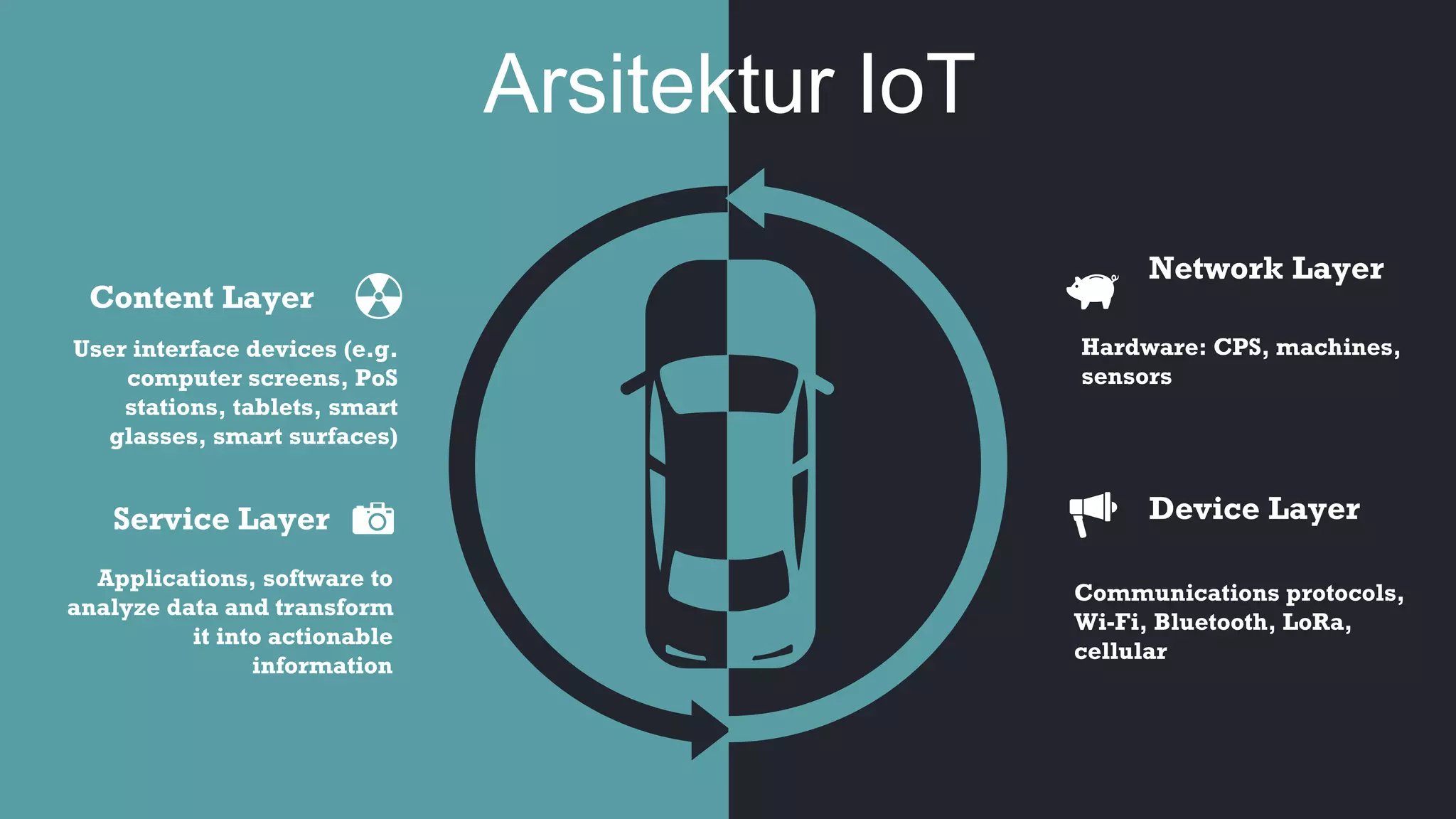
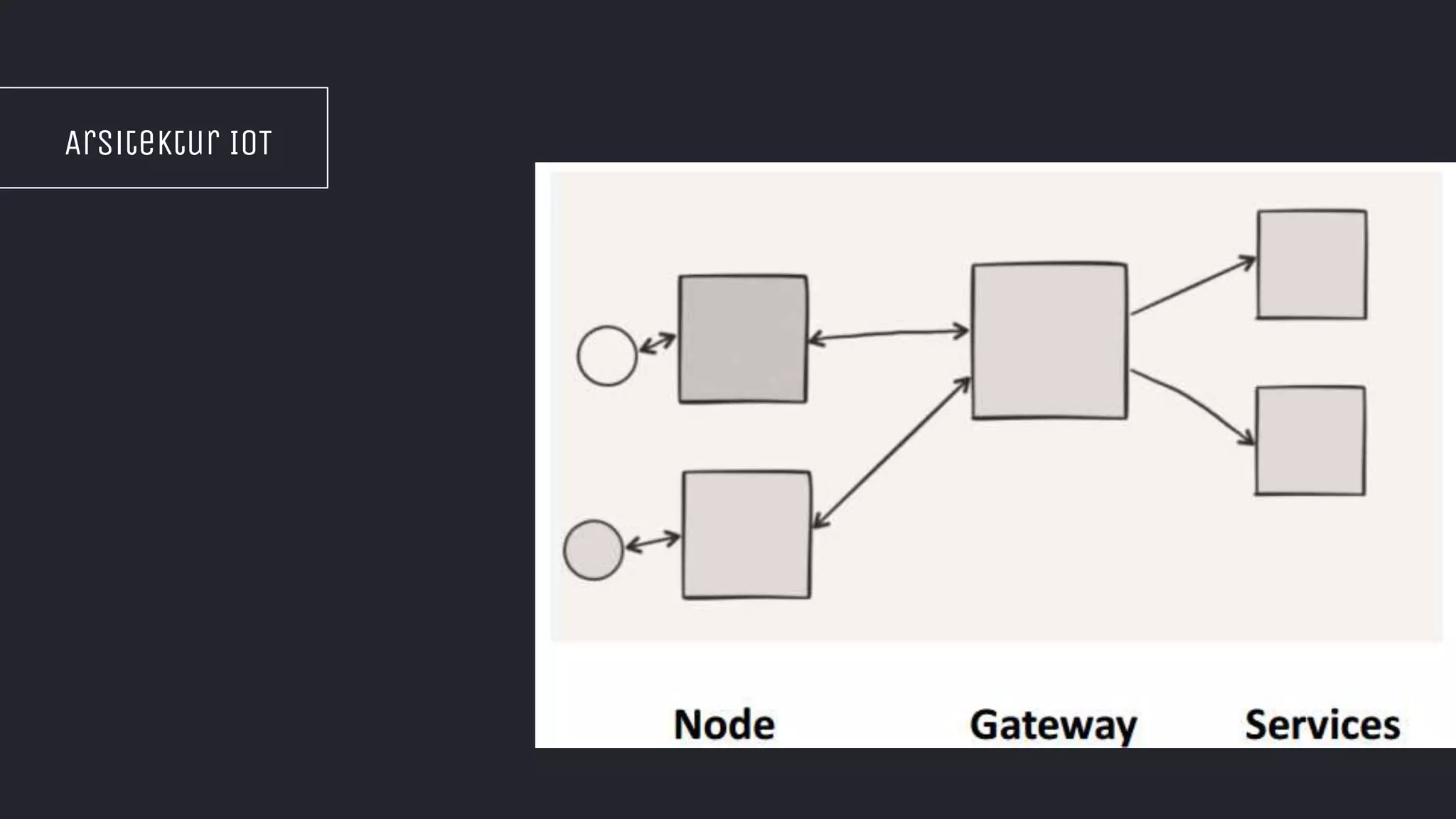
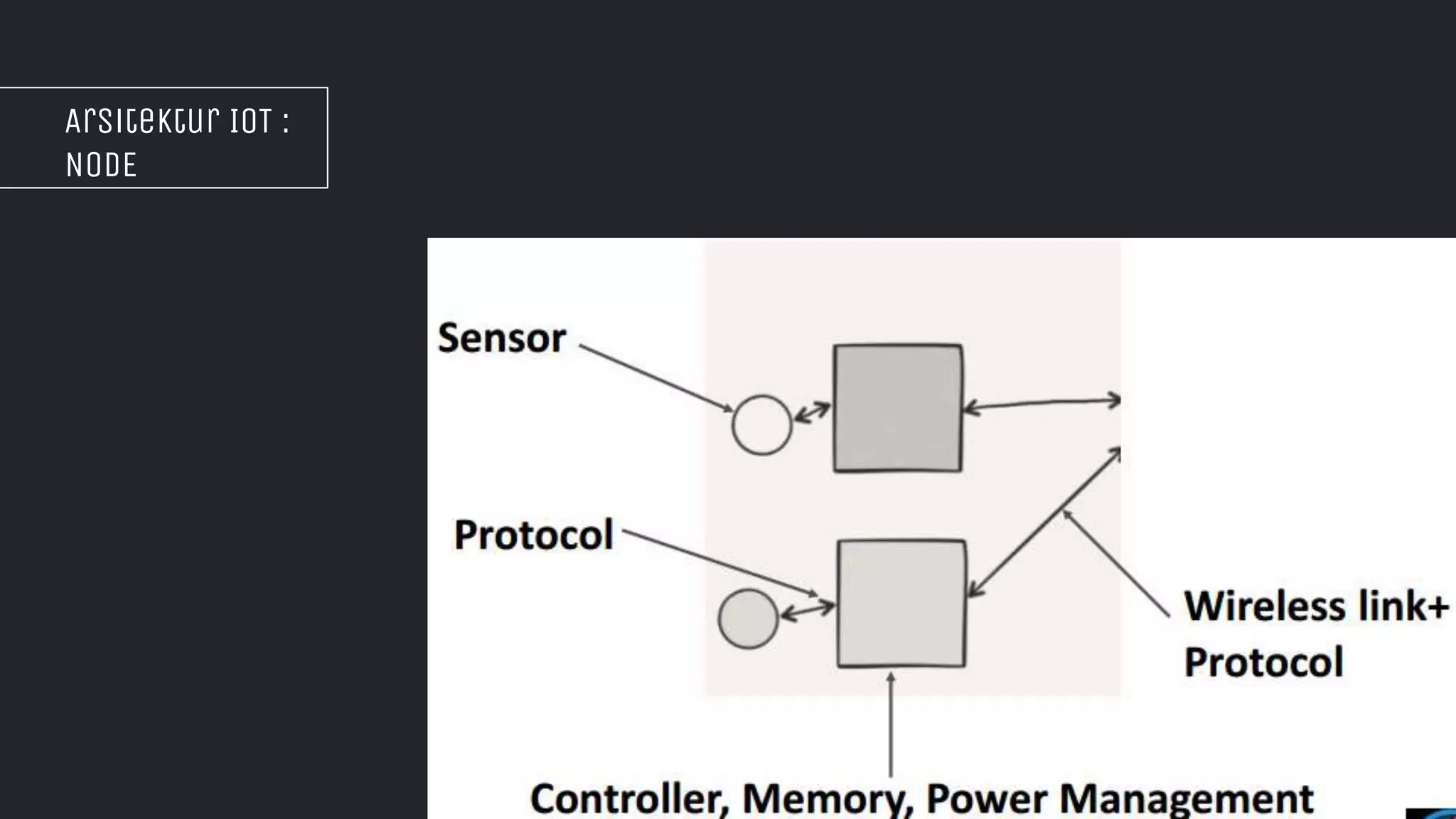
