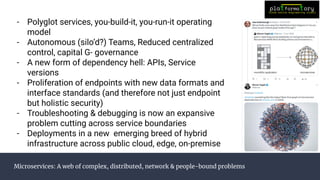
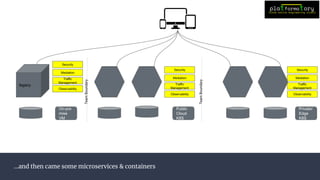
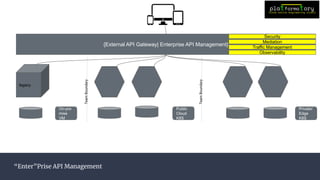
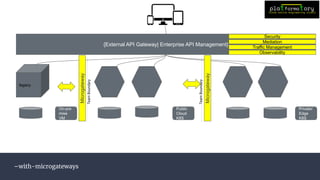
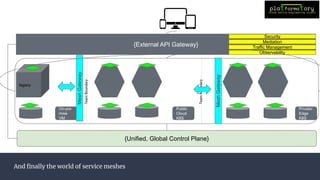
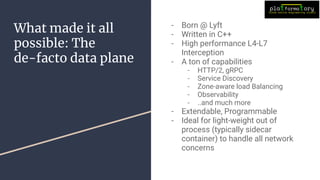
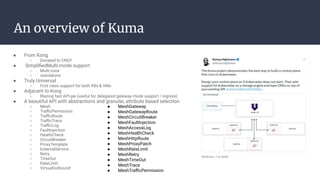
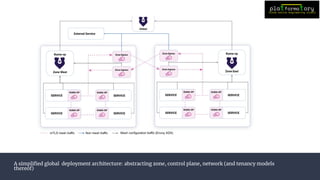
The Kuma workshop at the Kong meetup on February 23, 2023, covered essential topics related to service mesh technology, including its landscape, zero trust security, traffic routing, and observability. The session featured demonstrations of Kuma's capabilities such as installation, canary deployments, and traffic mirroring. It emphasized the evolution of microservices, the complexities involved, and provided insights into the architecture and deployment strategies for modern applications.