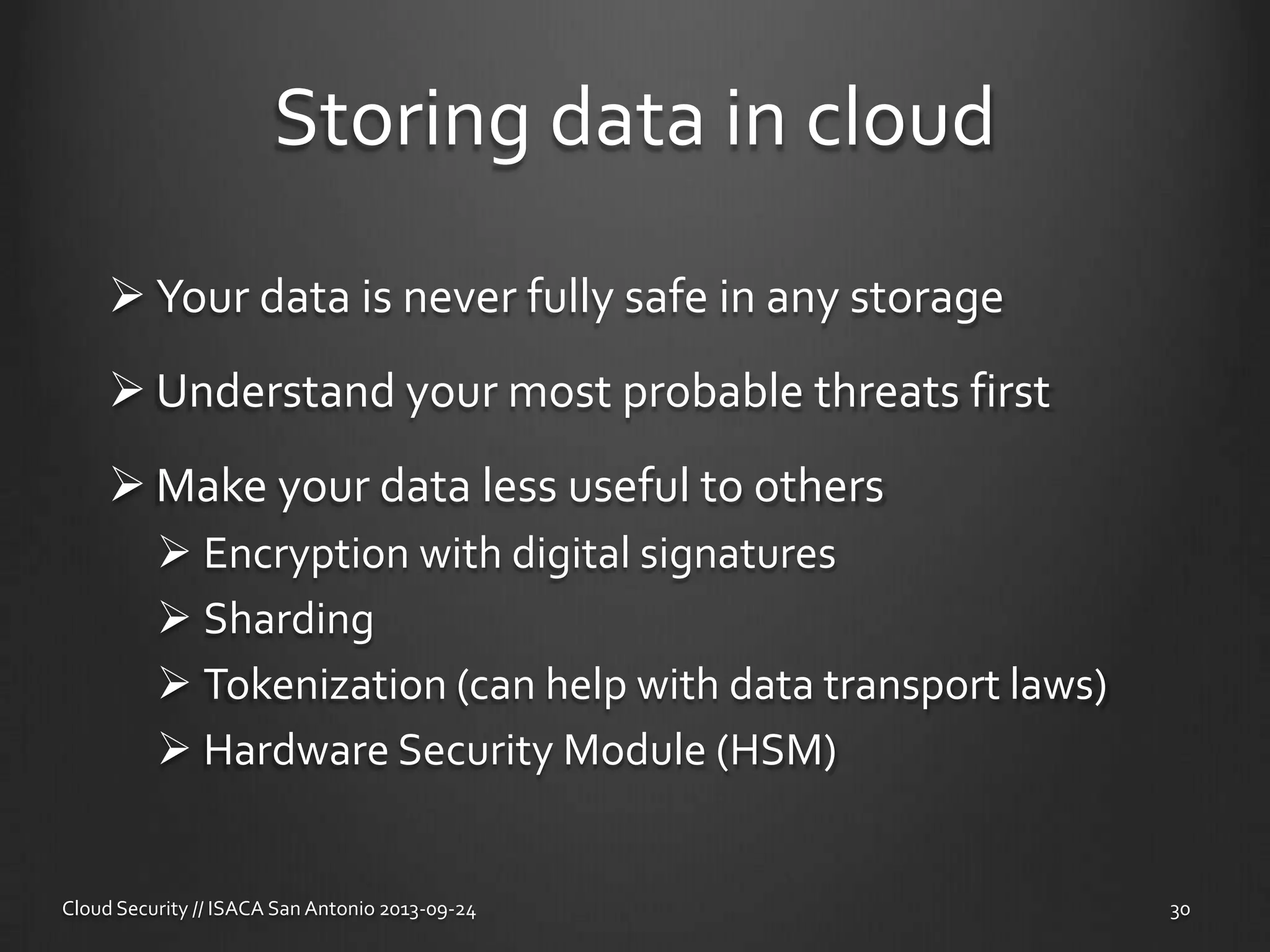
Major Hayden is a chief security architect at Rackspace who has over 5 years of experience in cloud operations. In his presentation, he discusses cloud hosting and the shift from managing computers to utilizing computing resources. He outlines the different types of cloud deployments including public, private, and hybrid clouds. Hayden also addresses common security questions about selecting cloud providers, contractual agreements, risks of company-owned servers, public cloud networking risks, and securely storing data in the cloud.