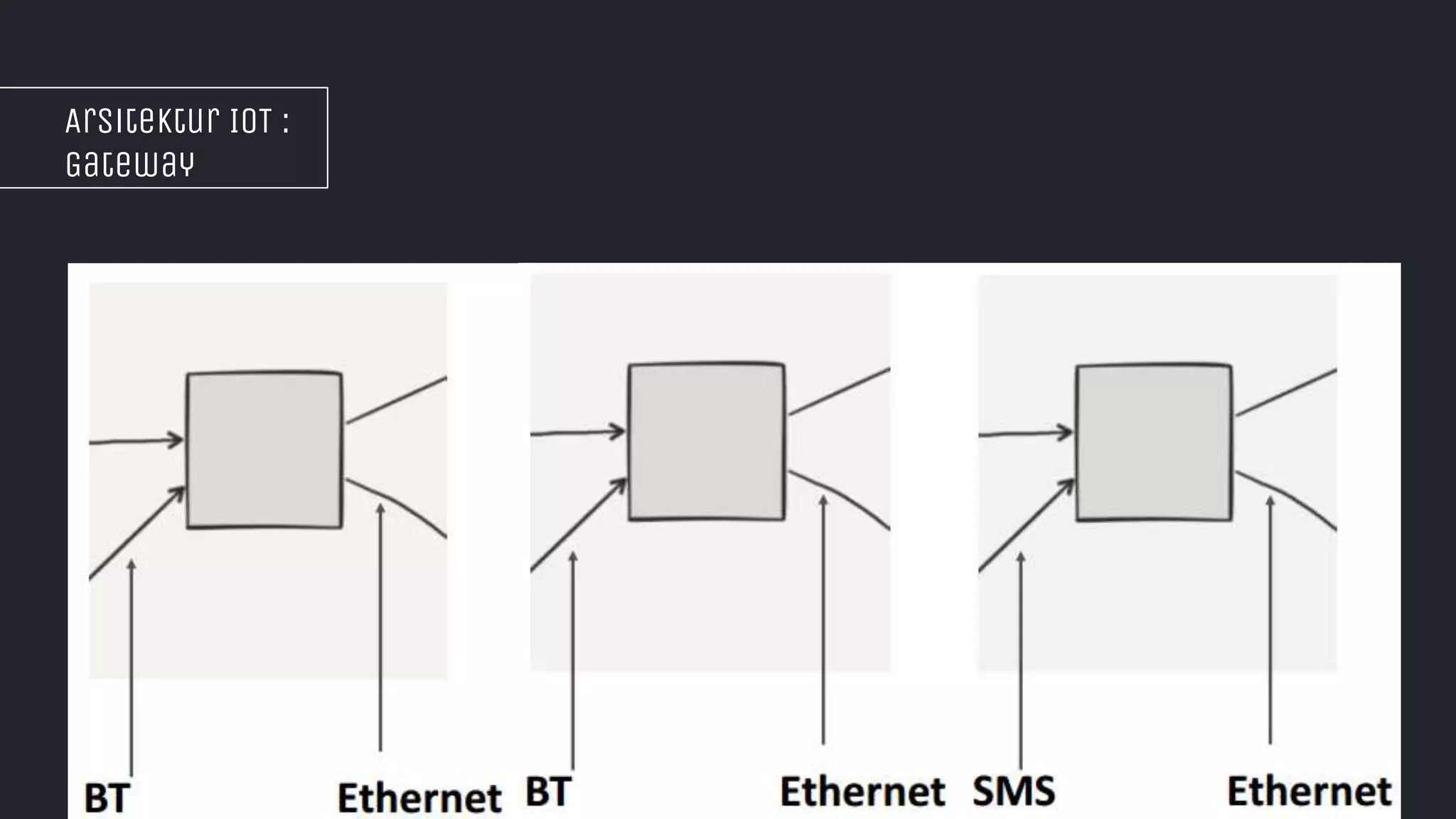
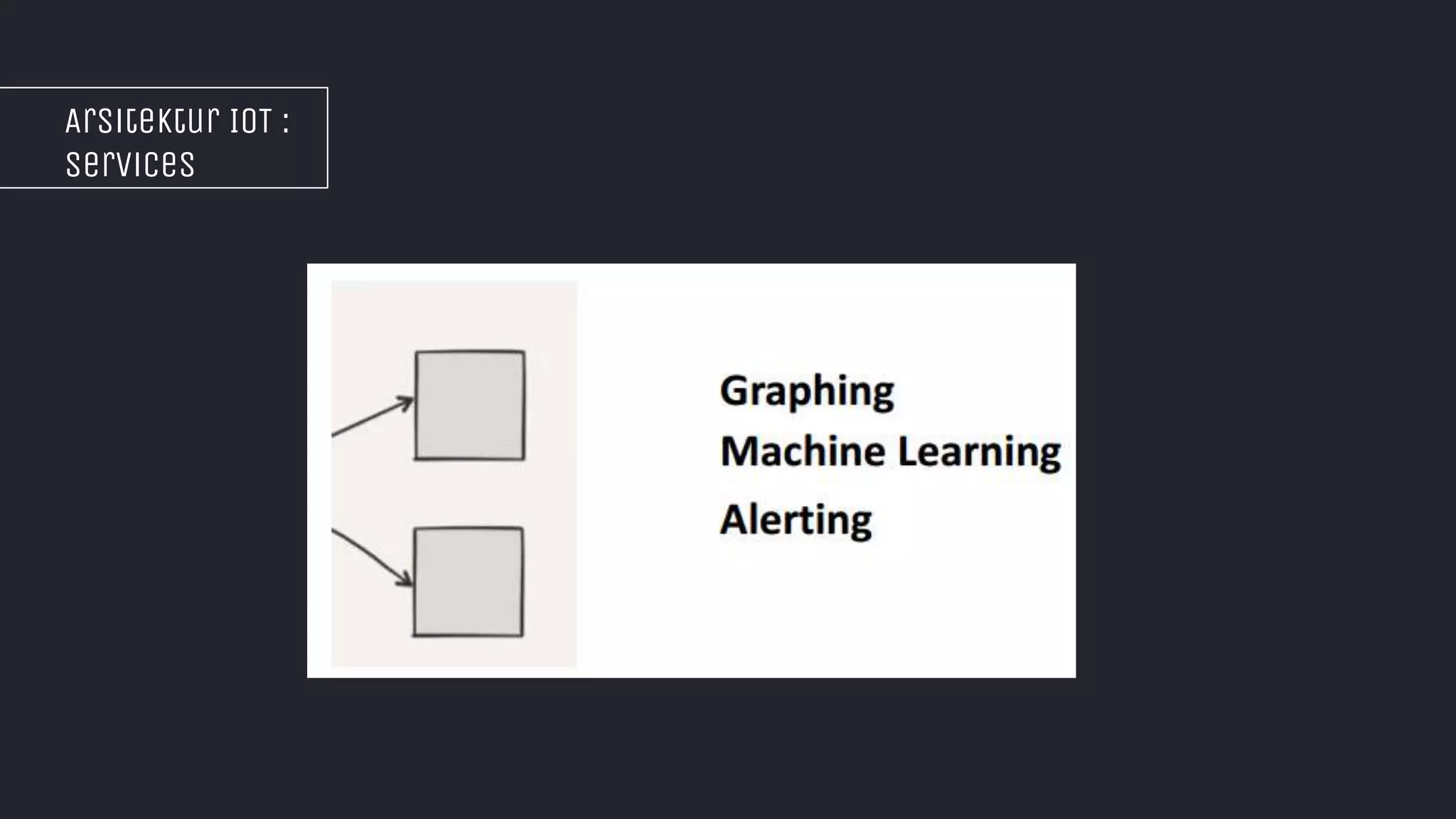
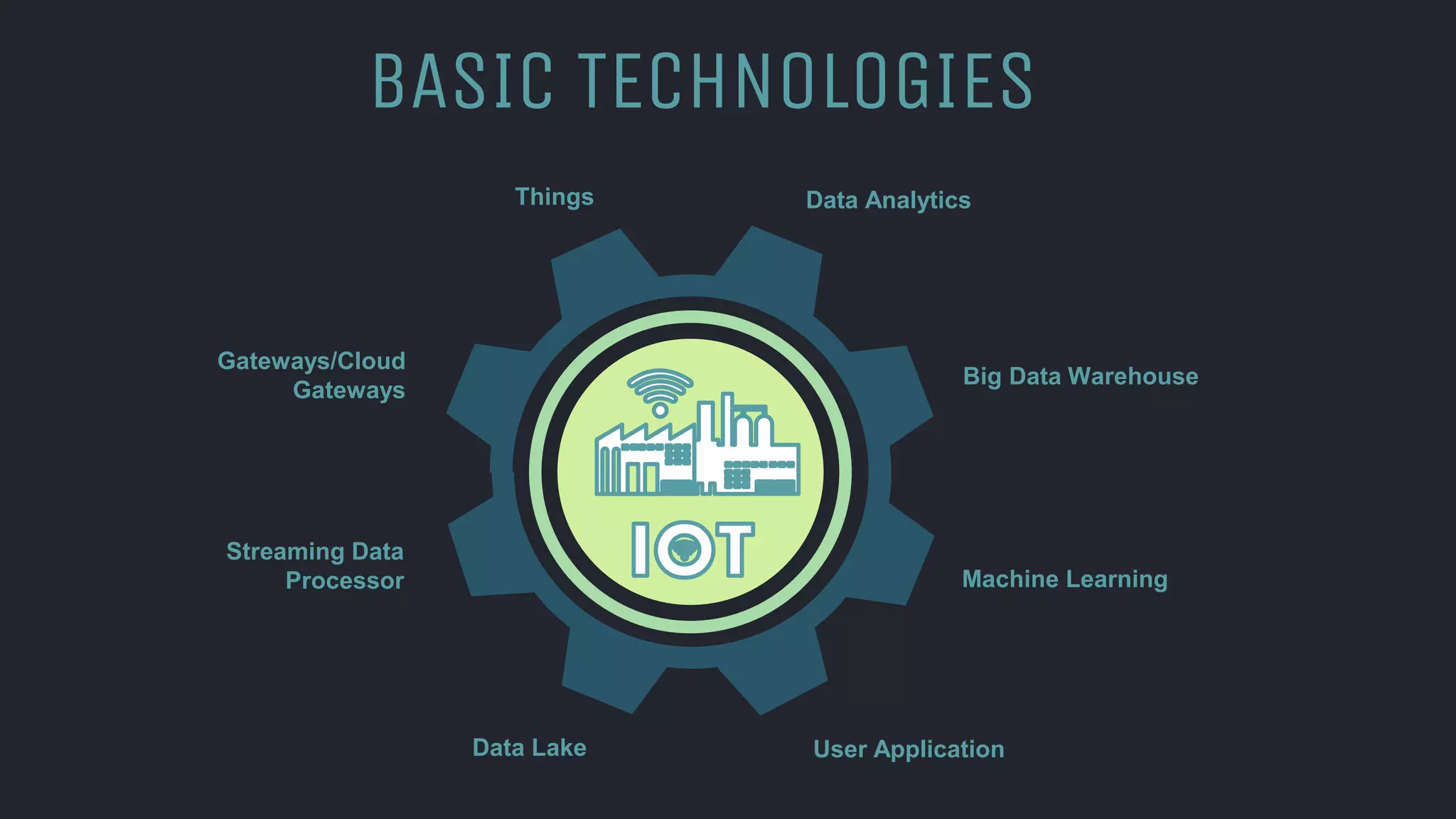
