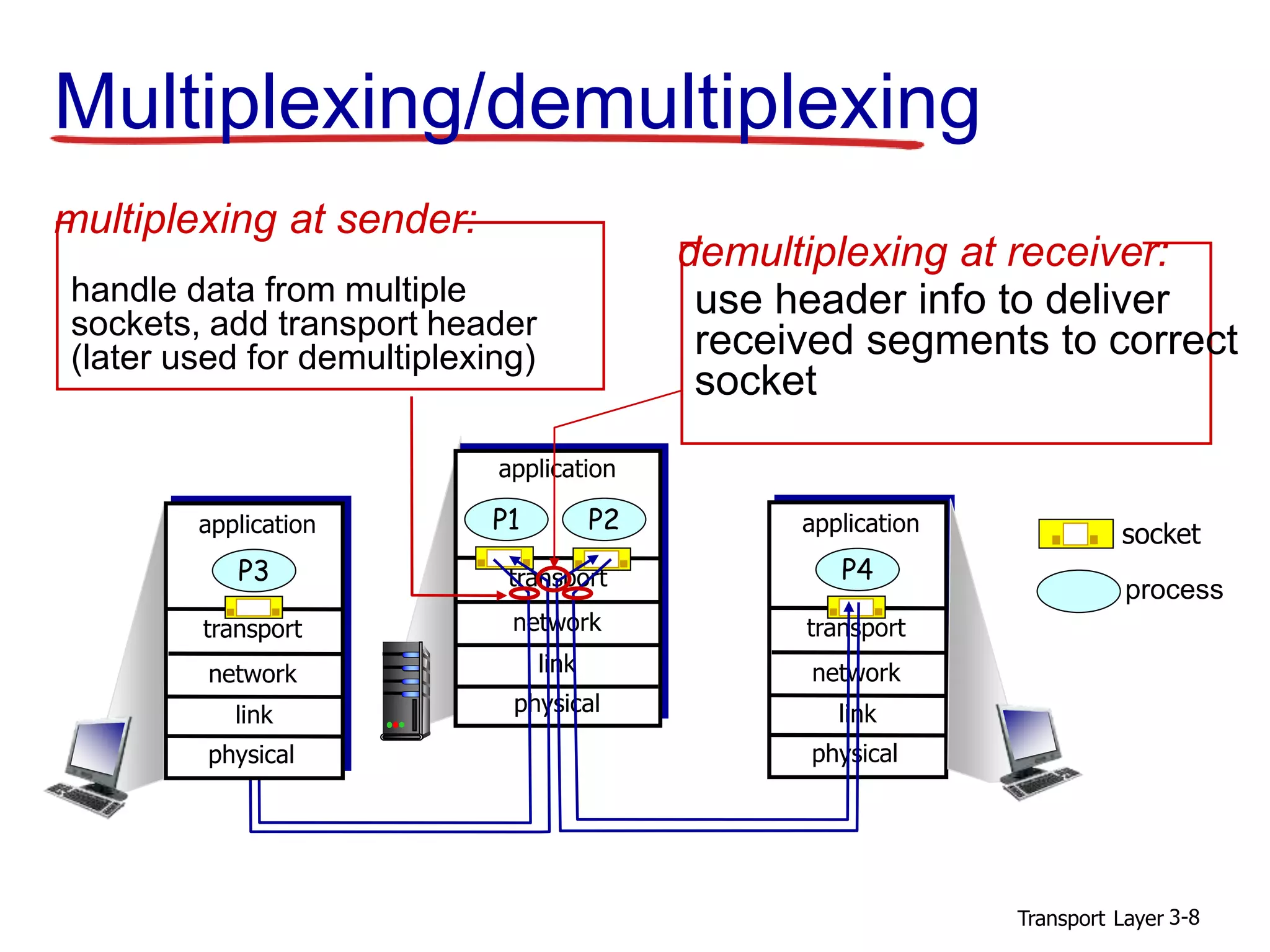
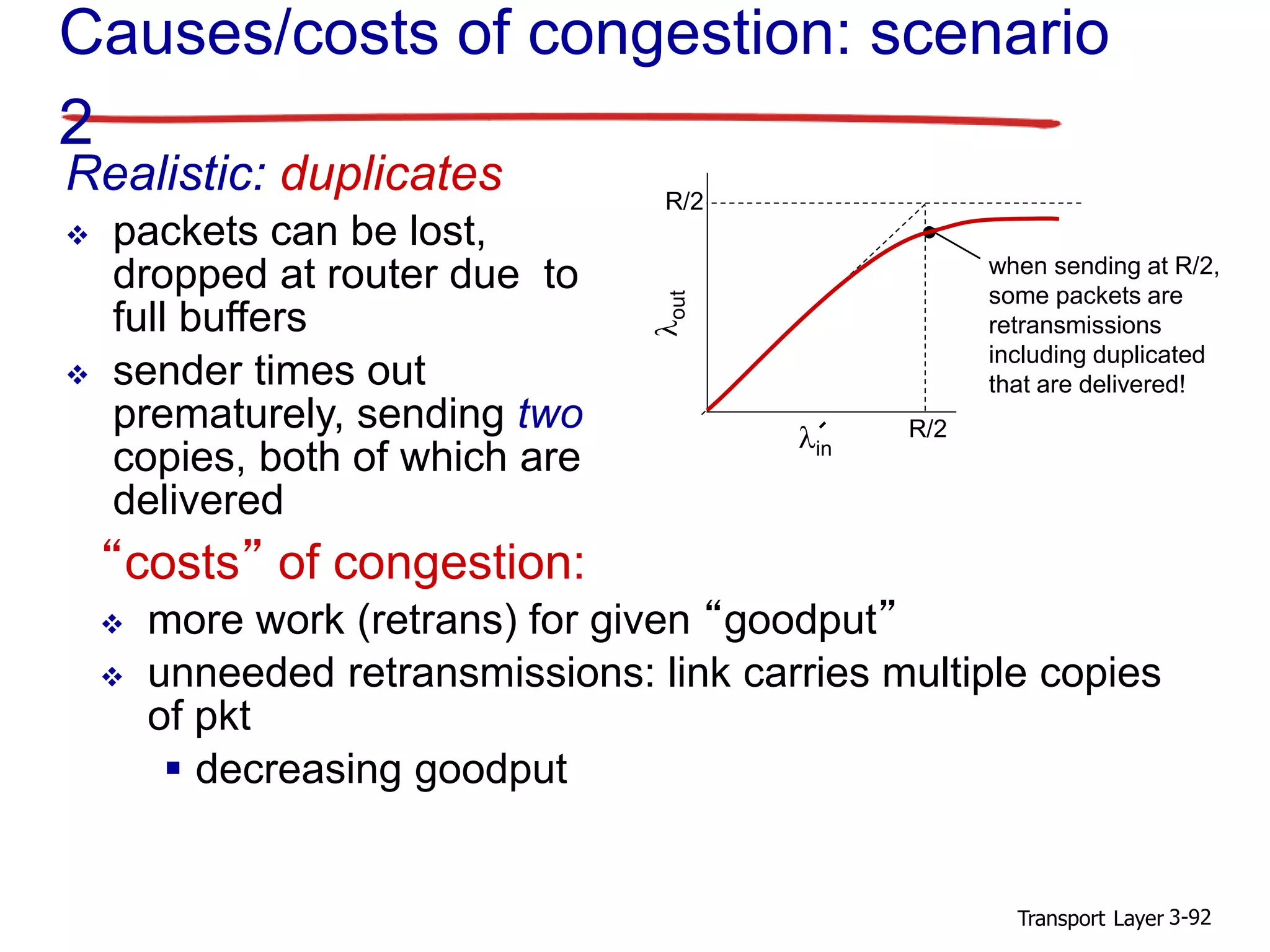
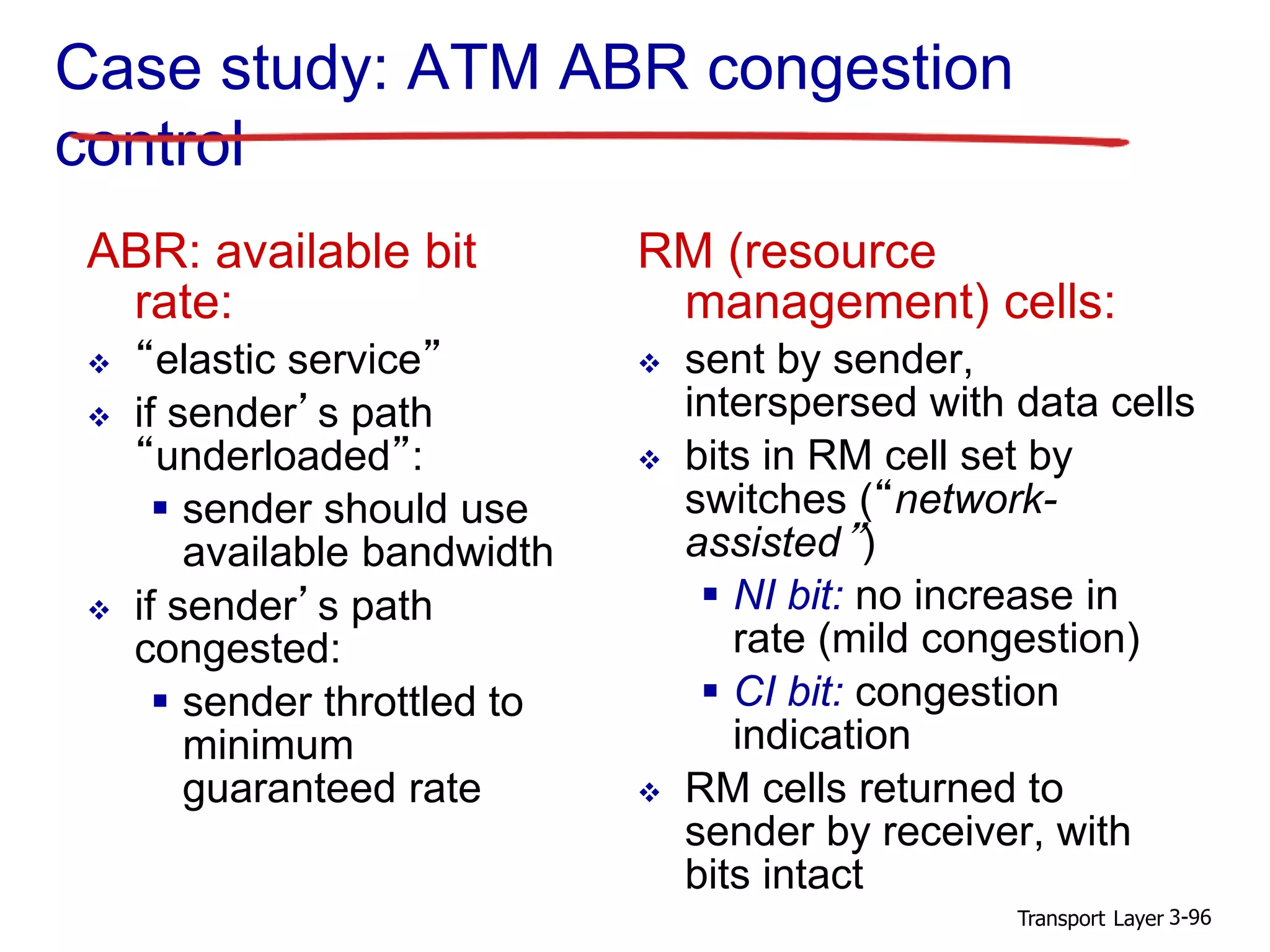
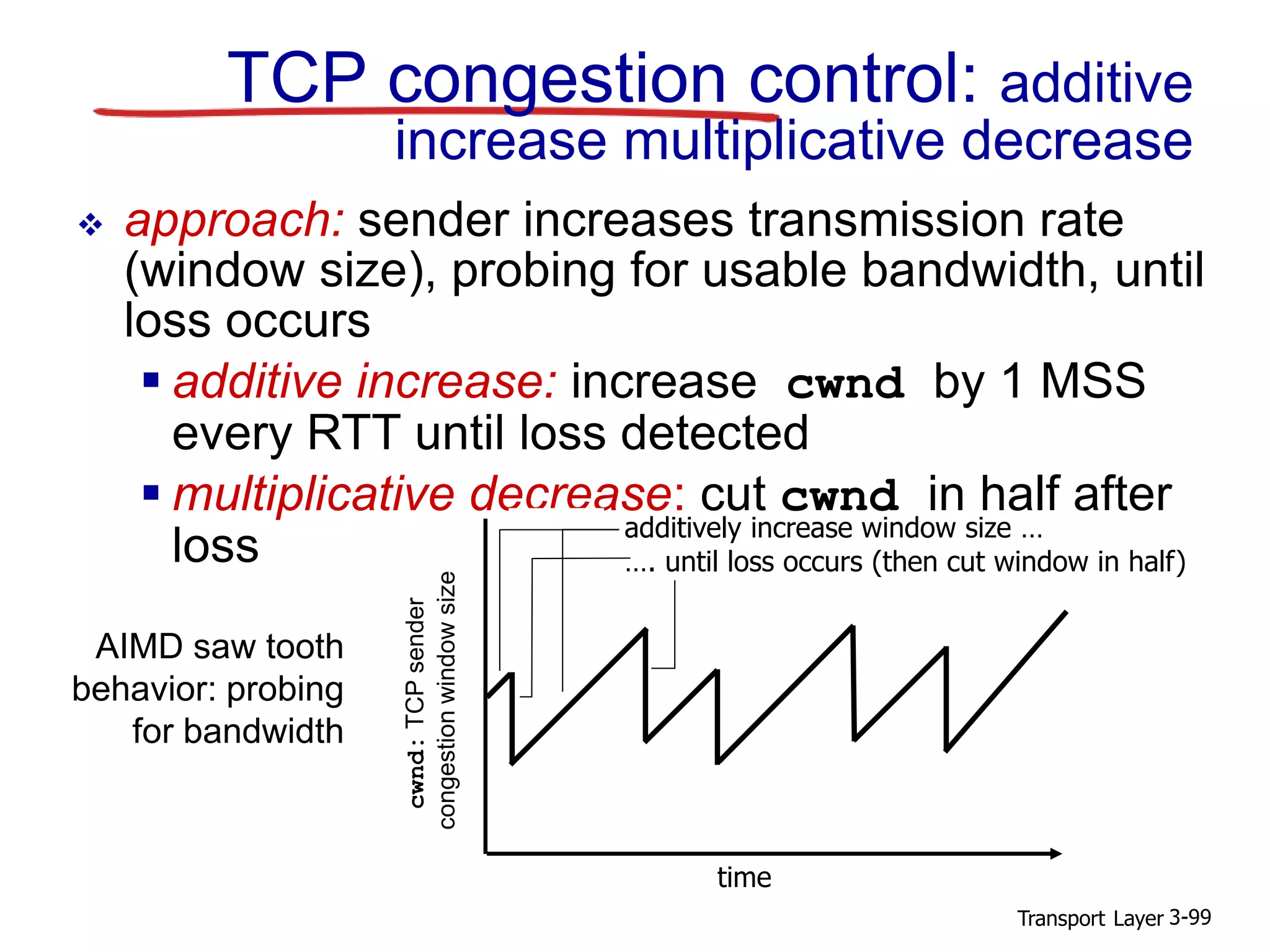
The document discusses the transport layer and key protocols TCP and UDP. It outlines the chapter which covers transport layer services like multiplexing and demultiplexing, connectionless transport with UDP, principles of reliable data transfer, connection-oriented transport with TCP including segment structure, reliable data transfer, flow control, and connection management, and principles of congestion control including TCP congestion control. It provides details on multiplexing and demultiplexing to direct segments to the appropriate socket, UDP using port numbers but providing unreliable delivery, and TCP using a 4-tuple to identify connections and providing reliable in-order byte stream delivery with congestion control and flow control.
