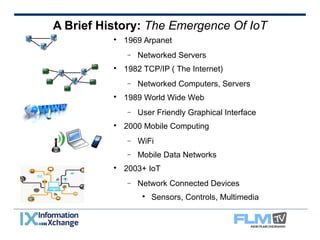
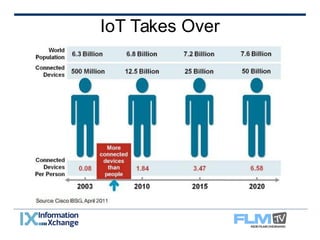
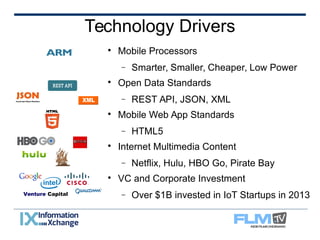
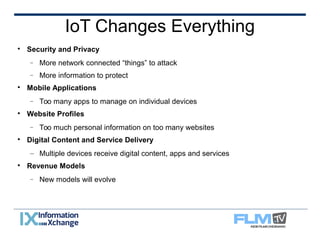
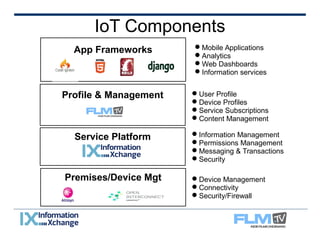
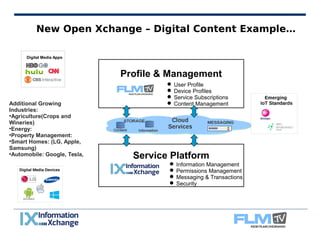
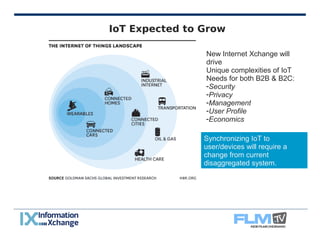
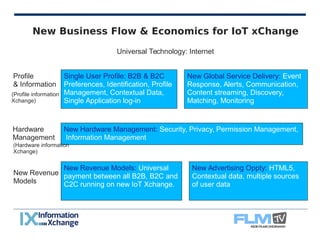
The document discusses the evolution and impact of the Internet of Things (IoT) from its inception with ARPANET to its current applications across various industries. It highlights technological drivers such as mobile processors and open data standards, as well as emerging challenges in security and privacy. Additionally, the document outlines potential new business models and revenue opportunities associated with IoT, emphasizing the need for integrated management systems to address user and device synchronization.