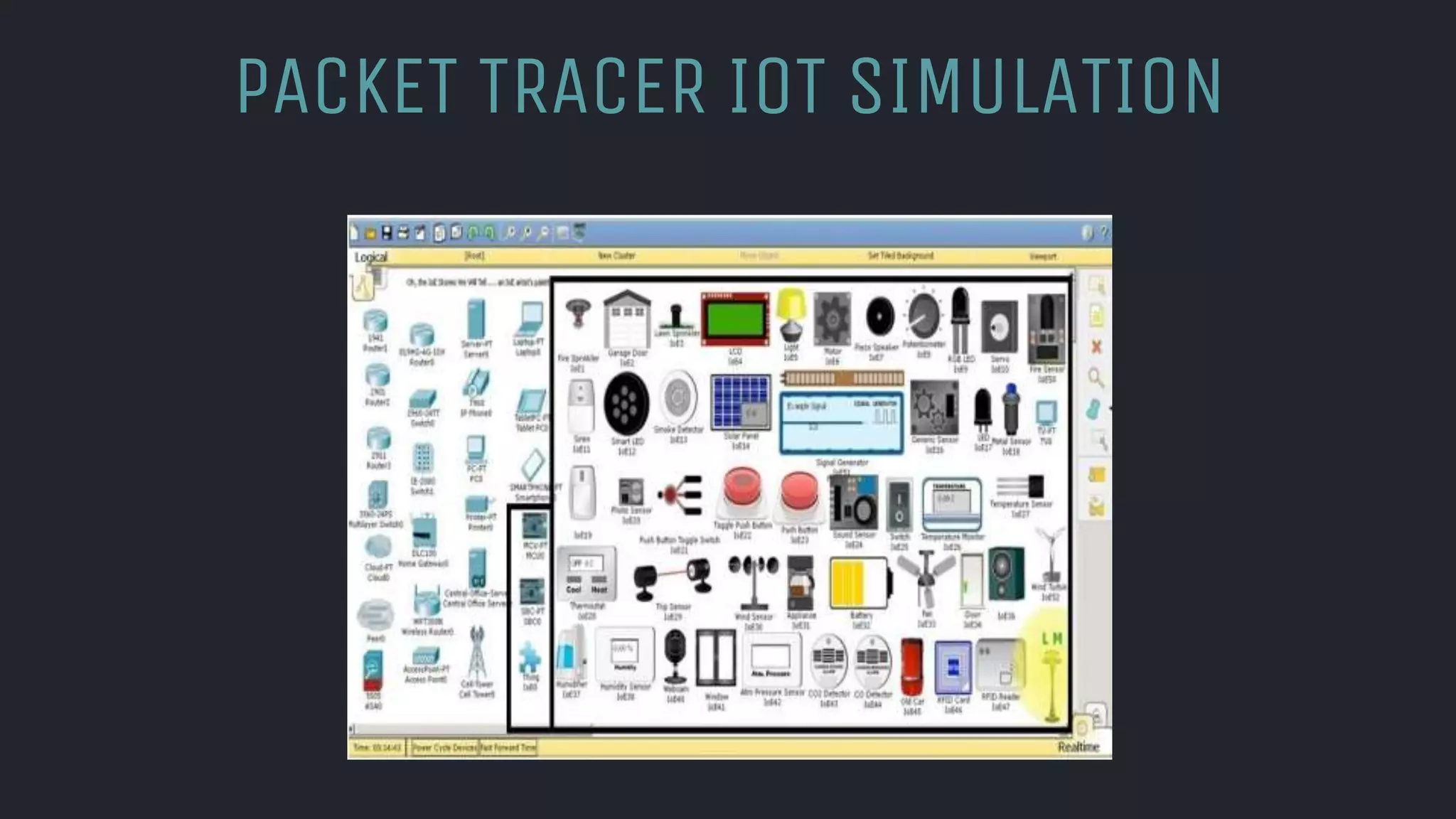
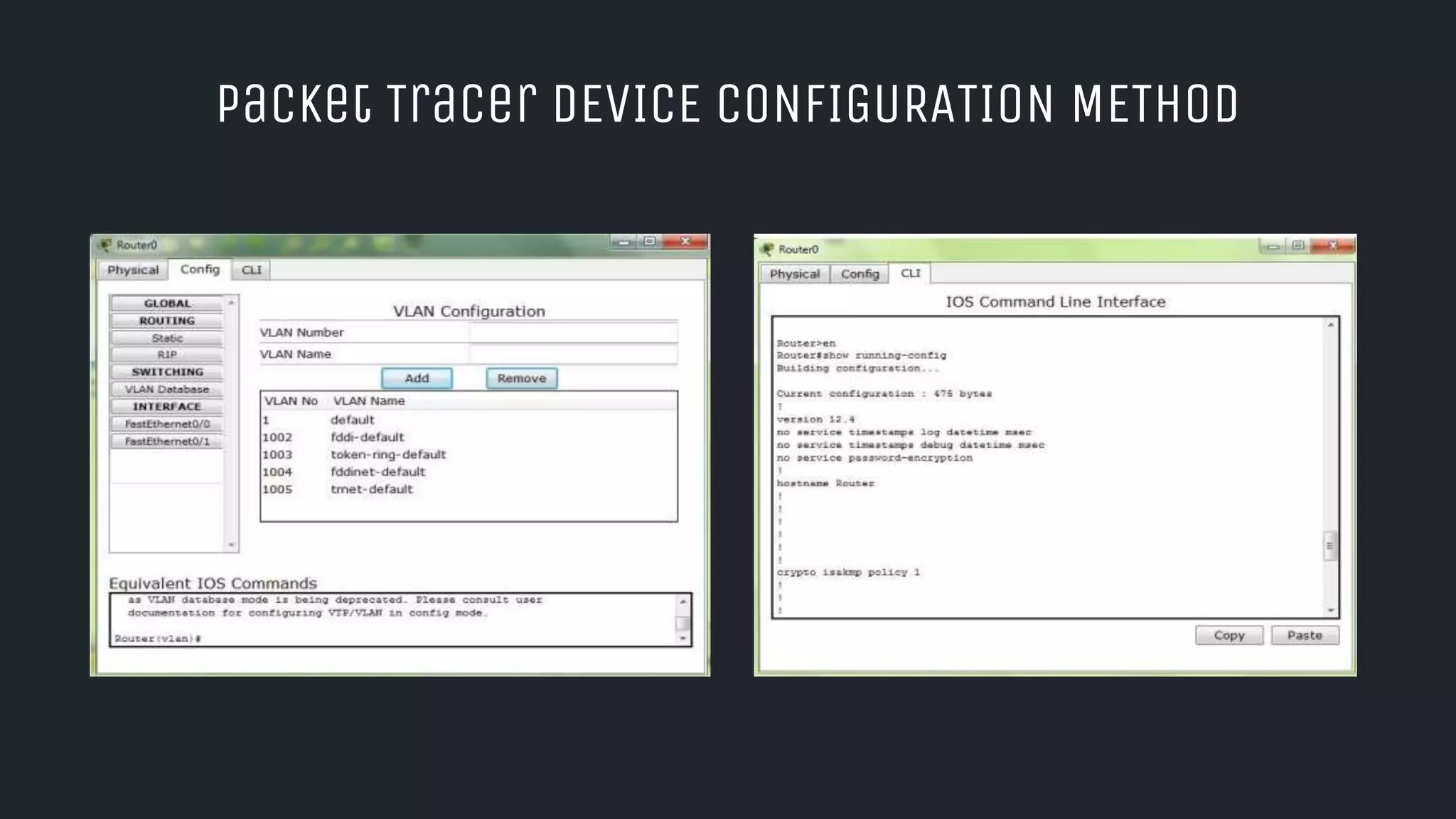
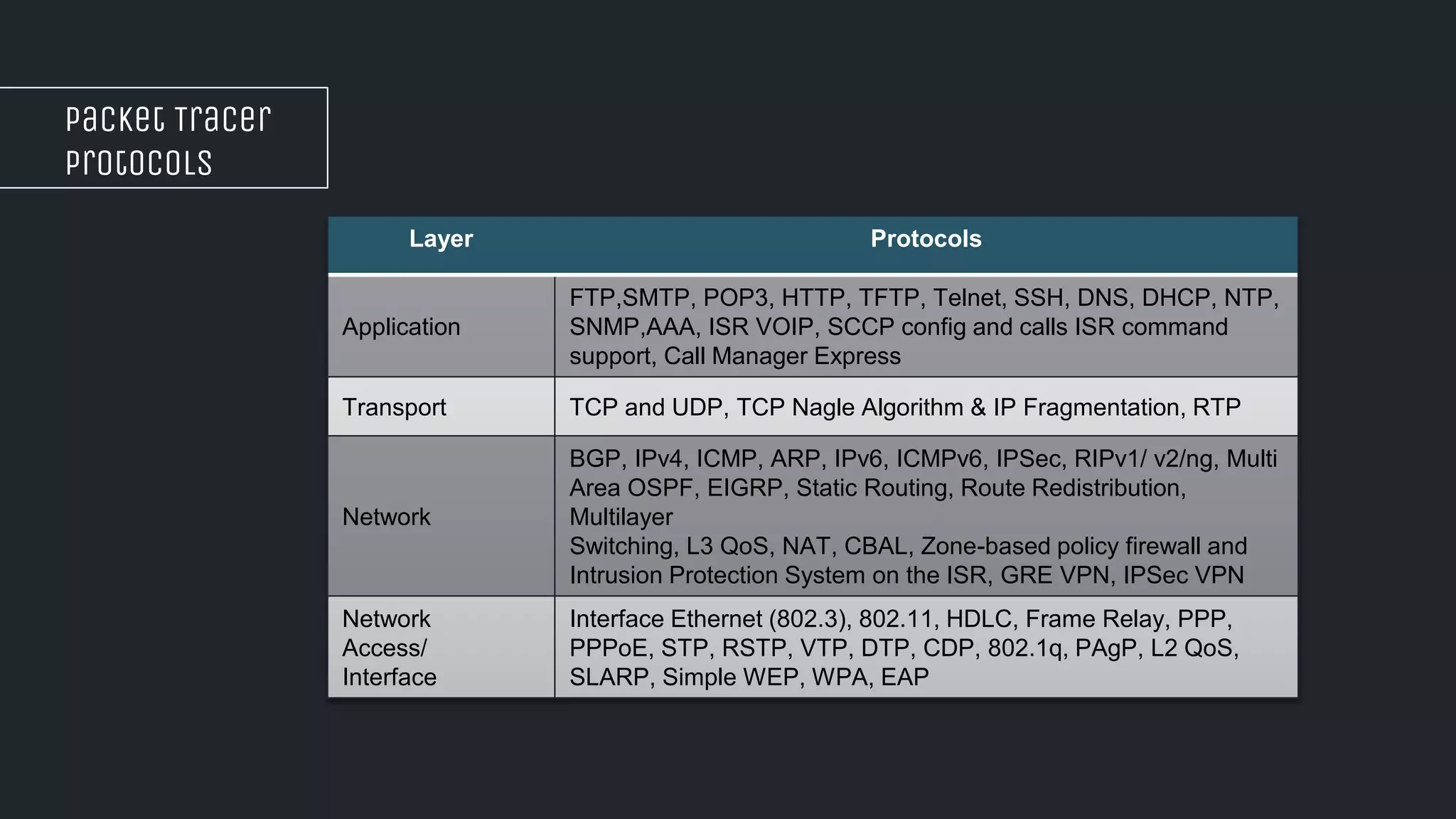