![Transport Layer 3-16
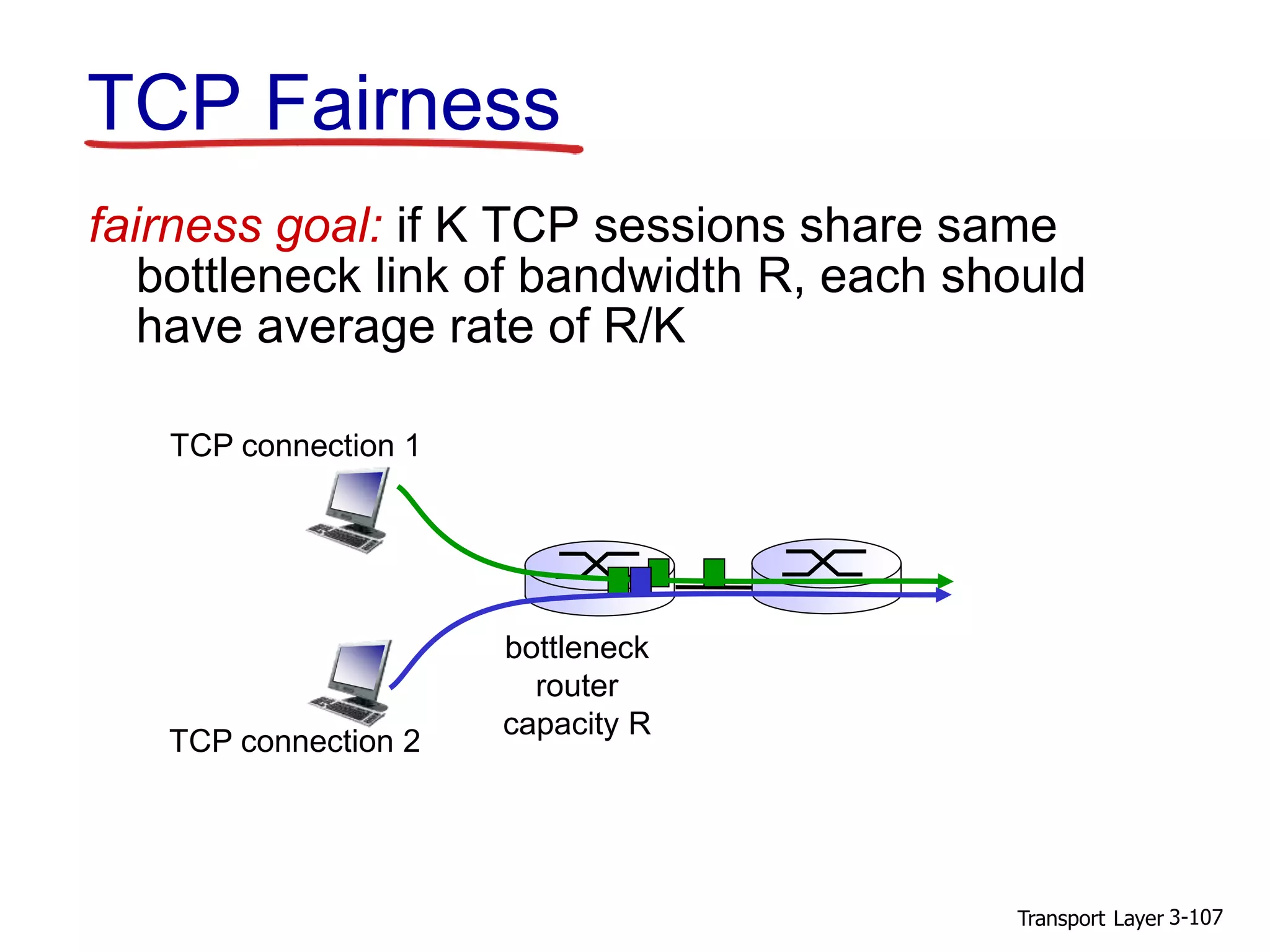
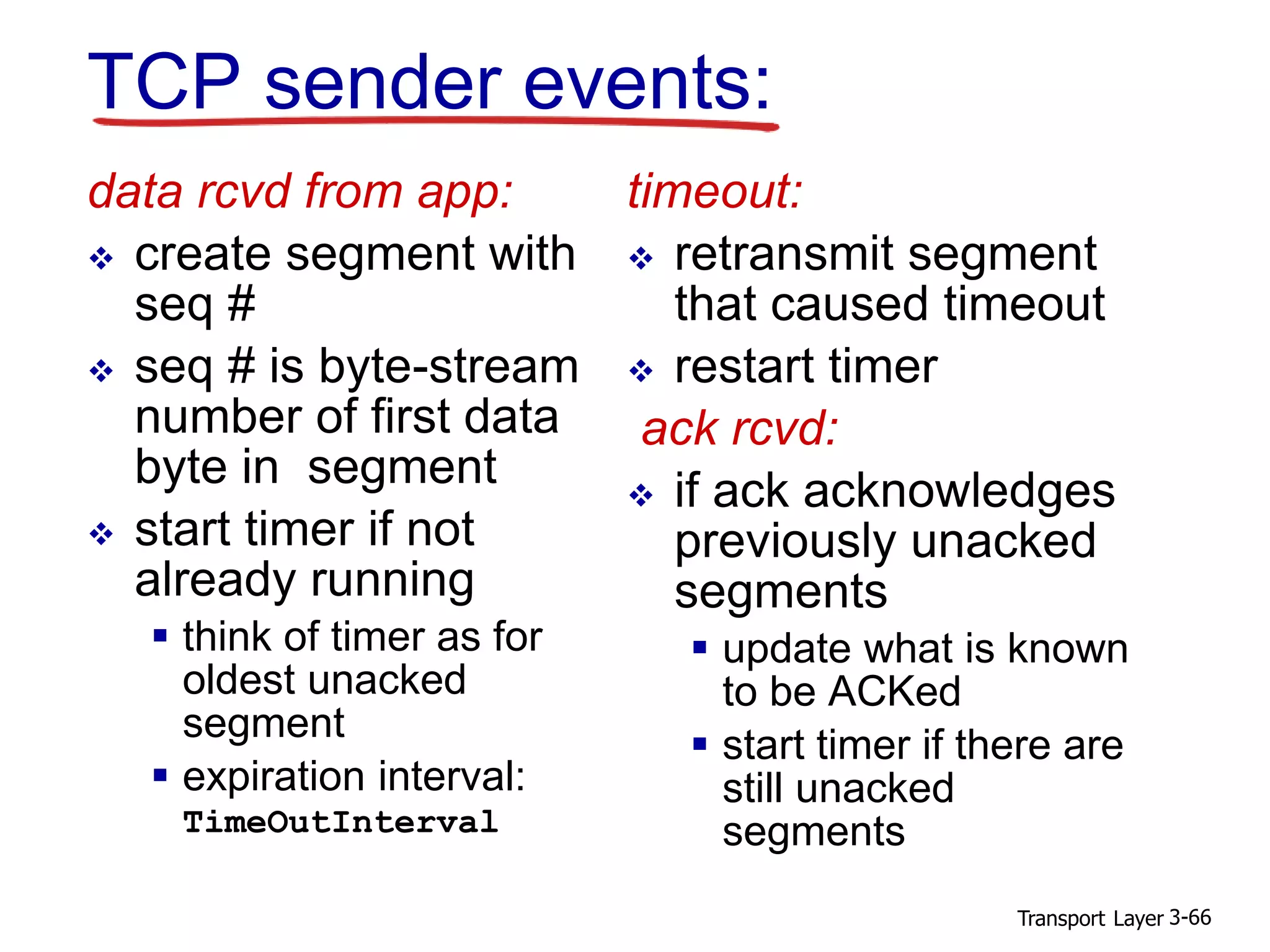
UDP: User Datagram Protocol [RFC
768]
“no frills, Internet
transport protocol
“best effort” service,
UDP segments may be:
lost
delivered out-of-order
to app
connectionless:
no handshaking
between UDP
sender, receiver
each UDP segment
handled
independently of
others
UDP use:
streaming multimedia
apps (loss tolerant,
rate sensitive)
DNS
SNMP
reliable transfer over
UDP:
add reliability at
