Embed presentation
Downloaded 42 times




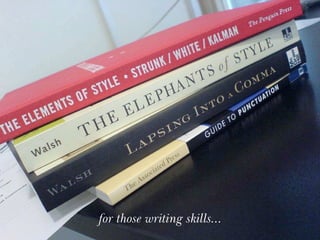
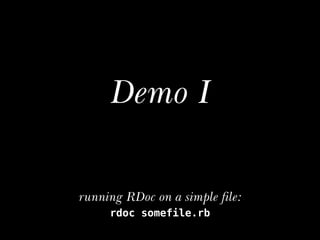

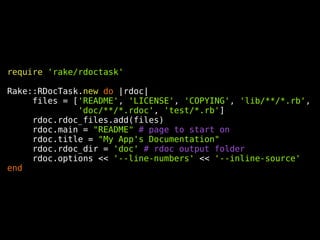
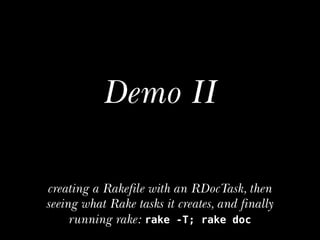

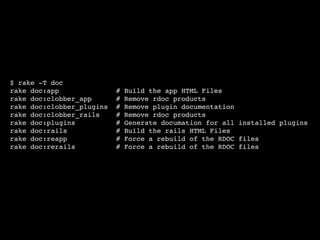

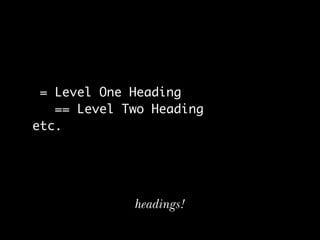
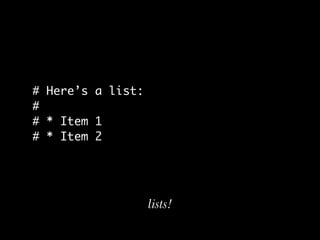
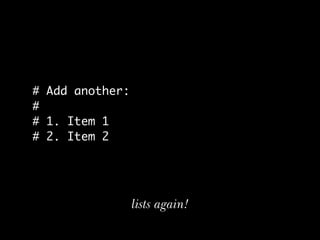
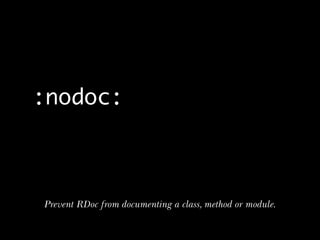
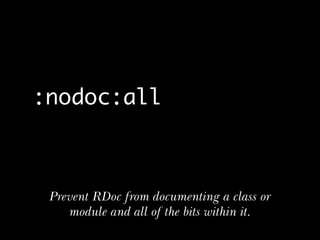
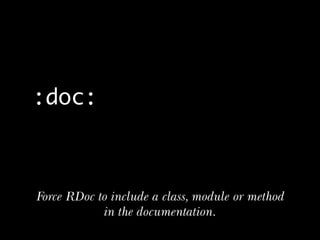
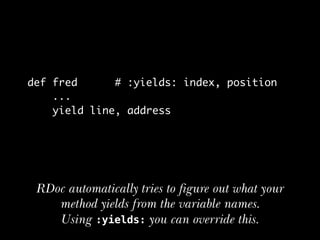


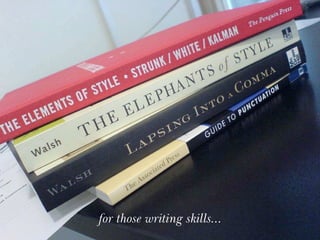
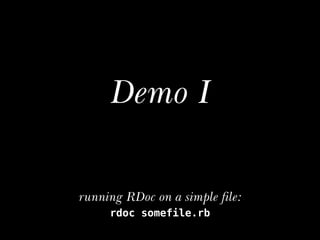
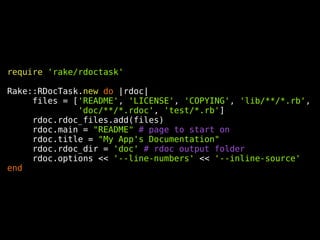
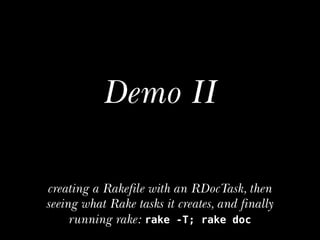
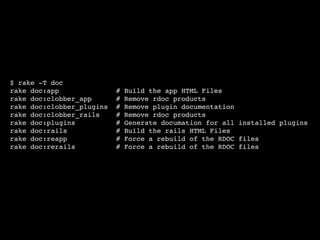
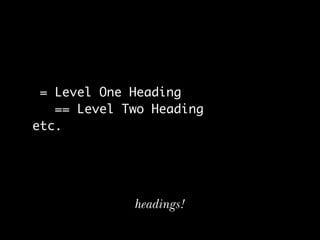
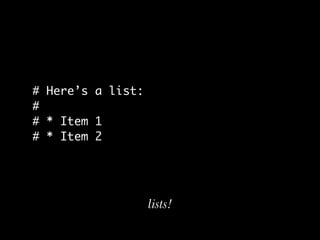
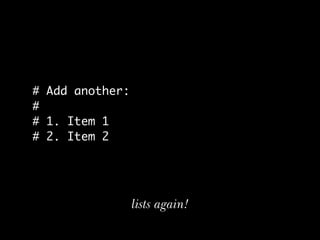
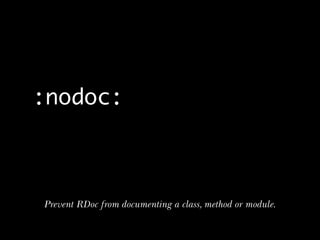
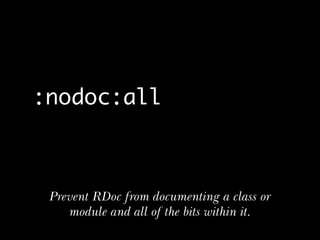
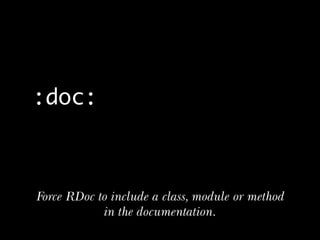
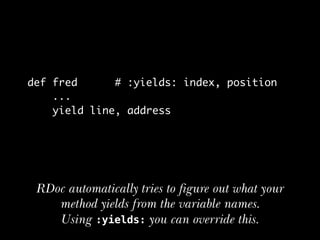
The document discusses the basics for newcomers to publish their first Ruby gem, focusing on the importance of documentation and technical writing skills. It explains how RDoc simplifies the documentation process with automatic features and integration into the code, showcasing demonstrations on utilizing Rake tasks for generating documentation. The document highlights formatting, customization options, and specific RDoc tags for documentation control.