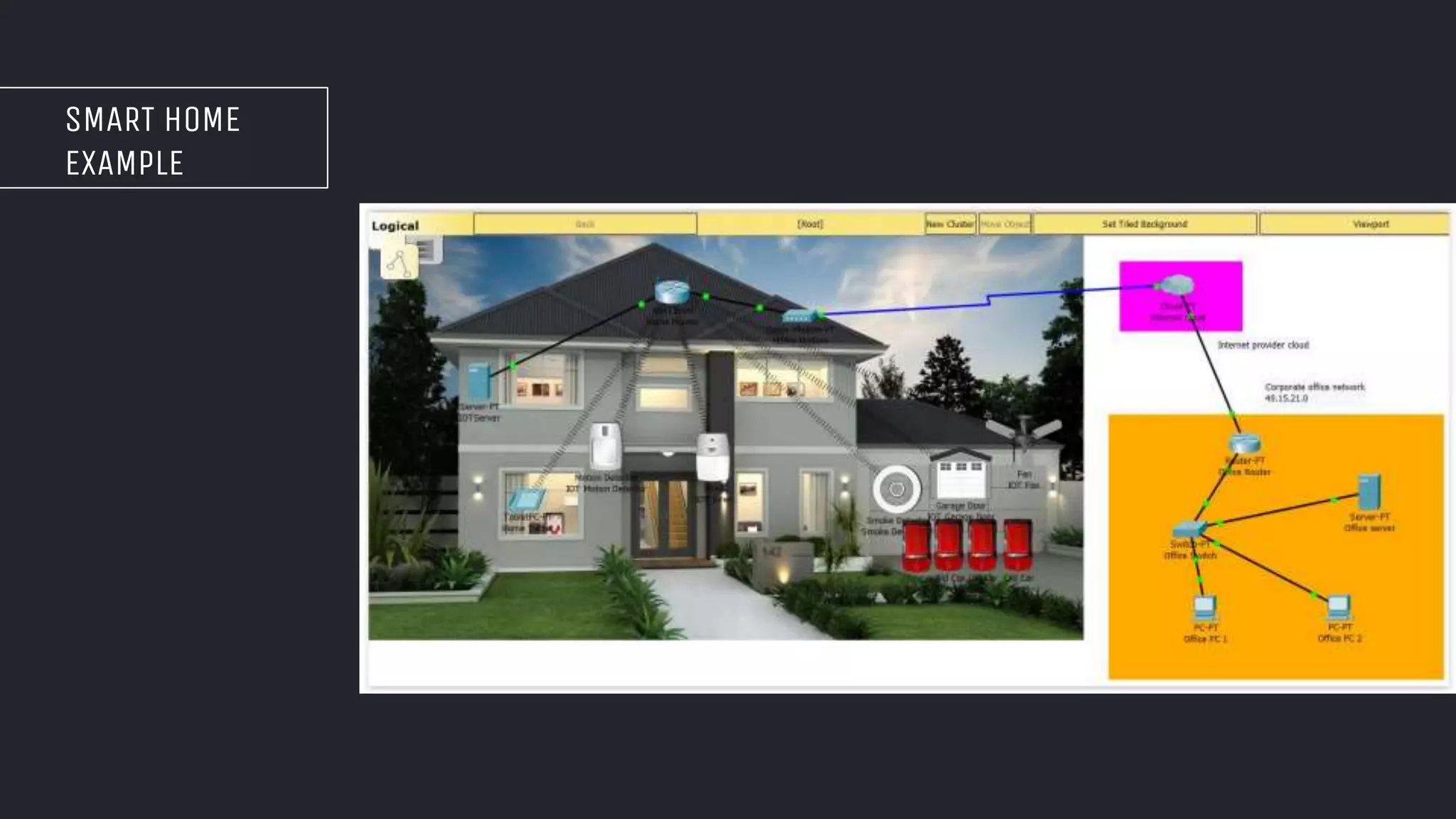
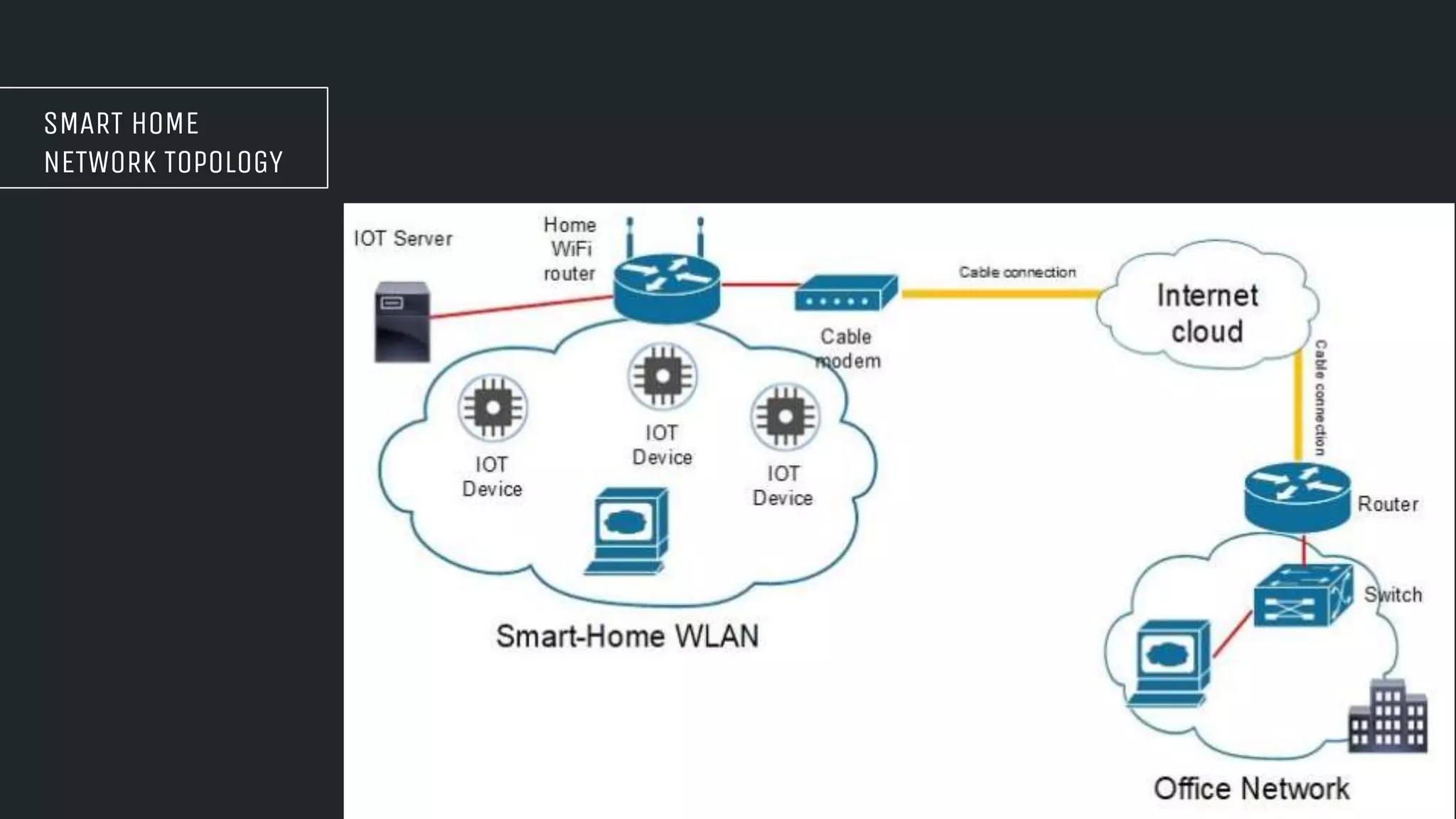
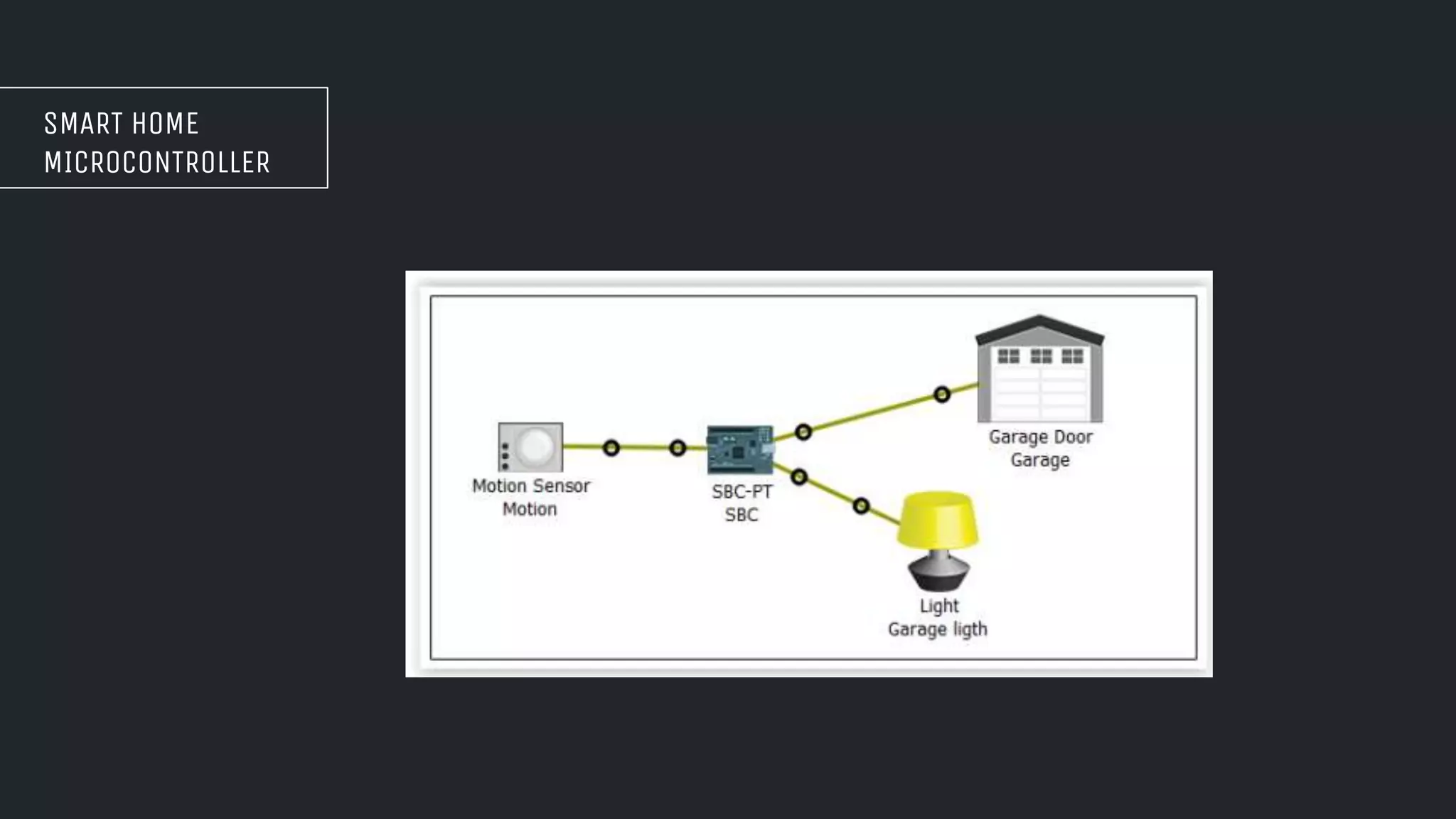
