language.pptx
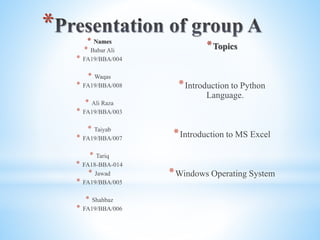
- 1. * * Names * Babar Ali * FA19/BBA/004 * Waqas * FA19/BBA/008 * Ali Raza * FA19/BBA/003 * Taiyab * FA19/BBA/007 * Tariq * FA18-BBA-014 * Jawad * FA19/BBA/005 * Shahbaz * FA19/BBA/006 *Topics *Introduction to Python Language. *Introduction to MS Excel *Windows Operating System
- 2. Python is a widely used general-purpose, high level programming language. It was initially designed by Guido van Rossum in 1991 and developed by Python Software Foundation. It was mainly developed for emphasis on code readability, and its syntax allows programmers to express concepts in fewer lines of code. Python is a programming language that lets you work quickly and integrate systems more efficiently. There are two major Python versions- Python 2 and Python 3. Both are quite different. *
- 3. • Beginning of the Python Language: • Before starting python language we need an interpreter to interpret and run the program. • Linux is the best interpreter for python language as it comes bundled with the python language. • Example with a program: • # Script Begins • • print(“PAKISTAN") • • # Scripts Ends • Let us analyze the script line by line. • Line 1 : [# Script Begins] In Python language comments begin with #. • Line 2 : [print(“PAKISTAN”)] In a Python script to print something on the console print() function is used – it simply prints out a line. And its also includes a new line. • Line 3 : [# Script Ends] This is just another comment like Line 1.
- 4. *Features of Python Language: * 1) Easy to Learn and Use * Python is easy to learn and use. It is developer-friendly and high level programming language. * 2) Expressive Language * Python language is more expressive means that it is more understandable and readable. * 3) Interpreted Language * Python is an interpreted language i.e. interpreter executes the code line by line at a time. This makes debugging easy and thus suitable for beginners. * 4) Cross-platform Language * Python can run equally on different platforms such as Windows, Linux, Unix and Macintosh etc. So, we can say that Python is a portable language. * 5) Large Standard Library * Python has a large and broad library and provides rich set of module and functions for rapid application development. * 6) GUI Programming Support * Graphical user interfaces can be developed using Python. * 7) Integrated * It can be easily integrated with languages like C, C++, JAVA etc. * 8) Extensible * It implies that other languages such as C/C++ can be used to compile the code and thus it can be used further in our python code.
- 5. Python language elements *Basic data types and containers * Python has several basic data types and containers. Becoming familiar with them is essential to effective use of Python, and is a good starting point for learning Python. *Variable names and assignment * Python variable names are case-sensitive and start with a letter or an underscore. A leading underscore may be used by convention to indicate a variable *Functions * When programs get too complex, they are likely to be full of bugs and hard to maintain. The most fundamental construct for keeping complexity under control is the function. *Exceptions and tracebacks * Exceptions are part of a program flow control mechanism that is specially designed for handling errors or other “exceptional conditions”, but that can be used more generally. A traceback is the error report from an uncaught exception, showing the chain of function calls leading to the exception. *Functions * When programs get too complex, they are likely to be full of bugs and hard to maintain. The most fundamental construct for keeping complexity under control is the function. *Exceptions and tracebacks * Exceptions are part of a program flow control mechanism that is specially designed for handling errors or other “exceptional conditions”, but that can be used more generally. A traceback is the error report from an uncaught exception, showing the chain of function calls leading to the exception.
- 7. *
- 8. Microsoft Excel interface Excel interface is very simple and efficient. It provides methods for carrying out tasks with minimum clicks of the mouse. It provides the ways to work with the keyboard. Elements of excel interface Worksheet: Worksheet is where you enter all your data. Worksheet is made up of rows and columns. Rows are labeled with numbers and columns are labeled with letters. Workbook: Workbook is a group of worksheets saved together as one excel file. Each workbook in excel contains 3 worksheets. The first sheet is called sheet 1 and so on.. . Active cell: Active cell is used to tell excel where you want to enter or edit data. Title bar: It is located at the very top of the screen . It displays the name of the current work book on it. Menu bar: Menus vary program to program. Menu commands are used to moving, saving, erasing, printing, saving, and changing the appearence of data etc. Toolbars: Toolbars provide shortcuts to. Menu commands. Toolbars are located just below the menu bar. It consist of icons that act as shortcuts to the commands. Toolbar that appears below menu bar is called standard toolbar.
- 9. *Formula bar: * This bar displays the location of the active cell and the value or formula used in the active cell. *Cell: Intersection of row and column is call cell. Cell holds data. Cell may contain text, numbers, and even graphical patterns. * Cell Address: Cells are identified by combination of their column letter and row number. * Sheet Tabs: Sheet tabs at the bottom of the workbook. Sheet tabs are used to move from one sheet to another in a workbook. * Status bar: It appears at the bottom of excel interface. It displays information about a command, a toolbar icon or an operation in programs Smart tags: * Smart tags appears when the user makes an entry and Microsoft excel believes the user may want to change. * Smart tags provide the facility to make changes easily.
- 11. *
- 12. * *About Windows XP * Windows XP is developed by Microsoft. * It was released in 2001. * XP stands for experience. * Easier to use * Available in different versions such as XP Home, XP Professional, and XP Media Centre. * Windows XP Professional is often used in business environment and by home. * The media Centre is built on XP Professional. *Features of Windows XP *New user interface: * Provides a new user interface with different visual style. Desktop and taskbar are more attractive and easier to use. Windows layout and design of start menu is also changed. *Easier to use: *Provides an easier way to work with files and folders. It saves all files in My Documents folder on desktop by default. It also manage a recently used files for quick access later. * Easier to manage * Multitasking
- 13. *Multi-User: * It means that many users can use the computer at a same time. These users can be connected to a computer over the internet. *Clean Desktop Wizard: * By default, the desktop cleanup Wizards runs every sixty days. It cleans-up desktop by moving unused desktop shortcuts to a folder called unused desktop shortcuts. *Networking: * It provides the facility to establish, maintain and troubleshoot a network. *Multiprocessing: * Multiprocessing is the capability to support and utilize multiple processors in a computer. Two or more processors can execute different programs at the same time . It increase the output of the computer. *System restore: * It is used to restore operating system in case of any problem. The operating system is restored to a previous state without any loss of data. *Latest Hardware Support: * Includes the latest drivers to support latest advancements in computer hardware technology. *Task panel: * It provides an easy way to access the most commonly used folder tasks. The task panel displays a list of hyperlink task to the left of the folder contents. For example, My pictures and My music folders provide links to manage pictures and music files.
- 14. *Windows Desktop * On-screen work area that contain windows, icons, menus and dialog boxes is called desktop. * Desktop is the entering point in Windows. * Desktop is the first object that appears when Windows is started. * The user can also change the look of the desktop. Icons on Desktop My Document My Computer My Network Places Recycle Bin Internet Explorer Elements of Desktop Icons: An icon is a small graphic that represent a program, drive, folder or document. Some important icon that appear on Desktop are My Computer, My Document etc. Taskbar: Taskbar is located on bottom of the desktop and it consist of start button and some elements in the right side. Start button It is used to access different programs installed in the computer.