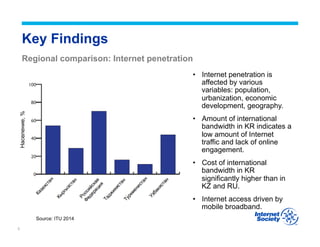
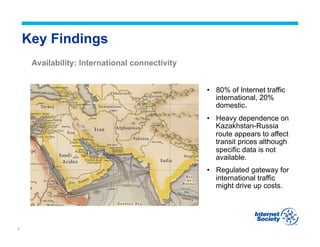
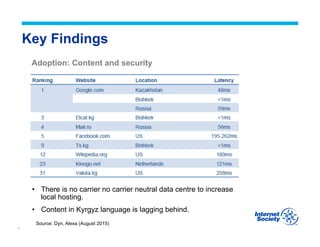
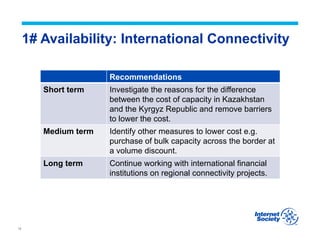
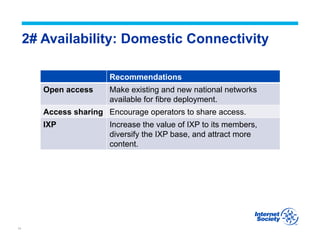
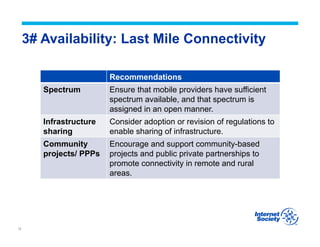
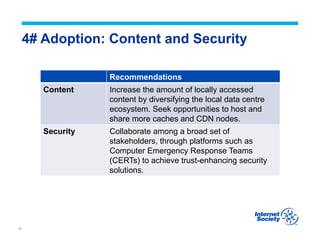
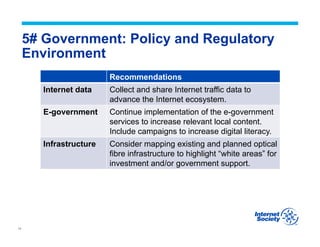
The document summarizes the findings of an assessment of the Kyrgyz internet environment. It finds that internet penetration is affected by factors like population and economic development. International bandwidth is low and costs are high compared to neighboring countries. The internet is driven by mobile broadband with limited domestic connectivity. It provides recommendations in 5 areas - lowering international connectivity costs, improving domestic connectivity through infrastructure sharing, increasing last mile connectivity through spectrum and rural projects, growing local content and data security, and improving data collection, e-government, and infrastructure mapping to support policy.