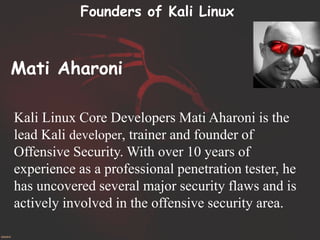
Kali Linux is a specialized operating system designed for penetration testing and security auditing, featuring over 300 tools and developed by Offensive Security. Key tools include Metasploit for backdooring, SQLMap for database exploitation, and Aircrack for wireless network attacks. In contrast to Ubuntu, which serves general desktop purposes, Kali is tailored for professionals in cybersecurity and digital forensics.