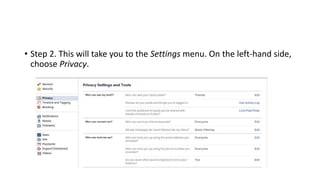
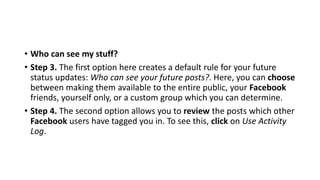
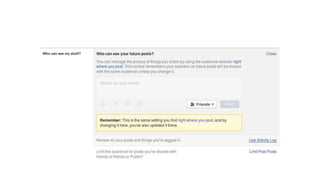
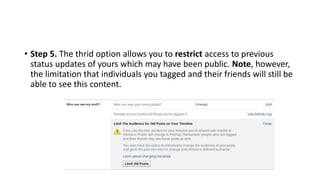
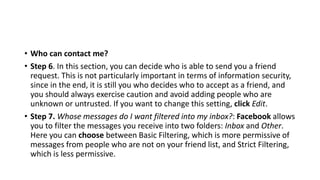
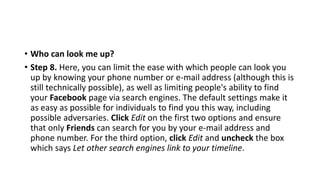
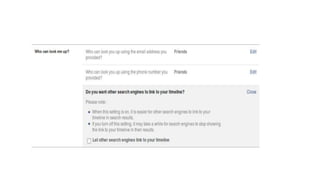
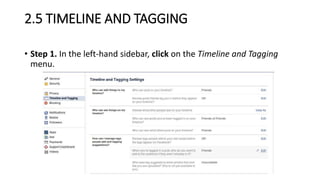
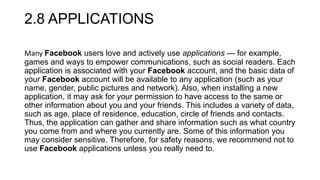
The document provides guidance on selecting and securing a social networking platform. It recommends carefully reviewing privacy policies to understand how personal data is used and shared. It also suggests choosing privacy settings that allow sharing only with close contacts, and being aware of a platform's server locations and compliance with government data requests. Location of servers and compliance with government requests impact privacy and security.