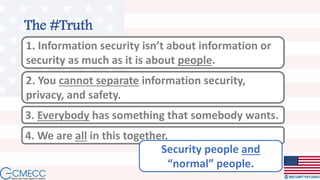
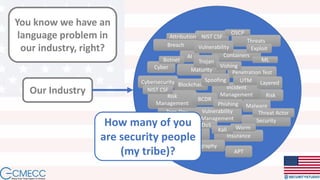
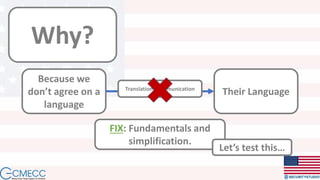
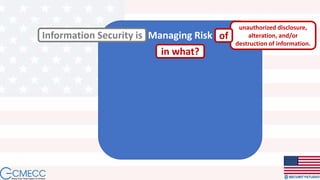
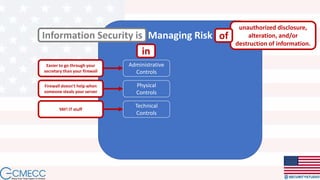
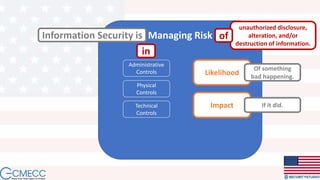
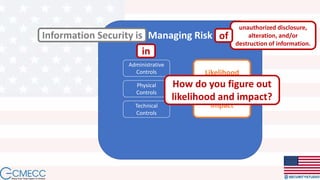
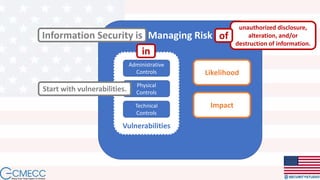
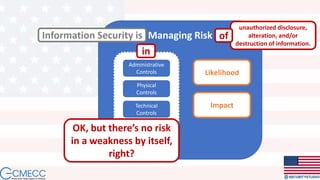
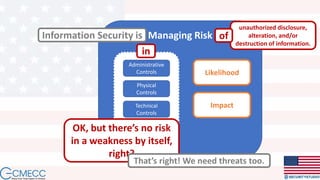
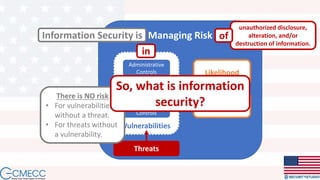
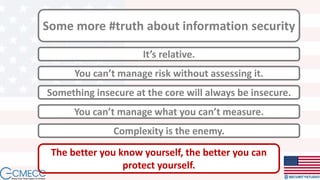
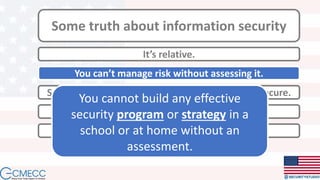
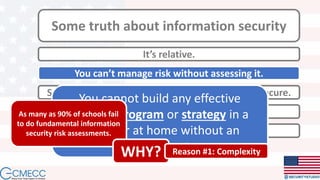
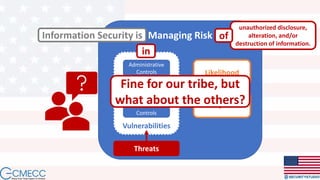
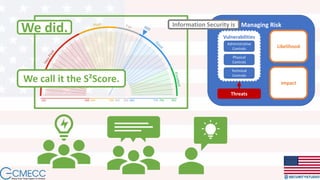
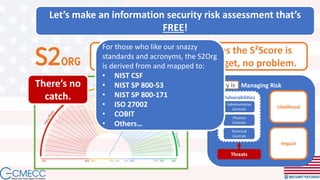
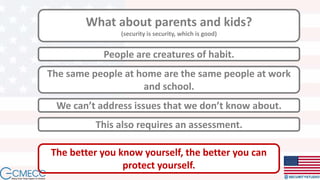
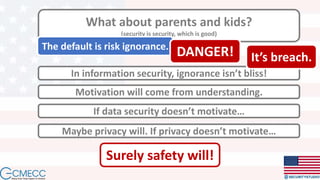
Evan Francen, CEO of SecurityStudio, discusses the state of information security, highlighting its failure to effectively protect individuals, particularly in schools. He emphasizes the importance of assessing risks and simplifying communication around security issues, introducing the concept of the S2Score as a tool for schools to evaluate their security posture for free. The document advocates for engagement from parents and students to improve security awareness and practices in both educational and home environments.