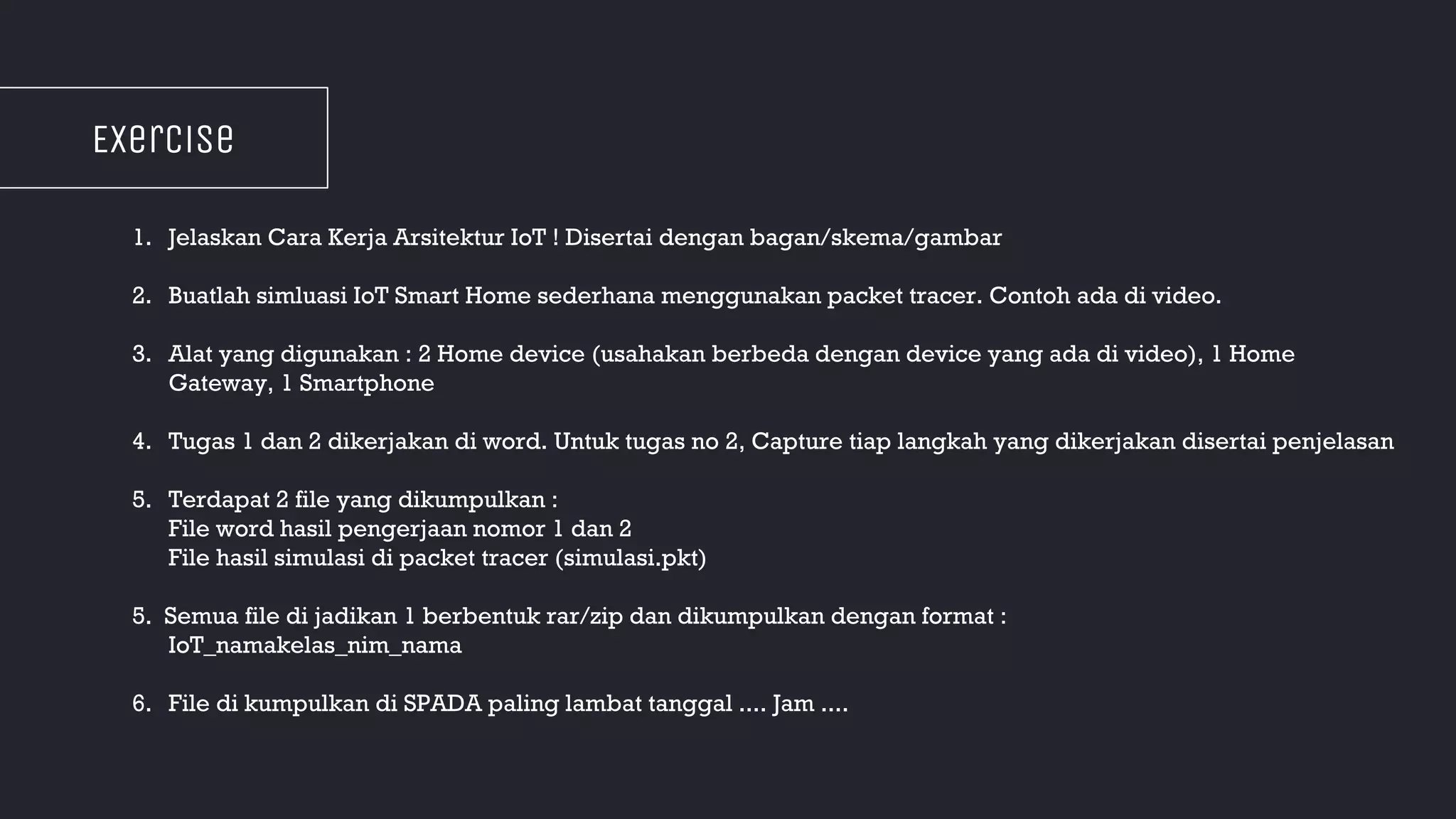
The document discusses the architecture of IoT systems. It describes the different layers of an IoT architecture including the device layer, network layer, service layer, and content layer. It also discusses basic IoT technologies like big data warehousing, gateways, machine learning, and data analytics. Furthermore, it provides examples of using Packet Tracer software to simulate IoT networks for smart home applications.