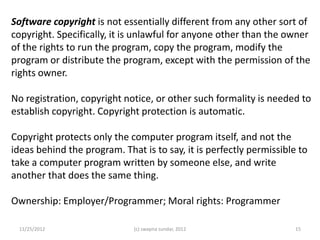
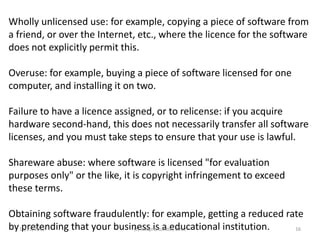
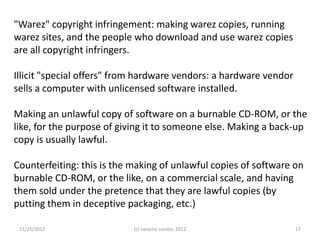
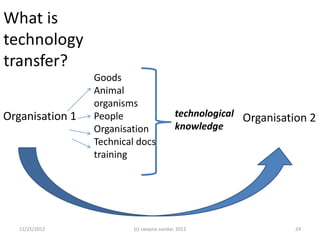
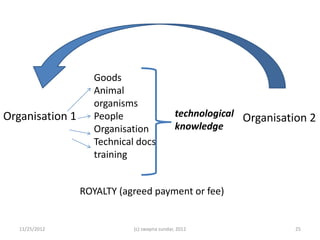
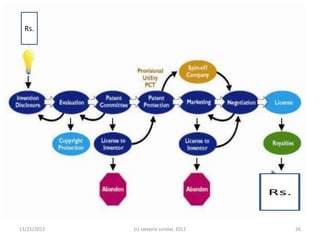
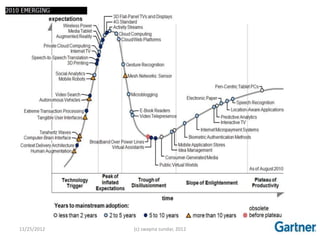
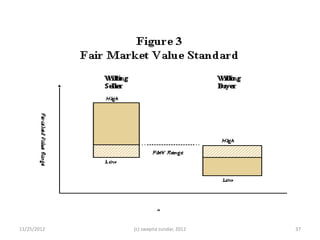
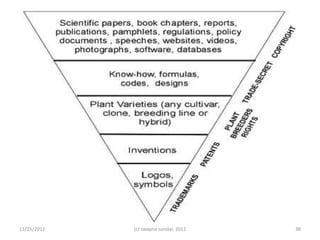
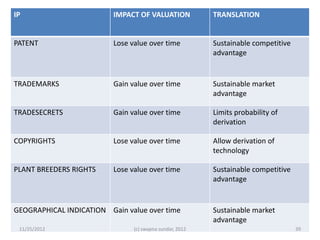
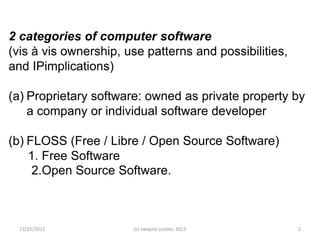
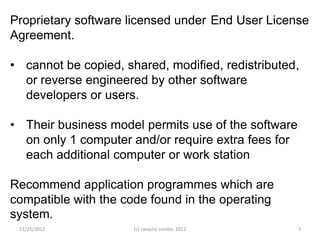
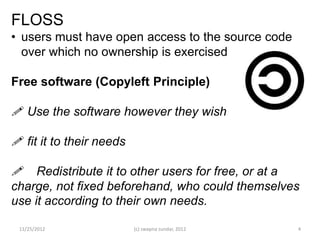
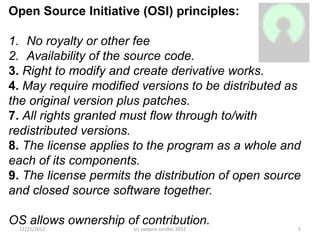
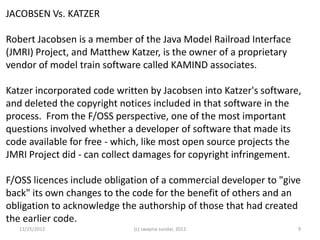
The document discusses various aspects of intellectual property (IP), focusing on the distinction between proprietary software and free/libre/open source software (FLOSS), along with the implications of licensing and copyright. It highlights the legal case of Jacobsen vs. Katzer, showcasing the importance of copyright in software development, and touches on the valuation of IP through different methodologies like market-based, cost-based, and income approaches. Additionally, it addresses challenges in valuing intangible assets and outlines the significance of understanding the purpose and nature of the assets being evaluated.
![In India, a person is entitled to a patent if
1. He is the owner of the invention
2. the invention is the proper subject matter for a patent, and
3. the invention is "useful", "new", and “inventive“
4. The invention should not have been published with some narrow
exceptions
In India, s/w per se is not a patentable subject matter
In re Bilsky: "the invention is not implemented on a specific
apparatus and merely manipulates [an] abstract idea and solves a
purely mathematical problem without any limitation to a practical
application, therefore, the invention is not directed to the
technological arts."
11/25/2012 (c) swapna sundar, 2012 13](https://image.slidesharecdn.com/ipinit-121126003726-phpapp02/85/Ip-in-it-13-320.jpg)