application layer
application-specific
error recovery!](https://image.slidesharecdn.com/lec6-191115071239/75/Lec6-13-2048.jpg)
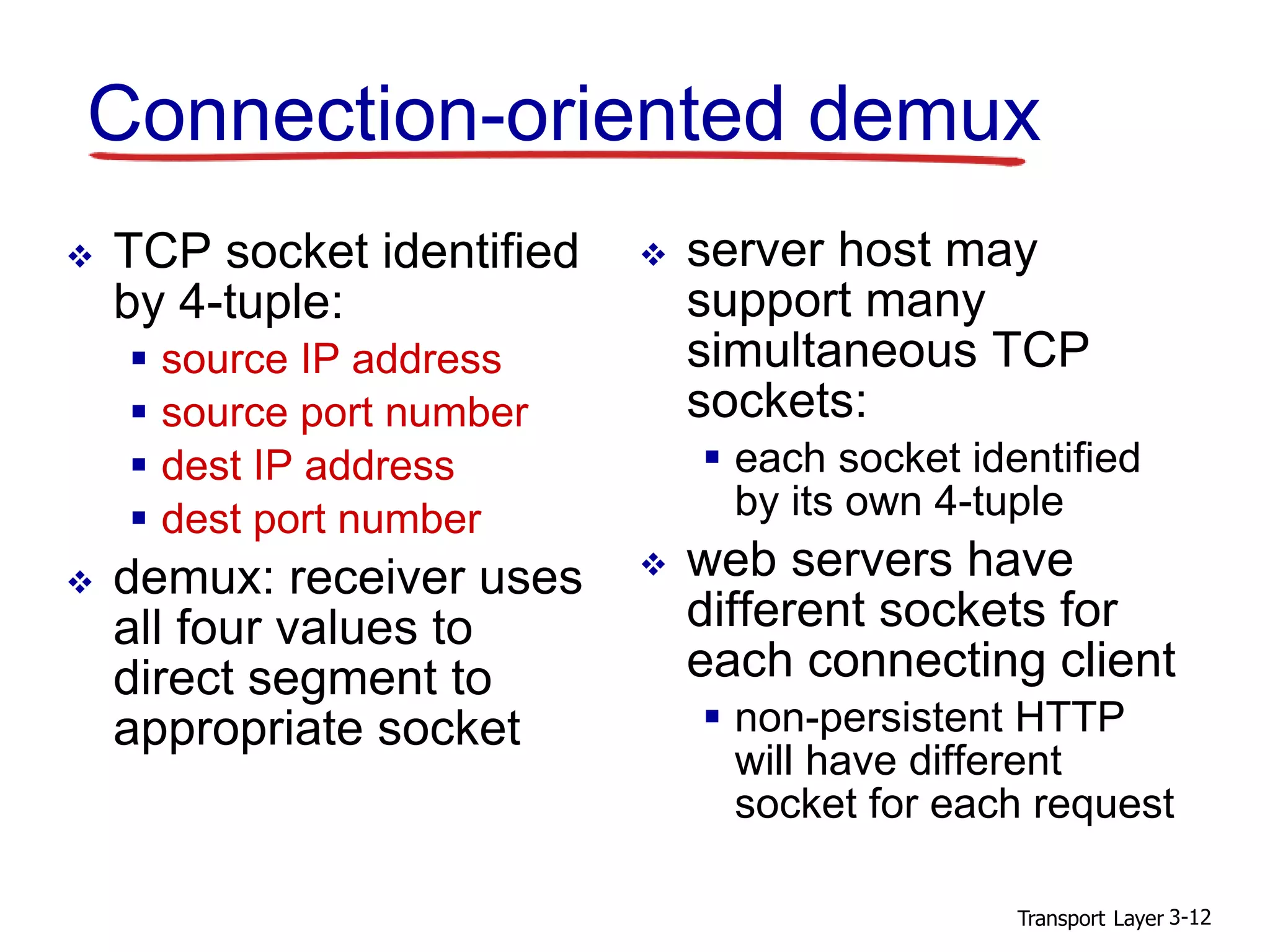
![Transport Layer 3-70
TCP ACK generation [RFC 1122, RFC 2581]
event at receiver
arrival of in-order segment with
expected seq #. All data up to
expected seq # already ACKed
arrival of in-order segment with
expected seq #. One other
segment has ACK pending
arrival of out-of-order segment
higher-than-expect seq. # .
