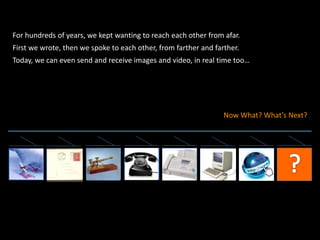
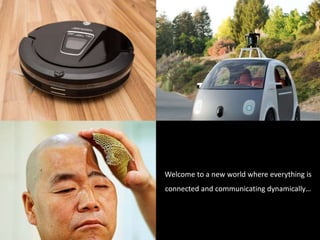
Human communication has evolved from physical interactions to advanced technologies that facilitate connection over distances, highlighting our intrinsic need to communicate. As machines and electronics become integral extensions of our existence, the nature of our communication transforms, blending the physical and digital realms. The concept of the Internet of Things (IoT) represents a new era where everything is interconnected and communicating dynamically.