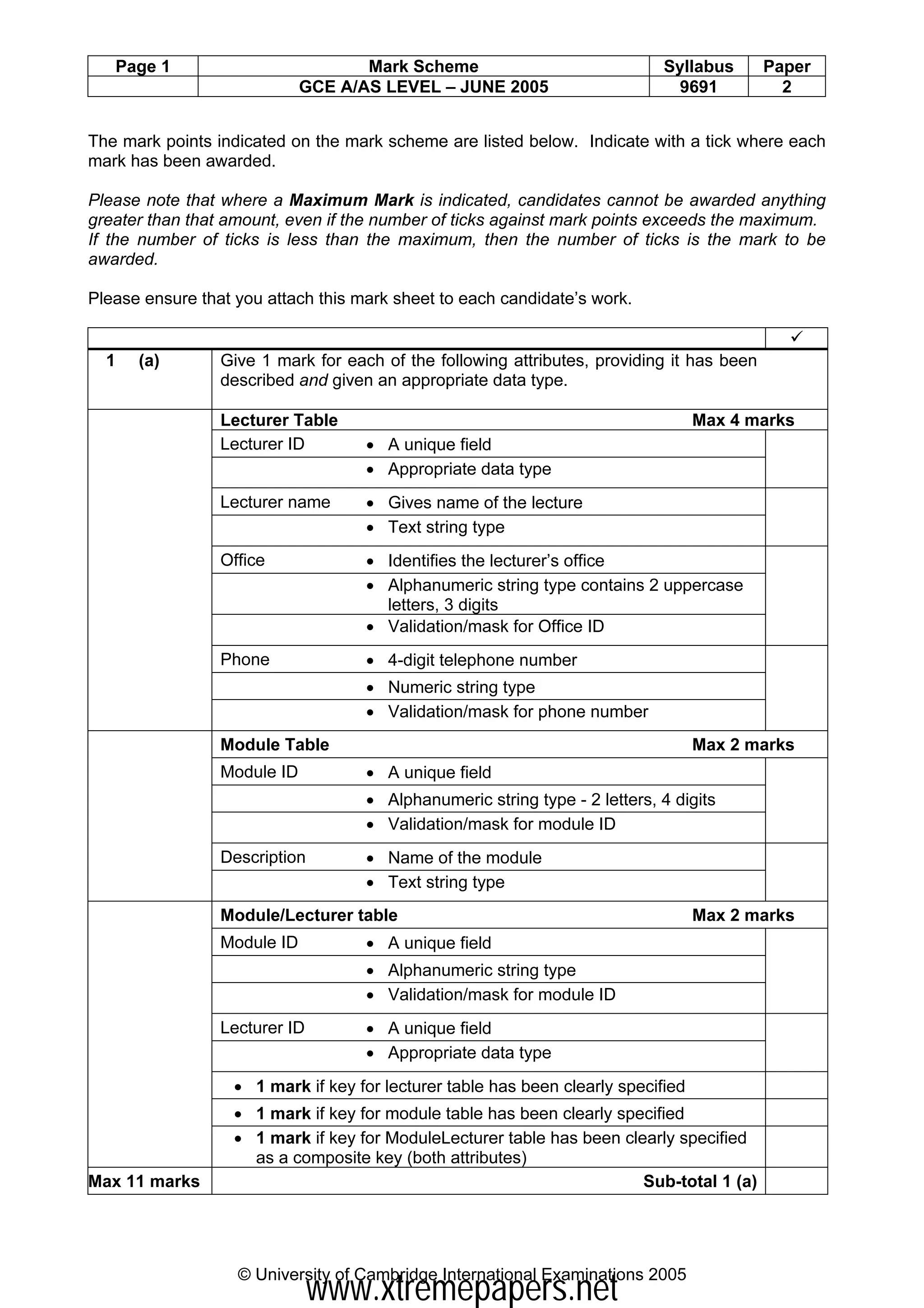
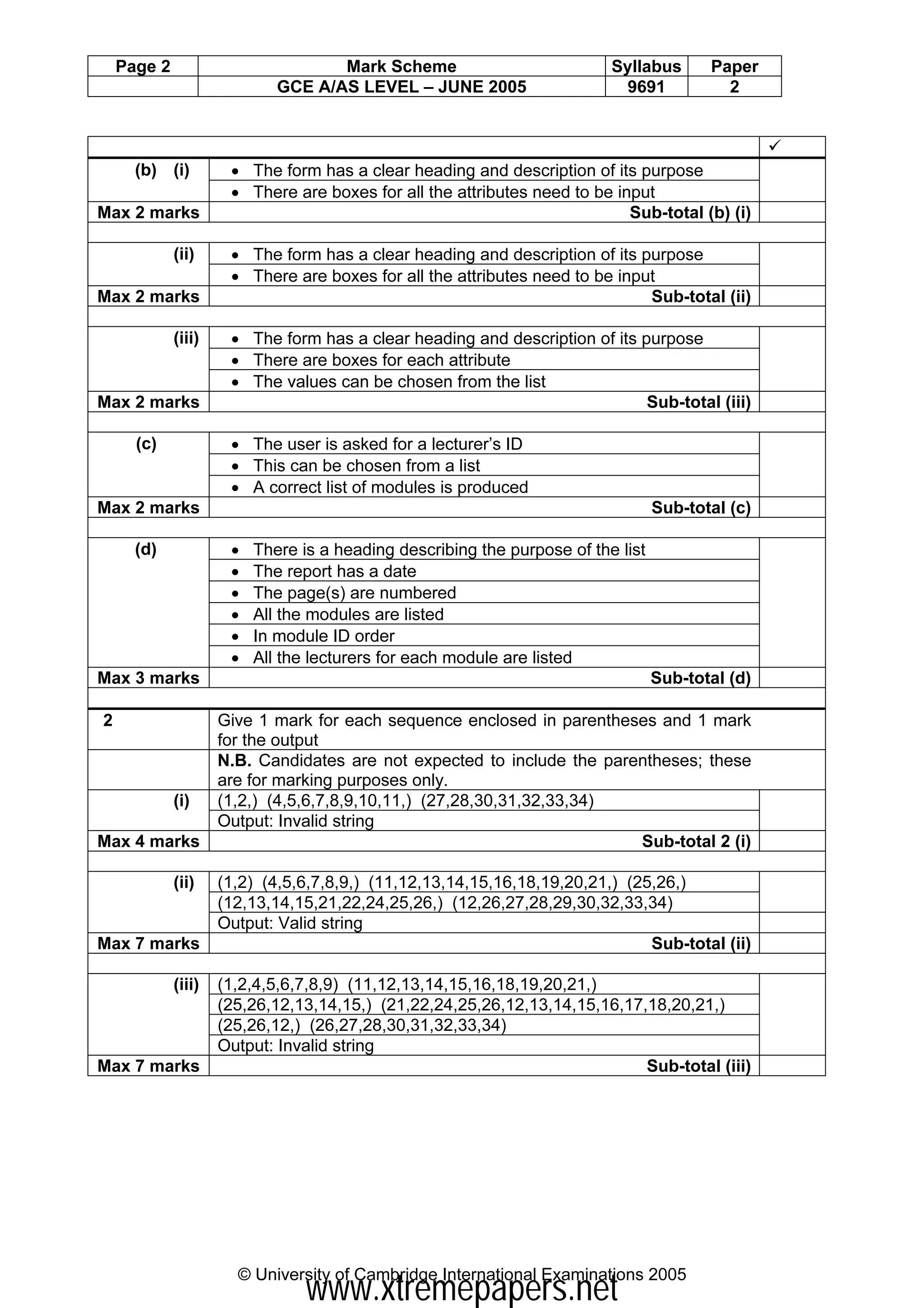
The document provides a mark scheme for the June 2005 computing exam for GCE Advanced Subsidiary Level and Advanced Level. It outlines the requirements and expectations for awarding marks to exam questions and practical tasks. Key points include providing marks for describing database attributes and validation, creating forms to enter and display data, validating strings of binary numbers, and functions to convert between binary and decimal numbers. Examiners are instructed to award marks that fairly reflect the knowledge and skills demonstrated in candidates' responses, even for unexpected correct answers.