Gap detected
arrival of segment that
partially or completely fills gap
TCP receiver action
delayed ACK. Wait up to 500ms
for next segment. If no next segment,
send ACK
immediately send single cumulative
ACK, ACKing both in-order segments
immediately send duplicate ACK,
indicating seq. # of next expected byte
immediate send ACK, provided that
segment starts at lower end of gap](https://image.slidesharecdn.com/lec6-191115071239/75/Lec6-39-2048.jpg)
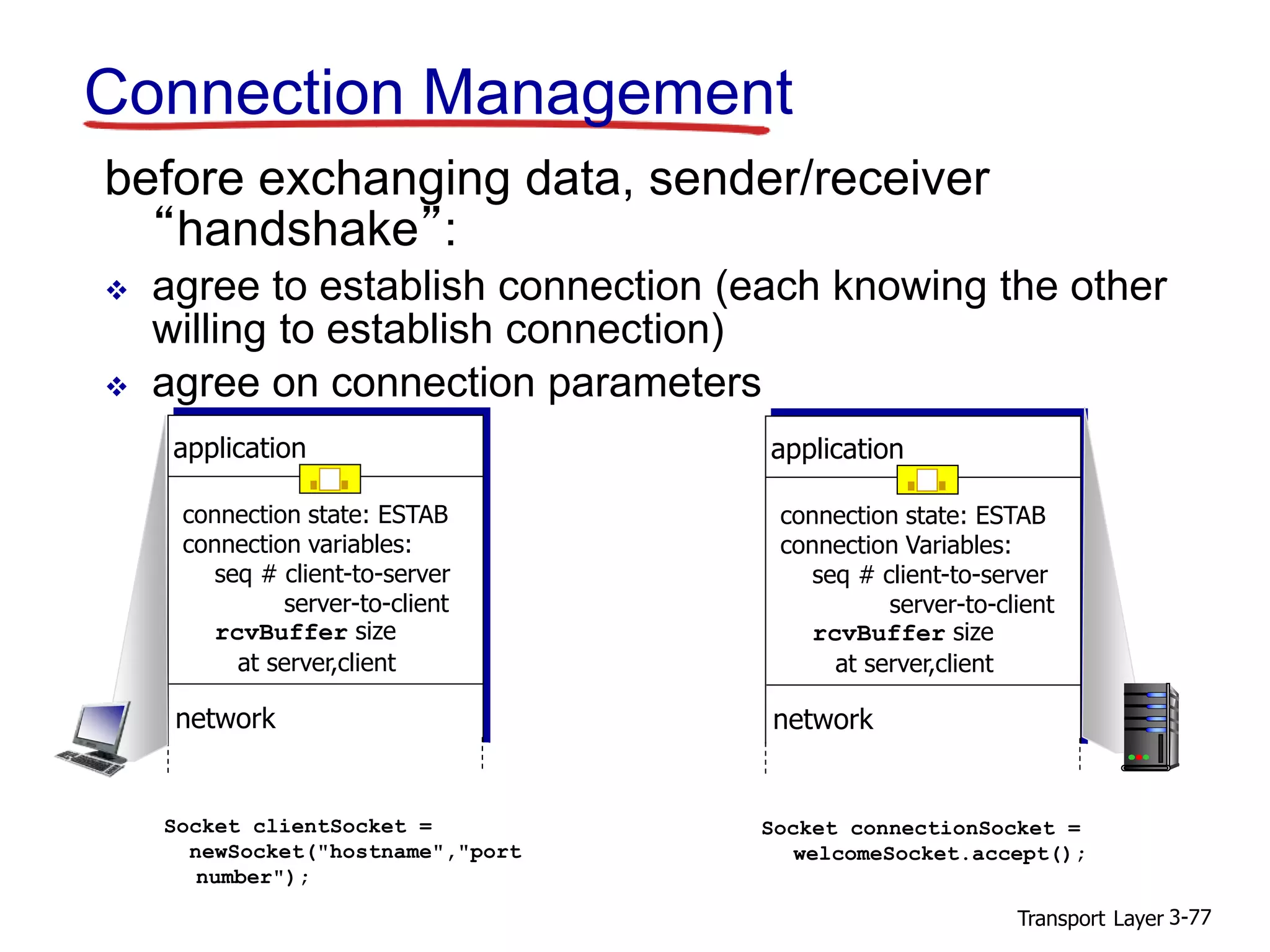
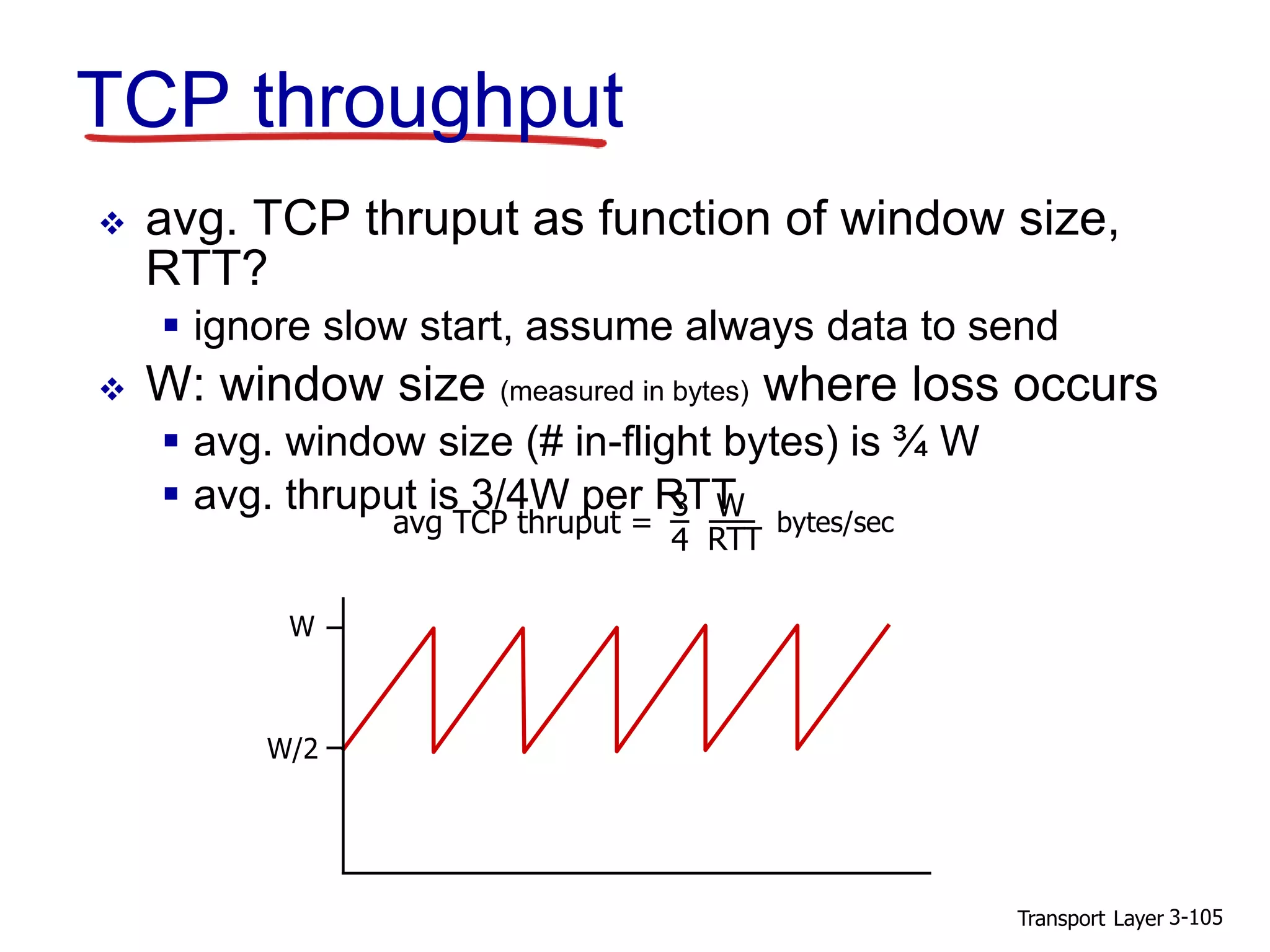
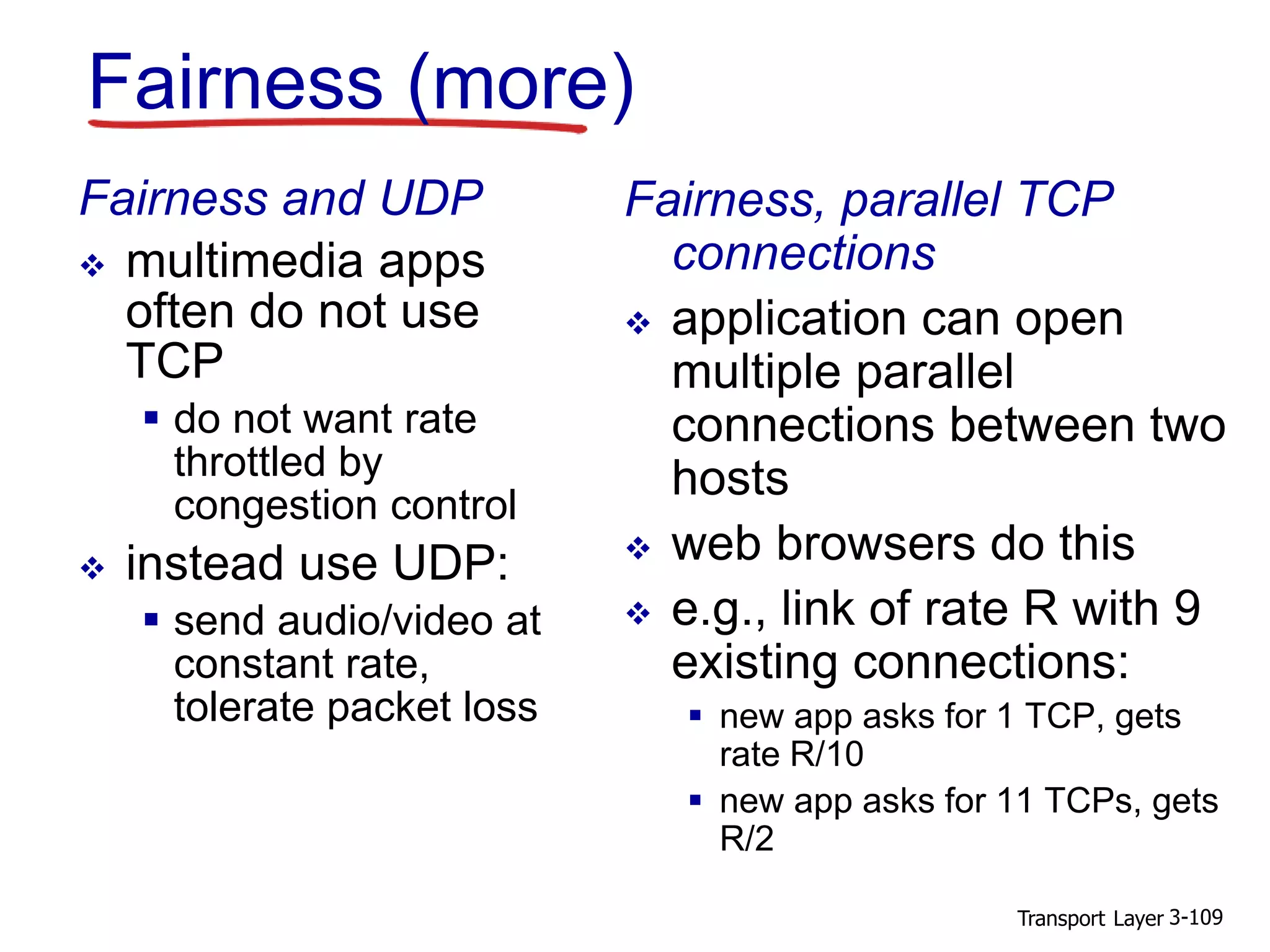
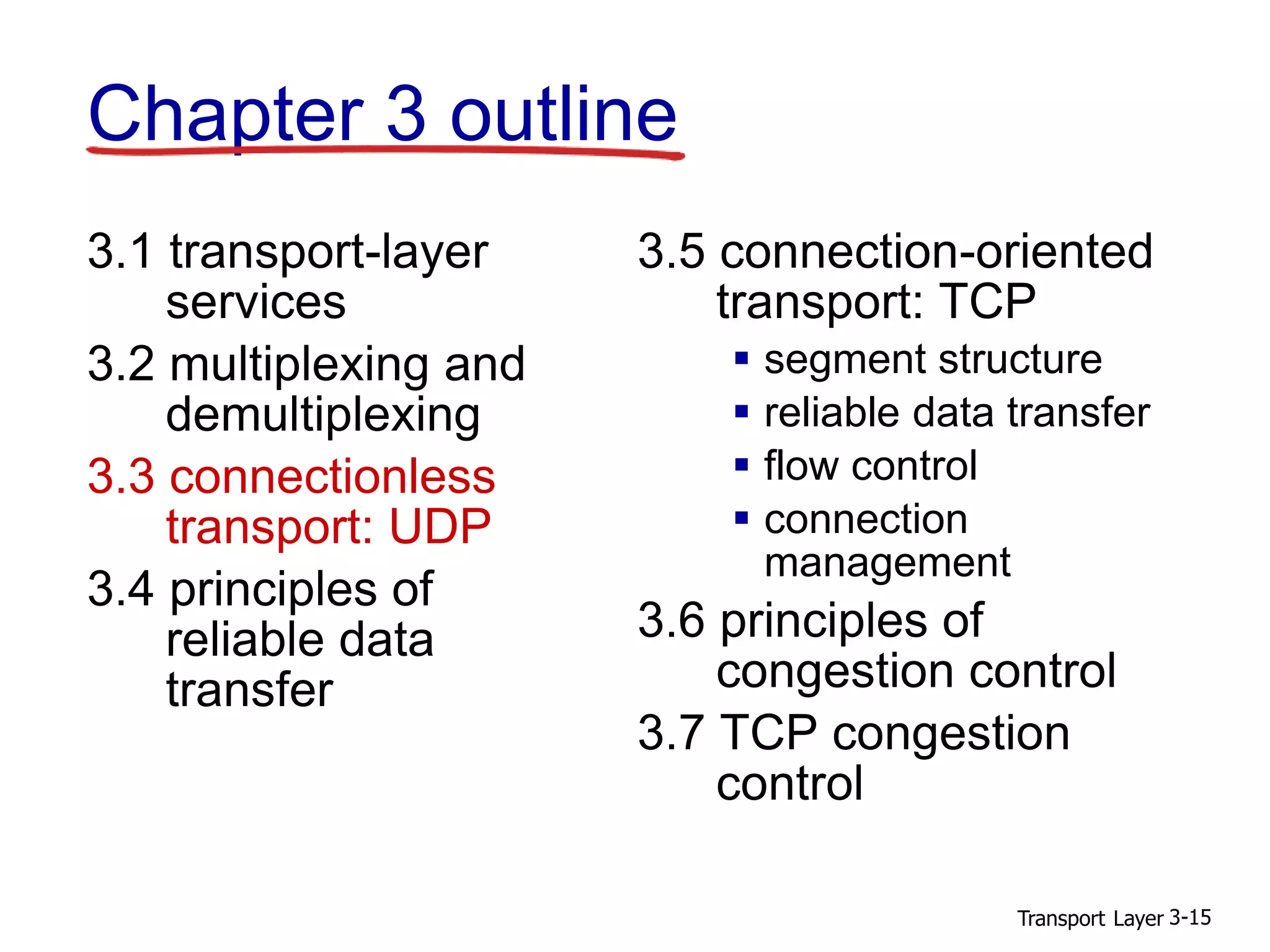
![Transport Layer 3-106
TCP Futures: TCP over “long, fat
pipes”
example: 1500 byte segments, 100ms RTT,
want 10 Gbps throughput
requires W = 83,333 in-flight segments
throughput in terms of segment loss
probability, L [Mathis 1997]:
➜ to achieve 10 Gbps throughput, need a loss rate
of L = 2·10-10 – a very small loss rate!
new versions of TCP for high-speed
TCP throughput =
1.22 . MSS
RTT L](https://image.slidesharecdn.com/lec6-191115071239/75/Lec6-57-2048.jpg)